- HubPages»
- Technology»
- Computers & Software»
- Computer How-Tos & Tutorials
How To Configure Your Bit-Torrent Client


Bit-Torrent Configuration
Bit-torrent clients have rapidly become the preferred filesharing applications that are now used, mainly due to their high speed download abilities which is useful for larger files. With technological capabilities evolving at an incredibly fast rate, it's true that files are constantly becoming larger and larger. Needless to say, bit-torrent clients are capable of downloading files at much higher speeds than conventional network based peer-to-peer applications such as Limewire or FrostWire, which both rely on the Gnutella network.
The mistake that many first-time bit-torrent client users make is that they do not learn how to configure their bit-torrent software properly which, according to software developers, limits both the upload and download speed of the client. However, there are certain security risks associated with configuring theseapplications the way intended and by configuring these applications with security in mind, download speeds don't generally seem to be too much slower. If an bit-torrent client is configured for high security then the client won't be able to receive connections via the trackerless (DHT) network but files can still be seeded and uploaded in the normal way.
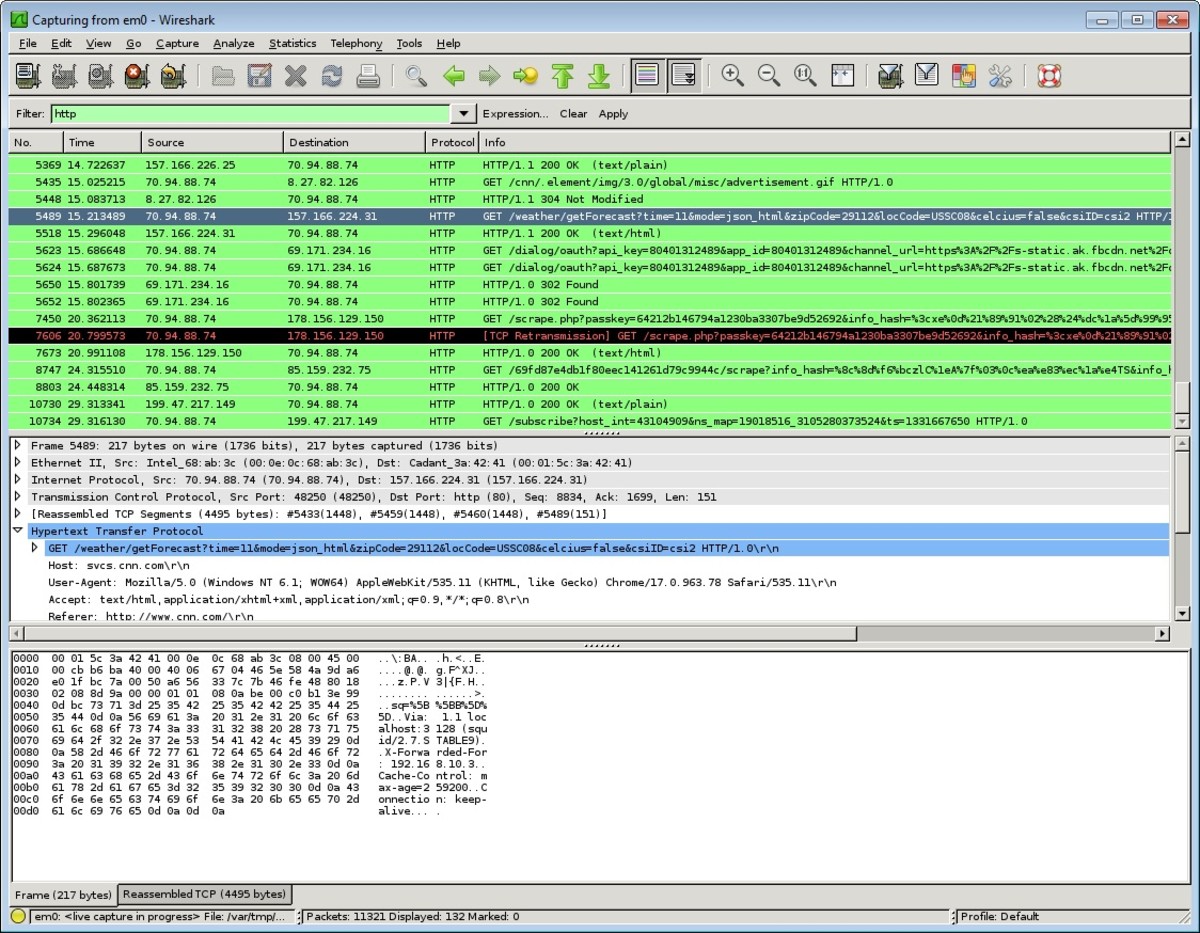
The correct way to configure a bit-torrent client, such as BitComet or uTorrent, is to configure your modem/router to forward (open) a listening port which can receive incoming connections from other users clients and to configure your firewall to allow these incoming connections through the listening port. The only problem with opening up a port in such a way is that you will then be willfully accepting incoming connections from various IP addresses from all over the world. Unless you use an IP blocklist you are then just about guaranteed to have bad IP ranges connecting directly to your computer. Additionally, IP blocklists only tend to block out about 80% of bad IP ranges at maximum. Despite a lot of speculation on this issue, you are only as secure as the program listening on the open port.
If your bit-torrent software is accepting inbound connections then it needs to be monitoring every single IP address's activity to ensure that there is nothing untoward happening, then should ban any IP address which may have perceived risks associated with it. However, there are no bit-torrent clients that claim this procedure is performed and even if bit-torrent clients did operate this way, there is still a huge risk.
There are now a lot of fake files and virus torrents being hosted on many torrent websites, mainly put in place by governments (allegedly) in an attempt to deter illegal filesharers. Many of these government agencies allegedly use a reconfigured bit-torrent client to try to make a direct connection to your computer. Should they find you downloading one of their files who is then to say what sort of thing they may be capable of once that direct connection has been established?
Governments have access to software which is considerably more advanced than software available to home users and they may keep track of all the IP addresses that the hosted (shared) file has been receiving hits from. Should you be attempting to download copyrighted material, they may then send out a government warning to your internet service provider (ISP) for you, warning you to stop downloading or to be cut off from the internet. They could also intentionally infect the files with specially crafted software that, once downloaded, allows them access to your computer. Governments do in fact have the legal right to develop and utilize this kind of software in such a way. Ultimately, they may be picked up by decent security software as being malicious or may potentially be detected using heuristic scanning.
On Amazon
Software such as Bitcomet suggests at startup, if you are using XP Service Pack 2, that you should patch your TCP/IP limit and allow between 50-200 half-open (unestablished) connections. In Service Pack 2 there is a default security limit of ten half-open connections per second. This limit is put in place to stop malicious viruses and worms spreading infections over the internet in large volumes. Of course, if you have an open port and someone that is connected to you is making a large volume of unestablished connections directly to your IP address then how are you going to determine whether this is a genuine connection or a worm trying to find its way into the open port? The answer is you can't.
Patching the TCP/IP limit is an old technique and was originally intended for use on dial-up connections because they are so slow. On faster broadband connections, the technique/patch is pretty much redundant as it will probably only help to make your initial connection to your peers a little faster at startup. Half-open/unestablished connections are only going to be dropped in the end anyway and it will probably therefore be more likely to slow things down.
If a machine is infected and has been turned into a spam-bot, then it will attempt to make large volumes of half-open connections in order to spread infection quicker. Remember, it's better to be safe (and legal) than sorry.
© 2007 Marc Hubs