How To Protect Your Credit Before And After A Security Breach or Hack
Published July 5, 2014
by Rachael O'Halloran
Protect Yourself From Security Breaches (Hacks)

Reaction Time
In light of all the identity theft and security breaches on the news in the last couple of years, protecting yourself and your personal information is now more important than ever.
Breaches do not only happen to large companies like Target and American Express. Small businesses are actually more vulnerable than large conglomerates because the hackers have figured it out - the small business owner feels safer from breaches so he doesn't have a lot of security bells and whistles for payment security, making it easy for the hacker to gain access.
Most people react after they hear about a breach or a hack. They will check their credit card and bank statements more closely or maybe sign up with an identity protection company like LifeLock to pay for an expensive service plan. Their costs can get pretty pricey as LifeLock explains what their many plans cover and the cost involved for each level. It is definitely not a "one price fits all" sort of business.
While the identity protection services are doing a thriving business, you don't have to be one of their customers because almost all of their services are free - if you do them yourself.
Now before you click off this article, let me assure you there is nothing - and I mean absolutely nothing - hard about doing this yourself. This article may be long, but that's because I have explained step by step and in very plain language how you can do this yourself. And, believe me, you can do it.
By doing your own monitoring, you won't be sharing any more of your identifying information with more people you don't know, nor will you have to pay a high fee to them for the privilege of being another hand in the pot. Your information already has plenty of eyes on it, most of whom you don't even know about.
So, instead of reacting after a breach or hack, the smarter thing to do would be to react before you hear about it.
Here's how to do it for free or almost free. It will require a little time and effort on your part, but your peace of mind will be well worth it in the end.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Follow The Steps And You Will Succeed

Why You Should Care About Security Breaches
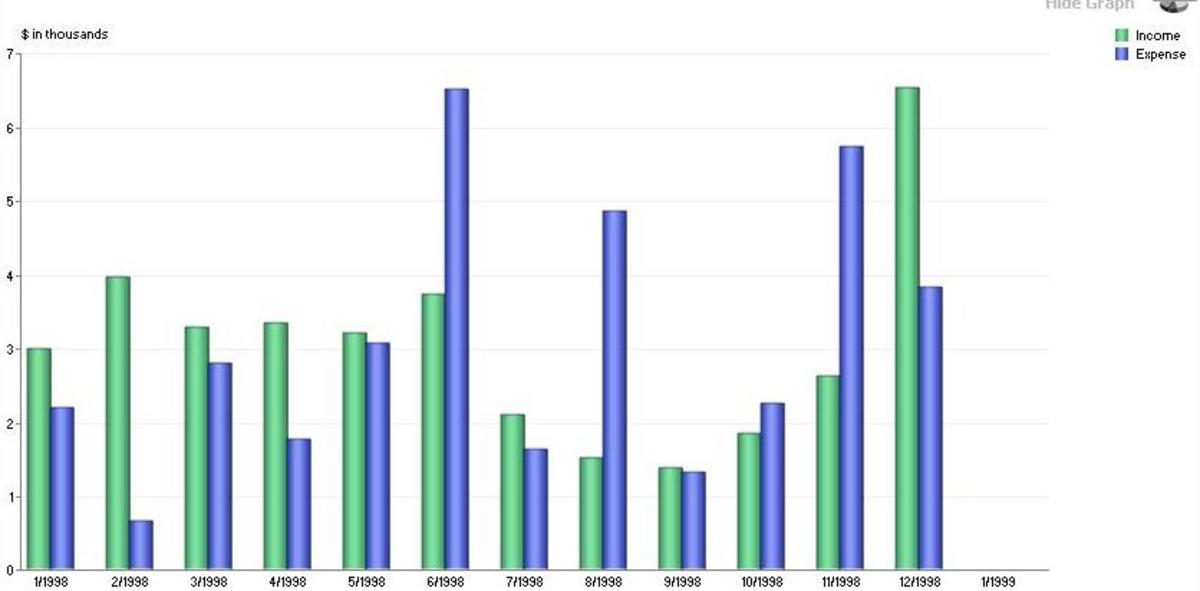
We have had an epidemic of security breaches and hacks in the past decade and more so in the last few years. In 2013, 63,437 known cyber incidents occurred, caused mostly by hacking and malware, according to Verizon 2014 Data Breach Investigation Report.
Every time a department store, a banking institution or a credit card company is hacked where consumer financial and personal information has been accessed (or stolen), we tisk at it if it doesn't affect us. But do we really understand what happened to those it did affect?
