What is IP Telephony?
Defining IP Telephony and VoIP
"VoIP is a generic term for using IP data networks like the public Internet to transmit voice traffic" (ShoreTel, 2005, p.3). Early Voice over Internet Protocol (VoIP) systems required the user's PCs to be equipped with sound capability and a software application to convert speech to digital packets suitable for transmission using TCP/IP as the transport mechanism. The disadvantages of these early systems were poor voice quality and system incompatibility. Both parties of a conversation needed to use the same software application.
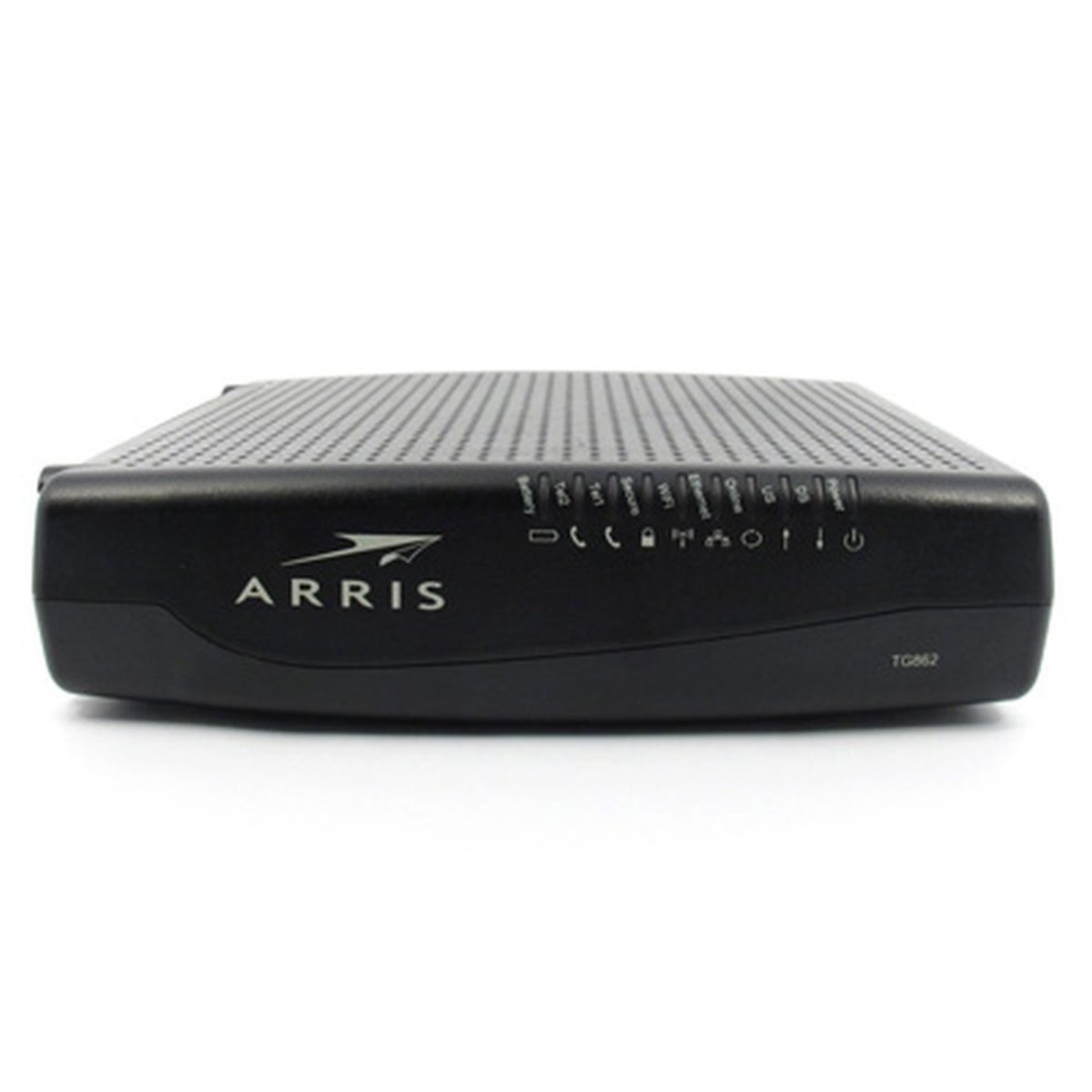
VoIP has evolved and the sound quality is now acceptable for commercial applications. Service providers like Vonage offer VoIP services to subscribers for a reasonable price. (Vonage Marketing, Inc., 2007). These services permit subscribers to initiate an unlimited number of long-distance phone calls for a set monthly fee. The Analog-to-Digital (AD) conversion occurs at the customer's premise and the packets are transported over the provider's private network using the TCP/IP protocol. When the receiver of a VoIP call is also a subscriber to a VoIP service the call is transmitted digitally end-to-end. When the receiver of a call is not a VoIP subscriber, the call goes through a Digital-to-Analog (DA) conversion process to convert the call back to a voice transmission suitable for a Plain Old Telephone Service (POTS) subscriber. Most residential non-digital phone services use the POTS infrastructure. The DA conversion takes place at the egress-port of the provider's network located at a Point-of-Presence (PoP) where the call integrates with the Public Switched Telephone Network (PSTN).
