Cases of Emotional Blackmail And Criminal Extortion
Blackmail Encapsulated
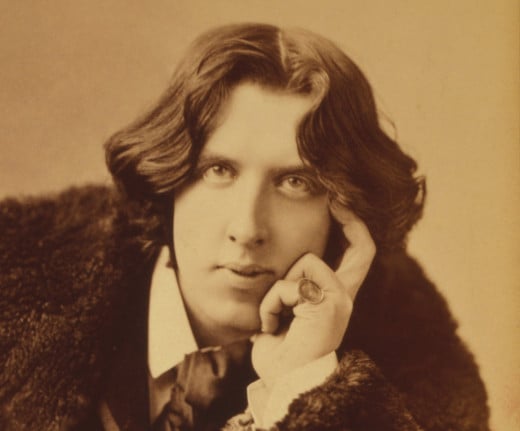
"If you don't help me, I must send it. If you don't help me, I will send it. You know what the result will be. But you are going to help me."
The above excerpt, taken from Oscar Wilde’s novel the picture of Dorian Gray, epitomizes the essence of blackmail. The Adonis-demon Gray, having committed murder, needs a former friend to deploy his scientific skills to erase any evidence of the corpse. Whatever is contained in this letter, it will destroy this man's future.
Anything You Say May Be Used Against You
The often-quoted fact that knowledge is power applies, in the ultimate sense, to those prepared to treat information of a damaging nature as a weapon to coerce compliance. This strategy pervades every aspect of business and interpersonal dealings. No-one who has trusted a friend/spouse/lover/colleague with sensitive information is immune to its menace. As we will discuss later in this article, even some monarchs have not escaped its intimidation.
Changes And Challenges
Fortunately, many things once deemed scandalous enough to dam or even doom a victim to lifelong ostracism and contempt have ceased to be fodder for extortion. The revelation of someone’s having given birth to a child out of wedlock, same gender preference, or a period of substance abuse are interwoven into our societal fabric. Conversely, the subtleties of technology have enabled recording of the most intimate acts or sensitive information. Hence, caution is needed.
Points To Consider Before Confiding
Nearly all of us have been tempted, during the conviviality of a social evening, to unveil areas of our lives we generally keep to ourselves, or open to only those closest to us. It can become far too easy to believe acquaintances may evolve into friends if we show readiness to treat them as such.
True, none of us wish to live in a state of ironclad guardedness. Still, it is wise to retain awareness that information, once given, cannot be withdrawn. In truth, it becomes the property of whoever might hear, including the random eavesdropper.
Social Blackmail: Heed The First Inner Chime of Alarm
Often, on a subliminal level, we sense things we have no basis to prove. When this occurs, we tend to edit out or ignore such a seemingly unfounded warning. By way of example, I was once in a group of women who accompanied their husbands to a gala following an all-male sports event. As the men gathered to verbally replay the match, we women snacked, sipped wine and chatted in the restaurant’s lounge.
Once we had all begun to relax, the team captain’s wife, as self appointed leader said,
“Let’s all go around and tell each other our maiden names.”
Uneasy, when my unwelcome turn came, I laughed, “Oh, I’ve had a lot of names.”
The next question was where each of us had been born. Now my anger began to rise as I said, “I’ve been born in a whole lot of places.”
By then, stares of animosity flaring, I stood up and strode away, saying, “I'm being too much of a killjoy to stay.”
Later, I wondered if I had been fair. This may have been an innocuous game to help strangers grow better acquainted. Still, any number of subjects would have been more fun to discuss: favorite films, music, vacation resorts; why this drab, personal data? In any event, I felt right to have decamped when the climate became disconcerting.
Beware of The Wily Wordsmith
On an emotional level, there are those who manoeuvre language in order to impose their wishes during a conflict. By way of example, one partner in a relationship would like the other to engage in an act which the other finds distasteful. The frustrated partner might ask, in a tone of betrayal,
“How can you refuse my desire because of a whim of yours?”
This phrasing has created its own hierarchy. Desires are viewed as deep and deserving of respect-even reverence. Conversely, whims can be dismissed and eschewed as mere selfish trivia.
Setting Parameters To Gain Power
One strategy of the emotional blackmailer is to set an arbitrary definition, meant to generate guilt in his prey, leading to acquiescence. Let’s say a partner states,
“If you truly loved and trusted me, you would be willing to exchange keys to each other’s homes.”
