Classical View and Parker Adjustments
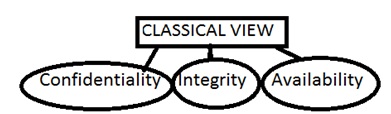
Under the classical view of information security, CIA maintained a focus primarily to preserve the confidentiality, integrity and availability of information from disclosure, modification, destruction and use. This was preserved by prevention, detection and recovery methods with a focus of reducing loss or the risk of loss of information. (Traditional INFOSEC framework PowerPoint, slide 1)
Classical View and Parker Adjustments
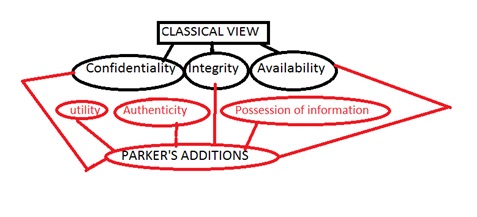
This was expanded by Parker to include preservation of availability, utility, integrity, authenticity, confidentiality, possession of information from accidental or intentional destruction, interference, use of false data, modification or replacement, misrepresentation or repudiation, misuse or failure to use, access, observation or disclosure, copying, stealing or endangerment caused by avoidance, deterrence, prevention, detection, mitigation, transference, sanction, recovery, or correction. These changes were made with the intentions to meet a standard of due care, avoid loss, reduce loss or eliminate loss all together. (Traditional INFOSEC framework PowerPoint, slides 2-3)
The ideal behind Parker’s expansion was to place government controls as well as business controls over information. The government controls include employee clearances, need-to-know principles, mandatory access control, classifications of information and cryptography. Business controls include need-to-withhold, discretionary access control, copyright and patent, and digital signatures. (Traditional INFOSEC framework PowerPoint, slide 4)
Parker’s addition to protect information from accidental or intentional destruction implemented the use of security clearances within the government. The classification was created to establish secret clearance, top secret, confidential, sensitive but unclassified or other business-like classifications. (Prof. Nichols, INFOSEC and Risk Management, PowerPoint, slide 64) The security levels established a need-to-know basis which is determined by the security clearance level. This created a restriction on what level of information was given to any particular person by limited what they had access to.
The improvements created by Parker are extremely important for further security placed on information. The expansion of the general focus to include additional focus on utility, authentication and possession, in addition to confidentiality, integrity, and availability established a far-more diverse realm of protection. By establishing authentication, information is guaranteed to be what it says it is. A limit on possession prevents a leakage of material so people cannot easily access it. Utility establishes the usefulness of the information in order to establish access level requirements.
Each change implied goes hand-in-hand with the classical view of CIA to further protect information from unwanted access and altering of information. The changes are important because they expand government security of information to secure business information through a higher level of protection and restrictions.