- HubPages»
- Health»
- Mental Health»
- Emotions
Cyber Bullying Hurts!

Online Bullying May Be New, But It Is Very Real.
Cyber-bullying is just as real as physical bullying and verbal abuse given in the real world. Some people might be inclined to dismiss it as something that happens online, but its effects can be just as hurtful as what is considered ‘normal’ bullying.
Bullies Can Hide Behind Their Avatars And Screens.
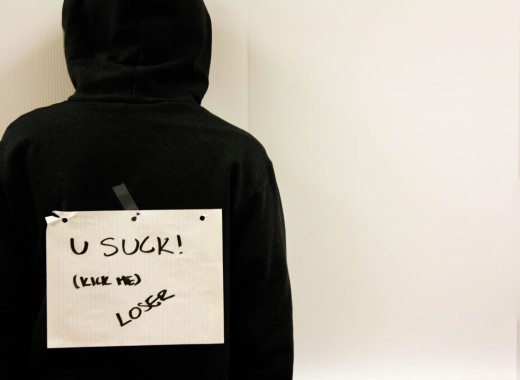
Cyber-bullying offers the perpetrators greater anonymity, so the bully may type offensive things they might be restrained from saying in real life. The bullies may also feel they are safer from prosecution than if they committed assault in the real world, although the law is being adapted to combat this problem. This can lead to them being extremely bold and cruel in what they post.
Cyber Bullying Is Technologically Enhanced.
Cyber bullies have the range of digital creative tools at their disposal. Hence they can add Photo- shopped images, ugly emojies or stream short movie clips on their posts. So imagine all the technology that has been developed for good - being used for evil.
Abusive Posts Are Highly Visible And Attract A Large Audience.
- Abusive posts are visible to everyone! While the whole world may not read any one bulletin board or be friends on the same social media, the potential audience is unlimited; and certainly far larger than in a corner of the playground or on a single street.
- Once a post is written victimising a person, it can often be viewed by peers, adding to the victim's humiliation. It may even be be accessed by complete strangers, exposing the victim to careless comments.
- Online “trolls” who are professional trouble makers may join the thread, bumping up its visibility and escalating the insults.
- Finally, persons who have no knowledge of the character of the victim may take sides.
Gossip And Innuendo Is Spread And Shared.
Abusive posts and images can be shared easily. For example, a short You-tube of a victim falling over may be taken on a mobile phone and have comical captions added. This may go ‘viral’ and be accessed by millions of people regardless of the embarrassment of the victim. If wielded with true malice, this could do a lot of damage to a person's reputation. It also makes the environment seem hostile and unsafe.
(Note, funny home videos are usually taken in good humour and with the subject's permission. They should not fit this category).

Online Hate Material Is Permanent In Nature.
Abusive posts are always visible. In some cases, the site administration will take them down if they are reported. However, too often, they remain somewhere in cyberspace and are accessible by a search. The victim knows that they can still be found and seen.
Online Material Is Continually Accessible.
Abusive posts are always accessible. The victim can view the posts several times a day, getting hurt every time. Unlike verbal insults, abusive posts do not fade from hearing. They may merely be pushed down the page by other posts, and the victim may keep receiving notifications that someone had added to them or replied.
Cyber Abuse Bypasses Physical Barriers.
Cyber abuse enters the home, destroying what ought to be a safe environment. Bullies cannot approach students physically once they have reached the safety of home and family, but messages can be sent to the victim’s mobile phone or posted on their social media. This represents an unprecedented level of access. The victim can be advised not to look at their phone messages or go online from home, but this represents a restriction of their natural activities.
Cyber Abuse Is Damaging To The Reader's Mental Health
- Cyber abuse may be damaging to the self-concept.
- It is never pleasant to hear criticism or gossip about one's self, and having read abusive posts could make even a healthy teen struggle to regain their confidence.
- Moreover, because of its pervasive nature, cyber abuse would seem likely to exacerbate any natural tendency to anxiety, and worry.
- Posts that suggest threat and harm, or speak of constant surveillance could even trigger paranoia.
This content is accurate and true to the best of the author’s knowledge and does not substitute for diagnosis, prognosis, treatment, prescription, and/or dietary advice from a licensed health professional. Drugs, supplements, and natural remedies may have dangerous side effects. If pregnant or nursing, consult with a qualified provider on an individual basis. Seek immediate help if you are experiencing a medical emergency.
© 2019 Cecelia