Is Big Brother Watching? You Can Probably Count on It

If the title of this article raises suspicions of paranoia, perhaps you haven't been keeping up with events in recent years – particularly the AT&T wiretapping scandal and the revelations of National Security Agency leaker Edward Snowden.
On the other hand, perhaps you're equally "paranoid" ... and have an uncomfortable sense that the sinister ultra-surveillance world of George Orwell's 1984, with a ubiquitous, omniscient Big Brother tracking our every move (and thought), is rapidly morphing from prophetic fiction into reality.
After all, we already know that the big corporate and government elite, at the controls of our society, are definitely tracking us – or at least they have the capability. Plausibly, it's quite likely they actually are tracking just about all of us, one way or another.
Now, maybe you're not bothered by any of this — maybe you think you've got nothing to hide? And so, if corporate bigwigs and government snoops want to peek on what you're up to at anytime, you're OK with that, right? But many among the rest of us value our anonymity and privacy ...
Unfortunately, we're fighting a defensive action – very defensive, indeed. And by and large, we seem to be losing. Major corporate execs, as well as top law enforcement authorities, regard any right to privacy as a kind of vanishing pipe dream.
“I think anonymity on the Internet has to go away” – Randi Zuckerberg, marketing director for the Facebook social networking empire, caused quite a stir when she asserted this in a professional meeting back in 2011. But she undoubtedly exposed the prevalent mindset of more and more of the techno-elite. For example, Google's former CEO Eric Schmidt has similarly called online anonymity “dangerous”, predicting that government authorities will eventually “demand” that we all be forced to expose our real names in all online activity.
The dimensions of the attack on personal privacy and anonymity are staggering – and it's routine, it's commonplace, for every single one of us, not just for those that are being intensively scrutinized. Even if you've had some awareness of the spread of surveillance lately, the full, multifaceted array of these intrusions into our personal lives can be somewhat overwhelming. So here's just a summary of highlights:
Unleashing the government
• Since 2001, the USA PATRIOT Act has allowed authorities to search your home or business without your permission or knowledge; it's allowed the FBI to search your phone, Email, and financial records without a court order; and permitted law enforcement authorities to poke through your other personal and business records, including what you've seen or checked out at the library, and your financial records such as your bank accounts and credit cards.
• Every single time you send an Email or text message, perform a Google search, or visit a Web page, there's an excellent chance that you're being tracked in some fashion by computers of the National Security Agency (NSA) – all on the pretext of the so-called “War on Terror”. And huge mega-corporations like AT&T are surreptitiously cooperating with government authorities to facilitate this.
What happened to particularly clue the American public to all this massive government cybersnooping was that it was eventually exposed publicly by Bay Area AT&T worker Mark Klein (just before he retired). And the volume of information the snoopers are accumulating is vast – in both Utah and Texas, warehouses the size of small towns are being developed by the NSA to store copies of literally trillions of American citizens’ private Internet page views, downloads, Email posts, and other "suspicious" items of cyberinformation.
• Now, even without the Patriot Act and this other recent ultra-snoopery, government operatives had their ways of tracking most of us if they wanted to. Take credit card records, for example – law enforcement authorities (e.g., government prosecutors) have routinely relied on these to check on the whereabouts of targeted individuals.
• Likewise, airline tickets have represented another lucrative means for both corporate and government snoopers to track individuals' travel patterns (and another "security" pretext for the government to poke into your personal background, including your financial records).
Internet snoopery
• And back to the Internet ... Of course, just about everyone has already known that we're all being carefully tracked by Google, Microsoft, and numerous other cyber-giants (you've surely heard of "cookies"?) ... and your Internet Service Provider, among a whole array of other robot eavesdroppers, tracks where you go and what you see on the Internet by conveniently following your IP address.
• Social networking sites ... Billions of Internet users worldwide expose all kinds of incredibly personal information on sites like Facebook — including photos of their most intimate physical attributes. Mix that with what seems to be a haughty corporate disdain for privacy, and you get aggressive tracking of both Facebook members and non-members (including unsuspecting visitors to the website) alike: "Facebook officials are now acknowledging that the social media giant has been able to create a running log of the web pages that each of its 800 million or so members has visited during the previous 90 days" reported USA Today on 16 Nov. 2011. "Facebook also keeps close track of where millions more non-members of the social network go on the Web, after they visit a Facebook web page for any reason."
