- HubPages»
- Education and Science»
- History & Archaeology»
- History of the Americas
American Countermeasures

“China is the Voldemort of U.S. military planning. For, just as the appellation of Harry Potter’s dreaded nemesis may not be uttered aloud, American strategists dare not speak China’s name lest terrifying consequences follow.” Dr. Toshi Yoshihara & Dr. James Holmes, United States Naval Institute
This Research Paper will strive to formulate theoretical solutions that will counter the Russia, China, North Korea and Iran Asymmetric Warfare threat to the United States, Israel, and Western Civilization as a whole. Training methodologies will be explored as well as strategic planning and tactical measures. In summation a conceptual plan of action will be implemented as Countermeasures to the Asymmetrical Warfare threat that opposes America and her allies.
1) Overview:
In the wake of World War II, we can discover documented irregular warfare engagements
throughout the planet Earth. Harsh locations such as Rwanda, Somalia, the Sudan, and Chechnya were just a few of the more notable arenas where massive carnage was accumulated. (1) Brother against brother civil war, ethnic and religious clashes are a minuscule example of the complex nature of Asymmetrical Warfare.
However arguably none more complicated than what can only be described as the tribal conflict which entangles the Palestinians, Syrians, and Israelis within the turbulent Middle East region; from a historical perspective with no foreknowledge of the blood feud that pitted the Gemayels, the Jumblatts, and the Asads clans against one another and it is difficult for Western Intelligence Communities to comprehend the nuances of the region. (2)
In essence, there is now what experts describe as microclimates where fluctuating configurations of geopolitical grandstanding and intense violence are the rule of the day. “Hot spots” such as Egypt, Libya, Syria, and Mali feed the international media with much to report as the bloodshed increases while the Western world watches and anticipates the effect such chaos will have on the geopolitical landscape. (3)
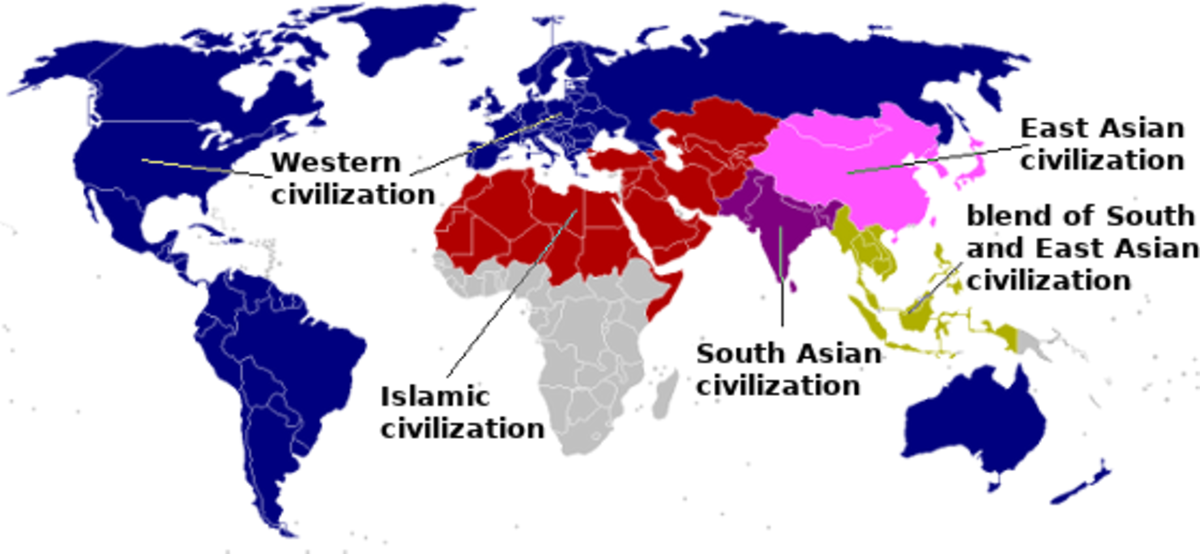
Moving forward; it could be debated that the following three elements, political, cultural, and physical geography play a major role in the delicate balance of global coexistence of human beings. Some experts subscribe to the notion that since the conclusion of the Cold War there has been a subsequent demise in the recognized world order. Consequently, developing nations throughout Asia, the Middle East and Africa have experience much unrest and are lashing out at the status quo powers that be within their home nation overtly while dispatching covert operatives throughout Western Civilization to create mayhem and havoc, via acts of unthinkable terror. (4)
2) Asia: Strategy, Tactics, and Solutions:
The experts agree that the strategic intelligence objective in East Asia revolves around China; today the denial factor is no longer acceptable, the People’s Republic of China along with her 4 million strong PLA military force need to be engaged by the United States Military and our allies. However; experts do also agree that prudence would be wise in such an operation; therefore the tactical perspective would include limited engagement utilizing both the United States Marine Corps along with a solid contingent of amphibious warfare trained U.S. Army soldiers. (5)
Moving forward, it would be crucial to procure a strategic partnership with our East Asian ally, Japan. This would provide tactical advantages throughout the Japanese held Ryukyu Islands, a chain stretching from Japan’s Kyushu Island to Taiwan that would enable U.S. led forces to position blockades that would harass the Chinese and close an important outlet for Chinese surface, submarine, and air forces into the Pacific Ocean thus providing an Asymmetrical, 4th Generation Warfare inspired attack against our formidable foe China. (6)
