The Entertainment Industry Has No Interest To Curb Piracy

What it is and how it works
The definition of a copyright infringement is as follows:
"Copyright infringement is the use of works under copyright, infringing the copyright holder's exclusive rights, such as the right to reproduce, distribute, display or perform the copyrighted work, or to make derivative works, without permission from the copyright holder, which is typically a publisher or other business representing or assigned by the work's creator." (Wikipedia)
In other words, whenever you choose to download or obtain a copy of the desired media without going through the proper channels, you are essentially involved in piracy. Of course, the world isn't black and white and neither is piracy. Should the same punishment be applied to the receiver of the content as well as the sender?
So how exactly does it work?
I mentioned earlier of the receiver and the sender and this is pretty much how it goes. First we have content that no one wants to pay for. This can consist of movies, video games, music, software, and so on. The sender of the content is generally the uploader. They will essentially send the content to the end user or receiver, the person that just wants a free copy of the works.
The next step is establishing the mode of transportation. In the real world, we have roads for cars and trucks, we have the sky for planes, and we have oceans for ships. However, in the digital world, the content must be stored somewhere. More specifically, the content are stored in only two possible places - third party servers and personal computers.
Storage on servers generally links to file hosting sites that make money by forcing users to watch a 30 second to 1 minute advertisement before continuing with the download. In essence, file hosting sites couldn't care less what files are being hosted as long as they make money.
The next solution would be on personal computers through the use of peer to peer networks, which consists of a collection of individuals that upload whatever they can to help the person downloading the specified file. The downloader of the file, in return, will upload the same file to the future downloader. This pretty much focuses on sustainability where as long as there is a network of individuals with the file, downloads will occur.
You can think of these two mediums as a centralized exchange for the former and a decentralized exchange for the latter.
The Megaupload.com Story
Before we go any further, I would like to share the Megaupload story. Megaupload was established in 2005 as a Hong-Kong based company specializing in large file hosting and sharing. It generated 82,764,913 unique visitors and over 1,000,000,000,000,000,000,000,000 page views. It became the 13th most visited site on the internet with its file storage hitting 25 petabytes.
It was shutdown in 2012 by the United States Department of Justice due to copyright infringement. Was this a good move? On one hand it did drastically remove a ton of pirated media from the internet, but on the other, it's not going to make much of a difference if there's no follow through. I will explain more on this later on.
Current Events
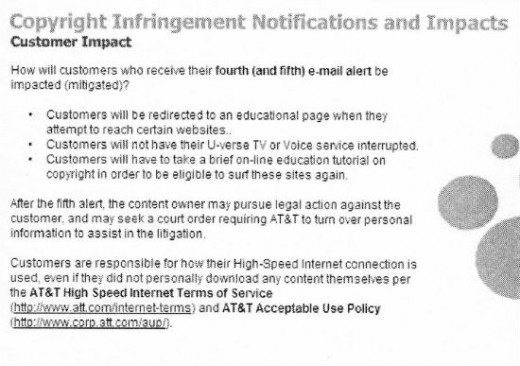
It looks like several organizations are cracking down on copyright infringements. Since last year, internet service providers (ISPs) have sent out warnings to their clients regarding their internet activity, specifically requesting the immediate termination of the distribution of copyrighted property. This is most notably movies and music, but can include other content as well. Last year, there was a 'six-strike' implementation where the offender will be given warnings to stop their current actions before they have to answer to the court of law. More information can be found here. In the event of a lawsuit, individuals can be fined to around $100,000 in the United States. However, this is a different story in Canada. The limit is only $1,500 to prevent against the abuse of the system. The purpose of lawsuits is to credit the rightful owners of their intellectual rather than to make money off of it.
The Bypass
I in no way encourage such activity, but I should downright state that it is not impossible to bypass such policy. It is technically still possible for downloaders to partially hide their activity through very cheap paid services.
There are many offshore solutions to handle large data downloads. By doing it offsite, it makes it significantly harder for outside prying eyes to see what you are up to. When it comes to sharing content, the file hosting server based and peer to peer network are by far the two biggest modes. More specifically, let's detail the services associated with the two.
