Three Hacking Methods You Probably Didn't Know About
Actually, the post title might not really be suitable for the post but in one word, this post is to enlighten people about some security flaws that can make hackers get their very useful information.
A hacker is a person who seeks for unauthorized access to useful data and moreover they spend their time to seek for weakness in computer system and computer weakness.
Now, I will be giving three methods of how hackers uses web security flaw to attack you and I hope after reading this, you will know what to do:
1. Keylogger
2. Carding / Spamming
3. Click Jacking
Keylogger
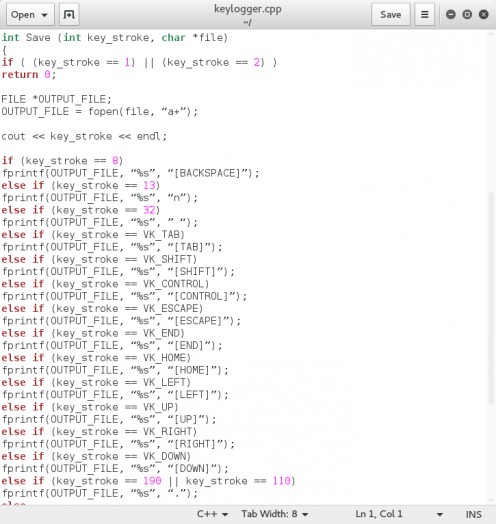
A keylogger is an example of a surveillance software but in most cases a SPYWARE that has the capability to store every keystroke you make to a log file. A keylogger can record Instant Messagess, Email and even any form of information typed at the time the keylogger is active time using your keyboard.
Some of us might be wondering that how is it possible to use keylogging method to get my details moreover it is a nice software.
Keylogger in most cases is used to hack because it takes in everything the user inputs. Therefore, it is an easy method for hackers to get your username / passwords, credit / debit cards, etc while typing it on the internet.
How to prevent Keylogging
1. The best way to prevent keylogger is to download a very active and working Anti-Virus on your system but yet that doesn't guarantee your safety.
2. Avoid installing of Applications with unknown sources and probably avoid files in SPAM messages.
3. Always take a smart checkup on your system to see what's wrong. If your browser pop-up too many tabs(I once experienced this on my Windows 7), you have been attacked probably not by a keylogger but by another serious hacking method which I won't talk about now. All you have to do is reset your browser and if that doesn't solve the problem, I advice you uninstall and probably install it back.
4. If you use old versions of Windows E.g Windows 8 or below, avoid using Internet Explorer (IE) to visit sites without an encrypted connection because some powerful scripts might take over your browser then they take over your system. In general, avoid website without a secured connected normally referred to as HTTP. Check if the connection is secured, you have something like HTTPs.
5. Browse Safely! Avoid unsolicited sites e.g adult sites, gambling sites with less useful information.
By now I think we all have been able to keep our cool and at least gained something. You don't know when a Keylogger works if you are not the one that initiate it. It works in background without giving any sign of notifications or so!
Carding

WHAT IS CARDING
Carding is the act of buying goods online without actually paying for it or using someone else credit card or money to pay for it without his/her prior knowledge. I don't know of now but eBay is suffering from carding and it does affect both the company and the seller. Carding is stealing!
In this case, hackers use security flaws to get your Credit/Debit Details and then they either sell it at cheap price or use it to request for goods and services online, I am not sure of what they do with it.
HOW DO THEY GET THE CARDS THEY USE
1. By attacking your bank, they can get your details.
2. Using the KEYLOGGER method.
3. Owners carelessness.
4. Browser Cookies: Like I said earlier, if you input your card details on a site without an Encrypted connection, well, I am telling you today that hackers can hijack the card details.
PREVENTION
This method might not be accurate because I have never been a victim of it before, possible prevention method are:
1. Avoid installing Apps with unknown sources be it on iOS, Windows, Mac OS, Linux.
2. Don't ever enter your Card Details on a site you are not sure of.
3. Beware of phishing and scam site and don't ever give your card details to anyone.
4. Disabling cookies might also works.
5. For android users, use your default keyboard apps, there are SOME keyboards that store users information / Cards. Avoid using them!
6. Avoid running GUI applications as privilege users. At least Linux has warned us severally.
I'd also suggest good VPN also and find companies that are capable of Card Encrypting, I won't mention one.
- What is Facebook ClickJacking? How to prevent it | Brainslodge
Clickjacking (User Interface redress attack, UI redress attack, UI redressing) is a malicious technique of tricking a Web user into clicking on something different from what the user perceives they are clicking on...
I guess we checked the link above to know more about Click Jacking. Meanwhile, if we didn't Clickjacking is making user click on something without the users intention. Sounds weird right? Clickjacking takes in user input and interpret it in another form. E.g When I click on more button in a site, I actually later found out that it was a Facebook Page I liked.
HOW TO PREVENT
1. Anti-Virus is required. I suggest Avast / McAfee
2. Visit websites with high quality and not sites with cheat or tweaks or whatever.
3. Always use incognito tab (if you can manage to)
4. Avoid using only one browser for all your social media account, it might get it compromised.
5. Use VPN, Hola VPN extension is available for Chrome and Firefox on PC and you can find others too.
Thanks!