- HubPages»
- Technology»
- Computers & Software»
- Computer How-Tos & Tutorials
Causes of Remote Access Computer Infection
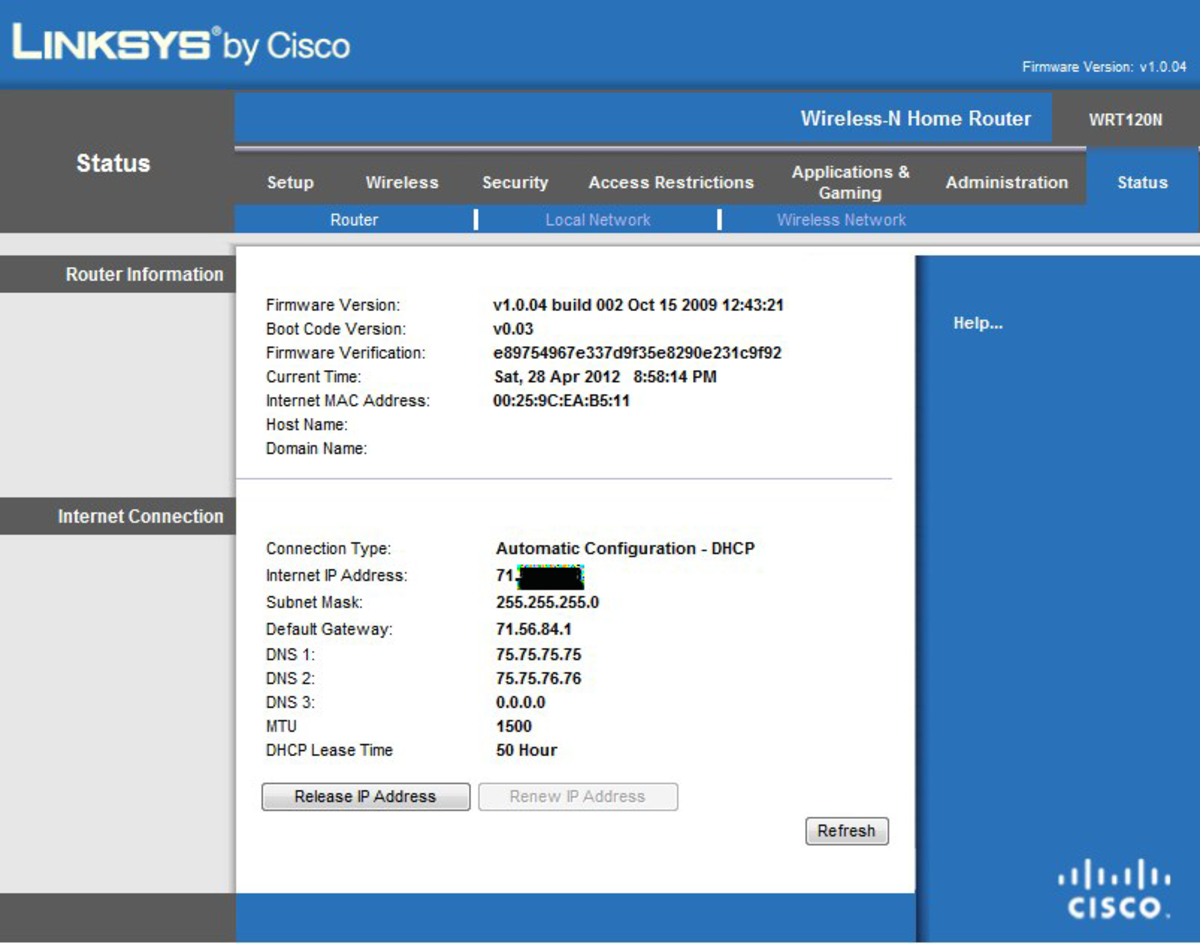
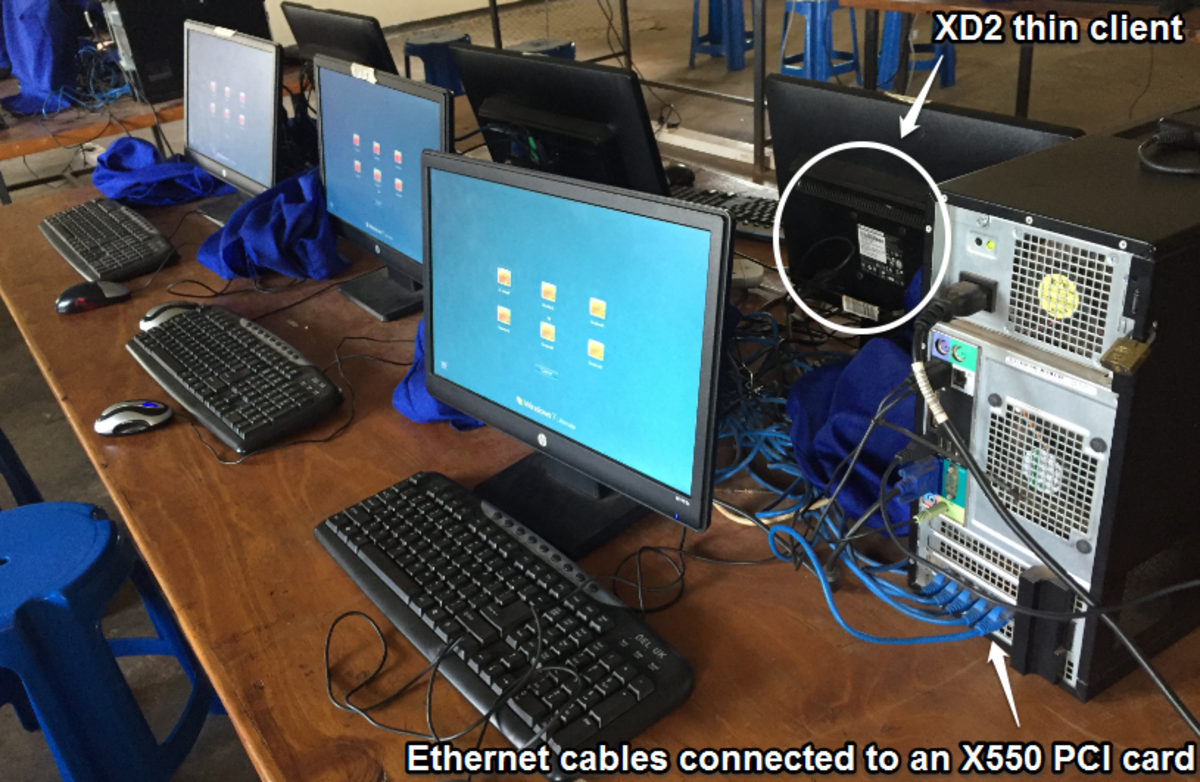
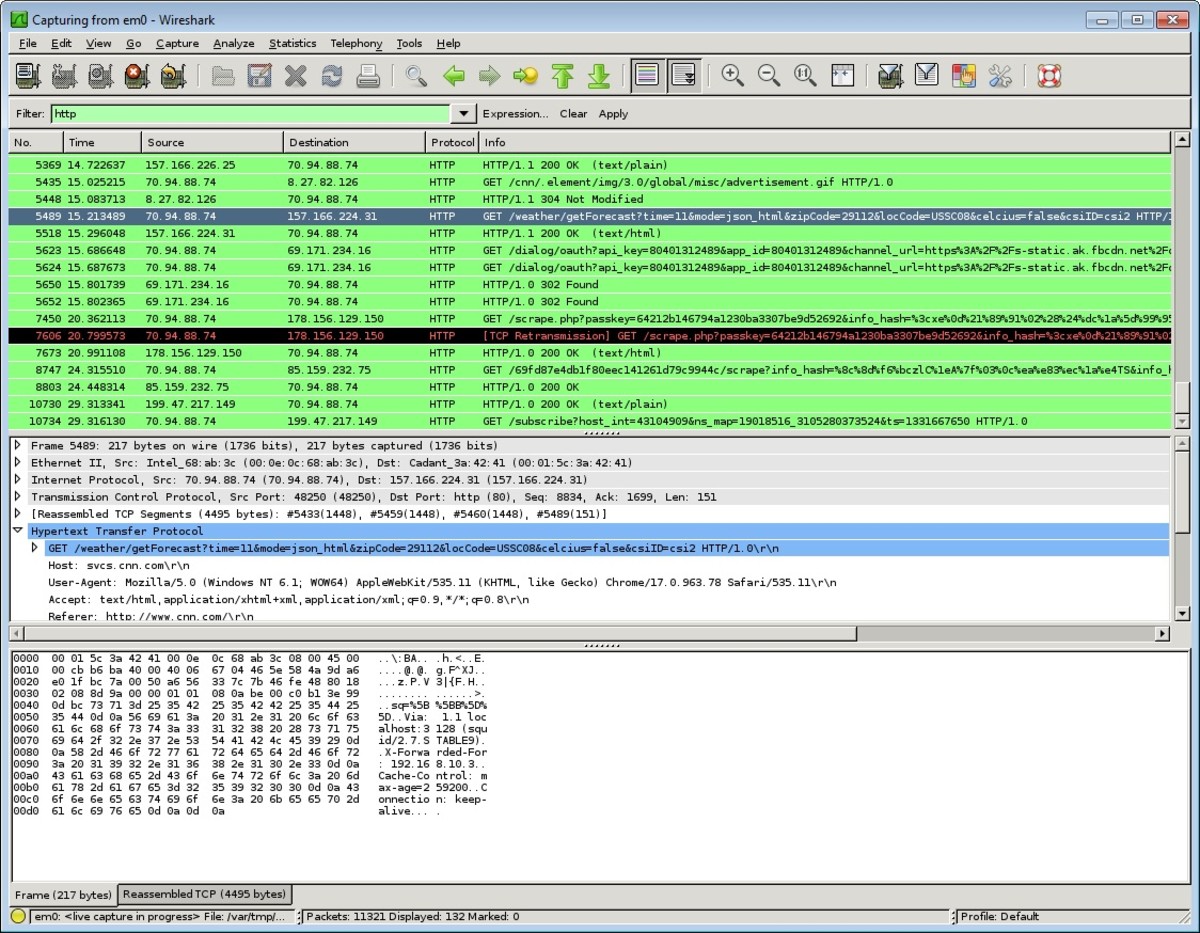
One dilemma that network security administrators face is what to do with users who remotely connect to the network. Administrators have little control over the security state of the computers that remote users connect with. There are two main ways that users connect and both of these methods offer unique challenges. The two methods of remote access are: Virtual Private Network (VPN) and dial up connections.

The least secure method is the dial up connection. In the push to implement VPN connections, many organizations forget about the modem-banks they used for dial up access. According to McClure, Scambray. And Kurts (2005), call-back security measures should be applied to all dial up accounts. Call back security permits a user to log in using a dial up connection then the modem immediately drops the connection. The modem connected to the network then calls back the user at a predetermined phone number to reestablish a connection.
VPN connections offer somewhat more security than dial up connections because the data streams are encrypted across the connections but VPN connections also present some vulnerabilities. For instance, if a user connects to a network using a VPN connection and maintains a concurrent connection to the public Internet, known as a split tunnelling, the user's action can open up the private network to attack from the public Internet. Companies that implement VPNs should decommission the analog lines and modem banks as soon as authorized users have transitioned to VPN access.
