Investigation Landslide: Breaking Down The Doors of The Dark Industry of Child Pornography
Investigation Landslide
There are no two words in any culture’s vocabulary that send more shivers up the spine of a decent human being than "child pornography". For centuries it has been a dark reality in society that has been hidden in the seedy circles of pedophilia and has impacted the lives of millions of innocent victims. Until the invention of the Internet, commerce in the industry related to the trafficking of material related to child pornography was restricted to transports such as couriers and postal systems. Due to its nature, “the mail” made discovery of these perverted trade practices virtually undetectable. Enter the Internet.
Many blame the Internet for fueling widespread growth in the legal industry of pornography and, subsequently, the highly illegal industry of child pornography. On a micro-timeline, this notion could be debated for years. However, over the past decade it is my argument that the Internet served as the catalyst that encouraged pedophiles to surface to levels of visibility that has allowed some of the most aggressive progress in law enforcement against this dark side of our world. It all started with Investigation Landslide and the massive dent it put in this illegal industry.
In April 1999, the United States Postal Inspection Service of Texas received an internal complaint via a postal inspector who, in turn, had received the tip from an acquaintance in Saint Paul, Minnesota. The tip provided information to a website alleged to be advertising child pornography. The tip, however, referenced a photograph that was not being hosted in the United States—it was being served from Indonesia. This presented a challenge as to whether US law enforcement could actually prosecute the offense.
The mere occurrence of a complaint sourced from Minnesota ending up in Dallas was the random result of a friendship between the tipster and a postal inspector. The fact that one year earlier the United States Department of Justice had awarded a grant to the Dallas Police Department to house an investigative unit under the Internet Crimes Against Children Taskforce Program was a fortunate coincidence. Being aware of the ICAS office within the Dallas Police Department, the original postal inspector presented his finding and asked the local ICAS director to confirm his notion that the Indonesian-hosted photograph could not be prosecuted under US Federal Law. This is where the story turns from coincidence to “meant to be”.
The Dallas Police Department had established an unofficial relationship with several volunteers who worked in the local offices of The Microsoft Corporation. Though the relationship was not officially sponsored by the software giant, who had their own legal problems with the US Department of Justice at the time, the notion of helping local communities was highly encouraged at all levels of the company. When contacted by the Dallas Police Department to confirm the physical location of the offensive photograph, the company responded by volunteering employees.
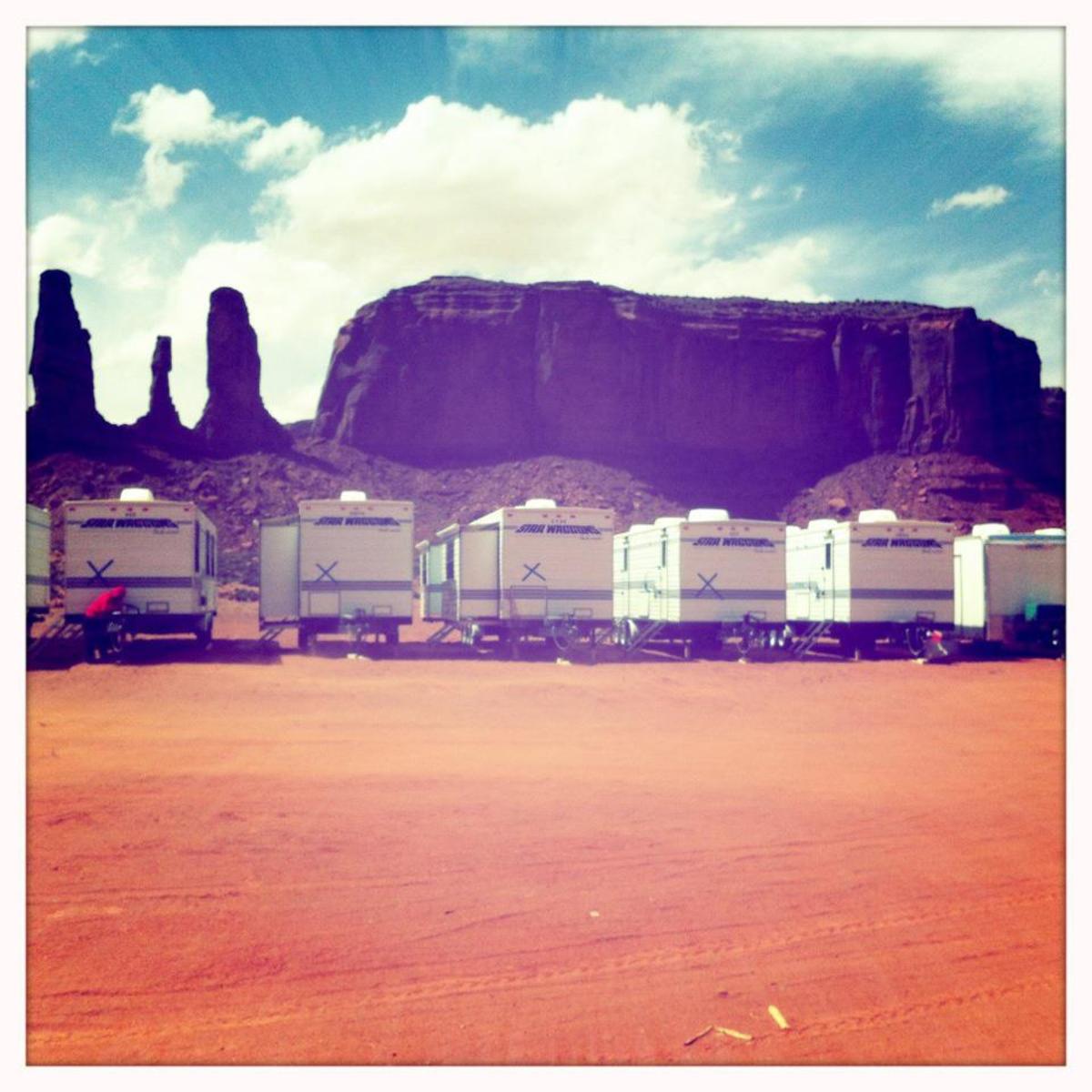
A software engineer from the company confirmed that the photograph was hosted via an Internet web server based in Indonesia. However, using a program called Web Buddy, the engineer uncovered a noticeable amount of traffic associated with the site hosting the photo that passed through an Internet Service Provider (ISP) based in Ft. Worth, Texas. The ISP was named Landslide Productions. After a lengthy investigation into the offending site, and the discovery of hundreds of other offenses, federal agents raided the Fort Worth-based Landslide Production on September 8, 1999.
