Don't Fall for These Phone Scams

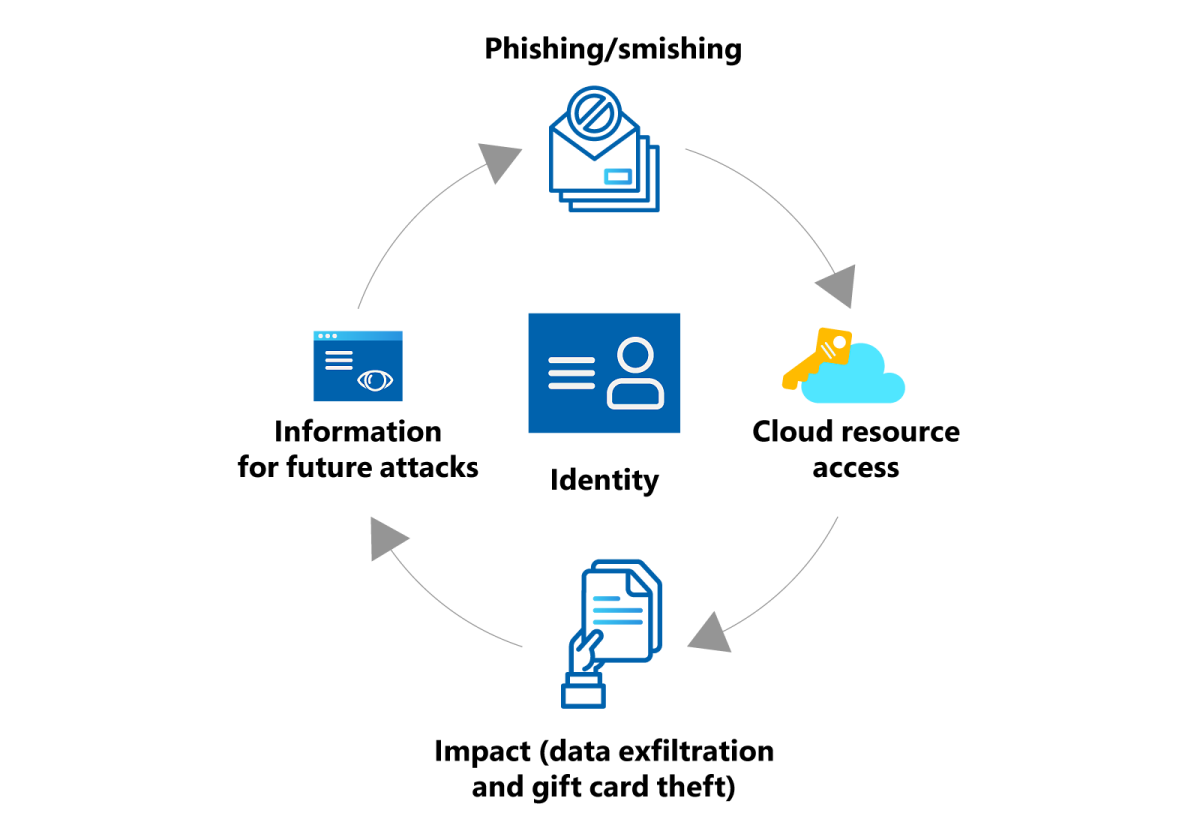
It is a sad fact that, in this age of technological wizardry, the crooks have kept pace with the good guys. This is particularly true for scams that are carried out over the phone, as this instrument maintains a level of distance and anonymity; perfect working conditions for for the scammer.
But forewarned is forearmed, as they say, so in the fashion of the TV show The Real Hustle, I will present details of three scams that you should be alert to, in the hope that this will prevent you, or someone you know, going through the pain of being ripped off.
All three cons involve manipulation via the telephone at some point. To demonstrate how they work, and what you should look out for, let me describe the scams using the fictitious householders, Tom, Dick and Harry.

1: The Mistaken Delivery Scam
Tom receives a package that contains a state of the art mobile phone. He doesn’t know why it has been delivered to him, as he never ordered it. Just as he wonders what to do about the delivery, he receives a phone call from the company that sent out the phone (or phones – this scam often involves orders of multiple items). The apologetic caller tells Tom, in a polite and professional manner, that the phone was sent to his address in error, and a courier will call later that day to collect it. The two parties arrange a time for collection, and the courier calls to take away the package. Tom thinks no more of the matter – until he receives a bill for the phone.
