TCP/IP network access and internet layers
The TCP/IP Model
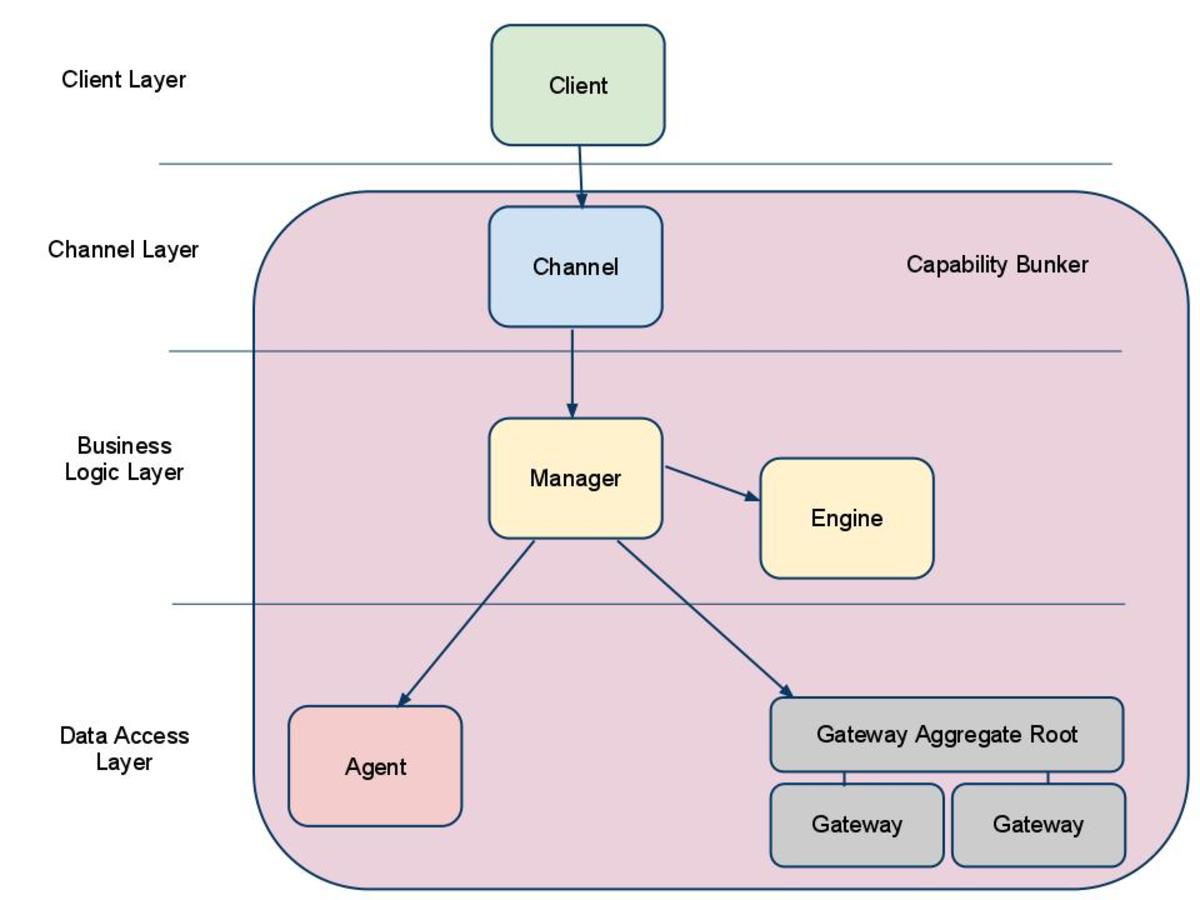
TCP/IP is an industry standard set of protocols developed by the U.S. Department of Defense Advanced Research Projects Agency (DARPA) in 1969. TCP/IP is made up of two acronyms, TCP, for Transmission Control Protocol, and IP, for Internet Protocol. TCP handles packet flow between systems and IP handles the routing of packets. However, that is a simplistic answer that we will expound on further. All modern networks are now designed using a layered approach. Each layer presents a predefined interface to the layer above it. The layers near the top are logically closer to the user application (as opposed to the human user) while those near the bottom are logically closer to the physical transmission of the data (Jeff Doyle and Jennifer Carroll, 2005). Viewing layers as providing or consuming a service is a method of abstraction to isolate upper layer protocols from the nitty gritty detail of transmitting bits over, say, Ethernet and collision detection while the lower layers avoid having to know the details of each and every application and its protocol. This abstraction also allows upper layers to provide services that the lower layers cannot, or choose not, to provide. Again, the original OSI Reference Model was extended to included connectionless services (OSIRM CL). For example, IP is not designed to be reliable and is a best effort delivery protocol.