Landslide Productions was owned and operated by the husband and wife team of Thomas and Janice Reedy. The crux of the raid was that Landslide Productions was selling subscriptions to a vast menu of child pornography sites across the world. The suspicions were nearly spot-on, as Landslide Productions was selling to a network of content providers who used the established Adult Verification System (AVS) combined with a proprietary payment system called Keyz to access a variety of pornography both legal and illegal.
As reported by British investigative reporter Duncan Campbell in his 2007 report entitled "Operation Ore Flawed by Fraud" , there was a set of complexities that were discovered in Thomas Reedy’s operation. A year earlier, Reedy claims to have discovered irregularly high volumes of stolen credit card transactions coming through his Keyz systems that were being processed by known webmasters and including Pakistani-based Imran Mirza and Brazilian hacker Antonio Francisco Tornisiello.
This posed multiple questions that had to be answered about Landslide’s payment operations. First, was Landslide in the business of selling child pornography subscribtions or was Thomas Reedy a victim himself? Second, what percentage of the customers in Reedy’s system were simply purchasing legal pornography as opposed to illegal child pornography; and, how many were simply the owners of stolen credit cards?
The first and most important question was answered during a federal a raid of Thomas Reedy’s Fort Worth, TX home which uncovered revealed emails on his computer that proved he was both aware and supportive of his payment system being used for child pornography. Second, a personal collection of child pornography was recovered from his computer (story in People Magazine). Thomas Reedy is currently serving 180 years in sentences related to the sale, distribution, and possession of child pornography. His wife Janice Reedy received a 14-year sentence (court transcriptions). The subsequent and more critical questions for future prosecution of potential pedophiles found in the Landslide databases would take years to play out.
The United States Department of Justice launched an official effort known as Operation Avalanche which methodically approached the recovered database with procedure-based law enforcement operated under the assumptions of “innocence until proven guilty” and that every US citizen is afforded rights under the US Constitution. The result was a solid law enforcement effort that vigorously and justly prosecuted hundreds of pedophiles in the United States. Furthermore, the operation resulted in precedents being established in the US for digital child pornography prosecution. Finally, the Landslide investigation was used to train hundreds of police departments in both the US and Canada on the prosecution of digital child pornography.
Unlike the United States, the United Kingdom, armed with a copy of the Landslide payment database, initiated an aggressive initiative known as Operation Ore that failed to distinguish the victims of credit card theft and consumers of legal pornography from those knowlingly purchasing child pornography. As reported by Duncan Campbell in several articles, the result was one of the biggest disasters in UK crime enforcement history and resulted in wrongful arrests and the destruction of the lives of innocent people. Many articles have been written about Operation Ore that point the blame at the Landslide investigation claiming foul play on behalf of the Americans involved including the inappropriate engagement of private sector volunteers and perjury during court proceedings.
The investigation of Landslide Productions was the result of fortunate coincidence and the persistence of local and federal law enforcement officials. In the United States, its result took child predators off the street and established the precedents and practices that have allowed our legal system and private sector (e.g. Dateline series) to make enormous progress against a problem that has persisted in society for centuries. The unfortunate actions of the United Kingdom have placed a dark cloud over the investigation into Landslide. Ironically, prosecutorial absence of due process was one of the inspirations that influenced our countries founders to break away from the UK in the first place. It is sad to think of the devastation the UK government’s actions had on innocent victims of credit card theft in that country. For the rest of us, it should be a lesson as to the dangers that lurk in the global Internet and the personal responsibility that we all have with regard to our personal information and the usage of financial instruments.
Derick Schaefer was an employee of the Microsoft Corporation and played a very minor role as a volunteer in the landslide investigation. As the founder of Orangecast, a Dallas, TX based Social Media marketing company, Mr. Schaefer is a regular contributor to Wikipedia, including the pages related to Operation Ore and Operation Avalanche. Mr. Schaefer has created a publicly available bookmark collection related to Operation Ore that can be found at http://del.icio.us/op_ore. His inspiration in writing this article was to present documented facts as to the accomplishments of the investigation of Landslide and Operation Avalanche that have been overshadowed by the flaws associated with Operation Ore.