Cyber Security and The Great Battle For Digital Liberty
Do you feel the Federal Government should regulate Cyber Crimes and Security?
You may have recently been made aware of the new Cyber Security bill the Republicans are determined to pass, it's called CISPA. You might also have followed some of the headlines that talked about SOPA or PIPA last year. Though I bet you didn't realize just how deep the battle for Digital Freedoms is, how long it's been going on, or how much more of a battle we have ahead of us, if we're going to keep the internet a free place for everyone to use in the way they wish.
Where It All Began: National Strategy to Secure Cyberspace (2003)
There were already a few cyber security acts before the federal government created NSSC to make recommendations for securing as much cyber space as possible. It is from this group, which is facilitated by DHS, that we began to see bills emerging that could truly threaten our digital and intellectual freedoms.
Here is an exert from Wikipedia about the NSSC:
"In addition to regulation, the federal government has tried to improve cyber-security by allocating more resources to research and collaborating with the private-sector to write standards. In 2003, the President’s National Strategy to Secure Cyberspace made the Department of Homeland Security (DHS) responsible for security recommendations and researching national solutions. The plan calls for cooperative efforts between government and industry “to create an emergency response system to cyber-attacks and to reduce the nation’s vulnerability to such threats.” In 2004, Congress allocated $4.7 billion toward cyber-security and achieving many of the goals stated in the President’s National Strategy to Secure Cyberspace. Some industry security experts state that the President’s National Strategy to Secure Cyberspace is a good first step but is insufficient. Bruce Schneier stated that “The National Strategy to Secure Cyberspace hasn’t secured anything yet.” However, the President’s National Strategy clearly states that the purpose is to provide a framework for the owners of computer systems to improve their security rather than the government taking over and solving the problem. Yet, companies that participate in the collaborative efforts outlined in the strategy are not required to adopt the discovered security solutions."
No End In Sight
It began long before I can find official 'evidence' for, but just to give you an idea, here is a list of bills that congress have created and attempted to pass:
- ICANN - Family Privacy and Security Act of 2002 (Landreiu)
- CSEA 2002 - Cyber Security Enhancement Act (Smith)
- SPY ACT - Securely Protect Yourself Against Cyber Trespass Act (2005) (Mack)
- Cybersecurity Act of 2009 (Rockerfeller)
- Cybersecurity Act of 2009 (Rockerfeller)
- CSEA 2010 - Cyber-Security Enhancement Act (Lipinski)
- Cyber Security And American Cyber Competitiveness Act of 2011 (Rockerfeller)
- CIFA - Cybersecurity And Internet Freedom Act (2011) (Lieberman)
- Homeland Security Cyber and Physical Infrastructure Protection Act of 2011 (Thompson)
- Cybersecurity Enhancement Act of 2011 (Jackson-Lee)
- SOPA - Stop Online Piracy Act (Smith)
- PIPA - Protect IP Act (2011) (Leahy)
- OPEN - Online Protection and Enforcement of Digital Trade (2011) (Wyden)
- CCPSA - Cyber Crime Protection Security Act (2012) (Leahy)
- SECURE IT Act of 2012 (McCain)
- Cyber Security Act of 2012 (Rockerfeller)
- CISPA - Cyber Intelligence Sharing and Protection Act (2012) (Rogers)
Now, IMO, one of the most interesting thing about these bills, is that the majority of them were either started by or sponsored by Senator John "Jay" Rockerfeller, Senator Joseph Lieberman, Senator Harry Reid, Senator Feinstein, Senator Patrick Leahy and/or Senator John McCain - All well known names... Setting that aside, most of the acts appear to be benign from first glance, but upon further inspection, there is always some devil in the details that would never work.
Thankfully, just about all of the acts have already been labeled "dead", though just from the list already going here, you can tell that the fight is far from over. Any number of these bills could be brought back to life, recreated or cut and pasted into an entirely new bill. And that's not counting the still active bills like CISPA.
The Empire Fights Back - Tally Ho!