This means that all transport layers must choose whether or not to provide reliability and to what degree. UDP provides data integrity (via a checksum) but does not guarantee delivery; TCP provides both data integrity and delivery guarantee (by retransmitting until the receiver receives the packet). By doing so, a modular design can be developed so as to minimize problems in the development of new applications or in adding new interfaces. It maps TCP/IP protocols to a four-layer conceptual model known as the DARPA model. The TCP/IP model does not exactly match the OSI model. (Laura A. Chappell and Ed Tittel, 2001)
OSI and TCP/IP Layering Differences
The Open Systems Interconnection (OSI) reference model created in the late seventies and used today consists of seven layers that include Application, Presentation, Session, Transport, Network, Data Link and Physical. The Application layer often dubbed Layer 7 is the most common layer to end users and can consist of applications such as Microsoft’s Internet Explorer or other browser software. The Presentation layer provides a translation of application data to network format in order to be processed and is considered bidirectional. The Session layer is responsible for controlling communication between applications by establishing, managing and ending dialogs. The Transport layer is responsible for end to end error recovery and the complete transparent transfer of data between systems. The Network layer is where all switching and routing of data takes place. This layer is responsible for congestion control as presented in this week’s discussion question and also provide packet prioritization. Finally we have the Data Link and Physical layers. The Data Link is where data packets are encoded into bits and is divided into two sublayers: Media Access Control (MAC) and Logical Link Control (LLC). The Physical layer is where hardware such as Network Interface Cards (NIC) and other protocols reside.
The universal Transmission Control Protocol/Internet Protocol (TCP/IP) model is not written in stone and can range from three to five layers depending on the model. I plan to use a model that is often used and contains four layers consisting of the Applications, Transport, Internet and Network Access layer. Under the TCP/IP model the application layer represents data using such protocols as Simple Mail Transfer Protocol (SMTP), File Transfer Protocol (FTP) and Telnet. The Transport layer has two dedicated protocols; the Transmission Control Protocol (TCP) in charge of assuring information is received as it was sent and the User Datagram Protocol (UDP) that performs no end-to-end reliability checks. “In the OSI Reference Model the Network Layer isolates the upper layer protocols from the details of the underlying network and manages the connections across the network.” The IP Internet Layer corresponds to the Network Layer of the OSI model and includes the Internet Protocol (IP), Internet Control Message Protocol (ICMP), and Internet Group Management Protocol (IGMP) protocols. The Network Access Layer consists of data link protocols such as Ethernet and Token Ring. The NAL mirrors or ties back to the Data Link and Physical Layers of the OSI model.
There is no universal agreement regarding how to describe TCP/IP with a layered model but it is generally agreed that there are fewer levels than the seven layers of the OSI model. Most descriptions present from three to five layers. In this technical reference document the layers of the TCP/IP model are defined as follows:
1- Application Layer
In TCP/IP the Application Layer also includes the OSI Presentation Layer and Session Layer. In this document an application is any process that occurs above the Transport Layer. This includes all of the processes that involve user interaction. The application determines the presentation of the data and controls the session. In TCP/IP the terms socket and port are used to describe the path over which applications communicate. There are numerous application level protocols in TCP/IP, including Simple Mail Transfer Protocol (SMTP) and Post Office Protocol (POP) used for e-mail, Hyper Text Transfer Protocol (HTTP) used for the World-Wide-Web, and File Transfer Protocol (FTP). Most application level protocols are associated with one or more port number.
