Apple/FBI Squabble Concerns Anything but San Bernardino

The most compelling topics are those on which many of us disagree. Liberty & security; nuance & fear – we’re not very good at keeping a sober perspective. We’re easily distracted by shiny objects; easily moved by impulse and emotion.
It is the job of our alphabet boys (and girls) to fight for more access and easier access to our personal information, more intrusion on our civil liberties. That is the role they have taken on, that is their raison d’etre – to keep us safe, of course.
It is expected that intelligence agencies would want to lap up every online search, every chat room discussion, every email exchange, every text, every call, every skype/facetime – to keep us safe...
It is expected that the FBI would want access to a cell phone which could provide evidence the investigation of a terrorist attack.

Unfortunately, it is also expected that the corporate media establishment will utterly fail at their raison d’etre - properly informing the American public. That they would instead exploit our fears in a cynical ploy to exploit our fears for increased ratings. For all of our feigned machismo, the American people are easily exploited by fear – which we simply cannot get enough of. We absolutely adore being terrified, so that we can be swept off of our feet by a strapping authoritarian father-figures who assuage our fears by promising to make the bad men go away.
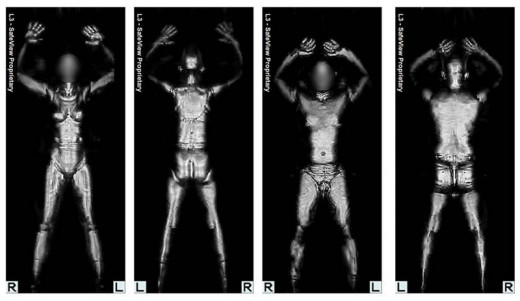

Inevitably, chasing away the bogeymen requires our acquiescing liberty for the promise of security. We were warned against such folly by our founding fathers, and yet, such has played out time and again. We were told to fear “Chinamen” so we outlawed opium and denied citizenship. We were told to fear Mexicans, so we (re-branded cannabis and) banned marijuana (sounds more ethnic). We were told to be terrified of the Japanese, so we locked away Japanese-Americans in internment camps and seized their property. We were terrified of black folks practicing their second amendment rights in California, so Saint Reagan signed an assault weapons ban. We were terrified after 9/11, so we started torturing people; we started locking people away without charge; we started assassinating American citizens without trial for saying “death to America.” We make our grandmas & granddads remove their shoes & belts while our sons & daughters are felt up by TSA agents.
Now the FBI is taking Apple to court, and public opinion seems to be split. Is Apple with ISIS? Or is Apple defending our privacy from an intrusive federal government?
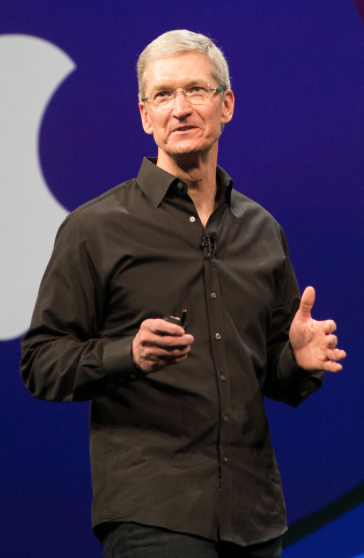




