- HubPages»
- Technology»
- Internet & the Web»
- Social Networking»
Defending your systems:New Security tools and techniques
New Security tools and techniques
As days pass, Information Technology Gigs keep on releasing and updating new threats. Most of the viruses, Trojan horses, worms, spywares and adware’s are an advancement of their previous versions. Similarly, Savvy technicians and security analysts also keep on updating their antivirus definitions, remodelling and restructuring their special softwares in an attempt to counteract the effects generated by new security threats and attacks. They also keep on modifying and innovating new methods that can be used to either evade or block security threats. Because most of the systems security attacks and threats are propagated via the internet, much emphasis is placed on new internet security protocols and tools that can be used to evade such a menace. Therefore, there are various latest technique and tools used to avoid the above-mentioned security threats and techniques. Below is a list of threats and an analysis of the latest tools and techniques used to counteract such threats?
Kernel Level root kits preventive/removal tools
The most efficient ways of defending against Kernel level rootkits entails denying hackers the chance to gain administrative privileges on the system. This is because attackers need the opportunity to install these rootkits manually on the system. However, the most current technique is the installation of relevant security patches. It also involves the use of kernels that do not support loadable kernel modules (LKMs) supporting dynamic kernel modification. Examples of such Kernel modules comprises of UNIX and versions V 1.09, V1.10 of HOWTO (Stevenson and Altholz, 2006). These Kernel modules do not allow for dynamic modification of Kernels, making it difficult for hackers to load rootkits on a computer. However, they are obsolete in Solaris. In addition, rootkits can be prevented by their early detection and removal using the latest rootkit detectors and removers. The latest versions of these tools comprise of Microsoft Root Kit-Revealer, Sophos Ant-Rootkit, GMER and Trend Micro Rootkit Buster (Stevenson and Altholz, 2006).
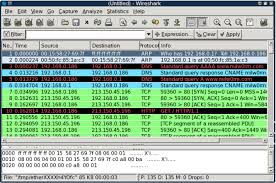
Wireshark
Anti-Packet sniffing tools and techniques
Detecting and blocking packet sniffing applications is difficult because packet sniffers are naturally passive. Additionally, it requires a high level of knowledge in network security-related courses and skills in order to analyse website traffic, identify their abnormality and encapsulate their data in order to pinpoint which bandwidths are running packet sniffing applications. However, there are various techniques and tools that are currently used to detect packet sniffing applications over the internet and block them before they sniff any data (Gandhi et al, 2014). These techniques include; the ping, ARP Watch, latency and Intrusion Detection System methods. However, the most secure way is the use of encryption using various secure protocols such as secure shell, (SSH) Hyper Text Transfer Protocols (HTTPs) and Secure File Transfer Protocols (SFTP). These security protocols encrypt their data packets such that only the receiver servers can decrypt once a handshake has occurred. A handshake refers to the exchange of digital certificates and seals between computer servers to ensure that the network content is availed to the legitimate receiver. Because most of the above-mentioned techniques are not easy to learn, security analysts have come up with new security tools that can be used to detect and prevent packet sniffing applications running over the internet. Most of these tools are advanced packet sniffers that allow the security analysts to view the threats at the angle or in the same dimensions of a hacker. For instance, Wireshark or ethereal is a packet sniffing software. It enables individuals to run it over their networks and sniff other data packets (Hess, 2010). Later, the security audits can filter and isolate these other packet sniffing applications (Gandhi et al, 2014). If these applications are not legally run by the host networks in accordance to their defined security plans, the applications are flagged as abnormal. In Ethereal’s outputs, abnormal network traffics and applications are themed with a black colour (Hess, 2010). The security auditor can then block/remove or shut them down. The network security auditors can also filter, sieve and encrypt data packets that were in the process of being sniffed in a bid to boost their security protocols. There are also other latest softwares that perform the same function as ethereal and are used to prevent data sniffing. These comprise of opti-view protocol expert, Netasyst Network Analyzer, Networks Instrument Observer, Snort, Neped and Anti-Sniff (Gandhi et al, 2014).
