Book Review: Insurgency And Terrorism, From Revolution to Apocalypse by Bard E. Oneill
Many of the books on insurgency and terrorism that I have read are written for combatants, often by combatants from the perspective of tactical engagement of the insurgents and guerillas. Bard E. O’Neill is a former Air Force officer, and seems to be more intellectually than tactically inclined with stronger ties his intellectual academia background. He has earned a doctorate in international relations and teaches International Affairs in Washington D.C. at the National War College. Here he directs Middle East Studies and Studies of Insurgency and Revolution. Furthermore, he teaches in the Department of Politics at Catholic University in the nation’s capitol. To add to his already impressive resume, he has also served as a consultant for various high-ranking officials within the Department of State and Department of Defense (O’Neill, 231). His experience in politics is evident, as he has written several other books on US policy focusing on various topics. His expertise unveils the politics of insurgency to include its nature, strategies, organizational and support structures as well as popular support and the government’s response. While the book wasn’t written with specific attention to intelligence, it will be useful to the intelligence professional as it explains things that will be very much relevant when composing intelligence reports and identifies information that should be sought out whether or not it is requested.
O’Neill attempts to define insurgency discussing its goals and the strategies that may be adopted by various types of insurgencies based on factors including popular support, organization and unity, external support and the government’s response. Knowing the enemy’s objective and how he plans to achieve it is vital to conducting intelligence operations in a counterinsurgency or any other campaign. Recognizing the environment that the insurgents operate in is important as it affects his tactical options socially, politically and militarily. “Insurgency & Terrorism,” not being written with a focus on intelligence, offers discreet lessons to the intelligence professional intelligent enough to recognize their implicit nature.
There are several issues addressed throughout his book. O’Neill defines insurgency as:
“…a struggle between a non-ruling group and the ruling authorities in which the non-ruling group consciously uses political resources and violence to destroy, reformulate, or sustain the basis of legitimacy of one or more aspects of politics.”
(O’Neill, 15)
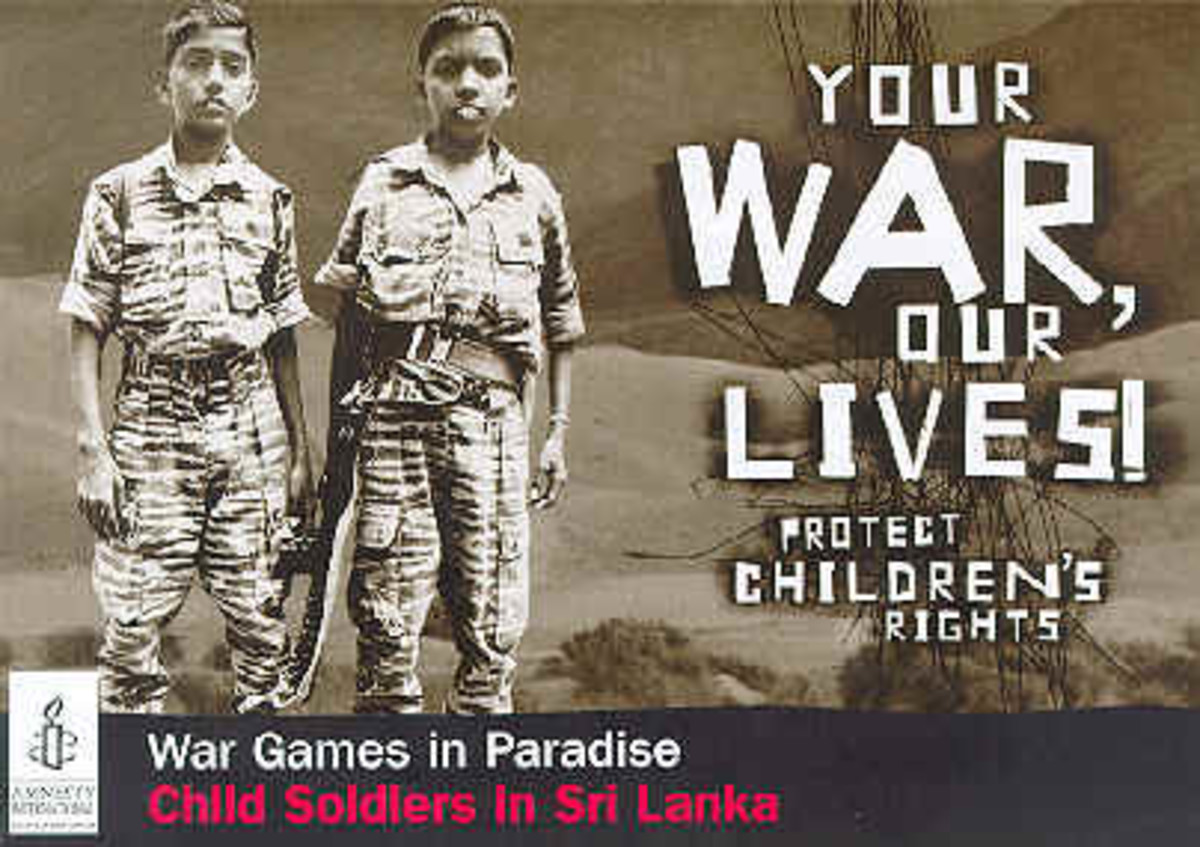
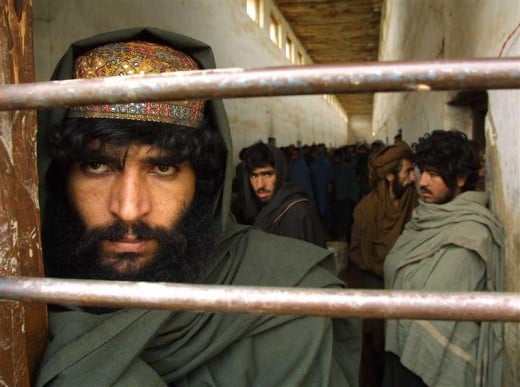
He goes on to identify and expound on several different types of insurgencies. There are anarchist insurgencies where the group believes that political systems should be eradicated and not replaced. Egalitarian groups strive to implement a system based on distributional equality and centrally controlled structures designed to mobilize the people and radically transform the social structure within an existing political community. Traditionalists advocate traditional values based on ancestry or religious foundations. Al Qaeda and the Taliban fit into this category. Apocalyptic-Utopian insurgents are the miscellaneous catch-alls of insurgency. They are in a category of their own because they don’t fit into any other group. It includes but is not limited to religious cults with political objectives. Pluralists set out to establish a system that stresses individual liberties and an autonomous and differentiated political structure. Secessionists seek to separate themselves from the political community, much like the Confederate states during the American Civil War. Reformists are non-revolutionary, but rather target policies determining the distribution of economic, psychological and political benefits of society. Preservationists are unique in that they engage in acts of violence against non-ruling groups and authorities that are attempting to bring about change. The Ku Klux Klan acted similarly by targeting civil rights leaders and members of the Black Panthers during the civil rights movement of this 1960s-1970s. Commercialists are the final type of insurgents that seem to be motivated primarily by greed as they seek to acquire material resources through seizure and control of political power. This is very much comparable to Mafia in the US and the blood diamond trade in parts of Africa. O’Neill goes into significant detail regarding each type of insurgency and how they go about achieving their objectives. This will make intelligence analysis much easier because it categorizes the often-ambiguous guerrilla styles that one will encounter in asymmetrical warfare. Painting a clear picture of the adversary and understanding their motives helps to form better plans on how to counter their actions.