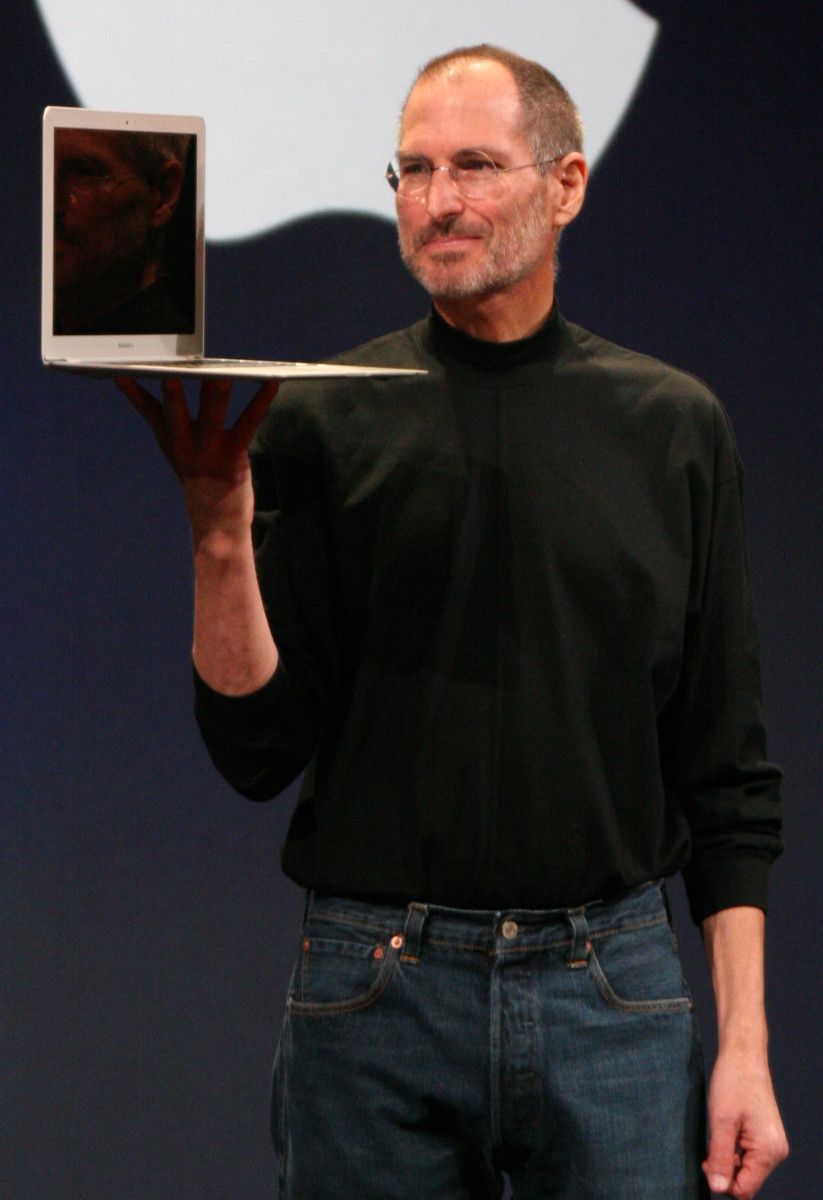
For starters, Apple is defending their bottom line – they have shareholders, after all. That said, Apple - specifically Apple CEO Tim Cook – is correct to deny a court order to comply with the FBI in this case.
The backdrop to all of this, of course, is the fact that the intelligence agencies have done nothing whatsoever to garner any level of trust. Leave aside J. Edgar Hoover, the Red Scare, MLK, the Movement, Watergate… They knew Bin Ladin was preparing to attack us, yet 9/11 still happened. They used falsified & misleading intelligence as evidence to illegally & senselessly invade an uninvolved nation, in Iraq. The Patriot Act immensely expanded their legal authorities (including turning the CIA from a spying agency into a killing agency) with the promise that they would be able to keep us safe. They didn’t see the Boston bombing coming. Didn’t see San Bernardino. (Didn’t see North Korea getting a nuke; didn’t even see the Arab Spring coming.)
While most of us have been unaware, the Crypto Wars have been waged for decades. Stands to reason, since most of us haven’t had personal devices with encryption capabilities for very long. The past few years though, following every “major” terrorist attack, alphabet boys are trotted onto cable news shows to fret about how that darned encryption might have kept them from preventing the latest attack.
When pressed, they are incapable of pointing to a single attack where either a “backdoor” to encryption (or mass surveillance in general, for that matter) has been used to thwart a major terrorist attack. Not. A. Single. One.
This fact does not keep them, however, from insisting. In this specific case, the FBI is in possession of Syed Farook’s work phone. It is inconceivable that a guy with forethought enough to destroy his personal phone would have used his work phone to communicate with terrorists (he wasn’t associated with any terrorists/organizations, he was simply inspired by online anti-American propaganda). Unfortunately for the FBI, said phone is password protected, and if the password is incorrectly guessed ten times, all data on the device is erased. Thus, the FBI wants Apple to create a backdoor/key in the form of malware that can be uploaded via iOS update which would disable said security function, giving investigators unlimited attempts at guessing the password. While the FBI insists that this “key” would only be used once, this is impossible to guarantee. Tellingly, NY District Attorney Cyrus Vance has 175 more iPhones he can’t wait to unlock – including one belonging to a person suspected of possessing meth - if the court order against Apple is successful (along with numerous other prosecutors, police chiefs, and the like across the nation).

This isn’t about San Bernardino at all, this isn’t about ISIS, this isn’t about terrorism or national security. The NSA already has access to all of the suspects’ communications. The DOJ already has its case, and the suspect is already dead. This is about legal precedent. The FBI/DOJ points to a law from the 1700s which compels third parties to hand over evidence. This is a different thing entirely. The US government wants to force a private company to develop technology which does not currently exist. Technology which, if created, would undermine the business model of a very profitable corporation. If the US government can compel Apple to undermine their security functions in order to gain access to a given device, so will China, so will Russia. Any government anywhere in the world could (and would immediately) demand access to anyone’s device they happen to be interested in. There would suddenly be numerous “keys” into everyone’s devices all over the world – easy pickings for hackers. The increased security features of each successive iOS model are a major selling point of the product. Undermining product security features at the behest of the government would inevitably lead to a decrease in sales (and trust).
Irregardless, encryption would still be in demand for those interested in privacy for whatever personal reasons. Foreign companies out of FBI reach would fill the gap in the market. The bad guys would simply buy new devices, rendering Apple's cooperation moot.

All of our communications, all of our contacts, our pictures, our passwords, our banking information, our health information - all of it is on our personal devices. We must demand a reasonable expectation to privacy. We must demand that code have first amendment protection. All of this little more than a workaround of that pesky 4thAmendment right to privacy which our alphabet boys so despise.