How to Block Malware Websites From Infecting Your Computer
Malicious software is also known as malware. Spyware can be similar but both have the affect of slowing down your computer or making your computer or operating system unusable without damaging any hardware or software. These sites can find ways to trick you into automatically download malware, spyware, adware, they can hijack your browser, or display popup ads that don’t go away.
Sometimes, you accidentally download malicious software, spyware without you knowing before it is too late. In this case, you may have bypassed the anti-virus software after thinking that the site is legitimate. How do you block malware websites?
There are many good products that can clean up Malware and Spyware after the fact. That means if your computer is already infected, these products can remove most if not all of them, as long as their malware database are updated. These databases will have a profile or some way of identifying what the malware looks like before it infects your computer.
In casual conversations with the average user, computer virus and other types of malware can be use interchangeably. Sometimes a virus can act like malware or malware can act like a virus. Malware won’t typically destroy hardware or critical software files.
Some products do a good job of shielding and removing Malware and Spyware. Sometimes some malware can get through. Hackers have found ways around the popup blockers and can defeat anti-virus software and firewalls.
There are ways to setup your computer to prevent specific malware from infecting your computer. The steps are moderately easy and may take a little research in locating the name or IP address of the website and editing the Window’s host file. But to make changes to the host file, you will administrator rights.
The first step is to find the list of known websites, especially the ones that keep getting forwarded to for some reason. Below are resources for finding rogue websites that can automatically download malicious software, hijack your browser, or display popup ads that don’t go away. You may find that they can run in the hundreds. This article will only demonstrate how to block two fake anti-virus websites: Windows Security Suite and Antivirus System Pro sites.
Editing the hosts file in Windows is one way to block any sites known to install adware, malware, hijackers, spyware, porn, and other nasty stuff. Hosts files maps IP addresses to host names before a DNS server performs the mapping. You can block access to a specific site before a connection is made to your computer.
In this example, if Windows Security Suite popup ad is causing you problems, find the site that is the source. Resources on the Antivirus System Pro site to block is included. For other malware sites to block, do a search within the same site. You must have the correct name of the malware. Many malware have similar names so it can be easy to confuse one malicious program with another.
Let’s assume you have administrative rights. In Windows’ My Computer or Windows Explorer, go to the “etc” folder depending on your version of Windows:
Windows 7 = C:\WINDOWS\systems32\drivers\etc
Windows Vista = C:\WINDOWS\systems32\drivers\etc
Windows XP = C:\WINDOWS\ systems32\drivers\etc
Windows 2K = C:\WINNT\ systems32\drivers\etc
In the etc folder, you will see the Hosts file. Before you make any changes, make a copy of Hosts within the same folder. For example, copy and paste the file, Hosts. You can call it “copy of Hosts”.
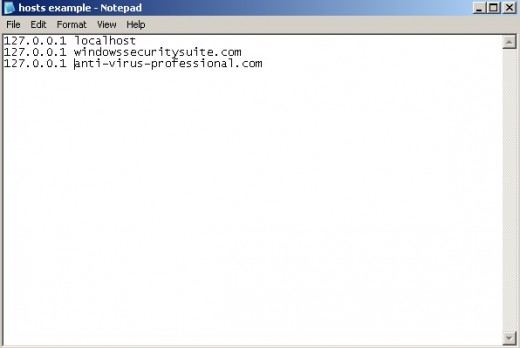
Double click on Hosts. Windows will not know which program to use to open Hosts. Hosts is a text file so any text editor can be used to open the file. If you see the “Open With” window popup, select the program “Notepad”. See Figure 1 – Example of Hosts File.
After the line that says “127.0.0.1 localhost”, add another line that says “127.0.0.1” a space and the name of the website. Don’t add “http”. Continue to add more sites to block in the same manner. Shown is an example.
After you have completed the list, save the hosts file.
One way to see if it the changes works is if the a website (legitimate or suspect) takes you to one of these rogue website. You should see a blank webpage instead.
If you computer is infected with a rogue software run your anti-malware or anti-spyware software to remove the offending application.
Resources for Identifying Rogue Websites
- Major Geeks
... Download freeware and shareware software utilities. Download files for your computer that tweak, repair, enhance, protect ... - 2 Spyware
Spyware news, discussions, Antispyware reviews, Corrupt Antispyware list, list of harmful files and manual removal instructions of various spyware parasites can be found on site. - Spyware Void
Remove spyware, adware. Spyware Threat Removal and other Spyware Resources. Detect Malware, Delete Rogue Antispyware, Get Rid Of Spyware, Adware & other Malware.