Here are a few statistics for you:
Since December 2012, American Express has reported more than 50 security breaches, mostly due to unauthorized access to merchant data and third party outsourcing. That is scary.
In 2013, 1 in 3 people who have had their data compromised by a breach suffered identity theft. In 2012, it was 1 in 9 people.
In 2013, 1 in 3 people who have had their data compromised had to be issued new credit card accounts. In 2012, it was 1 in 10 people.
In 2013, there were 614 data breaches that compromised the personal information of more than 550 million people.
Up to 110 million identities were compromised when retailer Target was breached in December 2013. The breach cost the banking industry $200 million because it had to reissue 21.7 million credit and debit cards. It also led to an estimated one to three million credit card numbers being sold on the black market at an average price of $18 to $35 dollars in the months following the incident.
--- from National Consumers League
Breaches do not only occur when someone hacks into your financial information via credit cards or banking institutions. Your computer and your mobile phone can also be breached in a number of ways, most notably through malware.
In 2004, Kaspersky Labs (a Russian security and virus software company) sealed their place as a premier virus protection service when they discovered "Cabir" which was, at that time, considered a malicious malware worm, infecting mobile phones and spreading through Bluetooth connections.
The extent of its maliciousness was that the worm depleted the phone's battery life within two to three hours and ran up the cellphone bill by auto-sending messages to premium-rate numbers (horoscope lines, adult talk lines, 900 area code numbers etc.)
Hackers and pranksters have come a long way since 2004. Malware is more malicious now than ever because these hackers are past fun and games. They are out for much bigger scores. They want cold, hard cash.
Step 1 - Place A Fraud Alert
A fraud alert serves a couple of functions but works best in conjunction with some of the other steps listed here. So don't do just this one step and quit. Follow through with monitoring your own credit report.
Here's how to put a free 90 day fraud alert on the three credit reporting companies Experian, Equifax, and TransUnion.
- Pick one from among the three links, fill out the online form to notify that one credit bureau and they will tell the other two agencies.
Now, for 90 days, if someone tries to open a new account in your name, the fraud alert will be one of the first things a vendor sees when they pull your credit report for the new account request.
Your fraud alert sends up a flare telling all creditors that they have to verify your identity before every transaction, before proceeding to talk to you on phone or in person, or before giving you any information or answering any questions you have about your credit card bill. If they don't do it, REMIND THEM!
If the person trying to open the new account is not you, this fraud alert should stop them from being able to succeed. Placing a fraud alert will buy you a little time until you can get to the Step 2.
Step 2 - Place A Security Freeze On Your Credit Reports
This is one of the best ways to protect yourself against identity theft - whether there has been a breach in the news or not, and whether your name was on their list or not.
A security freeze means that any NEW creditors will not be able to even look at your credit report or credit score in order to send you the thousands of credit card applications and insurance offers that the post office delivers to your house each year. (Also see "Opt Out" in Step 4)
- Did you know they look at your credit report before sending you all those pre-approved applications and advertisements? That's because they have to know you can afford to pay their bill and so they don't waste money on people who can't. (Even though most of their mail ends up in the trash). These companies access many credit scores to pick and choose who they send offers to. (Just more eyes who have no business looking at your credit information.)
The best part of a security freeze is that it also blocks anyone from being able to open up a new account in your name, thus stealing your identity. If they managed to slip past the fraud alert, the security freeze will definitely snag them.
My advice is to place the security freeze and fraud alert even if you followed my Step 4 and filed for the OPT OUT of offers of credit cards, mortgage refinancing and insurance policies. If one method happens to fail, any one of these other steps is extra layers of protection in a world where humans are primarily responsible for many security breaches.
The 90 day fraud alert and the security freeze are free to you. However, because of the many breaches recently, I read that some credit bureaus are either charging a fee or trying to limit you to one or two alerts per year.
However, if you have been the victim of identity theft or fraudulent credit or debit card charges, they cannot charge you. With some customer service reps, you have to stick up for that right.
Does The Freeze Affect My Mortgage, Car Payment And My Existing Credit Cards?
Any company which you presently have an account with is exempt from the freeze. The security freeze only applies to establishments that are new to you - where you don't have an existing account.
Now, this part is important ... If you decide you want to apply for any new credit - say, to buy or refinance a house, or new appliances or a car where you'll be making time payments - when a credit check is run to make sure you can afford the expense and if you qualify for a great interest rate for time payments, you will be declined because the security freeze is in place.
But don't worry, each credit bureau has a procedure where you can temporarily lift the freeze so you can buy your luxury, then put it back on when you are done. See the credit bureau links at the top of this page for the procedure.