Suffice it to say that purpose of such an unorthodox fighting style displayed by the powerful United States military would be the same ultimate goal of an adversary of America would strive for via an Asymmetrical Warfare attack; to test and attempt to break the will of the regime in Beijing. Will Chinese leadership be willing to embark on an operation that will be in direct violation of the U.S. government led mandate to allow American ally Taiwan to live in peace. (7)
Moving forward to incorporating additional East Asian allies such as South Korea into a mission of such a magnitude would be to take advantage of South Korea’s position along the sea lines on which China’s North Sea Fleet rely on. (8) To reiterate, gone are the days when the United States could pretend genuine friendship with China; the stakes are quite simply too high to continue the façade. The control of the continent of Asia is in the balance; America is no position to abandon its interest on that continent and simply walk away.
3) The Continent of Africa Dilemma:
Ethnic and Religious Factors-1:
It could be perceived that America and her citizens have seen their fair share of civil unrest due to ethic rifts, political antagonism, cultural divide; most notoriously within our brief existence as a nation-state there was the 19th Century American Civil War which serves as harsh reminder of the flawed humanity that lies within all mankind to include our nation as well.
That being stated; with all of America’s woes regarding ethnic division, most would agree that it pales in comparison to the ethnic, religious, and tribal conflict that plagues the continent of Africa. The issue with Africa could be considered a “powder keg” effect taking place to reach beyond the borders of the Horn of Africa and ignite Sub Saharan African.
The threat of a turbulent Africa open for “business” regarding her vast natural resources along with being receptive to influences from nations that may not have the continent of Africa best interest in mind, while standing in staunch opposition to the United States, Israel and Western Civilization as a whole is an unnerving, however probable threat.
4) The Middle East & Eastern Europe and the Islamic Jihadist Challenge:
Ethnic and Religious Factors-2:
Although most Westerners view the Islamic Jihadist movement as strictly a Middle Eastern plague; however the Boston Marathon bombing is a brutal reminder that the Jihad in which America is a primary target is now being carried out by Eastern Europeans who are able to move in a Western environment in a more stealth like manner than that of a Middle Eastern individual. Today, Eastern European Chechnya, Albania, Romania, Bulgaria,
Turkey, Bosnia Herzegovina, Macedonia, Kosovo, and Bulgaria are home to the bulk of Europe’s Muslim population. And as with most Muslims, these human beings desire to live in peace and worship God the way they sit fit. Nevertheless with the “Boston bombing suspects were ethnic Chechens has renewed the focus on an area of Russia beset by conflict and controversy over the past 20 years.” (9) It would appear to be sufficient to state that the Islamic Jihadist movement has penetrated the Eastern European Muslim community. The threat to Western Civilization at the hands of Eastern European terrorist is real; as it is formed from the equivalent type of sense of rejection and victimization that their Middle Eastern Islamic brethren vehemently express; such as the Croatian treatment by the Serbians during their war in which “after the destruction of over 1,000 mosques the killing of 300,000 people the rape of 55,000 sisters, Islam is rising out of the ashes of war, strong and confident.” (10) Some may agree that the aforementioned statement could be construed as a battle cry.
