The Art of Phishing



Phishing is an attempt to steal someone’s sensitive personal information such as usernames, Social Security numbers, passwords and credit card data. Those who do it are nothing more than cybercriminals. Phishing e mail messages, websites, and phone calls are designed to steal money. Sometimes they go directly for the pocket book by disguising themselves as a legitimate business website.
The term comes from the word fishing as, in what an angler catching a fish does. But in this case, “The big one” really does get away sometimes. That’s because more and more, people are learning how to recognize the threat.
However, despite attempts to educate the public and browsers having anti-phishing technology, some are still getting stung. Like all security measures in cyberspace, as soon as one is put in place, someone will find a way to circumvent it. So, how do you protect yourself? You have to learn to recognize what their illegal ploys look and sound like.
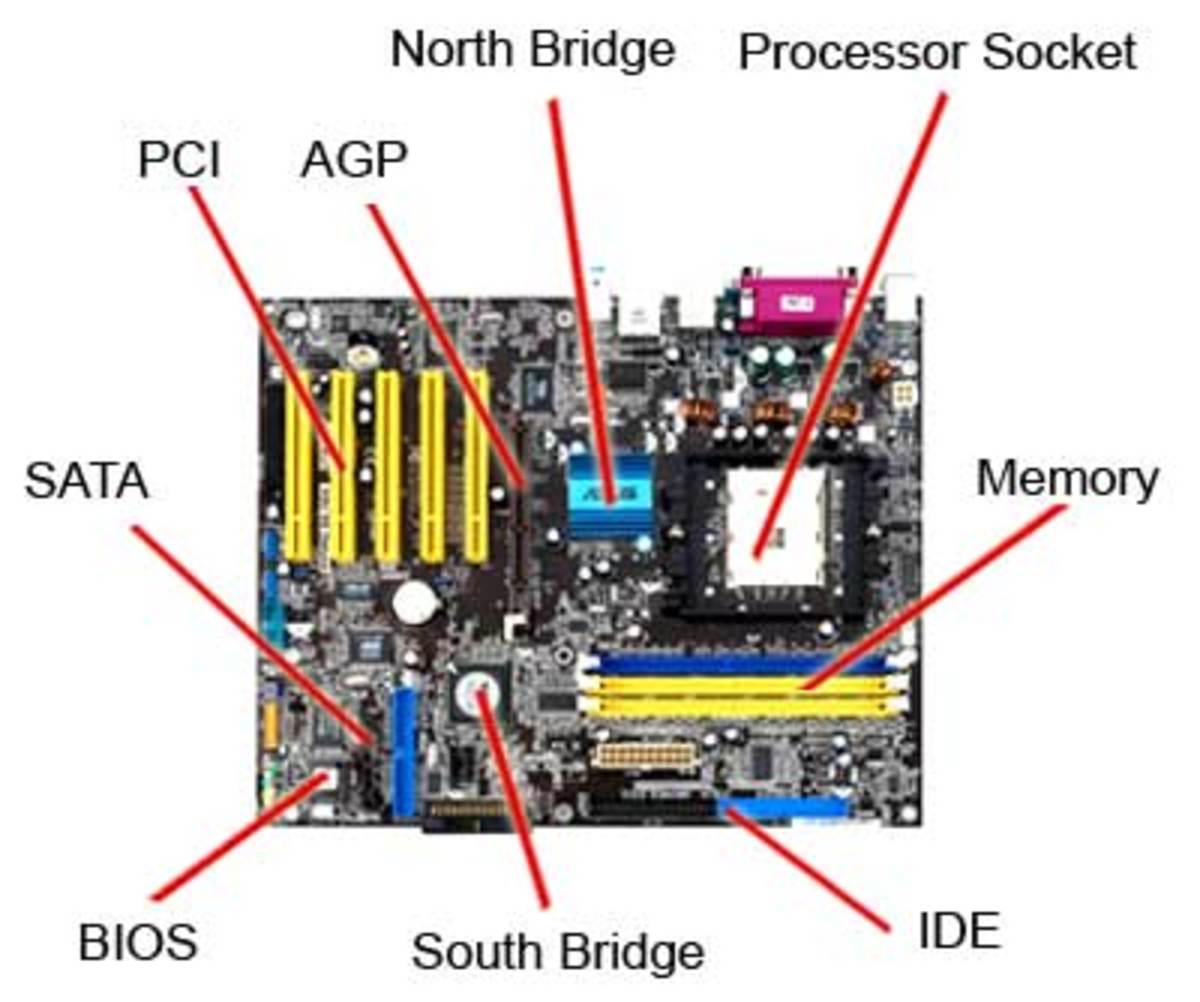
They might contact you by e mail or phone call trying to persuade you to download something off of a website. The danger of doing that lies in the simple fact malicious software from that site can easily be installed on your computer, capable of getting personal information off of your computer. No doubt you’ve heard of identity theft. These are some methods used to accomplish it. While it’s impossible to entirely control whether you will become a victim of identity theft, there are measures to take to minimize the risk.
