A New Breed of Botnet
Published: November 5, 2011
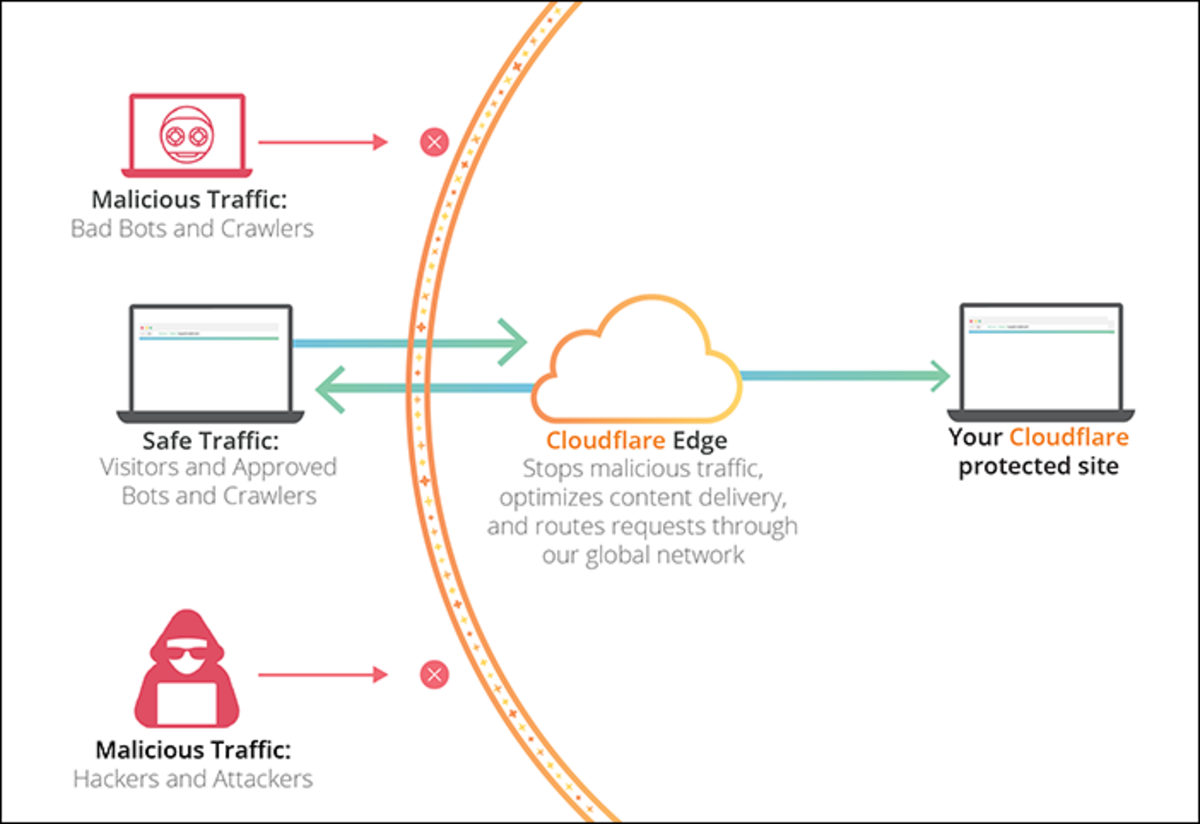
The discovery of Trojan Peacomm introduced new difficulty to the prospect of combating botnets. This difficulty arises from the use of encrypted tunnels for C&C communication channels and Fast Flux domain names. Shutting down botnets that use IRC channels is a matter of locating the C&C server and removing access to the server. Using encrypted channels makes locating C&C servers difficult; also, fast flux domain names enable the C&C server for the botnet to change hosts periodically.

Storm
The botnet created by the Trojan Peacomm has been nicknamed Storm by researchers and is the most advanced type of botnet to date. “By some accounts, the malware has successfully created a massive botnet — between one million and 10 million CPUs” (Dignan and McFetters, 2007). One of the most troubling aspects of Storm is that the sheer number of hosts involved in the botnet place the botnet in a position to leverage the computing power approaching that of a supercomputer.
By New Zealand computer scientist Peter Gutman’s calculations, the Storm Worm botnet “may be the first time that a top 10 supercomputer has been controlled not by a government or mega-corporation but by criminals. … The attackers have tied the spam lures to global news events, links to YouTube videos and online greeting cards. The sophisticated operation includes the use of fast-flux networks to avoid shutdowns, a rootkit component to hide from anti-virus scanners and a P2P command-and-control structure that makes it near impossible to kill the controlling server. (Naraine, 2007).
Peer-to-peer (P2P) communication is a mode of communication between two hosts normally used for media file-sharing. This mode of communication uses encrypted channels, which makes identifying specific data streams next to impossible. Using P2P permits Storm to hide the C&C streams between the bots and the C&C servers as well as between the C&C servers and the bot-herders.
- Storm Worm botnet partitions for sale | ZDNet
Dignan, L., and McFeters, N. (2007). Storm worm botnet partitions for sale. ZDNet. Available from http://blogs.zdnet.com/security/?p=592 - Storm Worm botnet could be world's most powerful supercomputer | ZDNet
Naraine, R. (2007). Storm worm botnet could be world’s most powerful supercomputer. ZDNet. Available from http://blogs.zdnet.com/security/?p=493&tag=rbxccnbzd1
Beware the Storm Worm
Fast Flux and DNS
Fast-flux networks use dynamic Domain Name Services (DNS), which means that the Internet Protocol (IP) address of a C&C server may change as often as an hour or less. Fast-flux networks enable Storm to frequently change C&C servers, making locating the C&C that much more difficult. The dynamic structure of the Storm botnet frequently changes C&C servers in a manner where any node peer could in fact be a C&C server. This is accomplished through the Overnet bootstrap protocol as explained by Enright (n.d.) and illustrated in Figure 2: Storm Overnet Bootstrap.
This C&C structure is much more complex than the simple push/pull styles used by IRC-based botnets. In order to maintain connectivity with Overnet peers, the nodes must frequently reinitialize to rediscover their relative locations in the overall botnet. This function is illustrated in Figure 3: Maintaining Overnet Connectivity – Storm. "’They've built a very resilient infrastructure,’ says Dmitri Alperovitch, principal researcher at Secure Computing, ‘if one command server gets shut down, it moves to the next’" (Acohido and Swartz, 2008).
Retaliation Mechanisms
One final disturbing characteristic of storm is that the developers of Trojan Peacomm showed some added cunning by designing retaliation mechanisms into the code. Researchers who get too close to locating the C&C servers or inner workings of the botnet find themselves targets of Storm. “New features of botnets created by the infamous Storm Worm allow denial of service attacks to be launched against security defenders that attempt to interrupt its operation” (Leyden, 2008).
- Botnet Scams are Exploding
Acohido, B., Swartz, J. (20080. Botnet scams are exploding. USA Today. Available from http://www.usatoday.com/tech/news/computersecurity/2008-03-16 computerbotnets_N.htm
Somehow, Peacomm includes a trace back feature to identify hosts used in an attempt to discover the botnet. Reverse-engineering of the captured Trojan is beginning to enlighten the security community but the cyber-crime gang running Storm has managed to conceal the specific C&C structure from researchers.
- Storm Worm retaliates against security researchers
Leyden, J. (2008). Storm worm retaliates against security researchers. The Registeer. Available from http://www.theregister.co.uk/2007/10/25/storm_worm_backlash/
What do you think?
The author appreciates all comments.