Android Malware Protection - How to Avoid the Android Malware Epidemic
Malware on smartphones has been largely ignored by most users who are unaware of the problems and their need to be vigilant in preventing infections. The amount of malicious software targeting Android smartphone system is growing daily, fed by user ignorance. Data compiled by various Antivirus firms show that Android malware, has risen about 40% in the last three months and has risen about 80% rise in the last year.
People install all sorts of apps without doing even the basic checks. People are aware of what to look for and the precautions to take to avoid malware infections on their PCs and laptops through bogus software and emails, but totally ignore the dangers on their smartphones. Its like a disease with a long incubation time that is spreading through the population because people are not taking precautions.
Many smartphone experts say the problem will grow until many more of Android customers experience all the inconvenience, frustration, and damage cause by a malware infection.





Like malware on a PC once you have an infection you can spread it to your friends. Suddenly your bandwidth disappears or you have a phone bill five time your normal rate and your friends start complaining - Take precautions now before its too late. The term 'malware' includes a wide range of malicious software such as a virus, or a trojan, or anything else that does unwanted things on your smartphone.
Known Effects of Malware Infections include:
- Sending messages without your permission to premium and expensive service SMS numbers
- Transmit your personal data and information on the smartphone to unknown parties
- Connecting your phone to a botnet network so that it can control your phone and execute commands remotely on your smartphone.
- Allow others to monitor your phone calls, view your saved messages and see your text messages
- Delude you into divulging financial information, such as birth date, account number, passwords and log in details and lots more
- Infecting your PC if you connect to your smartphone
Why is Android More Vulnerable?
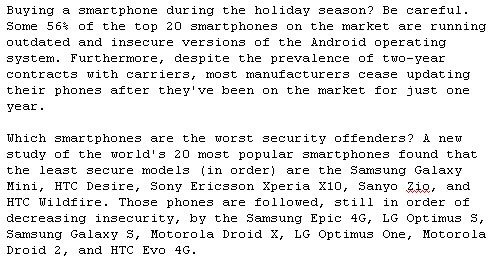
Android is more vulnerable because its open source and many players are involved - Apple owns and maintains complete control over the iPhone iOS operating system and regularly makes updates to all its customers at once, when a vulnerability is detected. Various manufacturers build Android phones, often modifying the software. Security updates are the responsibility of the carriers, not Google, and this makes the Android system much more vulnerable.
There are virtually no security checks for Android Apps - Anyone can post an infected app and other product into the Android Market or to a third-party app store. It is simply too easy to upload virtually any app. There is virtually no review system at all apart from the reviews and feedback provided by damaged users - but who reads these reviews and warnings.
Constant Upgrades to New Phones is part of the Problem - Unlike iPhones which are buy-once and use to 'end-of-life', Android customers are more likely to buy new handsets every 6-to-18 months, often switching to new manufacturers and this increases the risk that the new phone will be vulnerable to infection.
Upgraded Software has Security Improvements but its Still Vulnerable - Even after the recent release of Android 4.0 (Ice Cream Sandwich) that include upgraded security, such as Data Execution Prevention (DEP) and Address Space Layout Randomization (ASLR) the new software is still vulnerable. Various manufacturers tweak the software. Malware designers are always well ahead of the patches. Manufacturers should put much higher priority on security and users should not assume that the new software makes the software completely safe. Security advisers claim that the Android Market will probably never be as secure as the iTunes App Store. Only when Google and the manufacturers of the Android smartphones recognise the severity of the vulnerabilities will they do anything serious about it even to list known malicious Android apps.
What can Users do to Guard against Malware
Don't Blindly give Permission for Doubtful Apps - Many users blindly let Android apps access their smartphones without any check or precautions. Most users don't take the time to read and fully comprehend permission decisions. If you don't want apps to have access to your personal data, then don't install these apps and give them permission.
Lock Your Phone - so if your phone gets lost or stolen people cannot steal your personal information. If the phone is not returned to you, the person who has the phone would have to delete your personal data as part of the process of restoring everything to its factory settings and defaults.
Use a Secure Network - All transactions that involve personal information should never be made on an insecure network. Treat free Wi-Fi connections very warily and they are the source of many infections and they are many ways of tricking you into divulging your private data.
Only Install Trusted Apps - Only install applications from trusted companies or which pass the 'review before download' test. Always locate and carefully read the reviews of the app to ensure there are no security issues that apply to it or related apps from the same company. Only download apps from 'known' developers. If the app is new or from an unknown developer always do a quick check via Web search for both the developer and the name of the app. If the app is new - wait until reviews or information is available. Its not worth the risk.
Log Out Frequently - Keep your log-in information and passwords off your phone, and change them frequently. Always log out quickly every time you finish an online banking transaction or anything else that involves your personal data. This terminates the session and does not leave your the username and password exposed.
Install Mobile Security Software - There are various security apps available that offer virus protection and can detect and quarantine various types of malware. Packages from anti-virus companies such as Norton and McAfee can also be purchased. Up until recently, most Free Anti-malware Apps for Android were not very effective. A recent review showed that Only Zoner Anti-Virus Free showed relatively acceptable performance, with malware detection effectiveness of about 32%. Read the reviews and get a good one. Always check the reviews before investing in these protective apps to make sure they work.
Stick to the Default Software - Smartphones with factory settings have the lowest risk, and as soon as anything is changed the risk of intrusion increases. unlocking a phone or jail-breaking can increase the vulnerability.
Beware of unknown text Messages - As for emails, viruses and malware can be embedded within, or linked to, text messages. When opened, the malware can infect a mobile device. As for emails be very careful with any text from an unknown number, especially if the number looks suspicious or invalid simply delete the message without opening it.
Always check and Listen to User Reviews and Warnings - Other users may let you know if they are aware of problems with an app, including potential malware. If you know of any problems yourself then post information about it. Web searches are a very good way of checking for potential problems. If in doubt don't use the app.
© janderson99-HubPages
Update
© 2011 Dr. John Anderson




![How to Remove Kaspersky Password Protection? [Easily Recover] How to Remove Kaspersky Password Protection? [Easily Recover]](https://images.saymedia-content.com/.image/t_share/MTc2Mjk3NDcwOTAzNTkyMTI2/how-to-remove-kaspersky-password-protected-easily-recover.png)