Note: Unlike the fraud alert, each credit bureau will not tell the other about security freezes, so you will need to contact each of the three agencies individually when you want to lift the freeze and again to reinstate the freeze.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Don't Pay A Company To Do This Service For You

Step 3 - A Truly Free Credit Report
Under United States law, you are entitled to one free credit report per year. The average citizen doesn't take advantage of this privilege. It is surprising how many people have no idea what their credit report looks like or what their credit score is.
A step by step walk through on how to get it absolutely free is at annualcreditreport.com.
If you are not comfortable entering your personal information on a website, you can call annualcreditreport.com at (877) 322-8228 to request your credit report by phone. You will have to verify who you are with a short Q & A on the phone, and then your credit report will be mailed to you by regular post office mail.
You can also mail them a letter of request so you don't have to give any information over the phone or on their website by writing to:
Annual Credit Report Request Service
P.O. Box 105281
Atlanta, GA 30348-5281
For more information, click to read their FAQ's.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
What's On Your Credit Report?
Your credit report has a list of every financial account that is in your name (open and closed), all debts and late payments, every loan or mortgage you ever applied for, every bank account you have, and every credit card company and insurance solicitation that has ever accessed your credit report to see if you are worthy enough for them to send you their offers.
Recap:
A) Anytime you place a fraud alert with the credit reporting agencies, you are entitled to a free copy of your credit report from all three agencies, even if you already received your one free annual copy for that year.
B) If you have been a victim of Identity Theft or got caught in the net of a company who had their payment centers breached/hacked, you also are entitled to a free credit report each and every time it happens.
C) When you request a credit report, you must contact each of the credit companies one by one. They will not tell each other you want a credit report; that's not one of their amenities. When you request it, ask for the report to be mailed to your home, instead of sending it to you in an email or giving you a secure portal where you can just view it. You want the paper copy for your records.
D) Here's how to get three free credit reports per year instead of one free credit report.
- Select one of the three credit bureaus, ask for your report to be mailed to you.
- Then wait a few months and ask the next credit bureau to do the same.
- Wait a few months and do it again with the last of the three credit reporting companies. Make sure you tell each customer service operator that this is your one free annual credit report to which you are entitled from their bureau.
E) By staggering your requests, you won't be getting three credit reports delivered to you at the same time, each with almost the same information on them. The reason we have three is because one may pick up on some obscure credit issue that the others did not. By staggering them quarterly, you are getting three free credit reports at three different times of the year that most likely will have different information on them because of your activity.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Disputes On Your Credit Report (possibly ID Theft)
If you ever find fraudulent accounts or companies on your credit report, follow the company's procedures and give them as much information as you can about the charges. Don't speculate. If you don't know, then you don't know.
If you are the victim of identity theft, no matter if you just got your credit report last month, it is a law in every one of our 50 United States that the 90 day fraud alert and the security freeze are FREE.
Whether I need it or not, I personally place a 90 day fraud alert with each of the three credit bureaus at least once a year. I get a second free credit report from all three bureaus and it keeps their alert system on their toes shooting notification emails to me for strange activity. I set it up so they email me if there is anything suspicious so I can get busy checking it out, primarily with my bank and credit cards. If I have to, then I'll cancel a credit card to keep thieves out.
It is to your benefit to place a 90 day fraud alert at least once a year too.
You can contact them by phone, email, or by letter to make your requests. Visit each of their website links above to know what procedure and information they require of you in your request.
Beware and Be Aware
Scams are everywhere and there are new ones popping up every day. Scammers are counting on a caring person on the other end of the phone or email who will take pity on their plight. Whether it is a request to donate to what sounds like a national organization, or a plea for money from a friend of your grandson, don't click REPLY and don't agree to wire any money.
Legitimate, respectable requests for money do not come in an email or a phone call!
If you get a phone call saying the credit card you used Saturday night for dinner is part of a breach the restaurant reported, thank them and hang up. Call your credit card's issuing bank to determine if it is a fact.
Often these hackers will try to keep you on the phone so they can wheedle your PIN number, your social security number or date of birth out of you by reciting the wrong information so they can get you to verbally correct it.
Don't give them a YES or a NO. Hang up.
Call your bank and let them contact the restaurant or establishment to see if they are aware.
These examples are call PHISHING where they are out to trick you into providing the credit card, personal data or location information they require or to click on their links in an email which more often than not, leads to a cloned website (one that looks like the one you always use).
As soon as you put in your name and password, they have what they need. If you get a link in an email, there may be an attachment to download. The email may claim it is to "fix" or "patch," a vulnerability, but usually it is a virus or malware which can plant a keystroke logger to monitor your passwords and sign in activity OR give your hard drive a virus so that it can steal your personal information.
