What Is Meant By Digital Signature Certificate?

Definition
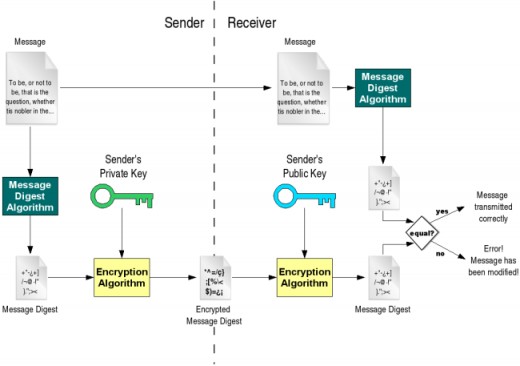
A digital certificate is an attachment to an electronic message used for security purposes. The most common use of a digital certificate is to verify that a user sending a message is who he or she claims to be, and to provide the receiver with the means to encode a reply.
It is issued by a certification authority (CA). It contains your name, a serial number, expiration dates, a copy of the certificate holder's public key (used for encrypting messages and digital signatures), and the digital signature of the certificate-issuing authority so that a recipient can verify that the certificate is real.
Each certificate comes with a public and private portion, called “keys.” The public key is what you share with the world to allow them to verify your electronic signature and to send you encrypted messages that only you can decrypt. The private key is what you use to sign and what you use to decrypt. Protecting the private key portion of your certificates is very important. The programs that use certificates will help ensure that you share only the public keys.

SIGNING
| ENCRYPTION
| |
|---|---|---|
Public key
| E mail address,
| Code used to
|
expiration date changes
| encrypt a message.
| |
to document since
| Only your private key
| |
certificate was attached
| can read that code
|
SIGNING
| ENCRYPTION
| |
|---|---|---|
PRIVATE KEY
| E mail address,
| code used to
|
expiration date
| read a message
| |
your personal
| encrypted with
| |
signature
| your public key.
|
Verifying the signed certificate....
The process of verifying the "signed certificate" is done by the recipient's software, which is typically the Web browser. The browser maintains an internal list of popular CAs and their public keys and uses the appropriate public key to decrypt the signature back into the digest. It then recomputes its own digest from the plain text in the certificate and compares the two. If both digests match, the integrity of the certificate is verified (it was not tampered with), and the public key in the certificate is assumed to be the valid public key of the subject.
At this point, the subject's identity and the certificate's integrity (no tampering) have been verified. The certificate is typically combined with a signed message or signed executable file, and the public key is used to verify the signatures digital . The subject's public key may also be used to provide a secure key exchange in order to have an encrypted two-way communications session .
Major Data Elements in an X.509 Certificate
- Version number of certificate format
- Serial number (unique number from CA)
- Certificate signature algorithm
- Issuer (name of CA)
- Valid-from/valid-to dates
- Subject (name of company or person certified)
- Subject's public key and algorithm
- Digital signature created with CA's private key
Necessity for Digital Certificates
- The primary use for certificates right now is with
e‐mail on Windows, Mac, and Linux computers.
File and folder encryption is available for
Windows users. Certificates do not enable file
folder encryption in Mac OS X. - Are you using e‐mail to send Category‐I data,
such as human‐subjects research data, donor,
legal, or health information to other faculty or
staff? Certificates let you encrypt that
information as long as both the sender and
receiver have certificates. - Are you using a laptop or other portable device
that has Category‐I data? Certificates can enable
security options required by UT System. - Are you using e‐mail to send student grades or
other information? Students are not
included in the Digital Certificates service right
now, so you won’t be able to encrypt messages
to them using the Digital Certificates. You may
want to think about secure options on UT Direct
that are built to handle student information. - Do you mostly use a mobile device to stay in
touch during the day? While you should be able
to read signed messages on your BlackBerry,
PDA, and almost any computer or Web‐based
mail program, some devices won’t let you install
certificates, so you may not be able to read - If you don’t have your certificate files on the
computer where you are reading e‐mail
messages, you will not be able to read
encrypted messages, nor send signed or
encrypted messages. If there is potential that
will spend the majority of your computer time
where you can’t install certificates, they may
provide limited value. - If you share a computer with someone else, talk
to your desktop support staff about whether
you should use certificates on that computer.
Backing up your certificates
It is important to have a backup copy of your signing and encryption files. A backup contains both your public and private keys, and it ensures that you can install the certificates on a new or rebuilt computer. Backups must be stored in a secure location to which only you have access.
You can ask your desktop support person to help you create a backup on WebSpace, CD, USB drive, or other media, but it would not be appropriate to ask that person to store the media for you. If you choose physical media, lock it up in a safe or cabinet to which only you have access. If you choose WebSpace, make sure you save the files in a folder that is not and will never be shared.