2- Transport Layer
In TCP/IP there are two Transport Layer protocols. The Transmission Control Protocol (TCP) guarantees that information is received as it was sent. The User Datagram Protocol (UDP) performs no end-to-end reliability checks.
3- Network Access Layer
In TCP/IP the Data Link Layer and Physical Layer are normally grouped together. TCP/IP makes use of existing Data Link and Physical Layer standards rather than defining its own. Most RFCs that refer to the Data Link Layer describe how IP utilizes existing data link protocols such as Ethernet, Token Ring, FDDI, HSSI, and ATM. The characteristics of the hardware that carries the communication signal are typically defined by the Physical Layer. This describes attributes such as pin configurations, voltage levels, and cable requirements. Examples of Physical Layer standards are RS-232C, V.35, and IEEE 802.3.
4- Internet Layer
In the OSI Reference Model the Network Layer isolates the upper layer protocols from the details of the underlying network and manages the connections across the network. The Internet Protocol (IP) is normally described as the TCP/IP Network Layer. Because of the Inter-Networking emphasis of TCP/IP this is commonly referred to as the Internet Layer. All upper and lower layer communications travel through IP as they are passed through the TCP/IP protocol stack.
The four layer structure of TCP/IP is built as information is passed down from applications to the physical network layer. When data is sent, each layer treats all of the information it receives from the layer above as data and ads control information to the front of that data. This control information is called a header, and the addition of a header is called encapsulation. When data is received, the opposite procedure takes place as each layer removes its header before passing the data to the layer above.
3- Network Access Layer
The Network Access Layer is the lowest layer of the TCP/IP protocol hierarchy. The protocols in this layer provide the means for the system to deliver data to the other devices on a directly attached network. This layer defines how to use the network to transmit an IP datagram. Unlike higher-level protocols, Network Access Layer protocols must know the details of the underlying network (its packet structure, addressing, etc.) to correctly format the data being transmitted to comply with the network constraints. The TCP/IP Network Access Layer can encompass the functions of all three lower layers of the OSI Reference Model (Network, Data Link, and Physical).
The Network Access Layer is often ignored by users. The design of TCP/IP hides the function of the lower layers, and the better-known protocols (IP, TCP, UDP, etc.) are all higher-level protocols. As new hardware technologies appear, new Network Access protocols must be developed so that TCP/IP networks can use the new hardware. Consequently, there are many access protocols -- one for each physical network standard.
Functions performed at this level include encapsulation of IP datagrams into the frames transmitted by the network, and mapping of IP addresses to the physical addresses used by the network. One of TCP/IP's strengths is its universal addressing scheme. The IP address must be converted into an address that is appropriate for the physical network over which the datagram is transmitted. Two RFCs that define Network Access Layer protocols are:
- RFC 826, Address Resolution Protocol (ARP), which maps IP addresses to Ethernet addresses
- RFC 894, A Standard for the Transmission of IP Datagrams over Ethernet Networks, which specifies how IP datagrams are encapsulated for transmission over Ethernet networks
As implemented in UNIX, protocols in this layer often appear as a combination of device drivers and related programs. The modules that are identified with network device names usually encapsulate and deliver the data to the network, while separate programs perform related functions such as address mapping.
4- Internet Layer
The layer above the Network Access Layer in the protocol hierarchy is the Internet Layer. The Internet Protocol (IP) is the most important protocol in this layer. The release of IP used in the current Internet is IP version 4 (IPv4), which is defined in RFC 791. There are more recent versions of IP. IP version 5 is an experimental Stream Transport (ST) protocol used for real-time data delivery. IPv5 never came into operational use. IPv6 is an IP standard that provides greatly expanded addressing capacity. Because IPv6 uses a completely different address structure, it is not interoperable with IPv4. While IPv6 is a standard version of IP, it is not yet widely used in operational, commercial networks. Since our focus is on practical, operational networks, we do not cover IPv6 in detail.