A valid response might be, in essence, “If that is your definition, then you are right; I do not love or trust you. Still, this is YOUR standard of proof and not mine, so I do not feel bound by it.”

Spoiling The Blackmailer’s Bluff: Oprah Winfrey’s Candor
The many-faceted Oprah Winfrey is known, among her attributes, as a philanthropist, giving a good deal of her annual income to charities, and supporting causes in which she believes. She has also provided help to her family in various fruitful and constructive ways. Still, she has not been willing to waste her financial resources on those who have failed to make a genuine effort to confront their own struggles.
Thus, having paid twice for a sister to receive care in a top scale drug rehab center, when asked to do so a third time, she refused. Her sister then threatened to publicize the fact that, at age 14, Ms. Winfrey had given birth to an illegitimate child. Wisely, Oprah refused to allow this menace of extortion to overcome her principles.
A backfiring Threat of Vengeance
Oprah decided to trust the public to accept these errors as part of her human fallibility. Admitting to having been “a promiscuous teen”, at some point she also owned up to having smoked crack cocaine during her younger years. She thereby stripped her sister of any further attempts to discredit her. Also, in a well-deserved twist of justice, her sister became exposed as a long-term drug addict and potential blackmailer.
An Innocent Photograph Can Become A Tool of Extortion
While wealth can procure, among countless perks, the freedom from many tedious tasks, it can also spawn vulnerabilities. The day of the nanny who has looked after two or more generations and is truly integral to a family is now, if not completely in the past, at least heading for extinction. Hence, those needing live-in staff can no longer feel cocooned by its decades of loyalty.
Indeed, more than one young nanny has married her male employer, destroying familial structure and causing the children’s mother humiliation and anguish. An added hazard lies in allowing household frolics to be snared on film, to be used as the photographer chooses.

A Nanny And Her Partner’s Shenanigans
Famous model Cindy Crawford employed a nanny who assisted in caring for her two children of husband Rande Gerber. During 2008, the nanny took a photo of their seven year old daughter, Kaia Gerber in an innocuous game they were playing. Acting the part of a thief apprehended, Kaia was tied to a chair and gagged.
A year later, Edis Kayalar who was in a relationship with the nanny, ostensibly stole the photograph from her.
Kayalar then demanded money from Crawford and Gerber in exchange for the photograph. He believed the content of the photo could be sensationalized and therefore of great media value, especially tabloid journalists. Initially, Gerber paid him $1000 to obtain a copy of the photo. Kayalar then demanded in excess of $110,000 for the return of the original.
Undoubtedly both Ms. Crawford and Gerber knew this extortionist was unethical enough to keep a copy for future use. Rather than succumb, they refused to pay and informed the police of the menace. When arrested, Kayalar confessed to blackmail and was sentenced to two years imprisonment for attempted extortion.
CBS Report on The Attempted Extortion of Cindy Crawford
If She Really Loved Him: A Father Impels His Young Daughter To Commit Murder
Infamous murderer David Brown, like most sociopaths, felt no concern for the consequences to others of whatever he wished. This coldness encompassed his 14-year-old daughter, Cinnamon. As Brown had by then been married 5 times, Cinnamon’s early years had been disturbed and unsettled. Hence, when her father told her Linda, his fifth wife was plotting to kill him, Cinnamon feared losing the nearest thing she had to an anchor-her dad.
Manacles of Manipulation Deployed
David Brown convinced Cinnamon that overheard intercepted telephone conversations had left him in no doubt of Linda’s savage intentions. As Linda was only 23, she and Cinnamon had become friends, while Linda remained somewhat maternal. Thus, Cinnamon was at first incredulous.
Even more difficult was his demand that Cinnamon shoot her stepmother. He based this bizarre request on the fact that Cinnamon’s youth would urge the court to be more lenient towards her than they would be towards him as an adult. When Cinnamon hesitated, Brown claimed her compliance was the sole means of preventing his death.
The Penultimate Test
His final tactic was to tell Cinnamon that if she genuinely loved him, she would intervene between him and his doom. Her refusal could only mean she felt no love for the man who, though he had made his share of errors, had done everything he could to be a good father to her. Aghast, she protested; how could he even doubt, for one moment, the boundless love she felt for him? This rendered Brown the victor, reducing his daughter to a fawn cornered by a deer hunter.
