Top Misconceptions About Hackers
Hackers + 'The Hollywood Effect'
You have heard about Hackers. And seen them do their Evil stuff in a super-cool movie, typing in front of maybe 6 computer screens with one keyboard controlling them all, in a dark dark basement at 3.15 AM in the morning. Their eyes seem tired-yet-so-focused on the black screen decorated with white character commands. Suddenly they hit a button and you see sparkle in their eye and a curved smile on their face. On the screen, out comes the list of the Top-Secret Internal Affairs files. He copies them all in some 'floppy drive' and just at that moment FBI surrounds the building. And he escapes with the floppy or passes it on before being captured and thus the adventure begins....
I tell you there's nothing like watching a "Hacker" doing his Super-Cool "Hacking" through the eyes of Hollywood. Problem is, if you know a little about hacking yourself, then some of this stuff gets real hard to swallow. But why be intent on blaming the Hollywood alone while there are other factors leading to defaming of the hackers. Look at this little "informative article" below in the picture,
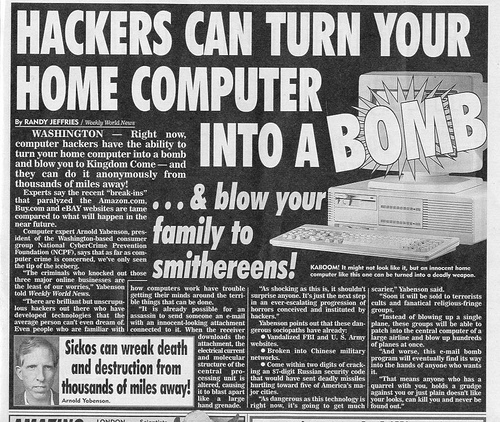
Wow, that's really something! Imagination and Paranoia at its best. I'd love to attend a seminar where the Washington people explain the technical reasons for believing so. A hacker getting through the network security, then through your personal defenses (Firewalls and all) and then actually "Blowing up" the Hardware! Hackers remotely 'opening up CD Trays' or 'turning on your webcam' is pretty believable (actually not that hard to do), but "blowing you to kingdom come" and "blowing your family to smithereens"?? Wow! Words fail me.
Anyway, I don't want to seem too arrogant and let us assume that it is possible (only way I can think of it being doable, is if there was some major hardware issue with a particular device of a particular make + the Hacker in question is Super-Elite). Now that we've assumed that it's possible, Have you ever heard of a Homicidal PC Explosion??
I haven't.
The Truth About Hackers
The word Hacker is not strictly computer-related. It means a person who has deep knowledge of a particular system and has used his creativity and knowledge to contribute to it. I personally rate 'Alessandro Volta' as one of the best Hackers.
The term Hackers is extensively used in media these days to suggest a person who gains unauthorized access to a system for malicious purposes. Hackers themselves call these people 'Crackers'. Hackers are classified into White Hat, Grey Hat, Black Hat etc to suggest the kind of activity of that Hacker. Black Hat of-course being the bad guys (I'll get into the Hats thing in some other Hub).
The Common Misconceptions:
1. All Hackers are Black Hat Hackers/Crackers.
Truth: Not all Hackers have bad intentions or aim to ruin your computer or files. Hackers are curious people and like to discover new things. Some Hackers after getting into a system, leave note to the administrators telling them about the security hole. Hackers are the same people who have built the Internet and USENET groups to bring us together. Hackers are the same people who offer their expertise online when you have a computer problem.
2. All Hackers know the same kind of stuff/ have the same kind of knowledge.
Truth: I could go and on about the various areas of expertise that different Computer Hackers work in, but lets not make this hub technical. Different hackers focus on different technologies and have different purposes and skill levels. Some maybe expert programmers, some maybe Reverse Engineers/Software Crackers, some maybe have excellent TCP/IP Stack knowledge, and so on. Hackers are not all same.
3. Hackers are well-organized.
Truth: There are Hacker Underground Communities where we discuss latest trends but there's nothing like a well-organized single body. Couple of Hacker groups are: Alt-2600 and Cult of the Dead Cow.
4. Hackers are usually people in the same age group (12-30).
Truth: As opposed to the common thinking that Hackers are usually Teenagers with nothing better to do, Hackers belong to all age groups.

End Note
Click edit above to add content to this empty capsule.
Hope you've enjoyed reading and of-course the next time you see that 'Hollywoodified Hacker', you'll know better. If you already did, then I'm glad.
(I really love to read your comments about my pages, Please leave some).