When it comes to file hosting sites, there are just too many out there. When one site goes down, another one will just start right up again because these sites can be extremely profitable. While they do require huge start up server and storage costs, they earn it back quite quickly through advertisements. As mentioned earlier, file hosting sites will display advertisements in exchange for a free download. The other way is to sell premium membership which will bypass the advertisements and jump to the download directly. In any case, this is a win win situation for both the hosting company and pirates. The hosting companies seize the opportunity to rake in big bucks while pirates find a free solution to host their content and sometimes even work alongside the hosting companies in the revenue sharing. Some file hosting companies include DepositFiles, FileFactory, RapidShare, and Sendspace. These are just a few I pulled up from a quick search.
The other solution is the peer to peer file exchanging also known as torrenting. In order to not get side tracked, I will refer you to this article for those interested in learning more about torrents. For the average everyday user, torrenting will be done on a personal computer. However, if this is no longer possible due to a previous warning by your ISP, there is always the option of going offshore.
There are numerous virtual private server providers and dedicated seedboxes for this purpose. A virtual private server or VPS can be thought of as a remote computer that is turned on 24/7. One simply needs to run the torrent client, attach the torrent file, and will passively download and eventually upload (seed) the files to other users. If done correctly, there is pretty much no way to trace the connection back to you. More specifically, a seedbox is specifically designed for torrenting where, depending on the subscription package, the user has the option of attaching a certain number of torrents under a certain size limit to their account. Once again, their are several services, but two most known are Iwishost and DediSeedbox. I apologize for not going to in depth as to how these work as this article is to focus on what needs to be done and what is currently done to combat such an issue. However, I hope the attached video below will clarify the understanding of how torrents work without going into too much details.
Torrenting Explained
It's All About The Money!
The entertainment industry (movies, music...) is probably best known for handing out lawsuits to individuals requesting payment of hundreds of thousands of dollars to the illegal possession of intellectual property. Is this fair? There's no doubt that these companies should be reimbursed for their rightful property, but it's another issue when they hand out lawsuits as it becomes more profitable than to actually produce films. This can be seen with Voltage Pictures as they fired lawsuit after lawsuit for the award winning film 'The Hurt Locker'. Due to the over-piracy, the film's bestselling standing was at risk and, well, long story short, Voltage Pictures did something about it. However, in many cases, this is a band-aid solution at best. There is no point in trying to target the individual users as there will just be more where that came from.
The Real Solution
This process is actually much simpler than trying to trace IP-addresses to individual downloaders and sending out a warning before proceeding with a lawsuit. It's time for the production companies to work with the government and target the source. More actions like the ones against Megaupload are needed. When it comes to comparing file hosting sites and torrent directories with downloaders, there is no reason to target the more tedious crowd. Of course, gathering evidence against file hosting sites is no easy task, but I ask again, why? Why stick with the long and tedious approach?
Fileserve, a file hosting site, offered up this feature voluntarily in order to avoid being seized. This feature basically states that only the original uploader is allowed to download the files. In essence, it is still a file hosting site, but rather no longer a file sharing site. By implementing such a simple policy, especially when provided a government incentive, this will completely eliminate the option of using file hosting sites to share copyrighted property.
However, the decentralized peer to peer network is a lot harder to regulate. This can be seen through the bitcoin exchange. The government is finding that it makes more sense to regulate and control the exchange companies rather than the individual buyers and sellers. So why not bring this to the torrent network? Rather than cracking down on each individual torrent, working with domain hosts to crack down on torrent directories is a first. Of course, this introduces a whole new set of issues of U.S jurisdiction. This is why ThePirateBay is located in Sweden and the new Mega by Kim Dotcom is in New Zealand now.
At the end of the day, the entertainment industry is not taking the mentioned approach even though it is significantly easier to regulate a smaller body of people rather than the massive public. Why? Because as long as there's revenue, it's perfectly fine for them and they couldn't care less about combating piracy.