Don't be fooled by any popups or links who say you can get a free credit report. Often they have a membership fee if you forget to cancel by the opt out date or charge you a handling fee to get the free credit report.
Use the links I gave you in this article along with the other ways to get more than one free credit report per year. They are truly FREE.
Step 4 - Use "Opt Out"
If your credit report goes on and on for more than five pages or so, chances are you are the victim of mass mailing of credit card offers, mortgage refinancing, and health and life insurance solicitations.
Contact each credit bureau and ask to sign up for Opt Out. This will remove your name from the lists of all those pre-screened, pre-qualified, and totally unsolicited pre-approved credit card, mortgage refinance, life and health insurance offers you receive in the mail.
To opt out for five years, call 1-888-5 OPTOUT or 1-888-567-8688. You can also access it online at www.optoutprescreen.com.
To opt out permanently: Complete the Permanent Opt-Out Election form online at www.optoutprescreen.com. Then they will mail it to you for your signature (electronic signature will not be accepted in this case). Sign it and return it. Keep a copy for your records.
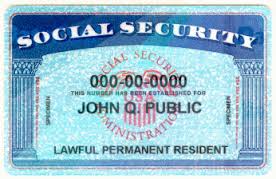
Know that the information collected online is confidential and will consist of your name, Social Security number, date of birth, home phone number and present address. Check the form when you receive it for signature to make sure all the data is correct.
If you don't want to deal with it online, you can call the phone number and ask for the form to be mailed to you. OR you can write a letter to request permanent opt out including the above identifying information so they know it is YOU! This link will give you more information about the pre-screened process.
HINT: All captcha letters need to be CAPITALS or the form won't submit.
Here are the addresses of the credit bureaus for OPT OUT only:
Experian
Opt Out
P.O. Box 919
Allen, TX 75013
TransUnion
Name Removal Option
P.O. Box 505
Woodlyn, PA 19094
Equifax, Inc.
Options
P.O. Box 740123
Atlanta, GA 30374-0123
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Step 5 - Watch Your Account For Fraudulent Purchases
Especially after an announced security breach, monitor your accounts very closely. Log in to your credit, debit and bank accounts and check all amounts, no matter how small they are, to make sure you made those purchases.
Hackers like to test cards with small purchases which the average person won't notice on the bill.
Call the card's Customer Service immediately if you see anything that is not your purchase. If you get an email telling you of suspicious charges, don't call any phone numbers in the email because they can be a phishing scam. Use the phone number on the back of your credit card or on your billing statement.
For added insurance, I use a free credit monitoring service called Credit Karma. They have saved my neck a few times with timely email notifications. I love them!
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*

Step 6 - Change Your Passwords
If you are affected by any security breach or hack of your financial, personal or medical information, as soon as possible - go to those websites and change your password.
Make it strong and make it long. Try to shoot for at least 12 to 16 spaces using letters, numbers and characters).
Do not use the same password for every website you visit OR the name of your child, pet, husband, (address) number or street, birthdate, or social security number.
I like to use the name of the site or account as my first letter of my password so when I look at them in my notebook, I know which one it goes to by looking at the first letter. Example: I use G for Google, B for bank, H for Hubpages, etc.
Then I make up a sentence. The hardest password to crack is one that uses the sentence method. Pick a sentence that applies to an event in your life or someone close to you.
For example, a Google password might use this sentence: Google the happiest day @ my life was my graduation day #65!
Your Google password will be the first letter of each word in the sentence, randomly alternating with capital letters, symbols and numbers.
In the example, the password is: GthD@mLwmGd#65!
You'll find yourself repeating the sentence every time you type in the password. Write it down (include your screen name) so you know which characters you used and which were randomly capitalized. If you don't have the exact sequence of capitals and lowercase, you'll be denied access.
Keep it in a safe place - preferably a notebook. Dedicate one page to each site.
Change passwords every week for 60 days after the breach, then every 3 months after that. Never use the same passwords over again. Make up a new sentence and proceed from there.
Get in the habit of clearing your browser cache daily and don't ever click the prompt "Save Password." It is convenient so you don't have to look up each password for each site you use, but passwords also store in your computer.
If your email or computer is ever hacked, the hacker now has access to your whole online life.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Step 7 - "Do Not Call" List
Credit card companies can call you on the phone about applying for a credit card.
Sometimes I would get as many as ten in one week!
Telemarketers call for every gadget and scam and they always seem to call when a meal is ready to be served.
