How to Assess Your Risk For Identity Theft and Take 5 Immediate Prevention Steps
Could You Fall Victim to Identity Theft?

Identity Hacking: It Can Happen to You
The voicemail came as a surprise during the busy holiday season several years ago: "This is the Fraud Department from American Express calling about questionable transactions on your account." Whoa. What?
As it turned out, my husband's corporate credit card had indeed been compromised. First, there was an innocuous $1 charge to see whether the card was valid. Quickly there followed $1,000 or so in charges for online merchandise.
An investigation revealed that it was an inside job at his workplace. Hundreds of other employees had already been affected.
What's worse is that between my husband and I, it was the fifth time our personal information had been stolen, lost, or accidentally shared by an organization we trusted. In 2005, our credit card information was compromised along with that of 40 million other Visa, MasterCard, American Express, and Discover account holders when an intruder gained access to a third-party credit card processor's payment database.1 This massive breach exposed us and others to potential identity theft.
That same year, I was among 12,000 government employees whose names, addresses, phone numbers, salaries, and social security numbers (SSNs) were accidentally published on the Internet. Oops.
Private Data Doesn't Always Stay That Way

In 2006, my husband and I were among the thousands of Wells Fargo mortgagees whose confidential data went missing along with a bank computer.2 Later that year, my personal and retirement data was exposed when five laptop computers were stolen from Towers Perrin (now named Willis Towers Watson), a firm that my employer had retained for HR Benefits projects.3 Ironically, Willis Towers Watson is an HR and risk management consulting firm.
Were we incredibly unlucky? I'd say! The upside, however, is that our experience has made us more cautious regarding what personal information we share, when, and with whom. The five data breaches we experienced involved organizations that had
- a false sense of invulnerability
- unchecked or unplanned for human error and
- a failure to maintain adequate safeguards.
As a smart consumer, recognize that no one is immune from identity hacking. No one. Ask the long list of celebrities who have had their identities compromised. Examples include Michelle Obama, Sarah Palin, Jay-Z, Beyonce, Kim Kardashian, Mel Gibson, and Christina Aguilera.4 If it can happen to them, can it happen to you? You bet.
It Happened Again and Again

The Bad Guys High Fived Each Other Over This One
Somewhere in Hackerland, whoever pulled off this computer coup is still high fiving his buddies. I'm so tired of the bad guys getting one up on the rest of us. But they are pretty smart.
Target announced in December 2013 that customer information had been stolen from 40 million credit and debit card users during the busiest shopping time of the year—from Black Friday to December 15. Compromised data included the card numbers, expiration dates, and the three-digit security code on the back of the card.7
Rather than immediately provide a complimentary one-year credit monitoring service, Target at first advised its consumers to monitor their own credit and immediately report any fraud. (They later came through with credit monitoring, but it took them way too long to respond to the crisis.) Credit card users are typically responsible for the first $50 in fraudulent charges but need to report the fraud in a timely manner.
So there we went again. No pun intended, but I felt like I had a target on my back.
Both my husband and I were among those 40 million shoppers, using two different credit cards! So that made our sixth (technically also our seventh, since two cards were involved) data breach since 2005.
We needed this data compromise like a third nipple, a unibrow, another ugly Christmas sweater, last year's fruitcake. You get the picture.
Is Someone Shoulder Surfing You?

Five Types of Identity Theft
Identity theft is a form of fraud involving unauthorized access and use of personally identifiable information, such as passwords, user names, financial or medical data, and confidential employment or educational information.5 According to the non-profit Identity Theft Resource Center, there are five types of identity theft:6
1. Financial
using another person's SSN to obtain a loan, credit card, or utilities
2. Criminal
impersonating someone else when dealing with law enforcement. Typically, this involves using the victim's SSN, name, and address to acquire a driver's license. The thief uses the stolen identity when s/he is cited or arrested. Then guess who has a rap sheet?
3. Medical
using another person's medical benefits card, Medicare identification, SSN or insurance number to gain prescription drugs or expensive medical treatment. Once the thief receives medical care, s/he lets the insurance company and the victim deal with the bills. Mix-ups in medical records are also a serious risk.
4. Governmental
exploiting stolen personal data to get public welfare benefits, government grants and loans, and to intercept tax refunds. It may also involve obtaining employment under another person's identity, especially for those not legally authorized to work in the United States or for those without the necessary licenses (e.g., impersonators of health care professionals).
5. Cyber/Reputational
using someone's name, image, or associations to damage their reputation or infiltrate their email or contact list.
There is a 1 in 4 chance that if your personal information is breached, you will become a victim of identity theft.
Odds are much higher if your Social Security Number is compromised.
No One Is Immune From Identity Theft