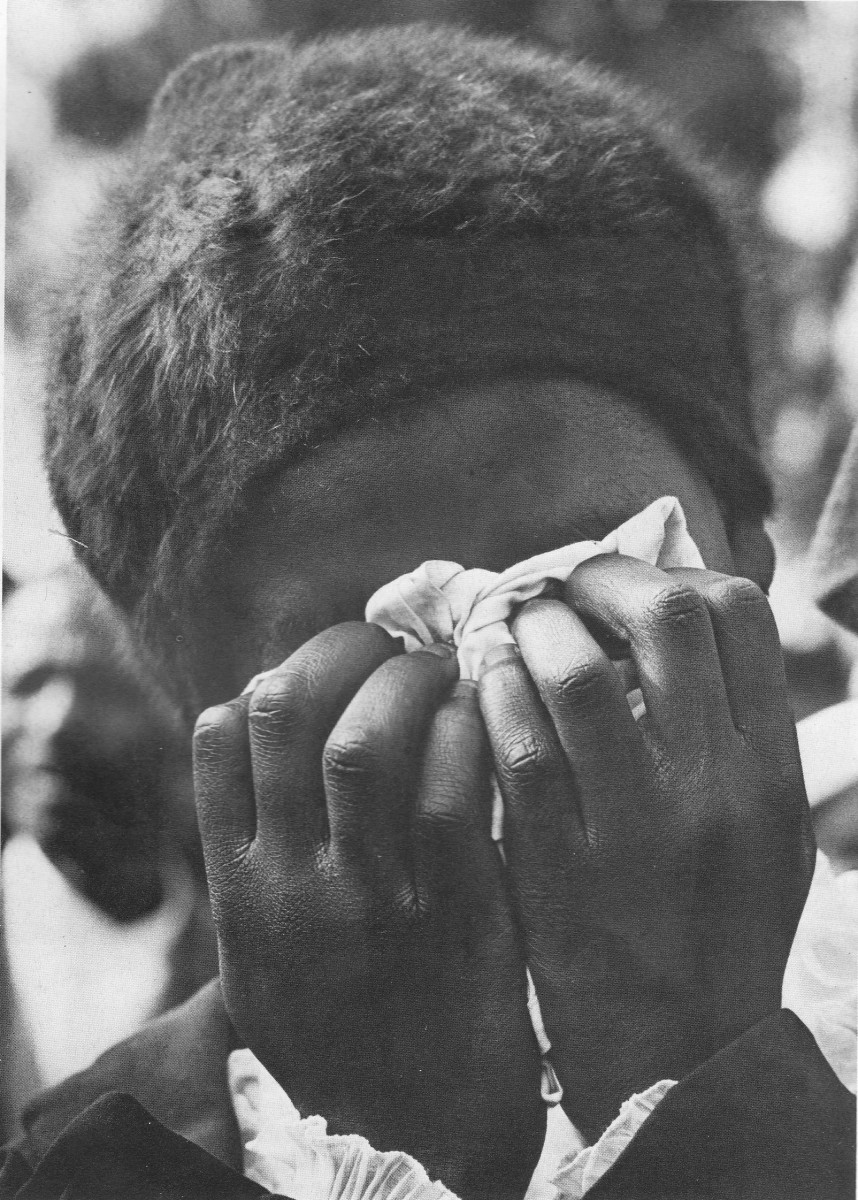
It is thanks to the vigilant few that most of these bills have never and will never see the light of day. And while the mugwumps are still making backroom deals to try and pass their coveted cyber security bill - there is always a light of hope that it will be stopped.
Some things that have been done or are being done to stop or prevent cyber security bills from passing:
- Lights Out Protest - Wikipedia Goes Dark (Included more than 7,000 websites)
- Operation Blackout - Social-Protesting
- Stop CISPA - Global Petition





![StarCraft II: Wings of Liberty - PC/Mac [Digital Code] [Online Game Code]](https://m.media-amazon.com/images/I/81mm5lhEtfL._SL160_.jpg)