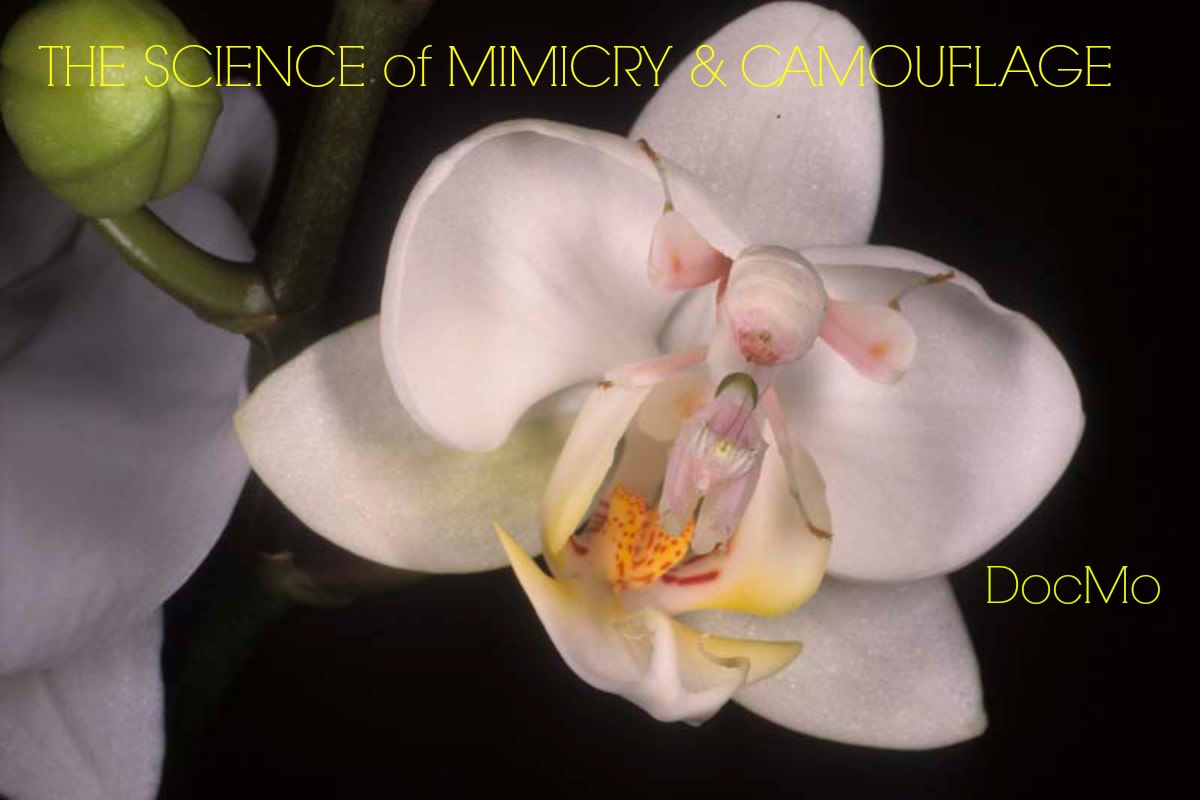
Sincere Flattery: Batesian Mimicry
What do you do when you have no natural defense against predation? You copy the aposematic markings of your noxious neighbors. Many animals today employ this strategy with great success. So what is aposematism? Aposematism is a term used to describe defenses used by animals to avoid predation. It includes the sequestering of toxic compounds in the body, or the use of stinging hairs or venom to inflict pain. Insects that employ these defenses are unpalatable to potential predators. They display this trait through a variety of warning cues:
- Patterns and bright colors.
- Sounds.
- Movement.
- A combination of the warning displays mentioned above.
Predators who attempt to eat aposematic insects will find themselves experiencing discomfort and will learn to associate that discomfort with the colors and patterns of those particular insects.
As time passed, palatable insects began to resemble unpalatable aposematic insects. Both model (aposematic insect) and mimic (palatable insect) share common predators. So when predators learn to associate the colors and patterns of the model with discomfort and consequently avoid preying on the model, they would also avoid eating their mimics.
