Codes, Signals, and Cipher Messages

By Joan Whetzel
Codes, signals and ciphers can all be used to send messages, some of them secretly, others not so much. The reasons for choosing one delivery method over another are as varied as the messages themselves. Just for the fun of it get together with friends and try sending each other messages with one of these codes, ciphers, or signals.
Ground to Air Signals
Survivalists, hikers, and wilderness junkies sometimes find themselves lost, despite their best efforts to know where they are at all times. They usually plan ahead for such circumstances, lettubg family or friends know their destinations and the message that if they haven't been heard from by a certain date, to call authorities and have search and rescue teams called out. Most of them also know the ground to air signals that communicate their needs to search and rescue teams in airplanes and helicopters. The list below gives the simple signals and their meanings. To send one of the signals, large branches or rocks are laid out in one of these signal patterns, made huge enough to be seen from the sky.
National Search and Rescue Code:
V = requests assistance
--> = [arrow] indicates direction of travel
X = unable to proceed
N = no, nothing is needed
Y = yes
LL = all is well
[rectangle] = map and compass are needed
F = need food and water
I I = medical supplies needed
I = serious injury, need doctor
Morse Code
Morse code is a way of sending text messages using a series of dots and dashes, or dits and dahs. Originally, it was used to send messages by means of a teletype or telegraph. Morse code can be sent by other means as well like using long and short bursts of light (from a lamp, lantern or flashlight), clanging two metal objects together, or hitting two objects that create a sound loud enough to be heard either nearby or from a distance. The object is to make sure someone sees or hears the dits and dahs and can recognize the sequences as Morse code. Hopefully someone on the receiving end either knows Morse code or has a chart to help them figure it out. The chart below shows the numbers and letters, along with their corresponding dot-dash sequences.
To use Morse code, there are a few things to remember;
- Separate multiple numbers or letters within a word by a short space, about one dot in duration.
- Separate words by a duration of dots.
- Dash duration is 3 times longer than dot duration.
- The international distress signal is SOS
1 . - - - -
2 . . - - -
3 . . . - -
4 . . . . -
5 . . . . .
6 - . . . .
7 - - . . .
8 - - - . .
9 - - - - .
10 - - - - -
A . -
B - . . .
C - . - .
D - . .
E .
F . . - .
G - - .
H . . . .
I . .
J . - - -
K - . -
L . - . .
M - -
N - .
O - - -
P . - - .
Q - - . -
R . - .
S . . .
T -
U . . -
V . . . -
W . - -
X - . . -
Y - . - -
Z - - . .
NATO Phonetic Alphabet
NATO developed a phonetic alphabet to help air traffic control and airplane pilots communicate messages by spelling words out using a phonetic alphabet. Basically, each letter is called out using a word that begins with that letter. For international flights, the message system defaults to this English phonetic alphabet, for use when pilots and air traffic control operators are from countries that speak different languages. When the pilots and air traffic control operators are from the same country (domestic flights) or from countries that speak the same language (Spain, most of South America, Mexico, Central America), the messaging system can revert to a national or shared-language based phonetic alphabet. The list below, created by NATO, is the international English version.
