- HubPages»
- Technology»
- Internet & the Web»
- Viruses, Spyware & Internet Security
Protecting Your Online Accounts from Hackers
Computer Hacker at Work

Computer Hacker Online
Protecting Your Online Accounts from Hackers
By: Steven Rich, MBA
Hackers are getting access to millions of online accounts and you need to know how to prevent them from getting into yours.
First of all, how do hackers get into people’s online accounts? Understanding how hackers hack is very important to be able to come up with ways to stop them.
Here’s a list of the methods hackers use to hack online accounts:
1. Keylogging (Using a program that logs every keystroke you make on your computer)
2. Phishing (Posing as a legitimate company and tricking an online account holder into revealing passwords or financial information)
3. Stealers (An internet attack which steals one’s account access by changing the password and proceeding to send out its own malicious emails from the victim’s account)
4. Sidejacking (Unauthorized identification credentials used to remotely hijack a web session in order to take control of a web server. Usually the sidejacker finds an unsecure socket layer (SSL) cookie.)
5. Session Hacking (Also known as TCP Session Hijacking, where the attack occurs during a user session in a protected network.) The hacker disguises him/herself as an authorized user.)
6. Mobile Phone Hacking (Gaining unauthorized access to one’s cellular phone)
7. Botnets (Where malware infects a network of interconnecting computers like in a work place)
8. Man in the Middle Attack (The attacker secretly gets in the middle of a two way communication to eavesdrop or relay false information)
9. DNS Spoofing (The hacker introduces data into a Domain Name System (DNS) cache causing the server to send an incorrect IP address which allows the diversion of all traffic to another computer like the hacker’s)
10. USB Hacking (Insert USB Flash Drive into a computer to steal all passwords or to take control of the computer with malware)
Scary stuff! Any one of the 10 can wreak havoc on your computer, cellular phone, smart phone, and your life.
Here are ways to protect you from hackers:
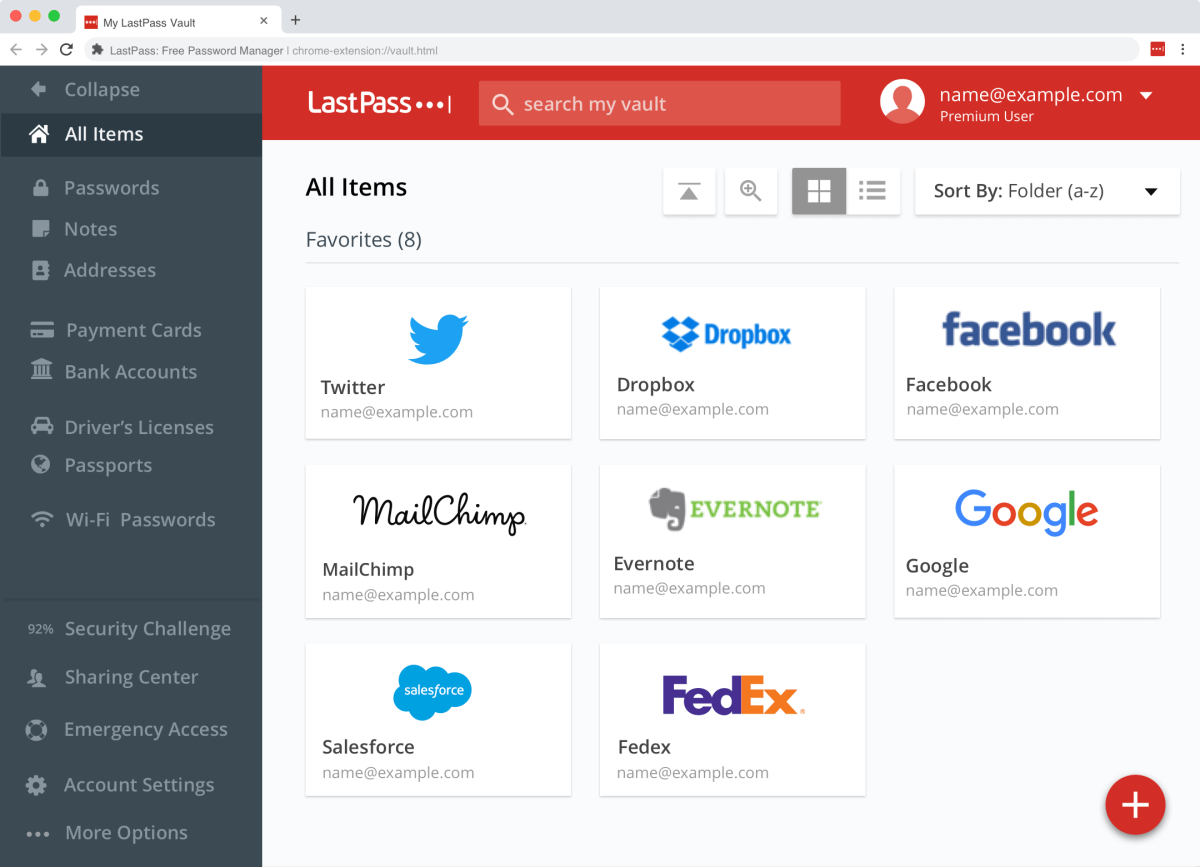
1. Change Your Password often. There are Password Manager Programs out there to help you to come up with difficult passwords and to keep you from forgetting what they are. LastPass is one where you can allow this program to sign in to all your online accounts. Then, you can access your passwords from any browser and device you use anywhere by accessing their online vault. Their Free version allows you
• Unlimited storage for passwords & notes
• Automatic backup & sync for your first device
• Automated filling of logins & forms
• Audit passwords with Security Challenge
• Multifactor authentication & One Time Passwords
2. Use a Firewall.
3. Avoid “Easy to Remember” Passwords (especially when using public access computers).
4. Only Use Strong Passwords, which are difficult to duplicate.
5. Be Careful When Approving Friend Requests as they might end up being hackers.
6. Activate Login Approvals so questions only you know the answers to will be posed before gaining access.
In Conclusion, there are many ways for hackers to hack into your computers and mobile devices. While there are no guarantees you can prevent access to hackers, at least there are ways to make it more difficult for them.
Steven Rich, MBA