Theoretical Countermeasures:
In an effort to discover appropriate Theoretical Countermeasures, one may need to consider such factors as the unconventional organizational methods in which a terrorist and or insurgent faction may operate. The tribal-like manner deployed by this Fourth Generation Warfare foe must be engaged with new strategy and tactics. These enemies recognize that a frontal confrontation with Western military forces would prove to be an exercise in futility. (11) Therefore continued intensified counter- asymmetrical, irregular, terrorist and insurgent training among all branches of the U.S. military and intelligence community is needed. Training that would focus less on technology and more on light infantry, guerilla warfare tactics, hand to hand, ethnic language/dialect and explosives concentrated training. Moving forward, further exploration needs to be done in the areas of psychological warfare to include population infiltration operations denial and deception operations with the goal being to expose disunity in a insurrection force which will require in-depth understanding of cultural human factors. (12)
Western military leaders must recognize that there is a lack of military doctrine in regards to the factions that have a propensity to employ Asymmetrical Warfare strategies and tactics. The lack of operational doctrine enables insurrection forces to remain an enigma for Western military leaders to unravel and overcome. (13) Some experts may concur that one additional unique aspect of the Asymmetrical Warfare threat that faces America has spawned even a new way we view the American warfighter. That view is the cutting edge mindset of distinguishing the professional Western trained Soldier versus the developing nation trained Warrior. Today’s American warfighter is a highly trained, disciplined professional Soldier who fellows orders and is by in large the property of our nation; however the developing nation Warrior has the freedom to operate on his instincts and his innate ability to take lives and survive. (14) Therefore continued efforts to prepare the current and next generation of American warfighter to develop into a lethal fusion of professional Soldier and instinctive Warrior is imperative. In conclusion, the China and North Korea East Asian unofficial alliance along with the conundrum of how much influence does Russia hold over its former Soviet Union “colonies” such as Chechnya; as well as soon to be nuclear armed Iran and the United States of America and her allies face formidable foes.
However what increases the threat factor is not only the danger of conventional warfare which could escalate into a nuclear holocaust. Today America’s enemies refuse to truly reveal themselves; only Iran and North Korea are willing to spew venomous Anti-America rhetoric, however common sense would dictate that there are many more enemies lurking in the shadows in the form of rogue state and non-state actors. The aforementioned type of perpetrators are willing to do the unthinkable to strike a lethal blow at the psyche of our nation’s leaders in Washington D.C. as well as the American people as a whole. Some may agree that at this point in American History our nation’s leaders may need to recognize that as the leaders of the Free World; as America goes so goes the safety, security and overall well-being of Western Civilization as a whole. Therefore, now may be the appointed time for the United States of America to increase our military’s role in leading small scale counter insurgency missions throughout the world, while aggressively seeking to capture and or eliminate high value targets that lead terrorist and insurgent forces and if required, the leaders of rogue nation-states that threaten the National Security of America and our citizens as well as pose a danger to our key allies such as Israel.
References:
1) CIA, Some Thoughts on Irregular Warfare, A Different Kind of Threat, Jeffrey B. White; https://www.cia.gov/library/center-for-the-study-of-intelligence/csi-publications/csi-studies/studies/96unclass/iregular.htm
2) ibid
3) ibid
4) ibid
5) United States Naval Institute, Asymmetric Warfare-American Style, Dr. Toshi Yoshihara, Dr. James Holmes, http://www.usni.org/magazines/proceedings/2012-04/asymmetric-warfare-american-style
6) ibid
7) ibid
8) ibid
9) Editors' blog BBC College of JournalismNews sourcesMedia ActionEditorial Guidelines;http://www.bbc.co.uk/news/world-europe-18188085
10) The Islamic Bulletin P.O. Box 410186, San Francisco, CA 94141-0186;http://www.islamicbulletin.org/newsletters/issue_13/islam.aspx#a3
11) CIA, Some Thoughts on Irregular Warfare, A Different Kind of Threat, Jeffrey B. White; https://www.cia.gov/library/center-for-the-study-of-intelligence/csi-publications/csi-studies/studies/96unclass/iregular.htm
12) THE IRREGULAR WARFARE CENTRE; http://www.irregularwarfare.org/Training.htm
13) CIA, Some Thoughts on Irregular Warfare, A Different Kind of Threat, Jeffrey B. White; https://www.cia.gov/library/center-for-the-study-of-intelligence/csi-publications/csi-studies/studies/96unclass/iregular.htm
14) ibid