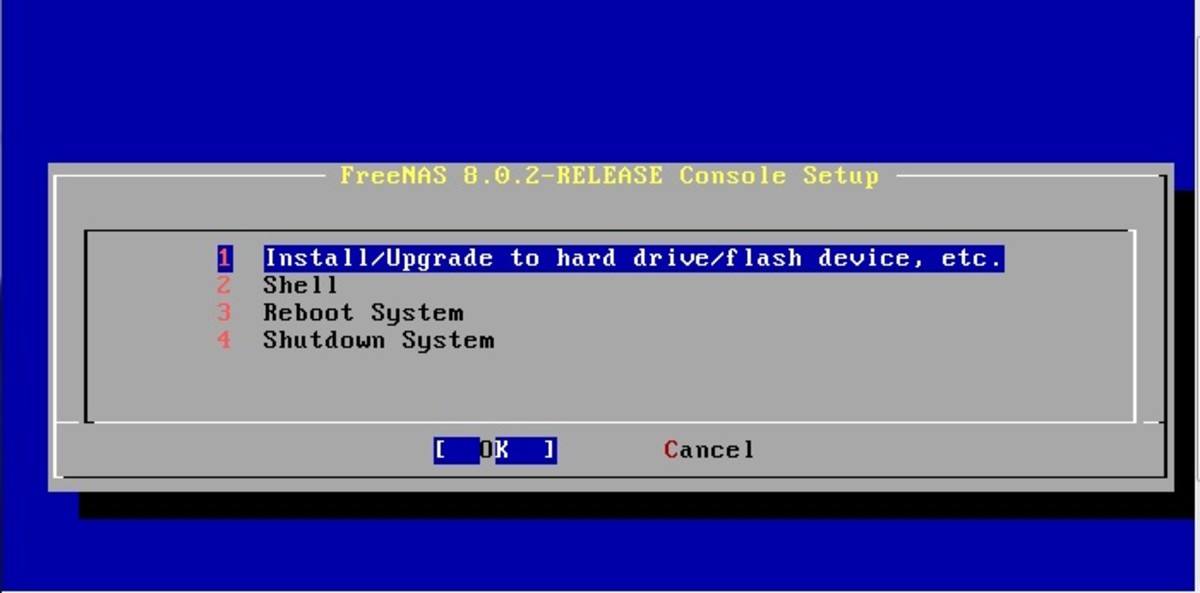
VoIP leverages a reduction in long-distance charges, whereas IP Telephony (IPT) "uses a private IP network for voice calls, not the public Internet. IPT provides organizations with the ability to leverage their existing private IP data networks to transport voice traffic" (ShoreTel, 2005, p.3). The principles of digitizing conversations are the same but the premise equipment is different for IPT compared to VoIP. IPT requires the addition of phone switches and a voice server to an existing Ethernet network. The phone switches control the connections between individual phone handsets and the outside PSTN network or between two or more internal handsets for calls within an organization. The voice server is a file server loaded with software configured for phone operations like voice-mail and control functions like auto-attendant and handset assignment.
