How Prepared is Your Business to Face a Botnet Attack (Being Hacked)?

How Prepared is Your Business to Face a BOTNET Attack
The business world is fraught with challenges and besides going head-long with and trying to beat your competition, one key thing business owners should do is put measures in place to protect their business from attack.
Hackers exist everywhere and will hit a business if conscious effort isn't made to guard against this.
Cyber security and Your Business Safety
Business online, more than ever, have to put measures in place to protect themselves from hackers as an attack to your system or website can harm your business in more ways than one.
Besides getting access to your business data for exploitation purposes, a few other dangers these hackers perpetrate include holding your data ransom, converting your data for personal use and gains, denying you access to your services and stealing and selling information or infrastructure.
While every kind of cyber attack comes with its sets of dangers, one of the worse kinds of online business attacks ever is the botnet attack.
A botnet is a large network of computers that have been infected with malware and are being controlled remotely. The way this works, the botmaster (hacker), creates a malware through which he can remotely control a host computer. He then gets thousands of people to unwittingly install this malware on their systems.
The botmaster is able to accomplish this by disguising the malware as harmless. Most times, these malware are disguised as email documents, software programmes or pop-up ads.
Once the malware is successfully installed, the host master gets a notification to this effect and proceeds to remotely control the system.
This botnet attack is bad in the sense that it it is not just an attack o your system, but is an attack to several hundreds or even thousands of systems, creating a kind of damaging network.
Some of the ways the botmaster controls these infected systems now in his network include:
- Sending bulk spam messages to the system.
- Serving personal ads to the computers on the network.
- Generating several hundred thousands of web traffic using the systems in his network.
- Demanding a ransom from the victim to be removed from the network.
- Access to these systems can also be rented out or sold by the botmaster to other hackers
A botnet attack is bad for a business in that too many hits can hit it hard, making it go offline.

How to Protect Your Business from a Botnet Attack
Since these botmasters are relentless and sneaky, business have to also stay on top of their game to avoid getting infected with a botnet.
Some proven ways to avoid a botnet attack include:
1. Keep Your Antivirus Up-to-Date
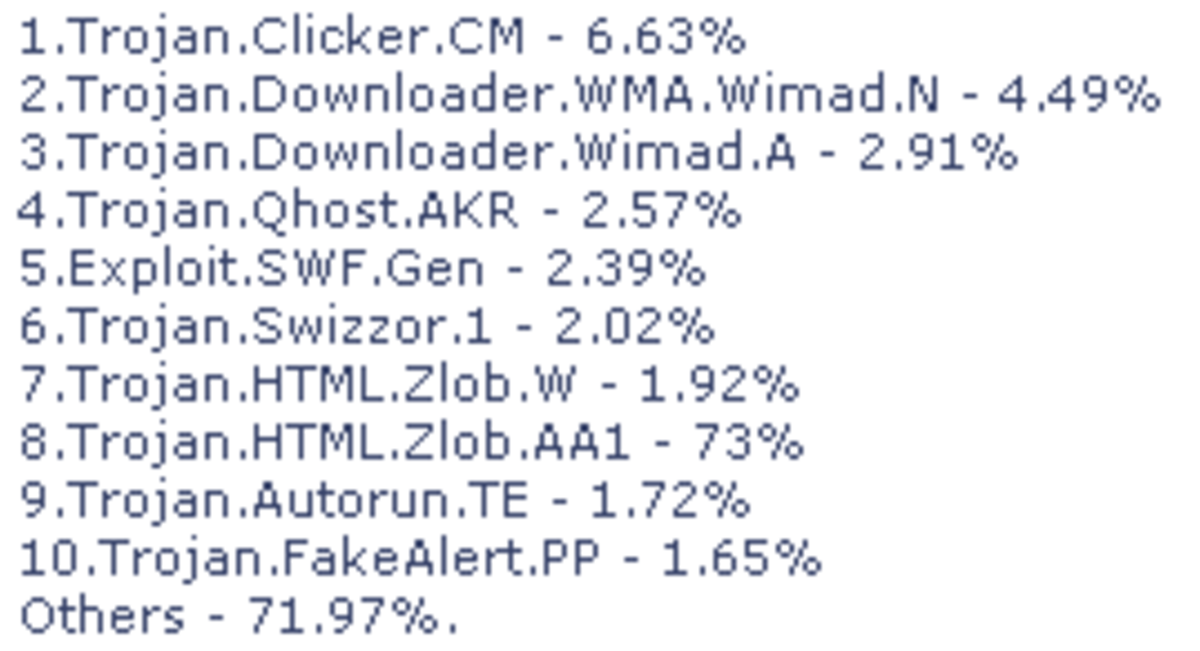
Several hundred viruses are being created by hackers daily and business owners have to be on their toes to ensure their antivirus is current enough to detect these malware.
A good way to do this is to ensure you keep your antivirus up to update.
Also, since most virus attacks go undetected, you should run regular antivirus scan to ensure your system is clean.
2. Desist from Opening Email Attachments from Unknown Sources
Since one of the commonest ways these malware get introduced to systems is via email attachments. You want to make sure you only open emails of people known to you.
You should also avoid ads and pop-ups from unknown ad networks as these could also be malware disguised otherwise.
Also, you should know a malware might also come from a known source. Once a system gets infected with a botnet, any email sent out from such a system could be infected with a maleware. This is done remotely by the botmaster, with the system owner being unaware of this.
At such times, this is when having a strong antivirus comes in handy as it will detect and delete the malware before it gets installed.
Understanding Botnet
A botnet is a large network o computers that have been infected with a created malware and are being controlled remotely.

3. Keep Your Operating System Up-to-Date
An outdated operating system is bad for your computer and your system. Besides slowing the system down, one other way it affects a system is making it vulnerable to attacks.
You should update softwares on your system once a month or as often as newer versions come out and update your operating system often to secure your system an business from hackers.
4. Some Websites Will Harm Your System
There are a number of websites created solely to distribute malware to unsuspecting systems. These websites most times disguise as freebies websites and would attach the malware to the freebies while downloading.
You want o avoid such websites at all cost. However, if you must download such free gifts, ensure you have an antivirus that is powerful enough to detect and delete the attached viruses before they can get installed on your system.
Some good antivirus you should check out include Bit defender, TotalAV, Malwarebytes and Norton.
5. Train Your Staff
Knowing about botnets and their damaging effect is great, especially if you put all measures in place to ensure your system is protected. However, if you run an organization and your employees remain in the dark about this malware, you run the exact same risk you would have if you were uninformed.
You should avoid this by bringing everyone up to speed about this virus, its effects and how to prevent it, that way you are protected from a attack from every corner.
This content is accurate and true to the best of the author’s knowledge and is not meant to substitute for formal and individualized advice from a qualified professional.
© 2020 Farrah Young