The Importance of the People-Technology-Process Triangle in Proactively Mitigating Potential Privacy Threat Breaches
Business Privacy and Security
Although commonly believed to have been conceived by Bruce Schneider in the late 1990's, Mr. Schneider merely popularized a concept that has been a fundamental principle since around 1976. Others may argue that it began long before that. Despite its unclear origins, the People-Technology-process is a crucial element in the mitigation of potential breaches of institutional privacy.
The importance of the People-Technology-Process Triangle in proactively mitigating potential privacy threat breaches is a given for the successful operation of any organization. Naturally, access to sensitive information is needed by various individuals for numerous reasons. For instance, doctors need to access patient records. Therefore a level of trust and reliable security must be instilled within that process. Managing, or even understanding the ramifications associated with that trust poses a direct challenge for business owners, especially in light of the frequency of inherent threats of insider hospital privacy breaches.
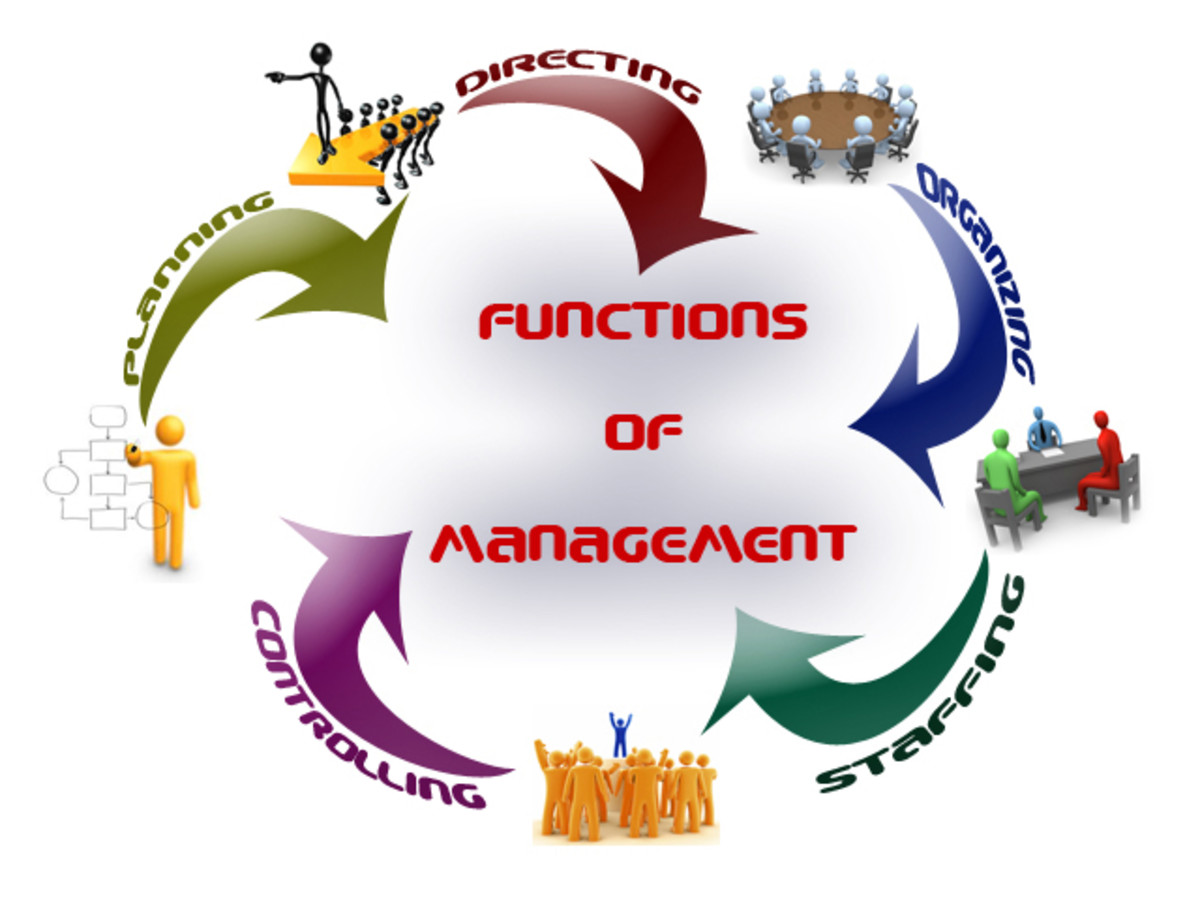
Traditional security principles include availability, integrity and confidentiality. However, true security exists as a combination of technology, people and process in equal strengths. When security breaches display potential vulnerabilities, strong processes are in order. However, without effective implementation, excellent technologies can be rendered ineffective. Additionally, human weaknesses can make technology less effective. The people-process-technology issue can be compared to a chair with four legs. If any one of the legs is broken or missing, it negatively effects the other three legs, rendering the chair useless.
Placing focus on technical security controls only, stands to leave the organization with insufficient people-power to maintain the overall system. Lack of human training programs results in poor policies and processes. In order to mitigate the potential for insider security breaches or threats the people, technology and process issues must be addressed simultaneously, as each element is as crucial as the other and should be implemented accordingly.