If you find telemarketers and other calls annoying, register your phone number with the National Do Not Call Registry by visiting www.donotcall.gov or calling 1-888-382-1222.
The next time the same party calls me on the phone, I tell them the fine is $50 for every phone call they make to me and that my Caller ID is keeping track. I've succeeded in reporting Verizon, a collection agency looking for the former owner of my phone number (called night and day for over a month!), and two health insurance companies who were hoping I wanted to sign up for their medical plan. The government gets the fine money. I get the satisfaction in knowing the callers had to pay it because they publish it in the newspaper classified section.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Safeguard Your Social Security Number
Step 8 - Set Up Notifications
Many websites have an email notification sent to your email inbox if someone tries to log in to your account, especially if they have tried multiple passwords to get in and have failed. Facebook and Google shoot off an email rather routinely. Check your spam folder often.
I have received emails from Google for password reset because someone tried to get into my Google account, clicked the "forgot password" link and it generated an email to me prompting me to change my password. (Thank you to the dumb hacker for the alert)
I have used the "forgot password" feature myself when my password didn't work because I screwed up the number and letter capitalization sequence. So if you start getting auto-generated emails at a time when you are not online, you'll know someone is trying to hack your account.
Never click a link in an email for password reset that you didn't request. It may very well take you to your account, but more than likely it will take you to a phishing screen that was cloned to look like the site.
Manually type in the web address to navigate to the legitimate website, then change your password after you get there. Write it down in your password notebook.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Step 9 - Only Use Credit Cards or Cash
Of course, cash is always best but it's not always practical, so opt for credit rather than debit cards. While you may be very comfortable using debit cards so that the charge amount comes right out of your bank account, you have also given the hacker direct access to the funds in your bank account. Debit cards offer little or no protection over credit cards in the event of fraudulent usage.
Credit cards offer much more protection because not only are most card holders not liable for any amount over $50, but credit transactions can be monitored more easily and accurately. In the event of a breach, credit card companies (and the banks who back them) are notified first, usually within an hour of the breach. The US Secret Service says that debit transactions can take two weeks or more to detect.
Always carry multiple types of credit cards (Visa, Discover, MasterCard) so if one gets hacked, you'll still have other cards to use.
Don't get all your credit cards from the same bank. If one banking institution becomes compromised, you will still be able to use your other credit cards. Plus, your credit rating will improve if you use different bank offered credit cards and if you pay them on time.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Security Breach

Step 10 - The Banks Hate This, So Do Hackers
If you are the victim of an announced security breach, as in the recent Target, Michael's, Nieman Marcus, or P F Chang's China Bistro hacks, do yourself a favor and as soon as humanly possible, just cancel the involved debit or credit card with the bank and ask them to give you a new card.
By acting fast, when your card ends up for sale on the black market, it will be part of the percentage of cards that are worthless, thus driving down the hacker's validity rate.
For those who haven't read my other HubPages articles, the hacker's validity rate is his trustworthiness and reputation. It's a guarantee that the cards he is selling to black market buyers are valid and can be used.
The reason the hacker knows they are valid is because he went online and tested a percentage of each batch of 100 by making small purchases. If the majority of charges go through (accepted as payment), he rates his validity rate as 100%. If 3 out of 100 have charges that don't go through, those three are worthless and his validity rate drops from 100% to 97%.
Black market buyers look for high validity rates to decide if they want to spend a lot money on a batch of 100 credit or debit cards, knowing there are some in there they won't be able to use. If the hacker lies, he loses buyers' faith and trust in his word. That's why I wrote above to be alert for small purchases on your billing statements. As time goes on and more cards come up cancelled, the hacker has to drop his prices to get rid of the remaining cards fast before none of them are worth anything and he makes no money.
Chances are if the breach involved millions of consumers, within a week or two, the bank will be issuing you a new credit card number anyway. With the Target breach, the banks issued over 21 million new cards to customers in a little over two weeks.
If you cancel your credit card and ask for a new one, you will save your credit reputation and credit rating from possible identity theft or fraudulent charges.
On the flip side, when the hackers go to "test" a sample of the stolen cards, yours will come back as useless because you cancelled the account.
Your takeaway message:Cancel your credit card so that black market buyers find your card useless.
Can you imagine if everyone followed this advice and cancelled their credit card after a breach? Hackers would be really pissed that their big haul wasn't such a big haul after all.
Piss off a hacker as much as possible.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Do Not Copy

"Be careful out there." - Sergeant Phil Esterhaus, Hill Street Blues (1981-1987)
Thank you for reading :)
© Rachael O'Halloran, July 5, 2014
© 2014 Rachael O'Halloran