The Discovery of Batesian Mimicry
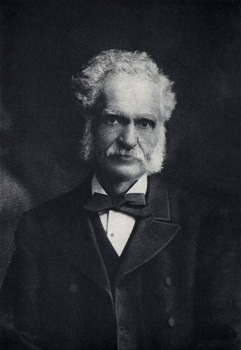
On May 28, 1848, the naturalist and entomologist Henry Walter Bates along with his colleague Alfred Russel Wallace left England in pursuit of wealth and discovery. Their aim: to collect and sell specimens from the Amazon Basin and perhaps unearth evidence that would help solve the problem of the origin of species.
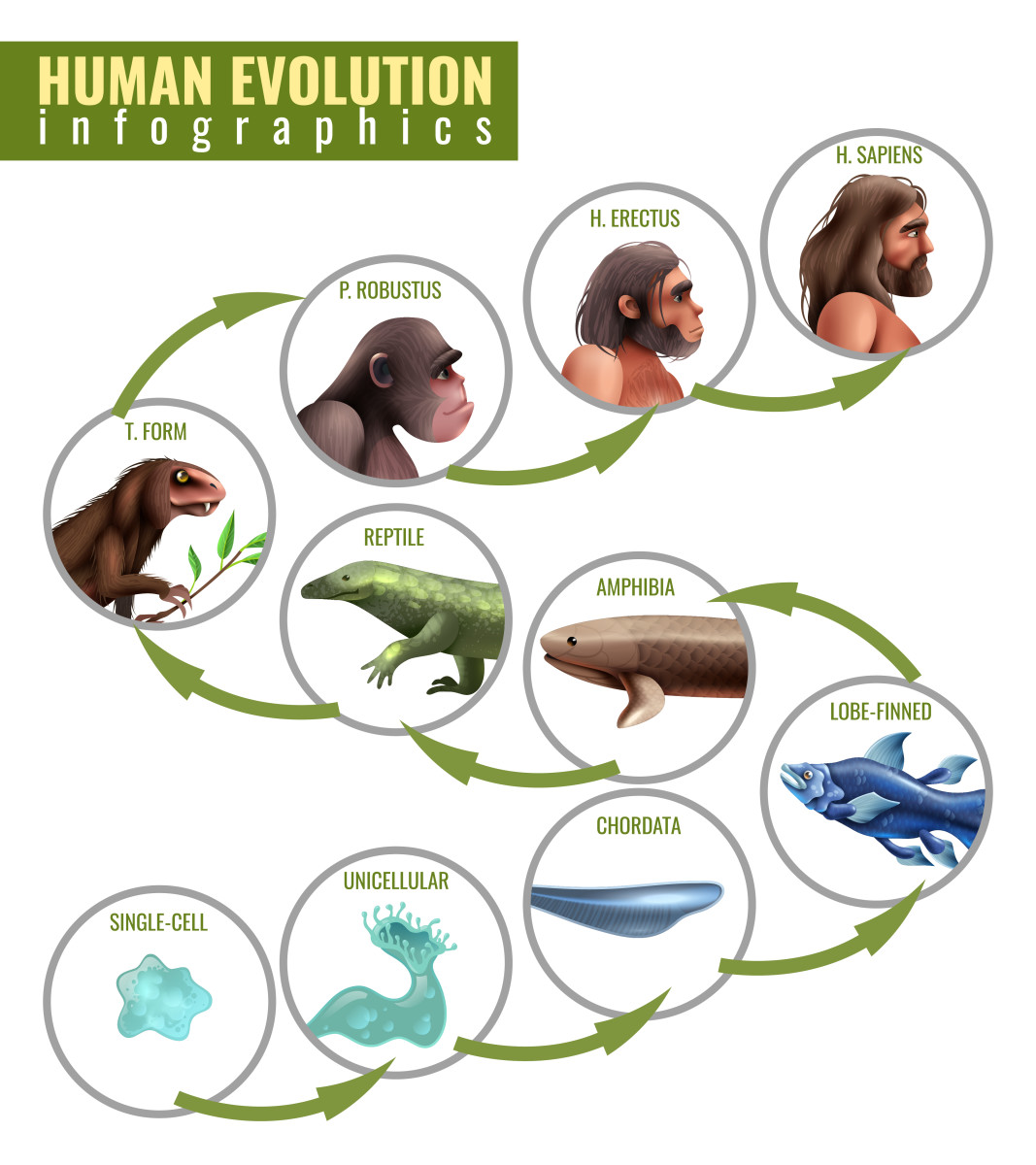
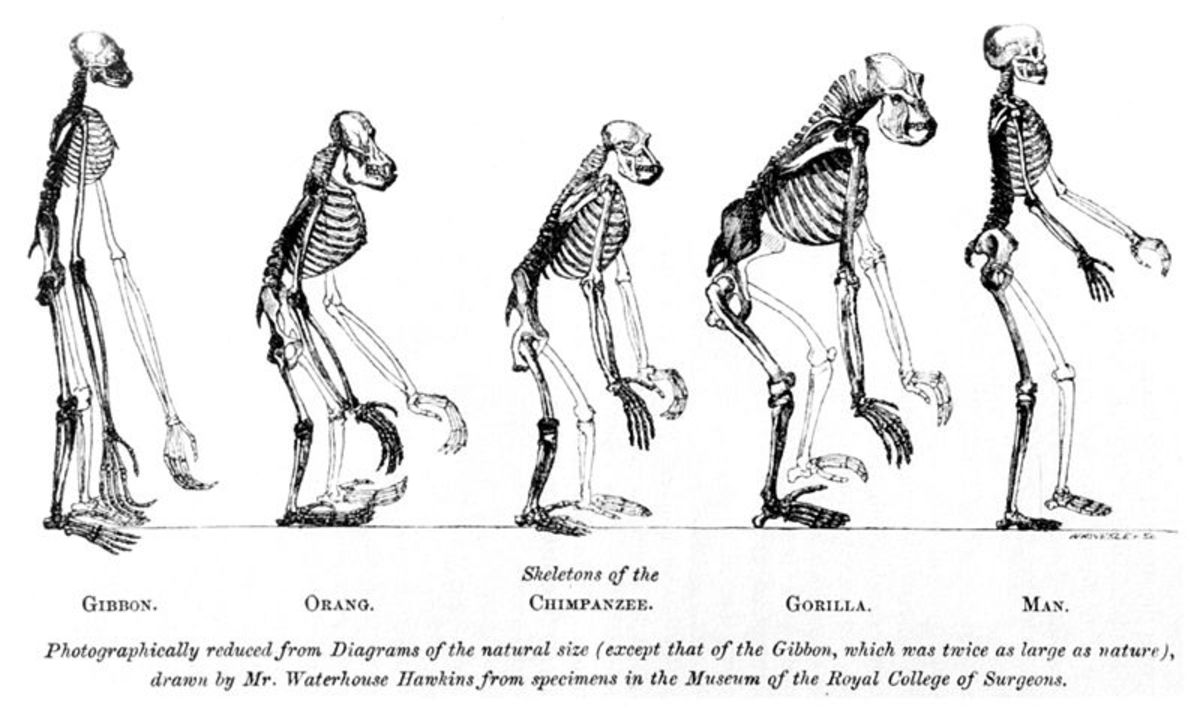
They arrived at Pará that very same year, disembarked from their ship, and headed into the untamed Amazon forest. This would be Wallace’s home for the next four years while Bates would stay there for a total of eleven years. Wallace would go on to conceive the theory of evolution by natural selection alongside Charles Darwin.
Bates, on the other hand, would spend the next eleven years passionately collecting insects that he would then send back to museums and collectors in Europe. Bates noticed that his collection contained species of butterflies that closely resembled other species of butterflies that lived in the area. He found this peculiar and thought to himself, why would it be necessary for two different species of butterfly to have such a close resemblance?
He later discovered that harmless butterflies were mimicking the species that were unpalatable to birds and lizards. His observation and theory crafting would lead him to conceive an explanation for this odd occurrence. Bates would later publish his explanation in a paper in 1862 that would later come to be known as Batesian mimicry.
