How to Implement Lean IT
Why Would Lean Management Principles Apply to IT?
Bureaucracy is often grows by default unless actively pruned. When resources (money, time, material) become more valuable due to shortages, scarcity or demand, managers often fall back to the mentality of a rationing scheme over efforts to improve productivity and profits.
Rationing means that the shortage is solved by keeping the same number or even more managers to supervise and ration resources. However, this is the opposite of a lean process - and explains why lean management is essential.
The same concept applies to IT. It is common practice to solve a mistake by adding another signature, another approval step to the workflow or another loop to the flow chart. The simple process thus becomes complex. The solution for solving a changing set of requirements is piling new requirements onto an existing process, adding more delays and complexity. This is why lean management techniques can be applied to IT.
How Can You Apply Lean Management Principles to Create Lean IT?
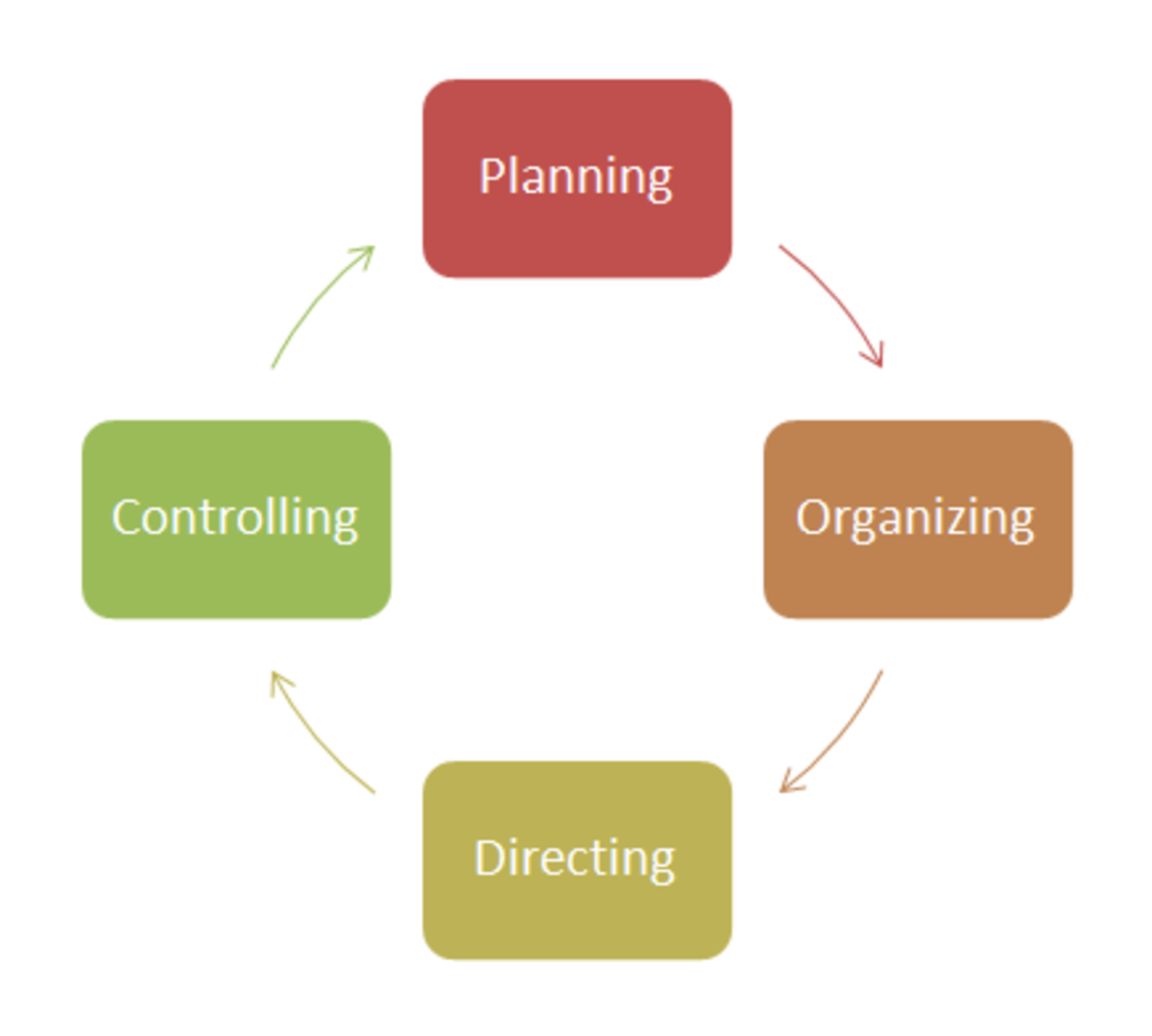
Create a standardized, simplified process for requesting new hardware. Use online forms with automatic generation of assignments to approve requests and assignments for hardware upgrades once the upgrades and installations are approved.
Use a standard process for new user account requests and access requests. Develop a rules matrix for determining who can be granted types of access and who can approve this access.
Plan on having exceptions, and then create a simple process for handling exceptions. If you are upgrading everyone to a new operating system and someone cannot upgrade because they have software that does not yet work on that system, they will need an exception to the OS upgrade process. Have a standard way to handle exceptions with as few decision loops and approvals that are necessary. You can add a loop-back to follow up with the user in six months to find out if an upgrade is now an option to avoid orphaned exceptions to the standard corporate process.
Use standardized software tools sets for users. You can simplify new user set ups by installing the same software on computers set up for new employees or transferred personnel or giving them the same set of applications through a virtual machine or Citrix thin client. The heart of Lean IS or lean information systems is having as few software applications as possible while using the same, controlled versions across the company.
Automate your software testing as much as possible and document the testing that is done manually. This lowers the headcount necessary that is required for testing. Then use standard criteria for identifying and assigning staff for testing to avoid delays finding people to do testing.
Maintain tight configuration management standards on your hardware and software. Require management approvals to make changes, but have multiple people capable of giving approval so that fixes and upgrades are not left in limbo because the necessary signatory is on vacation.
Document the logic behind your access control limits, information security policies and verification criteria. Allow those who want to make changes to hardware, software or policies have access to this information so that they can determine if their fix violates the intentions of your original set up. Involve management if the current controls and configuration are a hindrance so that the new environment does not leave holes that create security or confidentiality problems.
Use a common digital location to store documentation, whether it is instructions on how to fix common problems or the subject matter expert list for different software applications. Then communicate this information so that everyone knows where this information is located. Set up a recurring task to keep these personnel lists, documents and processes up to date.
Eliminate back doors on the server and in software applications. Require users to go through the software graphical user interface (GUI) or command line interface. If there is a critical function not available through the general interface, add it to the GUI so that the access can be controlled and activity logs are generated.
Use the same naming convention for user IDs across all systems so that users forget fewer user credentials and your help desk has fewer accounts to unlock.
Prevent the silo-ing of data, ensuring that all information is stored and accessible in common data repositories or databases. You'll avoid redundant software tools, wasted time searching in the wrong place and unnecessary complexity in IT support.