Ratings
Penguins

Anti-Botnets and Denial of Service preventive tools and techniques
There are various latest techniques used to prevent denial of service threats. Firstly, DOS can be prevented by installing the latest security patches (Gupta, Joshi and Misra, 2010). These patches prevent DOS by installing all the available security holes/flaws with the required programs that prevent the exploitation of these flaws. Secondly, DOS can be prevented by performing IP Hopping (Gupta, Joshi and Misra, 2010). This entails dynamically changing the IP of the active server with a pool of multiple servers after short durations. This confuses the botnets and other programs that create buffer overflows because they end up with unidentified IP addresses to ‘poison.’ Similarly, there are various tools/applications used to prevent the DOS attacks. The latest one comprises the use of a dotDefender web application firewall (Malekar, and Waghmare, 2013). This application scans routers, open ports, HTTP traffics and checks their traffic with its set rules such as allow or deny protocols. However, the most important feature of this firewall tool is that has inner capabilities of protecting the computer servers from other threats such as path traversals, buffer overflows, SQL injections, Cross scripting and security compromising techniques. Conversely, botnets can be removed and prevented via the installation and use of the latest antivirus softwares. One should also keep on updating their virus definitions to help prevent the latest virus versions. Currently, the most commonly used premium antiviruses are Webroot SecureAnywhere Antivirus, Kaspersky, advanced System Ultimate 7 antivirus and Panda Free Antivirus 2015.
The 10 Most Notorious Hackers of All Time!
A comparison of the above-given tools and techniques
The above-given security tools and techniques are applied in different situations. However, one thing is common: majority of them seek to prevent threats that emanate from network usage. Therefore, there must be those tools and techniques whose competence in providing security to computer systems is higher than the rest. In my opinion, I feel that dotDefender web application firewall is the best security tool among all others. It is also the tool that bears the highest chances of succeeding in the market. This is because of various reasons. Firstly, the tool runs several scanning procedures over every port, hub or router used to connect to the internet. According to Malekar and Waghmare, (2013) this gives it the added advantage of identifying and blocking threats before they compromise the system’s security (Malekar and Waghmare, 2013). Secondly, its applications are easy to run on the computer. It does not require intensive skills in system’s security as required while using ethereal and other related softwares. Thirdly, many security tools prevent one for of threat. For instance, antiviruses prevent against attack by viruses and worm but not hacking and sniffing tools. On the contrary, dotDefender web application firewall prevents different forms of threats such as SQL Injections, Cross site scripting codes, data sniffing tools and many other forms of threats (Malekar, and Waghmare, 2013). It even prevents botnets and buffer overflows that might lead to Denial of Service attacks. Therefore, it is its multipurpose functionality that renders dotDefender web application firewall capable of succeeding in the computing world (Malekar and Waghmare, 2013). Additionally, most of the rootkit detection tools such as Sophos Ant-Rootkit, GMER and Trend Micro Rootkit Buster are less likely to succeed in the modern world of computing. This is because they are engineered to prevent specific types of rootkits but not all. This renders them inefficient in providing absolute security to the computer systems. Additionally, the world of computing is dynamic. Hackers may come up with special rootkits that masquerade as rootkit removers and end up rendering them obsolete.
cyber-crimes
Have you ever been affected by cyber-crimes?
Malleficent

Recommendation
Having noted the various security threats and vulnerabilities that exist in the world of computing, it is highly recommended that security analysts be on the front line of innovating new techniques and tools of fighting against these security threats. Additionally, this report recommends the use of more effective security tools such as the dotDefender web application firewall for the purpose of ensuring that their systems are secure. For Network administrators and Network security auditors, this report highly recommends the use of Ethereal. This is because Ethereal enables them to not only track other packet sniffing applications running over the internet but also enable them to view security issues in an angle that a hacker might use. This would give them the advantage of identifying the vulnerabilities that exist in their network systems and find the latest security patches that can eliminate these security flaws.