In it, he theorized that colors and patterns of the unpalatable butterfly served as a warning to predators. Predators would learn to recognize these particular butterflies as inedible through past experiences of discomfort while eating said butterflies.
From then on, they would not bother eating them again. It was his belief that the mimics took on the appearance of their unpalatable counterparts because they received the same protection from predation. His theory was hailed by Charles Darwin as a fine example of natural selection and helped grow the field of evolutionary science in its early days.
How Did Batesian Mimicry Evolve?
Perhaps you’re wondering, how on earth did such a thing happen? Surely the insects did not just think to themselves one day that they ought to change their appearance to one resembling that of a noxious species?
You are right in your assumption that they did not purposefully change their appearance. The answer to how it occurred is quite simple: through a series of mutations and selection. Bates theorized that a mutation arose in the mimics that made them appear a bit similar to their models.
As a result of this, mimics within the population that had this mutation had lower rates of predation than their non-mutant brethren, because they were periodically mistaken for the noxious species. This mutation would then be passed down to their offspring (as it conferred greater fitness) until mutants were more abundant in the population.
Then another mutation arose that made the mutants more similar in appearance to their models. Predation rates for mimics that had both mutations would be lower than that of those that only had the first mutation, because they would be mistaken for the unpalatable model more frequently. This mutation would be passed on to their offspring and so on and so on until we arrive at a mimic that is almost indistinguishable from its model..
Bees, Wasps, Tiger Beetles, and Their Mimics
Having been stung by bees and wasps on a multitude of occasions, I know how painful and unpleasant the experience can be. What’s more unsettling is thinking you’re in the clear and then having another bee come darting at you with intent to sting.
Yet, in nature, there are some insects that exploit the reputation of bees and wasps for inflicting pain and anguish. The hoverfly is one example. Hoverflies are often seen hovering over flowers before promptly landing to collect their nectar. This tricky little bug mimics the colors and patterns of its pain-inducing, stinger-wielding cousin, the honey bee.
Most predators would rather not be stung by angry honey bees, so they leave them to their own devices. The hoverfly’s deceptively honey bee-like appearance, therefore, acts as an anti-predator repellent. The locus borer isn’t above mimicking bees and wasps either. This little beetle, which attacks black locust trees of the genus Robinia, can be seen skirting around wearing colors and patterns much like those of the paper wasp.
And much like the paper wasp, its appearance serves to ward off predators. Then there's the mimic of the tiger beetle, the grasshopper Condylodera tricondyloides. This grasshopper so closely resembles its model, both in movement and appearance, that even the experienced entomologist Professor Westwood mistook it for a tiger beetle placing it in a cabinet with other tiger beetle specimens before realizing his mistake.

The Mistaken Case of Mimicry
The milkweed protects itself from predation by producing and storing toxic chemicals called cardenolide. Immune to the effects of the toxin, Monarch butterfly larvae feed almost exclusively on milkweed. The larva capitalizes on cardenolide’s toxicity and its immunity to it by sequestering the toxin in its tissues.
The sequestered toxin is then passed on to its adult form, the monarch butterfly. By doing this, Monarch butterflies become foul-tasting and poisonous to potential predators. For many years, it was thought that Viceroy butterflies were harmless mimics of monarch butterflies. However, recent studies have shown that viceroy butterflies are just as unpalatable to predators as monarch butterflies.
They are now known to display a type of mimicry called Mullerian mimicry. A type of mimicry that exploits the decreased time it takes for a predator to learn the markings of a noxious species when it preys upon two separate species that have similar markings.

Just the Right Proportion No More No Less
Models tend to greatly outnumber their mimics. This imbalance creates a situation in which predators will have a higher chance of first encountering and trying to eat the unpalatable model. Armed with the experience of eating the unpalatable model, predators will leave both mimic and model alone.
However, if the mimic becomes just as common or more common than its model, predators will take longer to associate the bright colors and patterns of the model with an unpleasant experience. And so the cost of learning to avoid an unpleasant meal is increased, with casualties to both model and mimic.