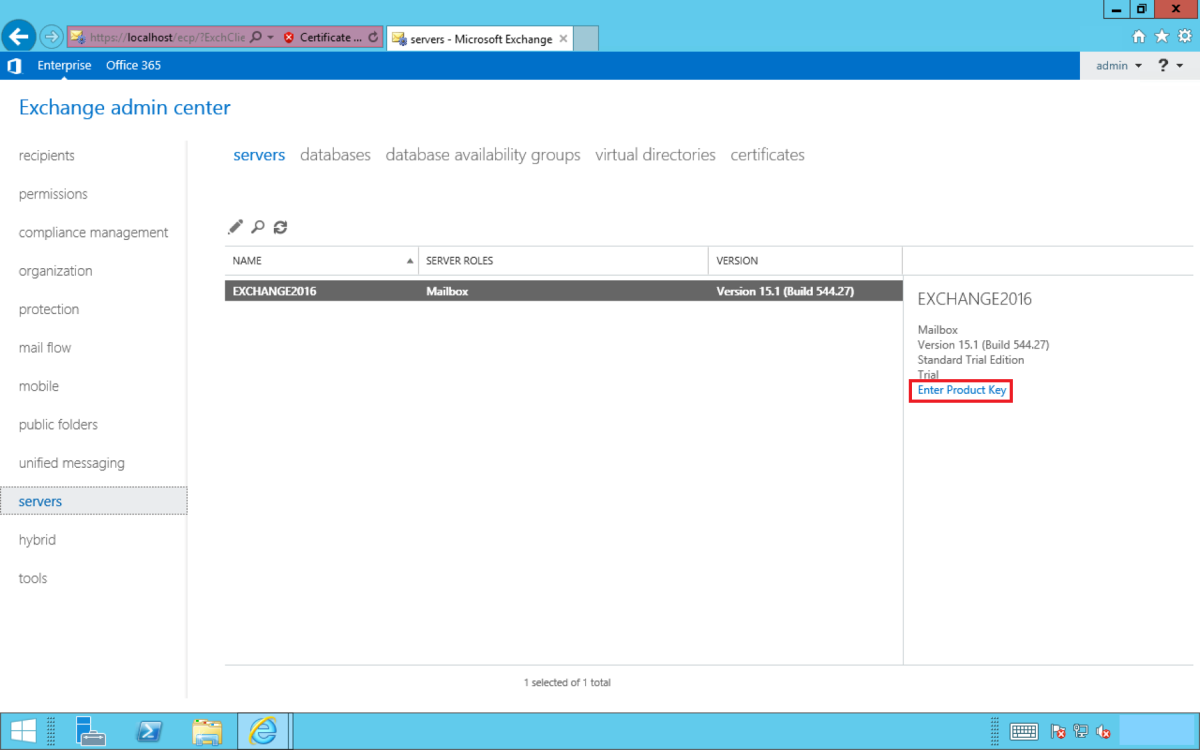
There are some measures that administrators can take to lock down their networks from remote user based vulnerabilities and attacks. Audits of analog lines and central placement of modem banks will ensure that security measures can be placed on dial up connections. All users should make sure their computers are up to date with software patches and hot fixes. Anti virus, anti spyware, anti adware software should be maintained on all computers. Finally, implementing measures like Authenticated Secure Sockets Layer (SSL) connections in combination with a Network Access Control (NAC) appliance would help ensure user compliance.
NAC appliances, such as that offered by AEP Networks, scans users’ “machines for proper security posture and quarantines those that come up short on a VLAN where they can be updated to come into compliance” (Greene, 2006). This may be one of the best measures to protect networks from being hacked by remote users.
References
- AEP debuts network access control appliance
AEP Networks at Interop this week is announcing NACPoint, an appliance that guards against improperly configured computers attaching to networks.
McClure, S., Scambray, J., and Kurtz, G, (2005). Chapter 6: Remote connectivity and VoIP hacking. Hacking Exposed Network Security Secrets & Solutions (5th Ed.). Emeryville, CA: McGraw Hill/Osborne.
What do you think?
Your comments are always welcome.