The Internet Protocol is the heart of TCP/IP. IP provides the basic packet delivery service on which TCP/IP networks are built. All protocols, in the layers above and below IP, use the Internet Protocol to deliver data. All incoming and outgoing TCP/IP data flows through IP, regardless of its final destination.
4.1- Internet Protocol
The Internet Protocol is the building block of the Internet. Its functions include:
- Defining the datagram, which is the basic unit of transmission in the Internet
- Defining the Internet addressing scheme
- Moving data between the Network Access Layer and the Transport Layer
- Routing datagrams to remote hosts
- Performing fragmentation and re-assembly of datagrams
Before describing these functions in more detail, let's look at some of IP's characteristics. First, IP is a connectionless protocol. This means that it does not exchange control information (called a "handshake") to establish an end-to-end connection before transmitting data. In contrast, connection-oriented protocol exchanges control information with the remote system to verify that it is ready to receive data before any data is sent. When the handshaking is successful, the systems are said to have established a connection. The Internet Protocol relies on protocols in other layers to establish the connection if they require connection-oriented service.
IP also relies on protocols in the other layers to provide error detection and error recovery. The Internet Protocol is sometimes called an unreliable protocol because it contains no error detection and recovery code. This is not to say that the protocol cannot be relied on -- quite the contrary. IP can be relied upon to accurately deliver your data to the connected network, but it doesn't check whether that data was correctly received. Protocols in other layers of the TCP/IP architecture provide this checking when it is required.
4.1.1- The datagram
The TCP/IP protocols were built to transmit data over the ARPAnet, which was a packet-switching network. A packet is a block of data that carries with it the information necessary to deliver it, similar to a postal letter, which has an address written on its envelope. A packet-switching network uses the addressing information in the packets to switch packets from one physical network to another, moving them toward their final destination. Each packet travels the network independently of any other packet.
The datagram is the packet format defined by the Internet Protocol. The first five or six 32-bit words of the datagram are control information called the header. By default, the header is five words long; the sixth word is optional. Because the header's length is variable, it includes a field called Internet Header Length (IHL) that indicates the header's length in words. The header contains all the information necessary to deliver the packet.
4.1.2- Routing datagrams
Internet gateways are commonly (and perhaps more accurately) referred to as IP routers because they use Internet Protocol to route packets between networks. In traditional TCP/IP jargon, there are only two types of network devices -- gateways and hosts. Gateways forward packets between networks, and hosts don't. However, if a host is connected to more than one network (called a multi-homed host), it can forward packets between the networks. When a multi-homed host forwards packets, it acts just like any other gateway and is in fact considered to be a gateway. Current data communications terminology makes a distinction between gateways and routers, but we'll use the terms gateway and IP router interchangeably.
In current terminology, a gateway moves data between different protocols, and a router moves data between different networks. So a system that moves mail between TCP/IP and X.400 is a gateway, but a traditional IP gateway is a router.
4.1.3- Fragmenting datagrams
As a datagram is routed through different networks, it may be necessary for the IP module in a gateway to divide the datagram into smaller pieces. A datagram received from one network may be too large to be transmitted in a single packet on a different network. This condition occurs only when a gateway interconnects dissimilar physical networks.
Each type of network has a maximum transmission unit (MTU), which is the largest packet that it can transfer. If the datagram received from one network is longer than the other network's MTU, the datagram must be divided into smaller fragments for transmission. This process is called fragmentation. Think of a train delivering a load of steel. Each railway car can carry more steel than the trucks that will take it along the highway, so each railway car's load is unloaded onto many different trucks. In the same way that a railroad is physically different from a highway, an Ethernet is physically different from an X.25 network; IP must break an Ethernet's relatively large packets into smaller packets before it can transmit them over an X.25 network.