Cellphone/smartphone tracking
• Then there's your cellphone, by which you're being constantly tracked, whether or not you're even actually using it — every several seconds, the phone is "pinging" your location to the nearest cell tower, and records of your whereabouts are being kept. (This has figured in quite a number of juridical criminal cases, such as those featured as real crime stories on NBC's Dateline or CBS's 48 Hours.) And, of course, the records of whom you actually talk with (via incoming or outgoing calls) are also kept.
• And with the popularity and near-saturation of smartphones, tracking on all levels has virtually exploded, becoming routine and virtually constant. A couple of headlines and ledes from news articles in recent years say it all. Huffington Post (1 Dec. 2011), "Is Your Cell Phone Spying on You?" by Josh Levy: "Are you being watched? ... An independent researcher just discovered a hidden application that records what millions of people write, view and search for on their mobile phones. It sends all of that data to a company no one's ever heard of. And we have no idea what that company is doing with our information."
And Discovery (1 Dec. 2011): "Is Your Cell Phone Spying on You? ... More than 140 million Android, BlackBerry and Nokia phones may be watching their owner's every move."
For government snoopers, smartphones offer an extra bonus: Not only can the where, when, and with whom of your calls be tracked, but your actual text messages – months or possibly years in the past – can be retrieved. (So, happy texting and sexting!)
Tracking your car
• Turning to your car: Government snoopers increasingly have been mining sources such as toll plaza records and even traffic camera data to record and track license plate data, thus tracking (at least partly) where you travel in your own motor vehicle.
• But such tracking is quickly being exponentially enhanced via the installation of automotive "black boxes" in cars – vehicle information recorders similar to those on airliners (except that supposedly, your personal conversations aren't yet being recorded). These can be interfaced with GPS technology to record not just your car's condition, but where you go.
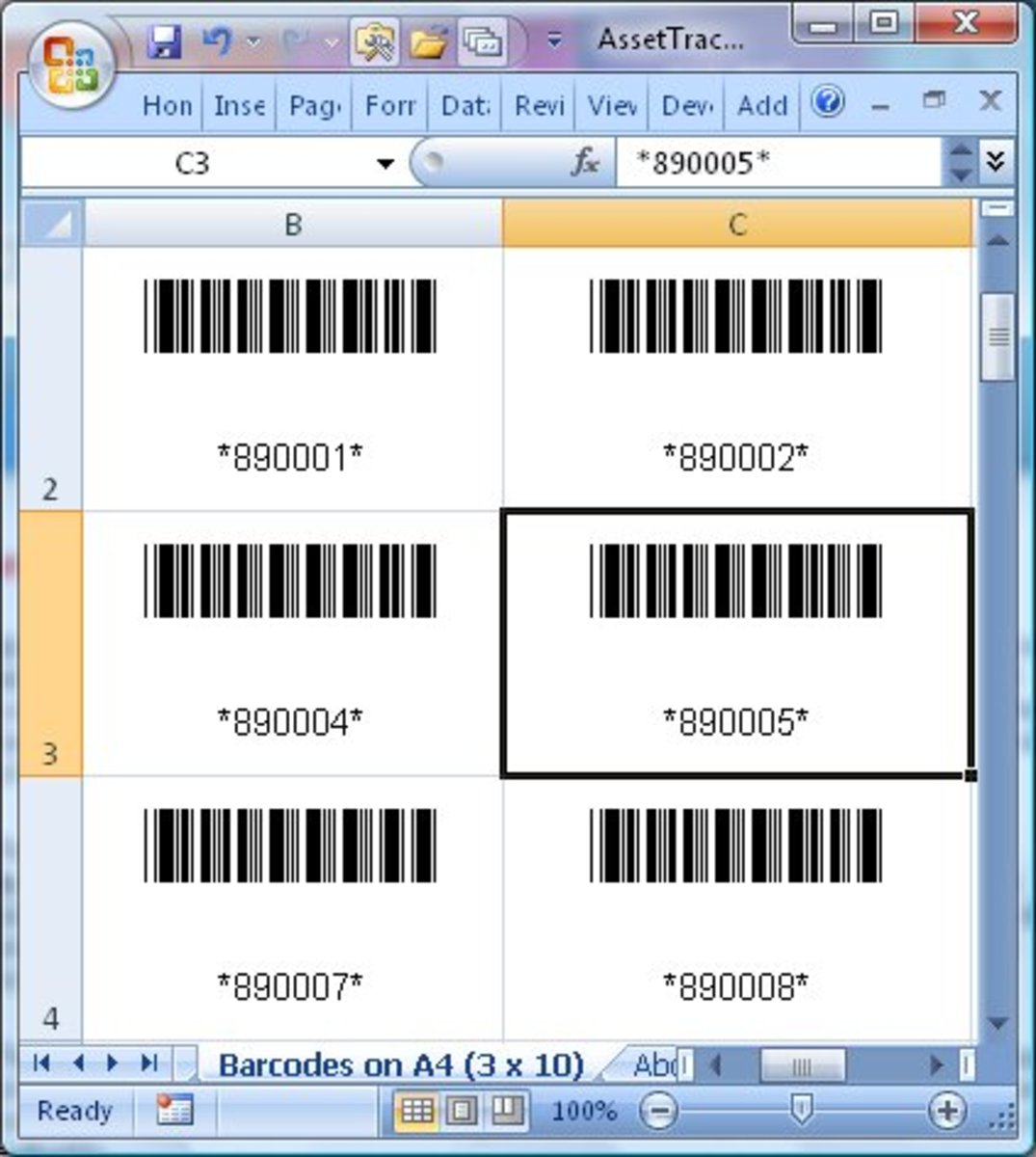
• Then there's RFID technology ... Radio Frequency Identification uses tiny chips embedded in stuff (already in U.S. passports) to communicate with various nearby devices and disclose information about you, including where you are. The combination of RFID tags and GPS technology allows both private corporations and government snoops to track you from the clothes you're wearing, the cars you drive, the phones you use, and piles of other routine physical items you rely on for everyday survival and convenience.
Biometrics and facial recognition
• But perhaps the crowning achievement of the tracking snoopers so far is the development of facial recognition and biometric technology, which has been leaping ahead at warp speed. As described by the Electronic Frontier Foundation in a 2003 report, biometrics refers to "the automatic identification or identity verification of living persons using their enduring physical or behavioral characteristics. Many body parts, personal characteristics and imaging methods have been suggested and used for biometric systems: fingers, hands, feet, faces, eyes, ears, teeth, veins, voices, signatures, typing styles, gaits and odors."