As with conventional warfare, insurgent operations are affected by the environment, not only natural, but also the political and cultural environments as well; the human terrain so to speak. O’Neil discusses how the physical geography helps or hinders insurgents as with the Ho Chi Minh forces and PLO respectively. The human environment, which includes the population’s demographic distribution, social structure, economic factors, and political structure among other things, is also a significant factor in the success of an insurgency.
O’Neil identifies major aspects of launching an effective insurgency and pitfalls the government needs bear in mind when attempting to launch an effective counterinsurgency operation. There is an entire chapter dedicated to this and will have HUMINT collectors and interrogators better prepared to make the most of information that they come across and to uncover relevant information when working their sources. At the end of the book, O’Neill concludes, “…the analysis of insurgency is a complex and challenging undertaking that [decision makers] must approach in an organized way and with an open mind.” (O’Neill, 203) The approach will be strongly influenced by intelligence that is gathered at the tactical level. Having all of the facts would be best, but such an ideal situation is very unlikely, however, having much of the information will contribute to the organization and further analysis of new information as it becomes available.
This book is presented in a clear, concise manner that prevents being bogged down by wordy “pentagonese” or military jargon as is common among works written by experienced and advanced tacticians. It has a professional presentation while at the same time engaging the reader by not breaking things down so far as to insult the audience’s intelligence, or as we say in the Corps, “Crayola Style.” O’Neill keeps his writing to the point and remains succinct while making a point not to be overly theoretical though he occasionally touches on conjecture. The pages full of endnotes after the summary of every chapter exhibit thorough research pulling from an eclectic variety of sources rather than relying heavily on only a few books, publications or case studies.
I can detect no bias in the writing style or tone that O’Neill uses. His background is more political than tactical, so it’s clearly apparent that he doesn’t have too much to do with ground pounding as it stays at the upper operational and strategic level of counterinsurgency operations. His book is written to cater to the audience that is more likely to counter an insurgency than to start their own. Beyond that, there are no evident political or ideological leanings. He sets out to present a straightforward and objective analysis of insurgencies and succeeds in doing so.
O’Neill’s book offers a good basis for understanding insurgencies and how they work. It could be better if it offered methods for achieving the logistic systems that allowed insurgencies to fund and arm themselves. Based on what is written, it would take a seasoned tactician who is politically inclined and “intel-savvy” to effectively work against an insurgency. It is by no means an all inclusive “bible” but definitely a good foundation. For intelligence professionals in counterinsurgency operations, this book should be combined with other works that go into more detail once the reader has developed a base of knowledge needed to process and understand more advanced subject matter.
“Insurgency & Terrorism” is an enlightening book that unveils exposes the reader to the larger submerged portion of the iceberg that most civilians simply refer to as call “terrorism.” It breaks insurgency down to the rudimentary elements and explains what makes it effective in some cases and ineffective in others. Essentially it provides the keys for winning the Global War on Terrorism although the socio-politico-military environment doesn’t necessarily allow us to symmetrically engage an asymmetrical force. For example, we can’t fight terrorism with terrorism and execute all of the Taliban’s supporters in the Middle East. Regardless of the limitations, this book identifies enemy strengths that often go unnoticed. The current generation of warriors and politicians can utilize it during times of peace as a playbook to lift restrictions that have hindered us in this endeavor to effectively eliminate terrorism and insurgency in the Middle East. Unfortunately the intelligence applications within its pages are implicit and must be sought out by one who can recognize the elusiveness and therefore the value of what they do not yet know.
O’Neill, Bard E. 2005. Insurgency & Terrorism: From Revolution to Apocalypse. Washington, DC: Potomac Books.
In the Wake of Terrorism