Network Requirements of IP Telephony
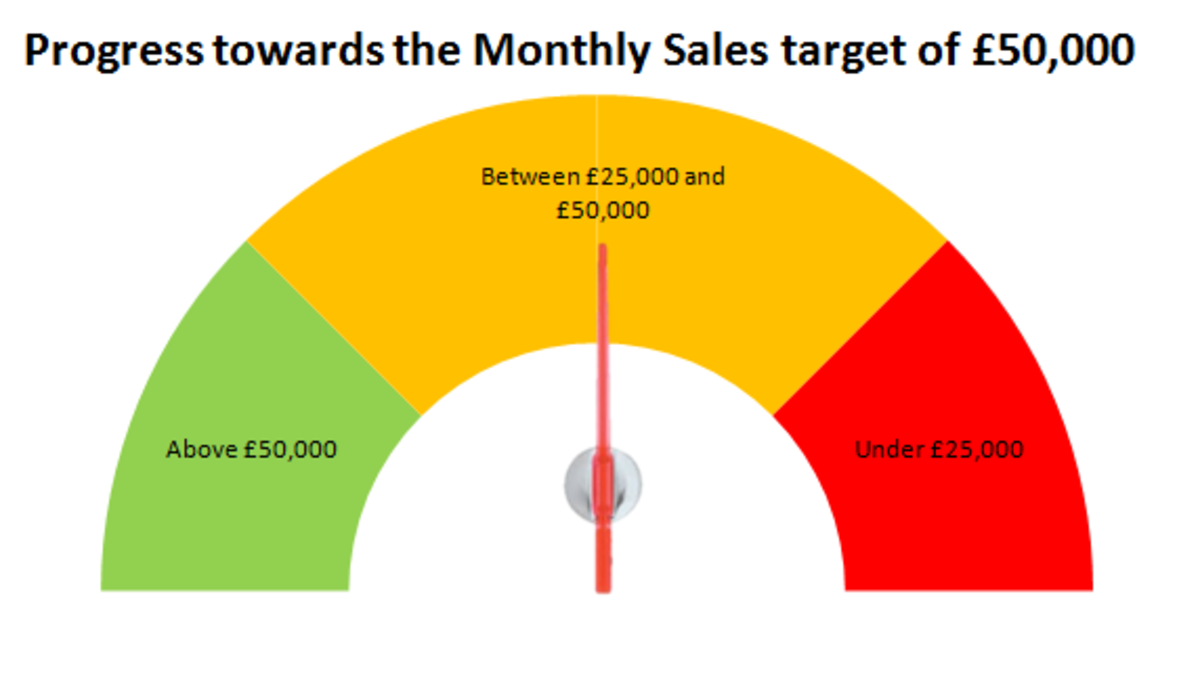
The two main requirements for IPT are enough bandwidth to handle call volume and acceptable latency times. According to ShoreTel (2005), on Local Area Network (LAN) circuits with high bandwidth availability 82Kbps may be used. Low bandwidth Wide Area Network (WAN) connections may only take up 28Kbps. Latency is the time from mouth to ear.
- It is the time it takes for a person's voice to be sampled, packetized, sent over the IP network, de-packetized and replayed to the other person. Distance alone on the WAN circuit can cause delay, as can lower-speed WAN circuits. If latency is too high, it interrupts the natural conversation flow, causing the two parties to confuse latency for pauses in speech. Latency must not exceed 100 milliseconds (ms) one way for toll-quality voice and must not exceed 150 ms one way for acceptable quality voice. (ShoreTel, 2005, pp.3-4).
According to McIntire (2002), getting good quality of service from VoIP is the greatest challenge because data networks were not intended for, or designed to meet, the constant steadystream demand that VoIP conversations require.
References
ShoreTel, Inc., (2005). Is your network ready for IP telephony? Available from
McIntire, T. (2002). Networking trends: consolidating your school network.
techLearning. Available from
Vonage Marketing, Inc. (2007). Simple to set up. Simple to save. Available from