How to Test Your PC for Viruses and Spyware
Signs your PC might be infected with malware
- Browser freezes, crashes, pop-ups, or redirects.
- Operating system freezes, crashes or reboots.
- Strange error messages or pop-ups appear.
- You experience BSODs, or blue screens of death.
- New unknown processes crop up in your task manager.
- Task manager, command prompt or other services are disabled.
- New unknown programs are listed in Add/Remove programs or elsewhere.
- Higher than usual CPU power consumption.
- PC runs much slower than usual.
- Incoming or outgoing traffic logged in firewalls trying to contact suspicious IP addresses.
- Files are missing or corrupted.
- Your online accounts are hacked.


Testing your PC
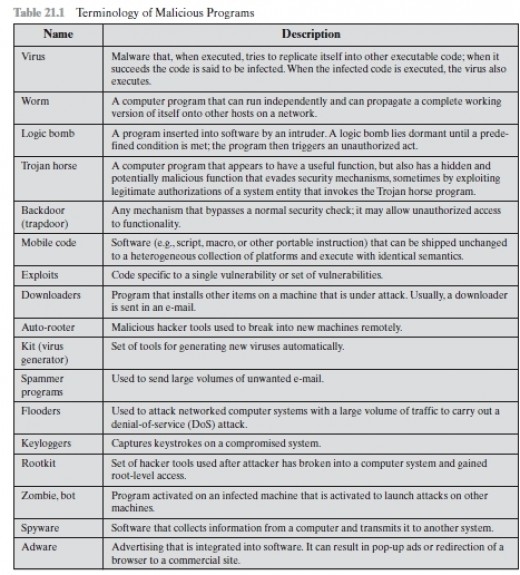
You should clean up your PC or laptop regularly – perhaps once a week, and test for malware (an umbrella term for viruses, spyware, rootkits, etc.). How you do this is as follows:
First make a backup of all critical stuff. You can make back up CDs, DVDs, or put data on flash drives and external HDDs. Basically this is anything present in My Documents, for most users (ones who use Windows anyway). You could also use cloud storage facilities too, but you're advised not to connect to the internet while cleaning and testing, if infected, and especially do not access any online banking, or social networking, or other personal websites while you're dealing with a potential infection. If you really must, do so from a clean system or device, if you have access to one. Think about changing passwords on these websites from a clean system or device too.
In some very severe cases, you may need to download programs that boot from a USB drive and allow you to run in a sort of safe mode environment so you can back up your data. Some malware scanners also run from a USB drive instead of on your hard drive, seeing as the offending malware might try to block your installed anti-virus programs. Some programs utilise a bundled CD or DVD instead. This is the case with some commercial anti-virus products.
You should then turn off System Restore. This flushes any restore points that may or may not have infections present. You’ll then have to reboot your system. Why you want to do this is to ensure that after you’ve finished cleaning, you don’t revert to one of these system restore points and risk re-infecting your PC after all the long, hard work detailed ahead.
Then check your firewall for anything suspicious. Take a look at the firewall logs, and the program logs. Then have a gander at program permissions – what’s been detected on your system, and what’s been given access to the web. Be careful about having programs automatically assign themselves internet permissions. Rather add things manually. For instance, having check marks in the internet server columns of Zonealarm (the firewall I have most experience with) will open ports, and you don't want to have this - at least not permanently. Programs might need access when checking for updates, and that's about it. if there are several attempts outgoing or incoming and one IP is constantly logged, you might be infected with a trojan or some sort other sort of malware. Take note of the IP address and look it up online. Sometimes IP addresses that fall in to an "IP range" end up belonging to legitimate company websites and other times not.
After that it’s off to Add/Remove programs (or Programs and Features in later versions), which comes with Windows. Take a look for installed programs, and remove anything that you don’t remember installing. Spyware often installs itself or is installed by mistake and will pop up here. I also tend to remove toolbars that are a tad too curious, or exhibit behaviour I don’t like – even if it isn’t picked up anti-virus scans or listed as spyware. Spyware is even bundled with legitimate software nowadays.
Run Disk Cleaner (or Disk Cleanup depending on which version of Windows you're using), which also comes with Windows. Check all items except “compress old files” and anything to do with Microsoft Office. Everything else should have its contents deleted – these will mainly be temporary internet files and temporary system files, which may house inactive (not installed) malware. You could also try CCleaner, which does practically the same thing, and you can even specify what should be analysed and cleaned, and what should be left alone. Usually the default settings that come with CCleaner should be fine.
You can also check startup processes inside CCleaner for anything suspicious, although CCleaner’s main feature is a registry cleaner. Be careful cleaning the registry as this might cause undue harm. Entries that are linked to software that has been removed recently can usually be removed safely, but you should at least back up the registry before fiddling around. There are more powerful registry editors around though, like Eusing. Some even have virus protection methods, but these will more than likely be the paid versions.
