Quantum Cryptography

At some point in our academic lives, we all must have read about the various interesting phenomena of Physics. In this regard, the long details of electron movements and their properties to spin around the nucleus or dissipate and absorb energy, used to be the main highlights of our physics text books.
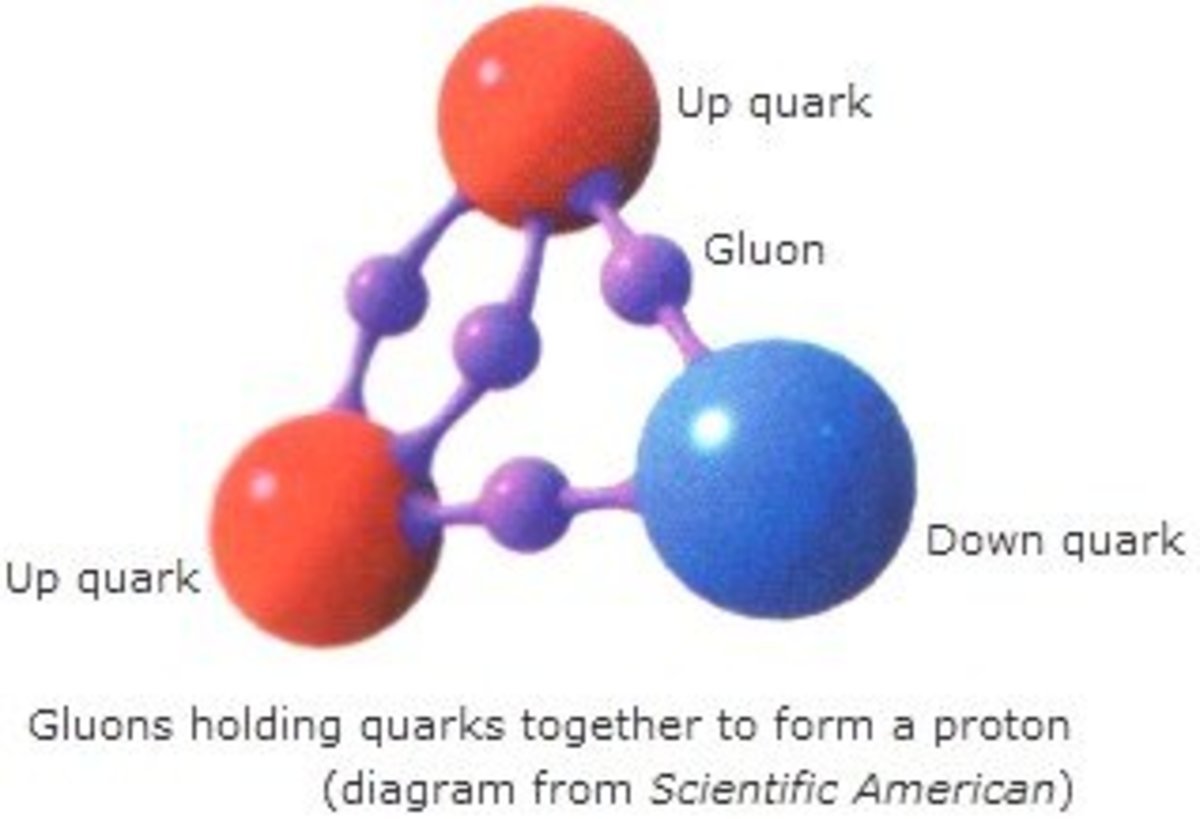
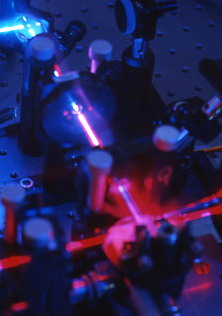
Notwithstanding the general lack of interest in the complicated and often regarded as boring theories, quantum studies are undoubtedly one of the important subjects in physics. The study of quantum mechanics is an important reality since it is expected to affect our macroscopic lives sooner or later. This prediction has been proven after with 20 years of academic research by scientists who formulated the safest type of computer encryptions in the form of quantum cryptography system.Quantum cryptography would help scientists to introduce a reliable system of secret keys with which e-mail messages, telephone calls or financial transactions can be encrypted, making it difficult to be identified. For example, if there are things that one wants to keep protected for 10 to 30 years, quantum cryptography can make it possible. This makes it doubly important for us to understand the concept of quantum cryptography system.Physicists investigating the fundamental mechanisms of the universe claim that they have found the key to the future of cryptography. Quantum cryptography was discovered independently in the US and Europe. It was first proposed by Stephen Wiesner of the Columbia University in New York as a secure approach of communication which has been developed on the basic principals of quantum physics.Researchers are learning that the manipulation of light may be the strongest form of encryption that has been devised in order to control the people from listening to the encrypted messages. Previously, the conventional cryptographic methods were based on mathematical entities and calculations. However, the conventional methods demanded that the propelling and receiving of messages be carried out by physical means: photons in the optical fibres or electrons in an electric current. According to the laws of physics, quantum