Reader Poll:
Has your personally identifying information ever been compromised?
Identity Theft Is an Expensive Crime
Identity theft is a $21 billion crime that affects more than 1 in 20 American adults at a rate of one incident every three seconds.8 Even children and the recently deceased are targets because in both situations the crime can often go undetected for extended periods of time.
Identity theft has increased as people bank and shop more online and rely more heavily on mobile devices—often without sufficient anti-virus/anti-malware or strong passwords. There is a 1 in 4 chance that if your personal information is breached, you will become a victim of identity theft. Odds are much higher if your SSN is compromised.
Still think you're immune? Unfortunately, both strangers, as well as people you know and trust, could be motivated to compromise your personal information for their own benefit. That includes co-workers, friends, and even family members.
Following are common methods that your personal information may be compromised, whether online, at home, in public, or in transacting business (see table below).
Make Them Work For It! Shred Those Documents

Methods for Gaining Unauthorized Access to Your Personal Data
At Home or Work
| In Public
| Through Merchants
| Through Trickery
|
|---|---|---|---|
Friends, family, or coworkers take information that is carelessly left out
| Your wallet, purse, or electronic device is lost or stolen
| A security breach at a school, medical facility, bank, or other business that collects your personal data
| Using emails, text messages, or phone scams, a thief tricks you into willingly providing personal data
|
Thieves "dumpster dive" for unshredded paperwork containing sensitive information
| A thief "shoulder surfs" (watches as you input passwords)
| Hacking, viruses, malware or spyware on your computer; websites with poor data security
| An imposter learns personal information about you through social networking sites
|
Thieves steal mail or divert it to another address to get account statements
| A card skimmer takes an imprint of your credit or debit card; you transmit personal information using a public Wifi hotspot
| An insider (e.g., waiter/waitress, bank teller) with access to your personal information steals it
|
Sources: Javelin Strategy & Research; Identity Theft Research Center
Identity Theft: Not a Victimless Crime

Share Your Experience with Identity Theft in the Comments Section Below
Violations of Trust
Even when your credit does not suffer, identity theft is not without costs. The disclosure of private information could be stressful or embarrassing, as when 1,000 private abortion records were discarded in a recycling bin, or when a national pharmacy chain's poorly designed smart phone app allowed access to other customers' identities and prescription histories.9,10
Data breaches may violate your trust and leave you wondering whether the full damage of the security breach is yet known. Additionally, investigations and fraud resolutions require your time and sometimes money to report and see through.
When an identity thief is prosecuted, the offense is typically penalized with up to 15 years in prison, a fine, and criminal forfeiture of any property that the thief used or intended to use to commit the offense.11
Oftentimes, there are other, related federal charges, depending on the nature of the fraud perpetrated. Examples include
- credit card fraud
- computer fraud
- mail fraud and
- wire fraud.
Prosecution is handled by federal prosecutors who work with the Federal Bureau of Investigation (FBI), United States Postal Inspection Service, United States Secret Service, and other federal agencies.
Data Thieves Want Your Personal Information

Who Is a Prime Target for Identity Theft?
Given the prevalence of identity theft and the associated headaches, recognize what makes a great target for an identity thief. Are you a prime target?
Likely targets may have certain characteristics as well as behaviors that make them more vulnerable to such exploitation. Characteristics include having 12,13
- an excellent credit history
- no criminal record
- personal or professional prominence (e.g., celebrities, corporate executives, people with access to key information)
- law enforcement background (see sidebar on "doxing")
- annual earnings exceeding $75,000; or
- being 18-29 years old, the most common age range for identity theft victims. College students frequently receive many credit card offers and fail to routinely review their financial records.14
Doxing: Dumpster Diving Goes High Tech
Hackers may comb the Internet looking for documents that contain personally identifiable information. When these bits of information are combined, an individual's identity is revealed. This is called "doxing," short for "document tracing"
The technique has been used to harass celebrities and to retaliate against law enforcement personnel who seek to crack down on computer hacking rings. For example, hackers gained access to a database of 7,000 law enforcement personnel and published the list of names, addresses, SSNs, email address and passwords on the Internet.
What's in Your Wallet?

