Terrorism, Espionage, And the Nation-State: The Importance of Intelligence

Terrorism and Industrial Espionage: Two Threats to Nation-States
Two primary threats to the safety and security of nations are, on the one hand, terrorist groups and their associated networks, with their harmful and unconventional tactics, and, on the other, industrial espionage, with its commercial consequences.
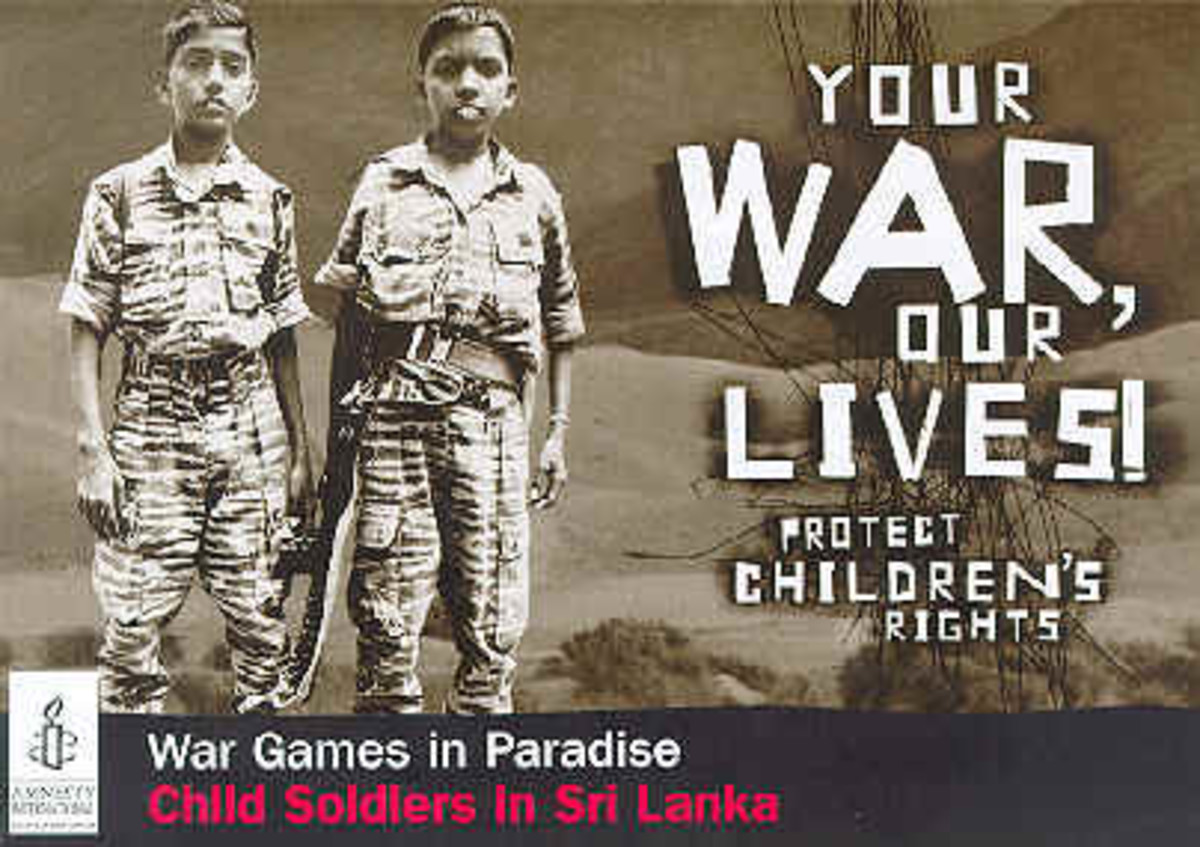
Examples of targets for acts of terrorism are prominent individuals and government agents, embassies and military installations, transports and supply chains, symbols of financial power and national identity, and critical infrastructure, such as nuclear and chemical plants, as discussed by, for example, Kydd & Walter in their 2006 article “The Strategies of Terrorism” in International Security (volume 31, pages 49-79). For a further discussion about the targets of terrorism, see Tsamboulas’ & Moraiti’s 2008 article “Identification of potential target locations and attractiveness assessment due to terrorism in the freight transport” in the Journal of Transportation Security (volume 1, pages 189-207) and Murphy’s & Ellson’s 2010 article “Responding to Target Buildings in a Terrorist Attack” in the journal Fire Engineering (volume 163, pages 20-26). The rationale for these types of attacks, from the point of view of the terrorist groups, includes provocation, intimidation, and attrition. Terrorist incidents have serious consequences for individuals, groups, property, and political life. History shows that the public will not tolerate governments that fail to handle intelligence related to terrorism properly and efficiently. The 2004 Madrid train bombings led to a critique of the Spanish government for not acting upon intelligence that was available to it prior to the explosions. As a result, the government was not re-elected in the elections held later that year. The Madrid example illustrates that poor security service work by intelligence and security services can impact government elections and shape the course of a nation’s history and future.