What had happened is that the crooks had genuinely ordered the phone using Tom’s details, which they had somehow obtained. So the phone that was sent out had, on the face of it, been ordered through legitimate channels, and a bill was issued. The con men swooped down and grabbed the phone before anyone was even aware that something was amiss. They were long gone by the time Tom realised he’d been duped.
How Safe Are You?
Do you think you are equal to the sophisticated methods of the phone scammers?
2: The Premium Rate Call Scam
Dick finds a card on his doormat that has been posted through the letterbox. The card informs him that a courier tried to deliver a parcel to his address, but there had been no reply. There are then instructions for Dick to call the number printed at the bottom of the card in order to arrange redelivery. Dick makes the call, and he is kept waiting for some time. Eventually, he gets the feeling that the party at the other end is stalling and deliberately stringing out the length of the call. Finally the call is ended without there being any redelivery arrangements made. This is because no such parcel ever existed. The entire operation was a scam, and Dick fell for it completely.
After the call, Dick had gone about his business without another thought to the incident – until he received his phone bill. The call, which had lasted seventeen minutes, had cost him a tidy sum.
Con men often set up premium rate phone lines that charge a lot more than the standard rate.. Once the line is established, they need a steady supply of people to call, so that the money will flow in. What better way to achieve that goal than by putting innocuous looking cards through hundreds of doors telling householders they have missed a delivery?
If you receive such a card when you are not expecting a parcel, check the number with your telephone company. If it is a premium rate number, it should be avoided.
Check Out This Premium Rate Phone Line Scam

A Fun Phone Scam You Can Try
Here’s a phone ‘scam’ you can try on your friends for fun. You’ll need a deck of cards and a friend in a remote location (at home, outside the building or in the next room; anywhere he or she can’t be seen or heard while you are perpetrating the ‘con’). Here’s how it goes.
You announce to your friends that you have discovered a remarkable mind reader known as The Master. You add that this virtuoso of vision has the amazing power to tell which playing card has been chosen from a deck – without being present in the room.
To demonstrate, you ask a friend to pick a card from the deck, and he chooses the seven of spades. You dial a number and ask to speak to The Master. A few seconds later you hand the phone to the person who chose the card. He puts the phone to his ear, and a voice says;
“You chose the seven of spades.”
Your friends are impressed, and everyone wants a try. Each time the trick works perfectly – but how?
It’s simple really; you just need to drill your accomplice in the set up. It all hinges on how you ask to speak to The Master. Here are the four versions – I would ask you to pay particular attention to the opening letter of each request.
1) Hello, could I speak to the Master?
2) Sorry to trouble you, but could I speak to The Master?
3) Do you think I could speak to The Master?
4) Could I speak to The Master?
As you can see, the opening letter of each of these requests will tell your accomplice the suit of the chosen card. Armed with this knowledge, he or she will slowly and quietly name the cards in the suit, starting at the ace. When they come to the chosen card, you stop the count with an innocuous exclamation. Here’s how it would work in the situation described above.
YOU: Sorry to trouble you, but could I speak to The Master? (this tells your accomplice that the card is a spade)
ACCOMPLICE: Ace – two – three – four – five – six – seven –
YOU: Hello?
You hand over the phone, and the correct card is called.
Try it – it’s pretty cool when it comes off.
3: The Don't Hang Up Scam
Harry gets an unexpected phone call from an electrical goods retail outlet. The caller informs Harry that an attempt was made to purchase expensive goods using his debit card, but the store clerk had become suspicious and blocked the sale. Harry is obviously worried by the news, and the voice on the phone advises him to call his bank immediately, using the number printed on his debit card.
Harry does this and he gets put through to the fraud department. The bank official tells Harry that it would be best to move his money temporarily into a new account until the problem is resolved. In order to do this, Harry must give details of his current bank account.
A few days later, Harry learns that no new account was ever set up, and his existing account has been cleared out.
Here’s how it worked.
The initial call did not come from an electrical goods retailer, but from the scammers. The bogus story of the attempted purchase alarmed Harry so much, he rang the bank immediately – or at least the thought he did. When Harry hung up the phone, the scammers did not, so the line was still connected.
The next stage of the operation involved a degree of risk and sophistication.
When the scammers heard Harry lift the receiver, they played the sound of a number being dialled, followed by a ring tone down the mouthpiece of their phone. After a few rings, and some 'on-hold' muzak, someone pretended to answer (in a very business-like voice). Harry genuinely believed he was speaking to an employee at his bank, and so his guard was down. He had played right into the hands of the scammers, who gleaned his bank details in order to steal money from his account.