These 11 Behaviors Make You Vulnerable to Identity Theft
Additionally, certain controllable actions can make you a likely target:
- writing down your PIN number on your ATM cards. This provides instant access to your bank account before you even realize it is lost. (The same goes for keeping the PIN in your wallet.)
- carrying too many credit cards, medical benefit cards, and your social security card with you in your wallet. When you leave the house, only carry what you will reasonably need. If you happen to lose your wallet, the chances of fraudulent charges will be lower if you have left extra credit and ATM cards at home. To facilitate reporting of a lost or stolen wallet, photocopy the backs and fronts of all important documents you may carry with you at any time, and keep them in a secure location. Your Social Security card belongs at home under lock and key.
- neglecting to review itemized charges on your credit card bills. You may not have recourse if you do not dispute the charge promptly.
- tossing credit card bills, receipts, medical bills, utility bills, and credit card offers directly in the trash or recycling bin. Instead, shred them first.
- failing to monitor credit - obtain a free annual credit report from each of the three consumer credit reporting companies (Equifax, Experian, or TransUnion) through www.annualcreditreport.com or by calling the companies directly. You may request the three credit reports either all at one time so that you can compare them, or you may space them out (e.g., every four months). Contact numbers: Equifax (1-800-685-1111), Experian (1-888-397-3742), and Trans Union (1-800-916-8800). If you decide to pay for an identity monitoring service, make sure it includes a public records check in addition to credit monitoring.
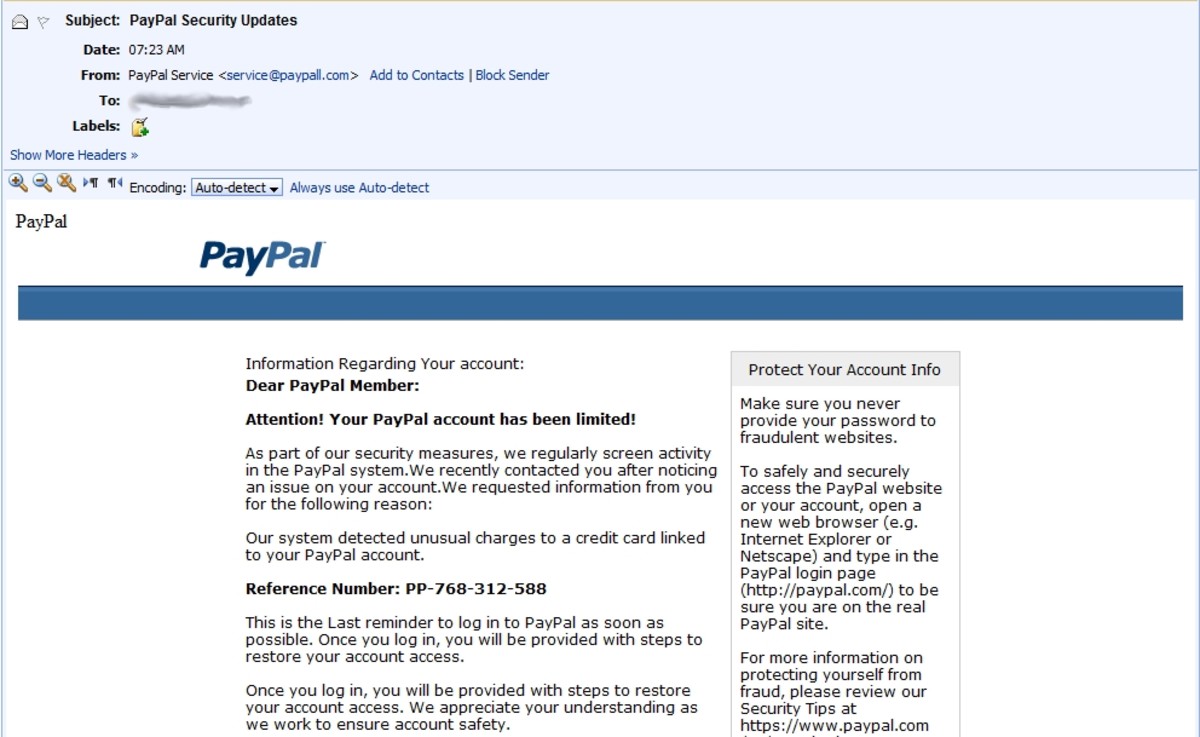
- responding to emails, texts, or phone calls requesting personal information - Never give out your private information over the phone unless you have initiated the call. Do not transmit personal data such as SSNs or credit card numbers through texts or email. If you receive suspicious communication requesting personal data (e.g., from your bank or credit card company), use established numbers that you already know. Beware of bogus job offers that seek to accumulate resumes and applications.
- failing to erase your hard drive and electronic devices before tossing/recycling
- placing your outgoing mail in unsecured mailboxes
- overusing "plastic" because of its convenience - Rather than pay electronically, consider using cash, especially for small and frequent incidentals. (You may enjoy the side benefit of spending less, too.) If you must use plastic, compare the liability for fraudulent charges by reading the terms of service for your debit vs. credit cards. Credit cards are usually preferable.
- regarding electronic security as too inconvenient - using weak or no passwords -- especially on a smartphone or tablet; not updating anti-virus/anti-malware; using public Wifi hotspots to transmit personal, financial, or medical information.
- ignoring calls from collection agencies or bill collectors as mistakes - This is often how people discover they are victims of identity theft.
Guard Your Personally Identifying Information

