The Wikileaks Time Line
Who or What is Wikileaks
Advisory Board
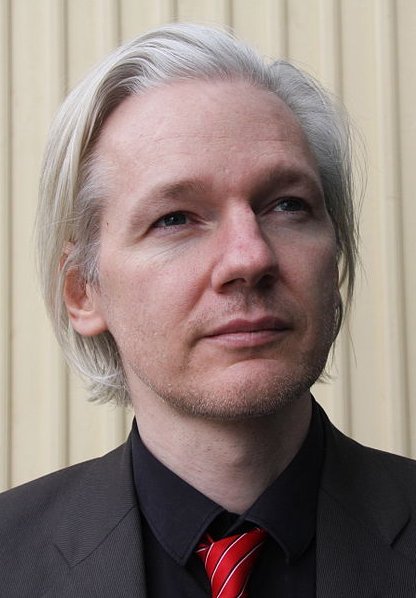
Though Julian Assange (pictured below) is often the only person mentioned along with Wikileaks, the organization has an advisory board of nine members. They are:
- Phillip Adams, writer
- Chico Whitaker, Brazilian social justice advocate
- Wang Youcai, Chinese Democracy Party advocate
- Wang Dan, Tienanmen Square dissident
- CJ Hinke, writer
- Ben Laurie, Internet security expert
- Xiao Qiang, Chinese human rights activist
- Tashi Namgyal Khamsitsang, Tibetan exile
- Julian Assange, journalist
Note also that the site clearly states that the founders of Wikileaks are anonymous and will remain so for the foreseeable future. Though it's clear from the list above I want to make an effort to point out that the man in the news, Julian Assange, is just one of the primary decision makers at Wikileaks.
When Did Wikileaks Begin
2006
Wikileaks began in 2006. It was originally supposed to be an open electronic forum for whistle-blower information. The "wiki" in the name indicates it's original open intent. Despite this, the domain name holder is listed as The Sunshine Press, indicating that this is a journalistic endeavor.
The organization was originally described as "having been founded by Chinese dissidents and journalists, mathematicians, and technologists from all over the world.
December: A document approving the assassination of Somali officials, signed by Sheikh Hassan Dahir Aweys, is leaked and posted on WikLeaks.
2007
August: A document detailing the corruption of the family of the former Kenyan leader Daniel arap Moi appears in The Guardian. The story is based on information obtained from Wikileaks.
November: Wikileaks publishes a copy of Standard Operating Procedures for Camp Delta from March 2003. This document details the standard operating procedure for handling detainees at Guantanamo Bay. Part of the document implies that some prisoners are not to have any contact with the International Committee of the Red Cross. The Department of Defense responds by stating that the document is out of date and no longer used.
2008
In this year Wikileaks won an award from The Economist magazine's New Media Award.
March: Wikileaks publishes what it calls the "collected secret 'bibles'" of Scientology. The Church of Scientology threatens to sue Wikileaks for breach of copyright three days later. This effectively validates the leak.
April: Wikileaks releases information that implicates The Swiss bank Julius Baer, Cayman Islands of illegal activities. The bank sues WikiLeaks shutting it down temporarily with an injunction. A judged overturned the injunction citing first amendment and jurisdiction concerns.
September: A whistle-blower1 gains access to Sarah Palin Yahoo account and posts the contents of her email to Wikileaks.
November: The membership list of the British National Party is posted on WikiLeaks.
2009
In this year Wikileaks wins the UK Media award from Amnesty International for the publication of Kenya: The Cry of Blood – Extra Judicial Killings and Disappearances."
January: Wikileaks publishes eighty-six telephone intercepts between Peruvian business-men and politicians regarding the Peruvian Oil Scandal of 2008.
February: Wikileaks posts almost seven thousand (6,780) reports generated by the Congressional Research Service.
March: Wikileaks releases the names of contributors to the Norm Coleman senatorial campaign.
Wikileaks releases a set of documents belonging to Barclays Bank that had previously been purged from its website.
July: Releases documentation relating to a serious accident at the Iranian Natanz nuclear facility. Later reports indicate the incident may have had something to do with the Stuxnet computer worm.
September: Internal memos from from Kaupthing Bank are posted on WikiLeaks. The documents reveal that large sums of money were loaned to various bank officer/owners along with the "write-off" of large debts.
October: The British Ministry of Defense Joint Services Protocol 440, is published. The paper offers advice to security services on how to avoid leaked documents. The twenty-four hundred (2,400) page document was written in 2001.
Though not the original publisher, Wikileaks hosts leaked email between climate scientists. This leads to accusations, in the press, of scientists colluding to falsify climate change data.
Half a million (570,000) intercepts of pager messages sent on the day of the 11 September attacks are published on WikiLeaks.
Wikileaks publishes Australia, Denmark and Thailand's lists of forbidden or illegal web sites. Though the lists were originally created to prevent child pornography and terrorism, other, unrelated sites, are included in the lists.
The Year 2010 to November
March: A thirty-two (32) page U.S. Department of Defense Counterintelligence Analysis Report, discussing the leaking of material by Wikileaks is published. The report suggests ways to prevent and deter such leaks.