theory is known to rule every phenomenon, but its repercussions are very blatant in microscopic systems, like individual photons, atoms and molecules.The quantum cryptographic tools characteristically utilise the individual photons of light and make use of either the uncertainty principal of Heisenberg (defines uncertainty of the presence of electrons in any locality of atom, dissipating and absorbing energy) or the quantum entanglement phenomenon of electrons. It is also possible to formulate and put into practice a communication system which is able to detect such eavesdropping.Since the science of quantum cryptography is based on two important quantum mechanics -- the uncetainity of photons and quantum entanglement -- it is very important to have an understanding of these mechanics.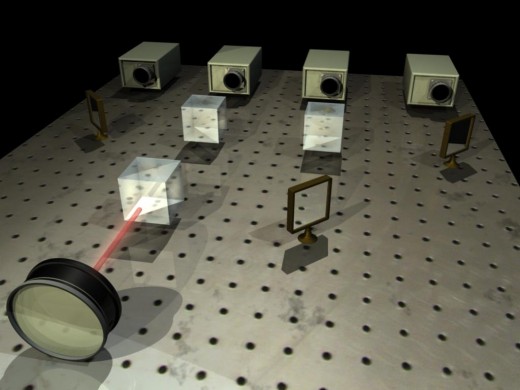
Quantum Entanglement
Quantum entanglement is a condition of two or more quantum particles like photons where the various properties are correlated. It is not possible to explain the entangled particles by just describing the states of every particle individually. However, they can combine or distribute the information in a way which cannot be accessed in any experiment performed on the individual particles alone. This can occur regardless of the distance between the particles at the time of experiment. The process of entanglement is difficult for very long distance quantum key distributions
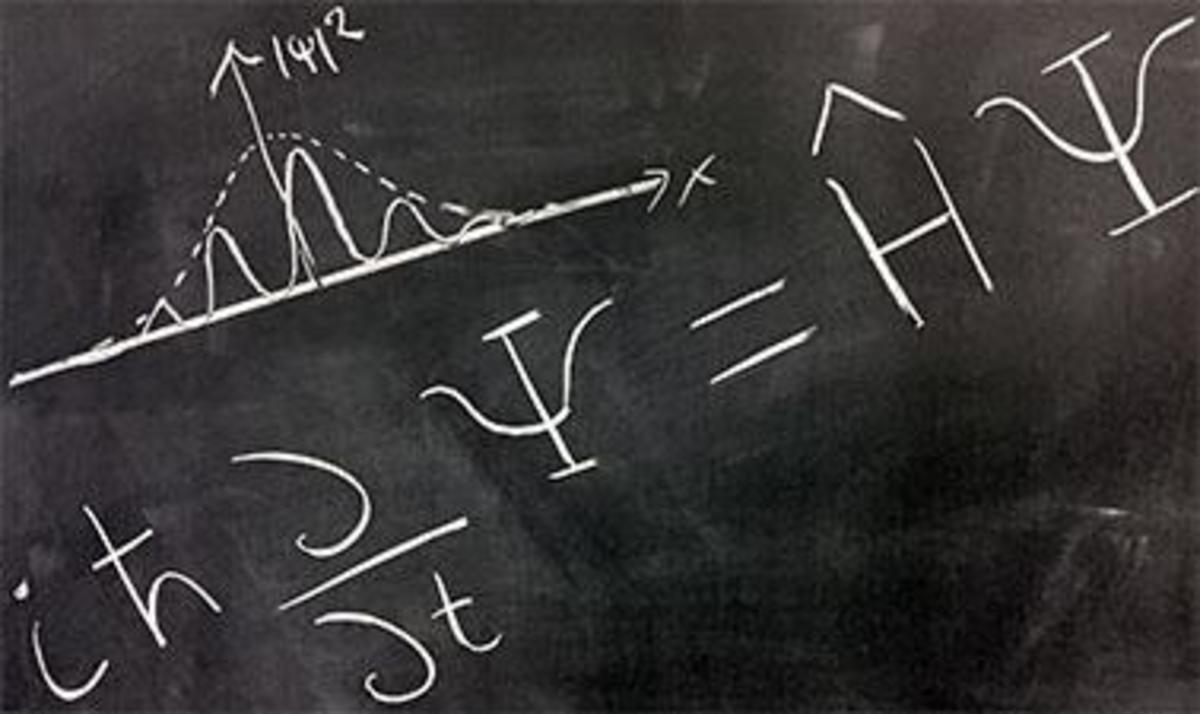
Uncertainty
Performing measurements is considered to be an important aspect of quantum mechanics. Hence, it is quite possible to encode information into some of the quantum characteristics of a photon in a manner that any effort to surveil them will change photons in some detectable way.
According to quantum theory, certain pairs of physical attributes of photons are complementary in such a way that one property significantly changes the other. Physicists have named this explanation the Heisenberg's uncertainity principle.The principle not only explains the limitations of a specific measurement technology, but it also sheds light on every possible measurement. One of the ways to send a quantum-cryptographic key between sender and receiver needs a laser which transmits