Terrorism, Scourge of the Modern Day

Terrorism, Lessons from the Past
In order to trace the roots of the labels ‘terrorism’ and ‘terrorist’, historians have attempted to trace these concepts back through the ages of war, crime and punishment, empires, gendered violence, territorial massacres and racial conflict in order to identify how far back it can really go.
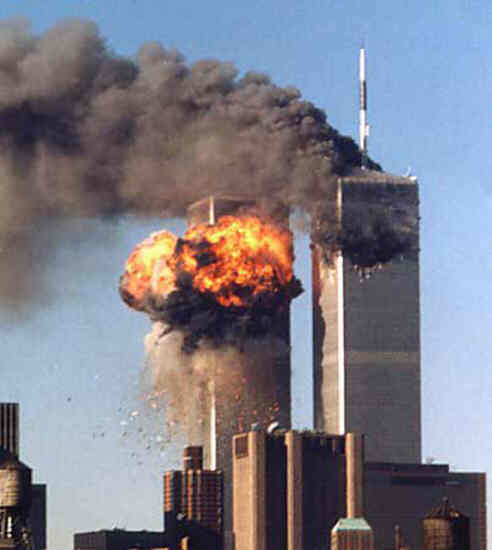
This process of digging into the history of violence to trace the concept of terrorism pretty much began after the September 11 attacks on the United States. The attacks let to a need for a more coherent understanding of the history of 'terrorism' than there has ever been before. Historians identified that, unlike other regular crimes, terrorism is politically motivated, making this one of the fundamental concepts in differentiating terrorist acts from other criminal acts. They also realized that terrorism has evolved over the years and has changed in both political context and time. However, terrorism is an atypical norm that has existed among humans since the beginning of time.
Have your say...
Do you think you government is doing enough to handle the issue of terrorism?
What does Terrorism mean to you?
‘Terrorism’ is a term used globally and people’s definition of it affects how they perceive terrorist threats. In addition to that, many people consider it a threat to their personal lives and a social evil. Terrorist attacks around the world have influenced how social psychologists examine the consequences of the perceptions of the threat of terrorism. They note that most scholars view it from a military and political perspective without considering the sociological aspects of it.
Therefore, people's perceptions of terror threats may result in significant social challenges in the society. They carried out a study to determine how demographics affect people's perception of terrorism. They identified people of different ages and gender and were able to determine that older people living in the suburbs requiredmore assurance that is psychological whenever there were ‘terrorist’ threats. It also determined that globalization has contributed to responses and perceptions of terrorist threats. However, even though sociologists refer to terrorism as a modern evil, they do not understand political evil. Their perception of evil may therefore be wrong in a political perspective.
How Terrorist Organizations Work
The structures of terrorist organizations often determine their capabilities and effectiveness is at ‘terrorizing’ the masses. As part of their structures, their security, resources, and membership determine their outreach. Factors like organizational commitment determine the nature of the terrorist group and its impact on the population.
The strength of the group often lies in its leadership, active members, and active supporters, with the passive supporters playing a minor but important role in fund-raising and nonviolent activities. Because the people in the different levels are often involved in the recruitment processes, the more they are, the more the number of recruits they can gather.
With terrorists from different social and ethnic backgrounds, a terrorist group can become significantly more powerful. An example is a U.S. citizen named John Walker who was captured in Afghanistan. His American background contributed to a widespread perception of the idealism of terrorism spreading to people from even the ‘victims’ backgrounds.
Of Suicide Attacks
The concept of suicide terrorism has also contributed to the labelling of particular criminal acts as ‘terrorism’ or ‘terrorist activities’. Since the September 11 attacks, suicide attacks with political objectives have become widely considered as terrorist attacks. The first suicide attacks date back to the 1980s, however, the numbers of these attacks increased in the 1990s.
Despite the sudden increase, it became difficult to explain why terrorist organizations were increasingly using suicide attacks. This became even more difficult to explain when the initial perception that suicide terrorists were idle, poor, or uneducated was proven wrong. More suicide terrorists are well trained and educated. This has helped to evolve the label ‘terrorism’ to an even more diverse group of individuals.
Different Approaches
Some may view terrorism as ideologically freighted making it lack any analytical value. To defenders and representatives of governments, terrorism is any politically motivated violent attack against an organization or a state, whereas to organizations and non-state groups it means political violence perpetrated by those states and their military forces. Slowly, the term 'terrorist' is becoming increasingly endangered in becoming a term an institution uses to refer to their enemies. These institutions name their enemies terrorists and this affects the analytical value of the word and the label.
Anti-Terrorism Efforts
The attacks deemed as terrorist attacks significantly affects society, and the society contributes to labels and how the media uses these labels. This has created pressure on law enforcement bodies and intelligence agencies to increase their efforts in the 'war on terror'. As such, this has created a new label, 'anti-terrorism'. People generally view this as any act or effort that attempts to curb or fight politically motivated violent acts. It is also technically a controversial term because the different parties involved can refer to any act to fight their enemies an 'anti-terrorism' act
.Another more recent concept that arose from the initial concept of terrorism is cyber terrorism. This is the use of information technology by 'terrorist' groups to achieve their goals. It is relatively more modern because of the recent exponential growth in the use of technology in the world. Most institutions that are sensitive to attacks use modern technology and whenever they are attacked, this is deemed as terrorism even though it does not involve violent attacks.
I know, I know….I didn’t go much into terrorism, but there’ll be more articles later about it. This particular article was introductory. Keep a lookout for more!