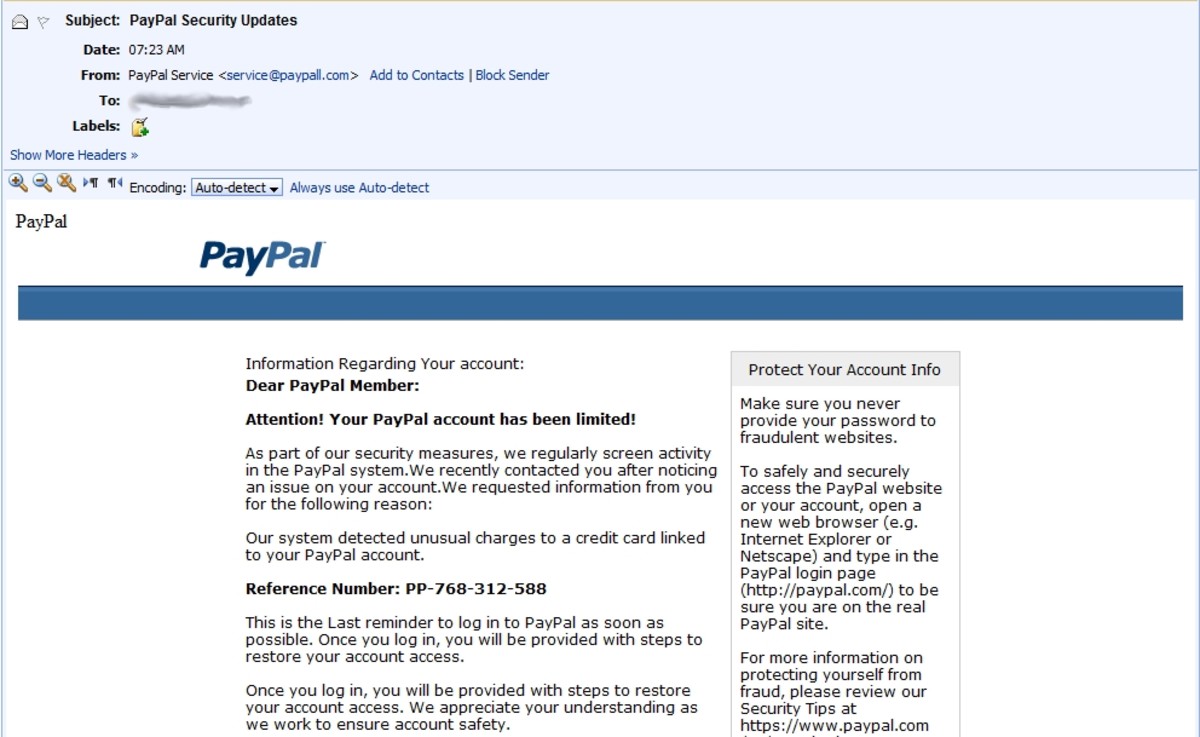
What does a phishing e mail message look like? Often, one can be recognized by bad spelling and grammatical errors. Cybercriminals are not known as being proficient in these areas. Legitimate businesses have professional copy editors that are. If you notice mistakes in an e mail, it’s best to just delete it.

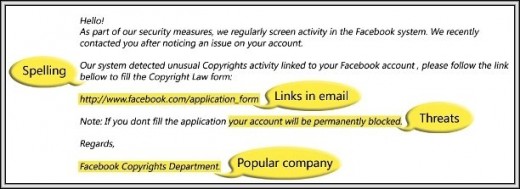
But, if you’re still not convinced, look at any links in it. Hold your mouse over a link. The address should appear somewhere at the bottom of your screen. See if it matches as in the example provided above. It doesn’t. Links might also lead you to .exe files, known to spread malicious software.
Here are two examples of what a fraudulent e mail might look like: “We suspect unauthorized transactions have occurred on your account. To ensure your account has not been compromised, please click the link below to confirm your identity.” And, “During our regular account verifications, your account couldn’t be verified. Please click on the link to update and verify your information.” They may claim to be from a bank, payment service like PayPal or even a government agency. In any case you are urged to “update,” “validate,” or “confirm” your account information.
Cybercriminals frequently incorporate threats in their e mail informing you your e mail account has been compromised. They will tell you if you don’t contact them to remedy the situation, your account will be closed. Be wary of these fake alerts. Other scam artists may use slightly altered web addresses, graphics and well known business logos that appear to be connected to a legitimate website. In reality, they more than likely lead to a phony scam site.