April: Wikileaks posts an edited video of Iraqi civilians and journalists being killed by an American gunship helicopter. The video is titled Collateral Murder. The incident took place sometime on July 12, 2007.
May: The New York Daily News calls Wikileaks one of the "websites that could totally change the news"
June: Former Army Specialist Bradley Manning, a 22-year-old US Army intelligence analyst, (now PFC) is arrested after former hacker2 Adrian Lamo turns over chat logs to the authorities. Manning is alleged to have confided, in these chats, that he had leaked the "Collateral Murder" video along with roughly two hundred-sixty thousand U.S. diplomatic cables.
July: Wikileaks releases ninty-two thousand (92,000) documents chronicling the war in Afghanistan. These papers relate to a period from 2004 and the end of 2009. The Guardian, The New York Times and Der Spiegel use excerpts from these documents as news items. The documents contain first hand accounts of friendly fire and civilian deaths.
Wikileaks follows up by posting a link to a 1.4 GB encrypted file. Wikileaks threatens to release the file's encryption key should the site or Julian Assange be harmed for publishing the ninety-two thousand Afghan documents.
November: Wikileaks, along with El País, Le Monde, Der Spiegel, The Guardian, and The New York Times together publish the first two hundred ninety-one (291) documents from the alleged leaker, Army Private (former Specialist) Bradley Manning.
December 2010
Sweden asks Interpol to issue a "Red Notice" asking for information on the whereabouts of Julian Assange.
Amazon stops hosting Wikileaks servers. They are moved to somewhere in Sweden.
Assange, visiting England, turns himself in to the authorities.
A judge, hearing the case, refuses to grant Assange bail due to a flight risk.
A day later the same judge overturns his own ruling and determines that Assange can go free on a $314,000 bond and wear an ankle mounted GPS device to track his whereabouts.
Sweden's attorneys challenge the ruling and Assange remains in jail for the next forty-eight hours.
Assange was granted bail in December 2010 and currently resides at journalist Vaughan Smith's Ellingham Hall, Norfolk, England. Assange is required to wear a GPS tracking anklet and must call the authorities every day to report on his whereabouts.
Sex by Surprise - Not
Somehow a writer/reporter for AOL started the "sex by surprise" ball rolling and most journalists in the U.S. continued this false assumption claiming that the Swedish women charging Assange with a crime had something to do with birth-control devices and briefly non-consensual sex.
In reality Sweden has no such law. Assange is being accused of rape, pure and simple.
Should the reader find a translation of the law, he or she will notice, with careful study, that word "surprise" is never once used in the statutes.
Apparently, Assange faces anywhere from two to four years in prison if convicted.
Attack and Counter-Attack
November 28th: The day that Wikileaks released a portion of the Diplomatic Cables a number of Distributed Denial of Service(DDOS)3 attacks were launched against the site.
December 1st: Wikileaks moved it's site to Amazon's cloud of servers, but Amazon revoked it's hosting privilege after Senator Joe Liberman complains.
Wikileaks moves it's site to a Swiss domain name (Wikileaks.ch) and then to wikileaks.org.
December 4th: Paypal suspends donation transactions to Wikleaks citing the "illegal activity" clause in it's user agreement.
December 6th: MasterCard and Visa suspended donation accounts for WikLeaks. A Swiss bank account for Wikileaks is also closed
December 7th: Julian Assange turns himself in to British police.
December 8th: DDOS attacks against the Swedish prosecution authorities and Claes Borgstrom (lawyer for the two women accusing Assange of sexual misconduct) brings these two sites down.
Early December: The U.S. government reminds it's employees that viewing or visiting WikiLeaks sites, while on duty, could get them reprimanded and/or fired.
December 10th: A large group of people identified only as Group Anonymous, launch a DDOS attack on Paypal, MasterCard, and Visa web-sites. Since the sites having nothing to do with actual financial transactions the results are somewhat questionable.
The U.S. Justice Department begins studying the law to determine if any charges can be filed against Assange. Of course this involves an investigation which the DoJ admits to.
December 13th: British judge denies Julian Assange bail.
December 14th: The U.S. Air Force isn't taking any chances. It's servers no longer grant access to The New York Times and twenty-five other sites. Though no reason is given it is assumed, in the press, that this is in direct response to WikiLeaks leaked diplomatic cables.
British judge reverses decision on bail. Swedish prosecutors appeal the decision and Assange remains in custody. The appeal will be reviewed Thursday, December 16, 2010.
December 15th: The U.S. Justice Department is trying to establish the level of involvement between Bradley Manning and Julian Assange regarding the video and reports leaked to the web-site. If the DoJ can establish that Assange helped or encouraged Manning it may be able to level a charge of conspiracy against Assange.
Excerpts of the chat between Manning and Lamo (the former hacker who reported Manning to the military) can be seen here.
December 16th: A London judge grants Julian Assange bail while he awaits extradition proceedings. This is a breaking item and all the conditions are not yet known.