You can also run Windows' own registry editing program or something similar, but be careful about deleting anything – you need to know what’s what. I mainly just look, but I don’t touch until I get some clarification. You may well need to do this to clean up after a malware infection seeing as there's still "blood on the walls" - and this is usually located in the registry.
Run the task manager by using the combination alt+ctrl+del (and selecting task manager in later editions of Windows), and have a look at your running processes, but don’t kill any processes unless you know what you're doing. Look for anything suspicious here too. The task manager might not list all processes however, or what they belong to. In this case it might be a good idea to use a third party application. There are some programs out there like Spyware Terminator that compile an entire database of programs and processes that are on your PC, and allows you to whitelist and blacklist these processes, too. I wouldn't recommend Spyware Terminator for anything other than this though.

"You may well need to do this to clean up after a malware infection seeing as there's still "blood on the walls" - and this is usually located in the registry."
Then it’s time to run your resident anti-virus program, and do a full system scan for rootkits, viruses, spyware; the lot. This will take some time, but you’ll make the process quicker by having cleaned up your system a bit beforehand. Then if you have some anti-spyware programs (it’s been said that you can usually run one or two alongside your AV program, as long as real-time protection is unavailable or it’s disabled), run some scans with those, too. Malware Bytes Anti-Malware, Super Anti-Spyware and perhaps Spybot S&D are considered some of the best out there, and there are free versions of these too, which will do just fine.
You can take it a step further and run the launcher for an online scanner like TrendMicro Housecall or ESET online scanner, and have these do a scan too. Once again, you can have several of these programs on your PC. They operate from the cloud (can only be run online), and don’t feature any real-time protection that would interfere with your resident AV program. They will have to download and install updates, just like your AV program or internet security suite, before they start scanning.
In addition to scanning your HDD, you can also scan flash drives, CDs, DVDs, etc for autorun worms and the like. But this will take a long time. If you want to do all this, you may well have to dedicate an entire afternoon or evening to just cleaning and testing your PC. So if you’re employed, do it on the weekend.
By this point you’ve been quite thorough. But if you want, you can take a step further, and run some other scans that will compile logs. You’ll find recommended programs like OTL and aswMBR (by Avast) that will scan your system, look for rootkits and other things that might still be hidden. And there’s some other powerful tools out there that are only to be used as a last resort, and not without some sort of assistance. ComboFix is one of these. While its development is hush-hush, you’d download and run it – but be very careful to have your internet security programs, particularly ones with any real-time protection, disabled. Combofix can be quite daunting as it has even reportedly caused more problems for some users' PCs. Always back up your data, constantly.
You can have a look through the logs these programs generate, but you should rather submit them to an expert of some sort, even online, and they will analyse it, and perhaps have it double checked by another person or two. But tools such as these are not recommended for regular use, especially if unsupervised. You could damage your system beyond repair if you insist on doing so.
Using tools like these is said to be the last resort before giving in and reformatting your HDD and reinstalling your OS. ComboFix, in addition to scanning for and removing malware, also patches up some leaks that could lead to infection on your system, but I’m not at liberty to say what these are.
Then after you’ve done all this (with or without the optional extras), you’d uninstall ComboFix if you have used it. Then go to system restore, turn it on, and create a system restore point which is probably clean after all you’ve done. You can then get confirmation on items that have been quarantined by your anti-virus software by looking items up in Google or a virus encyclopaedia. It's best to empty the virus vault of everything - not restore items.
Some experts are of the opinion that searching for rootkits in particular from the desktop isn't the way to go. They claim that the only way to is to do this from boot up, while using a rescue CD or USB stick (I mentioned this earlier), which may come bundled with your anti-virus software, or can be downloaded for free from the web. It might be the way to go to do a search for rootkits while using these tools as well just to be extra certain.
After that it’s back to the regular stuff you do for another week before going through some, most, or all all this again! But it’s a small price to pay for peace of mind. I’m sure you can’t be 100% sure that your system is clean, but you can at least try to keep it as clean as possible. Many alarmists and defeatists out there will tell you that it’s all pointless: if they’re going to get in, they’re going to get in. But I don’t listen to them. Following the above steps will reduce the risk of infection, perhaps even greatly – but it won’t eliminate the possibility of infection entirely. That I can agree with.
It’s like saying condoms won’t stop you from contracting an STD, but it’s been proven that they do reduce the risk of infection. Would you rather go unprotected, and have an almost guaranteed chance of becoming infected, or get some protection so you at least stand a chance of not getting infected?
Some time in the future I will also have an article or two up about what you can do to tighten your system's security. Until then, stay safe out there.
Have you ever had to deal with malware?
© 2012 Anti-Valentine