What is a VPN? [ Virtual Private Network]
Well, its time to know what VPN is.
In simple words, a virtual private network (vpn) is a technology that creates a more secure encrypted connection over a relatively less secure and malicious connection. It enables the users to send and receive the data over internet as if your device's network is directly connected to the private network which doesn't share its information. Advantage is that VPN ensures the security of the user at instance where the network the user normally uses fails to do so. In real world, vpn is extensively used by the companies, where they provide a private network to their employees such as company's private working network.
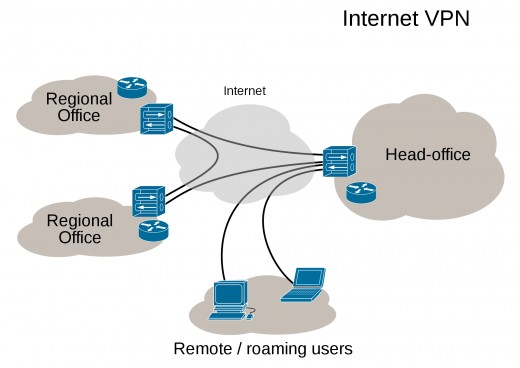
You may even think of using a simple private network instead of VPN. Well, VPN is relatively very feasible in many cases and even in the cost point of view, it is very economical. Usually there two kinds of VPN networks that are actually in practice. They are remote-access VPN and site-to-site VPN.
- Remote access VPN : Remote access VPN requires a basic telecommunication medium (like internet ) to provide a secure gateway between the remote users device and the organization. The basic requirement is that the remote users device must authenticate the private network ( its identity ) so as to provide a internal link to the organization the remote user trying to link up with (via internet ). A remote-access VPN usually relies on either IPsec or SSL to secure the connection.
- Site-to-site VPN : A site-to-site VPN uses a gateway device to connect the entire network in one location to the network in another, usually a small branch connecting to a data center. End-node devices in the remote location do not need VPN clients because the gateway handles the connection. Most site-to-site VPNs connecting over the Internet use IPsec.
Even the use of VPN is more when it comes to the matter of security between specific computers and privately working devices. VPN always stays in the protocol trying to provide a secure cloud-based connection between user and the service providing unit.
Guidelines to set up your own VPN :
- Implement DHCP services
- Create an enterprise certificate authority.
- Install IAS
- Configure IAS
- Create a remote access policy
- Configure the VPN server
- Link up the VPN server with DHCP server
- Configuring the remote clients
- Test the client connection
Better still, VPN technology is Exchange-independent. This means your remote users can use your VPN connection to access Exchange Server regardless of the version, and can also access other network resources.
Introduction of VPN's in mobile platforms :
Method implementation of VPN is somewhat different in the mobile platform. Mobile Virtual private networks are used in settings where an endpoint of the VPN is not fixed to a single IP address, but instead roams across various networks such as data networks from cellular carriers or between multiple Wi-Fi access points. Thing is that, the use of VPN's in the mobile platforms is increasing wildly as the tech-professionals are in the need of more reliable and secure networks.
Limitations of a VPN :
One major limitation is the orthodox VPN network is that it is based on the principle of point to point i.e they do not support broadcast domains. That means software, communication and network and are not fully functional to the limits of VPN as it cannot provide a secure gateway for them when the remote user is accessing them.