An example of a target for industrial espionage is a corporation that manufactures and develops advanced software, devices, high cost processes or similar. These products are attractive to competitors or foreign nation-states, as information, blueprints, design layouts, and other intelligence concerning these products are not available through open sources. Industrial espionage also has serious consequences for organizations and nation-states. In 1996, it was estimated that the cost of industrial espionage to Canada was $1 billion per month; the cost to the United States in 2004 was estimated to be $100–250 billion annually (See, for example, Jones' 2008 article “Industrial espionage in a hi-tech world” in Computer Fraud & Security, volume 1, pages 7-13). An example of industrial espionage from the corporate world is the well-known dispute during the 1990s between General Motors Corporation (GM), and Volkswagen Group (VW), two of the largest automakers in the world. In this conflict, VW was accused of involvement in activities in which secret GM documents went missing. However, the case, known to the public as the “Lopez Affair,” never went to trial. Instead, the two sides signed settlement papers that stipulated that VW would pay $100 million in damages and would agree to buy at least $1 billion in GM parts over 7 years. For more details, see for example Stephens 1999 article “Document security and international records management” in Records Management Quarterly (volume 31, pages 69-70). See also the article entitled “VW agrees to $100m settlement with GM” published in January 10, 1997, by The Independent. Industrial espionage can also escalate political concerns and result in diplomatic affairs. In 2002, for example, Sweden was not on good political terms with Russia following a diplomatic incident the same year involving industrial espionage. We Swedes claimed that company information was leaked from one of our nation’s top telecommunications and radar systems companies to the Russian intelligence service. The Russians denied these accusations but we still expelled two Russian diplomats, and the Russians subsequently expelled two Swedish diplomats, as discussed by, for example, Osborn in the 2002 article “Sweden expels Russian jet ‘spies’,” published in The Guardian (November 12). If you want to read even more about industrial espionage, see for example Crane’s 2005 article “In the company of spies: When competitive intelligence gathering becomes industrial espionage” published in Business Horizons (volume 48, pages 233-240). My personal favorite though, is Brown's 2011 book The Grey Line: Modern Corporate Espionage and Counterintelligence.
At first glance, it might seem obvious that counterterrorism should be considered more important than counterespionage, but the matter may be more complicated than meets the eye. For a discussion on the strategic decision to rank counterterrorism as more important than counterespionage, see for example Foryst’s 2010 article “Rethinking National Security Strategy Priorities” published in the International Journal of Intelligence and Counterintelligence (volume 23, pages 399–425). However, there is no room here to suggest or reach a conclusion regarding the strategic decision to rank one as more important than the other. Rather, terrorism and espionage are used here as examples of threats to nation-states and, as such, as stepping-stones for a discussion regarding potential challenges for intelligence collection.
Intelligence Collection Reduces the Risks of Terrorism and Industrial Espionage
Intelligence collection—used here in a broad sense—helps to reduce risks for the nation-state regardless of whether the threat is terrorism or industrial espionage. It encompasses activities performed by security services and other organizations for specific purposes—for example, to enhance decision-making by politicians, the military, civil servants, and other officials. The term security services, thus, refers to the intelligence community, which gathers and analyzes intelligence for the safety and security of nations.
Policing, another term that can be used in this context, refers to the work done by police forces to enforce laws and protect property. The work of ordinary police officers and patrolmen is important and their work is a significant part of the machinery that tackles these types of security and safety issues. Consequently, in the long run, they help protect nation-states and contribute to democracy. For anyone interested in terrorism investigation and policing, I strongly recommend William E. Dyson's 2011 book Terrorism, Fourth Edition: An Investigator's Handbook.
Criminal investigations, terrorism, and policing is also discussed in a number of articles, such as King's & Sharp's 2006 article entitled “Global Security and Policing Change: The Impact of ‘Securitisation’ on Policing in England and Wales” in Police Practice and Research (volume 7, pages 379-390). For further reading, if you want more on the issue of safety and policing, see Young’s classic 1991 chapter “Left realism and the priorities of crime control” in the book The politics of crime control, edited by Stenson & Cowell (London: Sage).
My ending argument is that there is a realistic and fair chance for police officers and patrolmen working in the field to intercept information that contributes in part or wholly to the disruption of terrorist plans. The use of unconventional tactics by terrorists means that they strike, in principle, anywhere and anything in their search for mass casualties. Therefore, police working the streets have an opportunity to capture information that could be valuable to intelligence officials and, as such, contribute to the disruption of terrorist groups’ plans. Needless to say, the public may also contribute intelligence, i.e., with support and information valuable to nations’ security.
© 2012 Kent Lofgren