• As an example of the current deployment of this technology, cops from 40 different police departments are hitting the streets armed with a gadget called the Mobile Offender Recognition and Information System (MORIS). Basically an iPhone accessory, MORIS can take an iris (eye) scan from 6 inches away, evaluate a person's face from 5 feet away, or even lift electronic fingerprints. (Incidentally, is everyone really comfortable with the assurances that there's definitely no possible health threat to our eyes from iris scans?)
• Using the digitized photos from ordinary driver's licenses, state agencies that issue these (Departments of Motor Vehicles, Departments of Public Safety, etc.) are collaborating with federal agencies like the FBI to develop huge facial recognition databases suitable for identifying and even tracking just about everybody everywhere in the USA. (Powerful supercomputers with vast storage capacity and ultra-fast processing speed can provide the artificial intelligence and monitoring capabilities for such pervasive surveillance.)
According to a July 2018 NBC News report, "Most adult Americans are already in a facial recognition database of some kind ...." Yet the accuracy of this technology is flaky. For example, "The FBI’s facial recognition system has been found to misidentify people 14 percent of the time."
The consequences have become evident to various victims, such as one innocent individual in Massachusetts, jailed for ten days while he tried to prove to state authorities that facial recognition technology had erroneously fingered him from his photo because he resembled a different guy wanted for ID fraud.
• If the public sector doesn't "getcha", maybe the private sector will. More and more public establishments and corporate enterprises – such as certain bars in major cities, casinos in Las Vegas, and big retailers like Kraft and Adidas – are deploying facial recognition technology to identify everybody from random individuals to customers, initially for marketing-related purposes (e.g., "targeted ads"), but with the potential for ultimately tracking where you go, what you visit, and what you're up to in general. (This capability of pervasive facial recognition has played a role in sci-fi dramas, such as the 2002 film Minority Report.)
• And of course, let's not forget about that favorite of both private and public surveillance operations, the CCTV camera. For years, it's been creepy enough to realize that, while you're in a public area, some human might be peering at you — and recording you for later review — from a remote console and trying to figure out who you are, what you're doing, where you're going. But now, facial recognition capability is giving that kind of snoopery a whole new dimension.
Perhaps you're not bothered by this, and – like most of the general public – are satisfied that "it's all for our own protection." But if privacy (and the right to remain anonymous) are rights you value, then you might find some of these developments disturbing, to say the least.
So far, popular toleration of this increasingly pervasive snoopery has been widespread. But is there a limit?
Maybe as the numbers of seriously abused victims grows, so will outrage and courage – and eventually even some vigorous pushback – including effective measures to counter or foil some of the snoopery? Time will tell.
■