A - Alpha
B - Bravo
C - Charlie
D - Delta
E - Echo
F - Foxtrot
G - Golf
H - Hotel
I - India
J - Juliette
K - Kilo
L - Lima
M - Mike
N - November
O - Oscar
P - Papa
Q - Quebec
R - Romeo
S - Sierra
T - Tango
U - Uniform
V - Victor
X - X-Ray
Y - Yankee
Z - Zulu
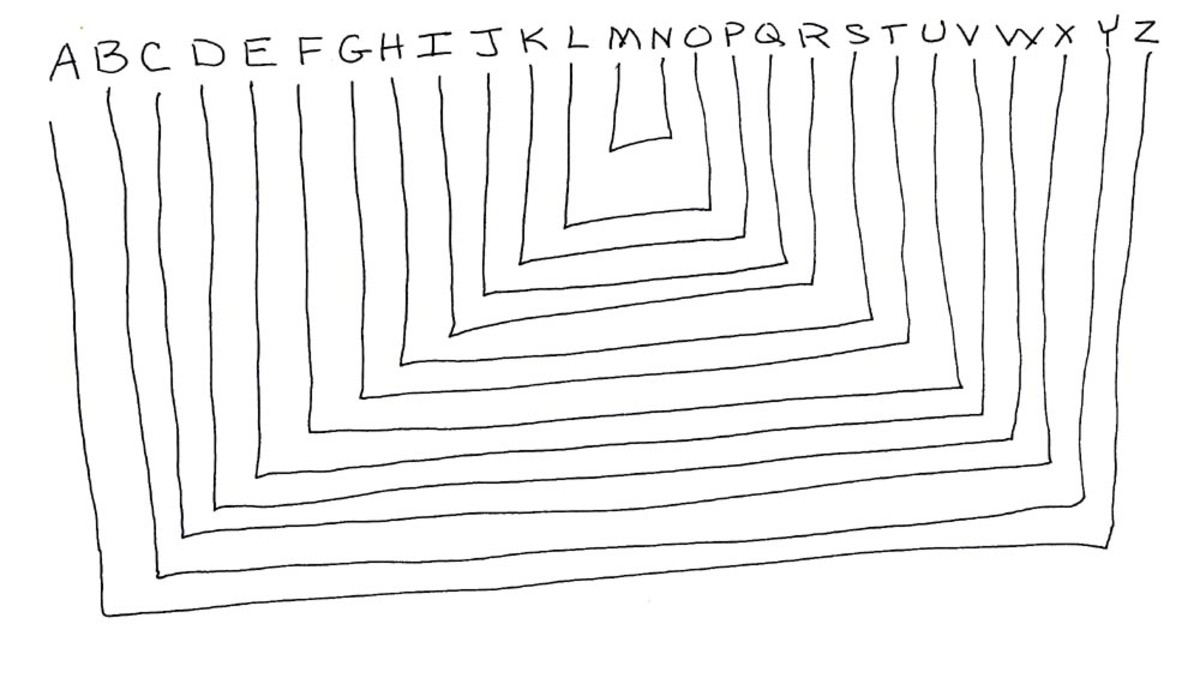
Substitution Ciphers
In cryptography, there are many forms of substitution ciphers, too numerous to count. One of the easiest is a simple substitution cipher where one letter is replaced by another. Usually a key to the solution either accompanies the cipher or is agreed upon in advance between the sender and receiver. The key might read 1 = 3, meaning the first letter of the alphabet is replaced by the third letter of the alphabet (a is replaced by c). The rest or the alphabet follows suit, with each letter being replaced by the letter three spaces later. Of course, this form of substitution cipher can be shifted in either direction and by any number of letters. Or a randomly generated, alphabetical substitution code could be created. The 1 = 3 substitution code would look something like the list below.
A = C
B = D
C = E
D = F
E = G
F = H
G = I
H = J
I = K
J = L
K = M
L = N
M = O
N = P
O = Q
P = R
Q = S
R = T
S = U
T = V
U = W
V = X
W = Y
X = Z
Y = A
Z = B
Letter Number Cipher
Another form of substitution cipher involves replacing letters with numbers. The most obvious and easiest, substitutes the letters with the number representing their placement in the alphabet. So 1 = A, 2 = B, 3 = C all the way through 26 = Z. The numerical substitution cipher can also be shifted or randomly generated.
Randomly generated substitution codes are more difficult to figure out. But if the message is spaced such that it reads like the original sentence, the receiver can look for patterns that correspond to common written English words and sentences, and decipher it from there. To make it more difficult, run all the words together. The person doing the deciphering not only has to decipher all the substituted letters, he or she has to figure out where the word and sentence breaks are as well.
The next time you need to send a message by code, cipher or signal, consider why you need to send it and who you're trying to reach. If you're sending a message just for the fun of it, try one of the "secret" messaging techniques, and see if the receiver can figure it out.