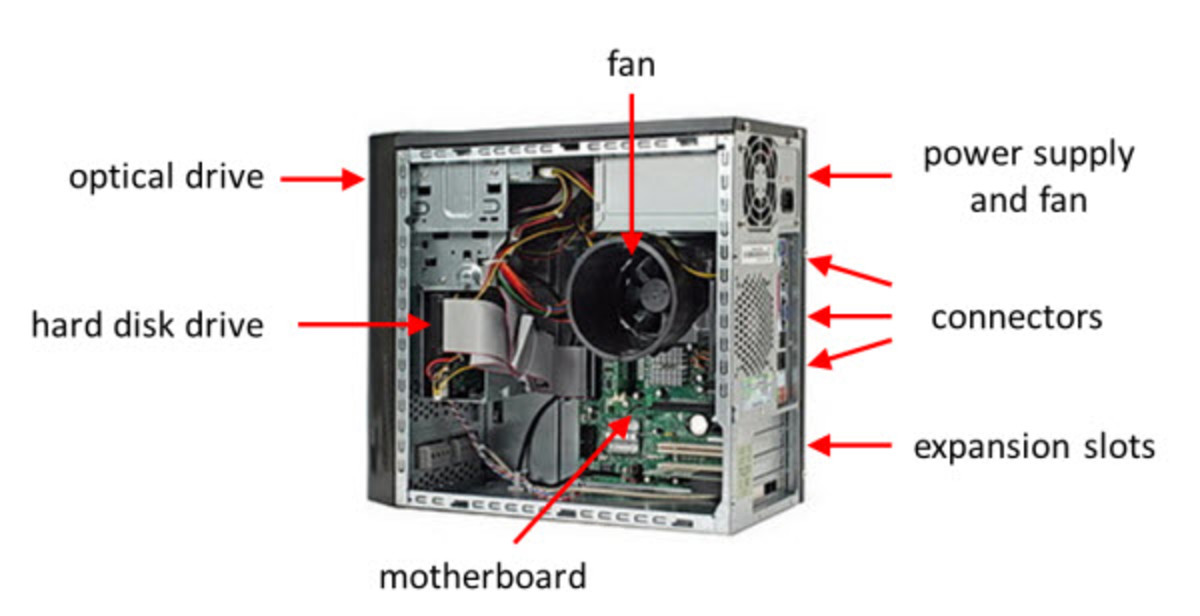
You might get a phone call offering to solve your computer problems, sell you a software license, or any number of services. You might be asked for your user name and password then instructed to go to their website in order to download software that will allow them to access your computer to let them fix it. This type of software is available, but not sold in this manner. The truth is, a reputable, legitimate business like Microsoft does not engage in this type of activity. If you receive such a call or e mail, get the caller's or sender’s information and report it to local authorities. Or Microsoft and others have tools to report suspected scams.
There are other times people accidently type the wrong Internet address into their web browser and end up on a fraudulent website. If this happens, you might be conned into giving personal information or downloading malicious software onto your computer. This is usually referred to as "cyber squatting."
The Federal Trade Commission, the nation’s consumer protection agency, has issued some tips to avoid becoming another statistic:
· If you get an e mail or pop-up message asking for personal or financial information, do not reply or click on the link in the message. Legitimate companies don’t request this kind of information by e mail. If you are concerned about it, contact the organization using a telephone number you know to be correct, or open a new window and type in the company’s correct Web address. Don’t cut and paste the link. Cyber crooks can make authentic looking links, but actually send you to fraudulent site.
· Telephone area codes in e mails can be misleading. Scammers, seemingly from legitimate businesses, will ask you to call a number to update an account or access a refund. Because they use Voice over Internet Protocol technology, the area code doesn’t necessarily reflect their correct location. Preferably, to reach an organization you do business with, use the number provided on financial statements or credit card.
· Use anti-virus and anti-spyware software, in addition to a firewall, and keep them updated.
· Remember, e mail is not a secure method of transmitting any information. If you want to provide your personal or financial information through an organization’s website, look for indicators the site is secure, like a lock icon on the status bar or a URL for that begins “https:” The “s” stands for “secure.” Unfortunately, no indicator is 100% foolproof. Security icons have been discovered to be forged.
· Review credit card and bank account statements as soon as you receive them to check for unauthorized charges. If it’s received several days later than normal, call to confirm the billing address and account balances.
· Be wary of opening any attachments or downloading any files you receive by e mail, no matter who they’re from. They can still contain viruses or other harmful software.
For other ways to avoid cyber scams visit: ftc.gov/spam.