The Deed Done In His Absence
On the evening of March 19, 1985, Brown left the house. While on errands, he made sure to chat with enough people, (a few more than once), to allow him to manufacture an alibi. Later, he claimed to have come home to an inconceivable horror. His 23-year-old wife had been killed, apparently by his daughter.
Judicial Repercussions
A lengthy legal struggle followed this crime, much of which is irrelevant to our study of the uses of blackmail. To summarize, once Cinnamon was locked away in a reformatory, pretending to have blanked out any memory of what happened that night, Brown luxuriated in a sumptuous life with Patti, his deceased wife’s sister, aged 15.
His pleasures were, however, curtailed when Cinnamon, questioned further by the police, came to detest her father. This change came about when she learned his lifestyle was subsidized by the proceeds of the $835,000 life insurance policies Brown had taken out on Linda, some of these taken out shortly before her death.
Confronted, Brown tried to blame the murder plan on his current wife, Patti. This vulcanized her into revealing her significant knowledge. Charged in 1988, David Brown was sentenced to life imprisonment without parole by a judge who stated he had been a master manipulator.
Perdita And The Prince of Wales: Would She Publish His Letters?
Mary Darby Robinson, 1758 to 1800 an actress and poet, is known in history as Perdita, based on her stage role as Perdita in Shakespeare’s play (The Winter’s Tale). During the late 1770s, the Prince of Wales, later King George the Fourth, became enamoured of her.
Up to this point, her life had proved difficult. Her family’s poverty had made her feel obliged to wed a Thomas Robinson, in hopes of financial help. Having done so, she was forced to suffer the public insult of his flagrant infidelities. At one point, she and her small daughter were held under house arrest due to his debts. Thus, when a chance to be recognized on the stage arose, it proved of enormous value.
The Prince Or Her Profession
Although she performed in a number of Shakespeare’s plays, it was as Perdita that the young Prince of Wales grew besotted. Indeed, he signed his early love letters “Florizel”, Perdita’s beloved. Pleased as she must have been by this attention, when he asked her to be his mistress, she became conflicted.
Knowing the heir to the English throne could not even consider marrying her, she was also aware if she left the stage, she would never be allowed to return. In her day, forgiveness for “fallen women” could not be expected. Still, her royal suitor conquered her fear by a pledge of £20,000.
Abandoned with a promise which she found to be hollow, in 1781, the prince, as he would with mistresses throughout his lifetime, discarded Perdita, simultaneously disregarding his pledge. This left her with a ruined career and few financial avenues. Hence, she threatened to publish his worshipful letters.
This Exposure Could Not Happen
Though tears and pleas could be dismissed and ignored, the prince could not risk being viewed by his future subjects as a cad and seducer. Thus, Perdita was paid a substantial amount in exchange for these letters. A lifelong pension was agreed too; although honoured, its payment was somewhat sporadic. Still, after their animosity passed, the prince and his former mistress maintained a friendship which remained cordial, even during his kingship.
Conclusion
As we have seen, blackmail can take infinite forms, from the venomous to the petty. Often, in familial terms, it can be difficult to detect until it has become so ingrained as to prove hard to eradicate.
One proverb states that illness is first a guest in a home, but can soon become master. This maxim can apply to any type of vulnerability: childhood, old age, illness and/or disability. While compassion and love should be offered to all, carers must shield themselves against subtle enslavement. The child who learns that crying at bedtime will gain an extra hour of TV or Internet use will soon make it a habit.
As to the elderly, one friend has said she and her siblings half-joke about having badges made stating, “Yes, Dad, we know you are over 80.” Conversely, one neighbor in her mid-80s deals with her food shopping on-line, has an excellent mobile hairdresser, arranges for her prescriptions to be delivered-in short, and asks as little as she possibly can of her children and grandchildren.
She has also chosen a care home where she hopes to spend her last years if she becomes too enfeebled to maintain her own apartment. Thus, her family finds her a fun and delightful friend and enjoy spending time with her. Ultimately, as longevity increases, it is worthwhile to be aware, both in ourselves and others, of any tendency to use guilt as a tool of manipulation.
Please enter the poll
Have you been blackmailed because of a secret you divulged about yourself or someone else?
© 2014 Colleen Swan