The format of each fragment is the same as the format of any normal datagram. Header word 2 contains information that identifies each datagram fragment and provides information about how to re-assemble the fragments back into the original datagram. The Identification field identifies what datagram the fragment belongs to, and the Fragmentation Offset field tells what piece of the datagram this fragment is. The Flags field has a "More Fragments" bit that tells IP if it has assembled all of the datagram fragments.
4.1.4- Passing datagrams to the transport layer
When IP receives a datagram that is addressed to the local host, it must pass the data portion of the datagram to the correct Transport Layer protocol. This is done by using the protocol number from word 3 of the datagram header. Each Transport Layer protocol has a unique protocol number that identifies it to IP. You can see from this short overview that IP performs many important functions. Don't expect to fully understand datagrams, gateways, routing, IP addresses, and all the other things that IP does from this short description; each chapter will add more details about these topics. So let's continue on with the other protocol in the TCP/IP Internet Layer.
4.2- Internet Control Message Protocol
An integral part of IP is the Internet Control Message Protocol (ICMP) defined in RFC 792. This protocol is part of the Internet Layer and uses the IP datagram delivery facility to send its messages. ICMP sends messages that perform the following control, error reporting, and informational functions for TCP/IP:
4.2.1- Flow control
When datagrams arrive too fast for processing, the destination host or an intermediate gateway sends an ICMP Source Quench Message back to the sender. This tells the source to stop sending datagrams temporarily.
4.2.2- Detecting unreachable destinations
When a destination is unreachable, the system detecting the problem sends a Destination Unreachable Message to the datagram's source. If the unreachable destination is a network or host, the message is sent by an intermediate gateway. But if the destination is an unreachable port, the destination host sends the message.
4.2.3- Redirecting routes
A gateway sends the ICMP Redirect Message to tell a host to use another gateway, presumably because the other gateway is a better choice. This message can be used only when the source host is on the same network as both gateways. To better understand this, refer to Figure 1-7. If a host on the X.25 network sent a datagram to G1, it would be possible for G1 to redirect that host to G2 because the host, G1, and G2 are all attached to the same network. On the other hand, if a host on the token ring network sent a datagram to G1, the host could not be redirected to use G2. This is because G2 is not attached to the token ring.
4.2.4- Checking remote hosts
A host can send the ICMP Echo Message to see if a remote system's Internet Protocol is up and operational. When a system receives an echo message, it replies and sends the data from the packet back to the source host. The ping command uses this message.
Normally the application programmers are in charge of layer 5 protocols (the application layer), while the layer 3 and 4 protocols are services provided by the TCP/IP stack in the operating system. Microcontroller firmware in the network adapter typically handles layer 2 issues, supported by driver software in the operational system. Non-programmable analog and digital electronics are normally in charge of the physical layer, typically using a application-specific integrated circuit (ASIC) chipset for each radio interface or other physical standard. (Andrew G. Blank, 2002)
However, hardware or software implementation is not stated in the protocols or the layered reference model. High-performance routers are to a large extent based on fast non-programmable digital electronics, carrying out layer 3 switching. In modern modems and wireless equipment, the physical layer may partly be implemented using programmable DSP processors or software radio (soft radio) programmable chipsets, allowing the chip to be reused in several alternative standards and radio interfaces instead of separate circuits for each standard, and facilitating. The Apple Geoport concept was an example of CPU software implementation of the physical layer, making it possible to emulate some modem standards.
References:
Jeff Doyle and Jennifer Carroll, (2005), “Routing TCP/IP”
Behrouz A Forouzan, (2002), “TCP/IP Protocol Suite”
Andrew G. Blank, (2002), “TCP/IP Protocol”
Martin R. Arick, (1993), “The TCP/IP Companion: A Guide for the Common User”