Update: Bail has been set at $370,000, Assange must confine his movements to a friend's estate. He must also wear an electronic monitoring device, report daily to the police, and observe a curfew which confines him to the house on that estate.
December 22nd: Julian Assange accuses the United States of using the criminal charges he faces in Sweden as "smear campaign" to shut him up.
“If they want to push the line that when a newspaperman talks to someone in the government about looking for things relating to potential abuses, that that is a conspiracy to commit espionage, that is going to take out all the good government journalism that takes place in the United States.” - Julian Assange
December 27, 2010
In an interview with The Australian Assange states that he has been forced, financially, to make a book deal with Knopf Publishing in order to defray the costs of his legal defense. The deal is said to be worth 1.5 million dollars.
Also in the interview Assange claims that the rape charges came about when the two women he "slept with" in Sweden discovered they'd both slept with Assange. Upon comparing notes they went to the police together to file a complaint. Allegedly a policewoman, on hearing their story, suggested the pair could pursue criminal charges. Assange has allegedly said:
"Sweden is the Saudi Arabia of feminism, I fell into a hornets' nest of revolutionary feminism."
January 8, 2011
The United States Department of Justice submitted a subpoena to Twitter, in San Francisco, demanding access to the Wikileaks Twitter account. Twitter responded, in part, by warning its user base about the demand. Wikileaks Julian Assange responded with:
"If the Iranian government was to attempt to coercively obtain this information from journalists and activists of foreign nations, human rights groups around the world would speak out."
February 24, 2011
Julian Assange is ordered extradited to Sweden to face charges.
February 2011
Assange's lawyers appeal the order.
November 2, 2011
Julian Assange loses his appeal to fight extradition to Sweden. His lawyers are now considering taking the case to The Supreme Court of the United Kingdom.
August 16, 2012
Ecuador has agreed to grant Assange asylum.
September 17, 2012
A Swedish lab fails to find DNA on a sexual protective device given the Swedish government by one of the woman alleging Assange raped her.
November 20, 2014
On this date Stockholm’s appeal court has rejected a demand made by Julian Assange’s lawyers to revoke the warrant for his arrest. This leaves Assange facing extradition to Sweden. He remains a guest of Ecuador’s, in the London embassy.
Sweden's prosecutor said: "There is a great risk that he will flee and thereby evade legal proceedings if the detention order is set aside. In the view of the court of appeal, these circumstances mean that the reasons for detention still outweigh the intrusion or other detriment entailed by the detention order."
Assange has been a guest of the London Ecuadoran Embassy for almost four years.
Per Samuelson, Assange's lawyer said: "Swedish and international law is on our side,”The ruling shows we are on the right track, but unfortunately the court of appeal did not have the courage to overturn the arrest warrant.”
Coda
Because this story has so much interest the author has attempted to give the reader a summary of the actual events as they have occurred. It is also the author's desire to dispel some of the misleading rumors and wild speculation in the press about certain aspect of this affair.
Notably the charges Assange faces in Sweden.
It Will Not Go Away
Three facts must be kept in mind when assigning blame to a lone individual.
Wikileaks has a nine member board of advisers; Julian Assange is just one of them.
The actual founders of Wikileaks remain anonymous.
Though a "Thermonuclear option" has been alleged no one has yet published the decryption key or admitted to decoding the "insurance policy," though the file itself has been widely distributed and copied.
September 17, 2012
Neutrality in this Article
At all times I, as author, have done my best to present the facts in a neutral manner.
This is over.
The Swedish lab has been unable to find any traces of DNA on the prophylactic in the accusation of rape against Julian Assange. Further, the second woman in this affair is now denying that a rape occurred. Sweden case against Assange just evaporated in a cloud of misdirection, false accusation, and smoke. But this finding is much much worse.
In the entire history of Interpol as a police agency not once as a red notice been issued in the instance a sexual assault. Further I now have the distinct impression that the two women who accused Assange of sexual misdeeds were coerced into doing so. Further the timing of these accusations is highly suspicious and has been from the start. Now that no evidence has been found (even skin would leave behind traces of DNA) Sweden's case against Assange is now revealed for what it is, an attempt to arrest Mr. Assange and extradite him back to the United States.
Sweden needs to drop the charges and apologize for being complicit in an attempt to not only illegally extradite a reporter for reporting, they need to apologize for dragging his character through the mud to do so.
Footnotes
1 By definition a whistle-blower is someone who reports illegal activities or violations of the law to authorities. The U.S. has laws protecting whistle-blowers.
2 Hacker can have three different meanings relating to computer security. a) someone who uses a computer to gain unauthorized access to data, b) an expert at solving computer related problems, c) someone who is a computer security professional.
The second two meanings were the most valid until the press began equating "hacker" to "thief."
3 Denial of Service is a means of tying up a web-site by repeatedly accessing that site with bogus requests. It is relatively easy to accomplish with enough people behind such an attack. Such attacks can also be accomplished with automated programs.
It is very difficult to determine who is behind such an attack because computer errors, user errors, and errors in coding can all account for the effects of a DDOS attack.
DDOS stands for Distributed Denial of Service.