What Is Personally Identifiable Information?
Personally identifiable information is any data about an you that either alone or in combination with other data could potentially be used to identify, locate, and contact you.
Examples: your name, street or email address, phone number, SSN, medical/genetic data, fingerprints, financial account numbers, date and place of birth.
Who has your personally identifiable information? Lots of organizations: government, your financial institutions, schools, your employer, doctors, merchants, and utility companies, just for starters. Here are examples of where such information occurs so you will know when you are at risk (and what needs to be shredded):
- Bank, credit card and brokerage statements
- Credit card receipts and both new and cancelled checks
- Driver's License
- Car rental agreement
- Tax returns and supporting documents
- Vehicle purchase documentation
- Mortgage records
- Employment records
- Health insurance records
- Prescription labels
- Social Security cards
- Marriage, birth, and death certificates
- Electronic hotel key
Fight Back Against Identity Fraud

5 Immediate Action Steps To Protect Yourself
So now you're convinced that it can happen to you, and you want to ramp up your protection against identity theft. Where can you start? Here are five immediate action items to get you going:
1. Review the contents of your wallet to minimize the information you carry with you.
2. Purchase and faithfully use a shredder.
3. Opt out of prescreened offers of credit cards and insurance by mail. You can do this permanently or for a five-year period. The three national credit reporting companies operate the opt out service. To opt out, call 1-888-567-8688 or go to https://www.optoutprescreen.com.
4. Order your free credit report. Consider enrolling in a credit monitoring service. (I use Credit Karma which is free.)
5. Ensure that your passwords are strong and have been changed recently and make sure your anti-virus/anti-spy ware is current.
References
1Finkle, J., & Skariachan, D. (2013, December 19). Target cyber breach hits 40 million payment cards at holiday peak. Retrieved from https://www.reuters.com/article/us-target-breach/target-cyber-breach-hits-40-million-payment-cards-at-holiday-peak-idUSBRE9BH1GX20131219.
2Vijayan, Jaikumar. "Deja vu for Wells Fargo: bank loses computer with confidential data." Computerworld. Last modified May 8, 2006. http://www.computerworld.com/s/article/9000293/Deja_vu_for_Wells_Fargo_bank_loses_computer.
3Sutherland, Ed. "Retiree Data Lost in Laptop Theft." InternetNews - Software, Storage, Security, Server, Networking News for IT Managers. Last modified January 9, 2007. http://www.internetnews.com/security/article.php/3652901/Retiree+Data+Lost+in+Laptop+Theft.htm.
4 The Huffington Post. "Celebrities Hacked: Jay-Z, Beyonce, Kim Kardashian And Others Victims Of 'Doxxing'." Last modified March 11, 2013. http://www.huffingtonpost.com/2013/03/11/celebrities-hacked_n_2854786.html.
5Microsoft. "What is Identity Theft?" Microsoft Corporation. Accessed April 15, 2013. http://www.microsoft.com/security/resources/identitytheft-whatis.aspx.
6 Davis, Matt. "Identity Theft Resource Center Blog: Classification to Mitigation - What You Need to Know about the Multiple Faces of Identity Theft." Identity Theft Resource. Last modified October 3, 2012. http://www.idtheftcenter.org/Privacy-Issues/classification-to-mitigation.html.
8Javelin Strategy & Research. "How Consumers Can Protect Against Identity Fraudsters in 2013." Javelin Strategy & Research. Last modified February, 2013. https://www.javelinstrategy.com.
9Adler, Eric, and Judy L. Thomas. "Abortion files tossed into recycling bin - KansasCity.com." KansasCity.com. Last modified March 26, 2012. http://www.kansascity.com/2012/03/26/3516018/abortion-files-tossed-into-recycling.html.
10Protected Health Information Privacy. "Rite Aid mobile app left customer prescription history vulnerable – customer." Last modified September 27, 2012. http://www.phiprivacy.net/?p=10267.
11Department of Justice. "Identity Theft and Fraud." The United States Department of Justice. Accessed April 15, 2013. http://www.justice.gov/criminal/fraud/websites/idtheft.html.
12Smith, Ph.D., Eva N. "New Study Profiles Credit Card Fraud Victims." Credit Card Help Topics. Accessed April 15, 2013. http://www.creditcardguide.com/creditcards/credit-cards-general/study-profiles-credit-card-fraud-victims-221/.
13Identity Theft Awareness and Solutions. "High Target Identity Theft." Identity Theft Awareness and Solutions. Accessed April 15, 2013. http://www.identity-theft-awareness.com/high-target-identity.html.
14Dakass, Brian. "College Students Prime Target For ID Theft." CBS News. Last modified April 22, 2009. http://www.cbsnews.com/2100-501103_162-3188716.html.
© 2013 Elaina Baker