single photons that are polarised in one of the two modes.There are two complementary characteristics which are frequently used in quantum cryptography. The first one is the two modes of photon's polarisation -- for example, the rectilinear -- which involves vertical and horizontal polarisations. The second mode is in which they are oriented at 45 and 135 degrees to the left or right of vertical, called the diagonal mode of photon polarisation. In both methods, the opposing positions of the photons represent either a digital 0 or 1.The sender, whom the cryptographers by convention call Alice, sends a string of bits, choosing arbitarily to send photons in either the rectilinear or the diagnol modes. The receiver, likewise, is called Bob in crypto language, who makes a similar random descision about the mode to calculate the incoming bits. The Heisenberg's uncertainty principle states that it is possible to measure the bits in only one mode, not both. Only the bits that Bob measured in the same mode as sent by Alice are guaranteed to be in the accurate orientation, thus retaining the proper value.The most challenging task for modern cryptographers is to distribute a key ensuring that no one has stolen a copy of it. The method is known as public-key cryptography and is mostly used for sharing secret keys for encryption and decoding of complete length messages.The conventional public-key cryptography depends on factorisation. The secret key code which has to be transferred between sender and reciever is encrypted with a publicly available key, for example, 408,508,091. Such large number can be decrypted only with a private key that the recipient of the data possesses. It is made up of two factors; in this case it will be 18,313 and 22,307. The problem of overcoming a public-key code can be solved by having secret keys, secured for a decade or more period of time.The era of quantum information is already in. And the ability of quantum computers to perform very complex and challenging factorisations may signify the ultimate end of conventional cryptographic techniques. However, contrary to public-key cryptography, quantum cryptography is expected to act safely with the arrival of more quantum computers on the scene.