Wise up to more scams here:
Forewarned is Forearmed
The main reason that these scams work so well is that they have a disarming aspect to them, because in each case, the victim is unaware that any criminal activity is taking place until it is too late. Tom, the victim of the premium rate phone scam, had not been asked for money, and he had the reassurance of knowing that if he felt the package (which didn’t exist, remember) was at all suspect, then he could refuse to accept it.
Similarly, with the mobile phone scam, Dick was never asked to pay any money, and he considered that, as he had the valuable items in his possession, this was a genuine error, so he happily handed the package over to the courier.
Harry thought he was dialling the number printed on his debit card. He thought he was acting to prevent money being taken from his account, when really he was unwittingly giving it all away.
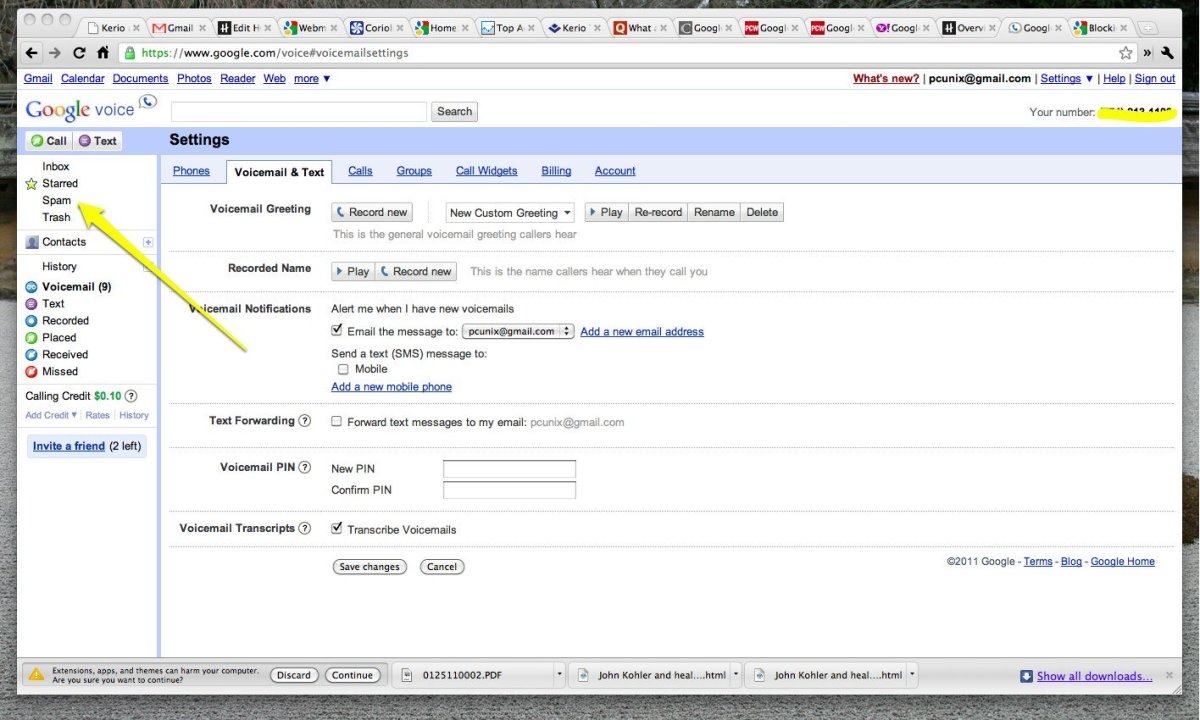
The best way to protect yourself against these scams is to be alert to them, and if you receive a package, or notification of one, that you are not expecting, treat it as suspicious. As for the mobile phone scam, you can stop the crooks getting their hands on your details by tightening up your own security. Destroy or shred all unnecessary documents that could give the crooks information, and store sensitive documents, bank statements etc, in a safe, secure place. Never reveal or write down PINs or email passwords.
These scammers are cowards, and they prey on the elderly and vulnerable, so do keep an eye out for those you know who may not be able to spot the scams themselves. Best of all, if you do receive an expensive mobile phone that you hadn’t ordered through the post, contact the police after you’ve arranged a collection time with the bogus courier. I’m sure they would like to be present when he or she calls.
Stay safe, and be alert.