The Intersection of Home Security and IT Security
Introduction
IT security and home security are no longer two separate worlds. As our social lives move online and our gadgets gain the ability to snoop on us, our privacy and our safety is increasingly dependent on managing the intersection of home security and IT security. What can you do to improve your personal security, privacy and personal information?

Behavior and Security
Never blindly accept help from someone who calls you out of the blue and says they are from the cable company, your internet service provider, phone company or web hosting company. Do not take the word of someone who calls you without a prior help desk request and asks you to visit a website or run software on your computer.
Do not give your user account login information and password to someone calling claiming to be from a telecommunications company or home security monitoring service. Those legitimately working on the help desk for these locations either have the ability to reset your password or access your account information without any action on your part.
Privacy and security go hand in hand. Do not post information on social media sites discussing when you will be on vacation. Thieves tend to be young and increasingly computer savvy. Telling them when you will be away tells them the best time to invade your home. You can post all the pictures and stories you want after you've returned home.
There are many jokes about the use of safe words. If you are going abroad, leave a safe word with family members that indicate that you are in danger and another one to confirm your identity. If you call and use the word that indicates danger, they should call police in the area where you are located and probably the embassy. If they receive a text message or voice mail that seems to be from you requesting money and it does not include the safe word to confirm your identity, they know not to send anything.
Do not let visitors, whether they are your family members or friends of your teenagers, use your computer without restriction or supervision. They could accidentally download malicious software onto your computer, deliberately download illegal files to your computer that they cannot access at home or choose to install monitoring software on your computer in the hopes of gathering information. Whether it is a teenager who wants to snoop on a friend's activity or an in-law concerned that you are having an affair, letting someone use your computer with full privileges is an invitation to disaster. You improve your privacy and security by limiting access to your computer.
Verify that everyone in your family old enough to handle visitors knows your utility service provider, ISP, phone service provider and local law enforcement. Children too young to ask whether an officer has a warrant to enter the home should not open the door to someone dressed in a uniform that imitates that of law enforcement. Would-be thieves often dress as utility workmen to scout out the inside and outside of your home. They may even cut off phone service or disable the home security system pretending to be responding to a system generated error while saying they were dispatched to fix it.
Review the data volume on your cell phone bill and that of any child in your household. Extremely high data volumes may represent a gaming addiction or indicate that someone has installed monitoring software on the device. The monitoring software may take pictures periodically or transmit everything it hears to a third party listener.
If you own a means of personal defense like a gun, know how to use it properly. And do not brag about owning the gun online, since this makes your home a target of thieves who want one.

IT Security and Your Kids
Keep very young kids off the internet. Young children do not understand that what they post is online forever, visible to almost anyone in the world and can be dangerous to share.
Your seven year old does not need to be on Facebook to make friends. And their search to find a website they heard about could land them on a mal-ware infected site or worse.
Inform any children under 18 that you have the right to review the files, logs and information on their computers at any time, including school owned computers they bring home. Then do so periodically. If your teenager is bullying others online, your child could be expelled from school while you, as the parent, could be held liable if the other child tries to commit suicide. Parents have the right to search a child's room for illegal drugs or guns. They have the same right to search gadgets for sexting, cyber-bullying, a crime in some jurisdictions and punishable by an increasing number of schools, and file sharing, illegal and sometimes a financial challenge for parents to resolve.
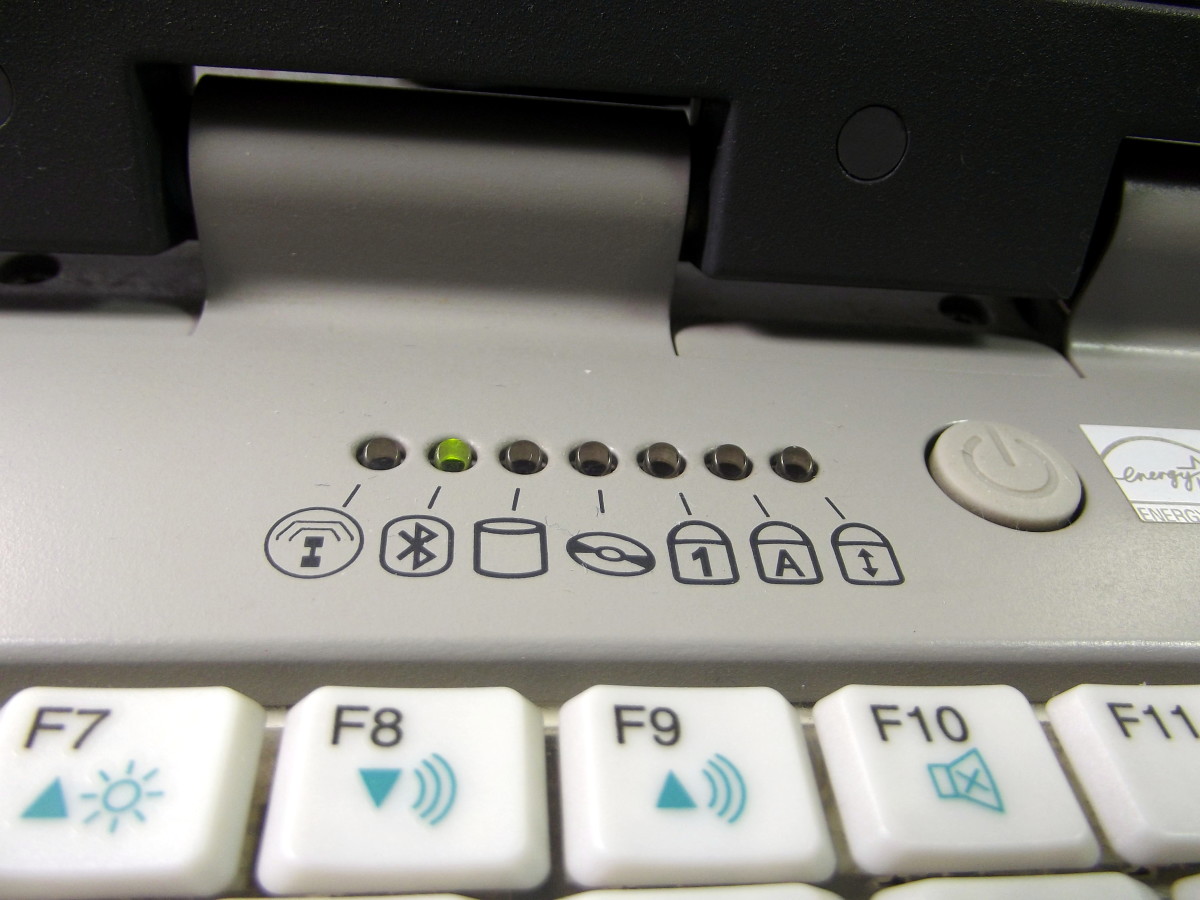
Replicate the IT security policy your network admin at work has onto your personal computer. Set up a limited profile for your children that prevents them from downloading software or installing anything or viewing financial software application information. Set up an adult account with most permissions except administrative rights. Set up an administrative account for the installation of software, since this will block many malicious software application installations. Use different login IDs and passwords for each account.