Defeating WinAntivirus Pro

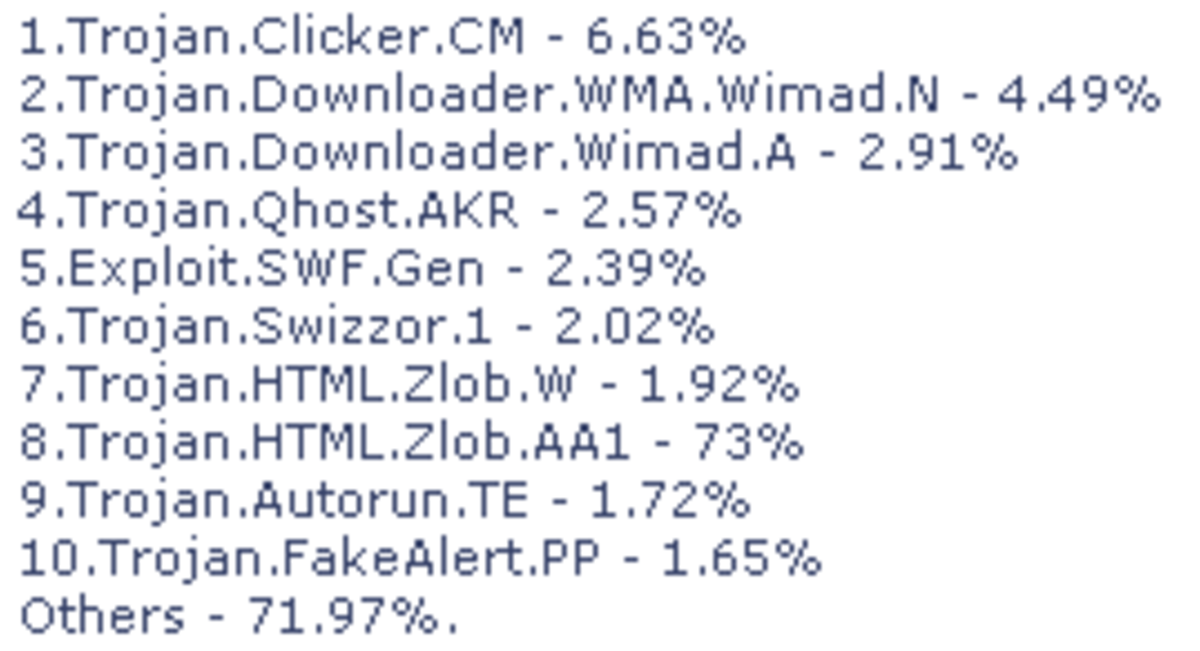
While performing my duties as a systems engineer I occasionally encounter a system that has been infected with a virus. This normally occurs after the license for an anti-virus package has expired or after the software was deactivated, for whatever reason. The clients who own these systems do not normally wish to pay for any extensive forensics investigation so the normal routine is to reactivate or reinstall the AV software and run a virus-scan along with ant-spyware and anti-malware scans to clean the system. If these three scans do not succeed, extreme measures are called for. These measures comprise reformatting the system, re-installing the OS, then reloading the applications and restoring whatever data was backed up to the time of the infection.
The anti-virus applications that my company endorses are Symantec and eTrust but I also recommend AVG to clients who wish a free solution. We also recommend free anti-spyware and anti-adware solutions which are Spybot S&D and AdAware 2008, respectively. Users should avoid the sites promoting Spywarebot and Adware because these sites use social-engineering techniques to entice users into believing that they are the SpyBot and AdAware sites. Downloading the applications from these look-alike sites will surely install malicious software on the surfer's system.
Intriguing Coincidence
The occurrences described above normally occurred once every couple of months so I spent little researching the incidents. However, not long ago, a PC at one of my associate's accounts fell victim to the WinAntiVirus Pro Trojan while I was filling in for him and I was able to preclude the infection by running SpyBot S&D and AdAware 2008. I did not think much about the incident until the next morning when the owner of one of my client-companies dropped off his personal computer because he claimed to have fallen victim to a virus: WnAntiVirus Pro. That same day the notebook belonging to an account-rep fell victim to the Trojan: Trojan.Downloader.
What was intriguing about these occurrences was that the frequency of infection was much shorter than usual, which indicated to me that these are very aggressive Trojans and that both types of infections exhibited the same symptoms. These symptoms begin with the replacement of the user's desktop wallpaper with a file called default.html. This file displays a blank background with a bordered text-box in the middle of the screen containing the message that the computer has been infected with a virus and a link to a site that will allegedly remove the virus. This is an obvious social-engineering tactic prompting the user to download more malware.
The first occurrence, the one that I successfully cleaned, only exhibited the first symptom; apparently the infection was cleaned before a user took action and clicked the link. The other two occurrences were much more persistent with other symptoms.

Persistent Symptoms
The most noticeable symptoms to users whose machines have been infected by WinAntiVirus Pro comprise the following:
- Hijacking the home-page of the browser to point to a malware-infection site
- Various pop-up messages that look like Microsoft Windows type warning boxes with headings like Windows Security Manager
- Clicking on the close button launches the browser pointing to the hijacked site location
- A yellow shield appears in the system tray when the pop-up displays (this lends the appearance of being a genuine Windows system-message
- The pop-up occurs approximately every 20 seconds so the user has a difficult time closing them
At this stage of the infection the system has been rendered unusable; installed applications will not run and web-browsing is constantly redirected to the malware site, which makes downloading a cleaning utility impossible.
First Cleaning Attempt
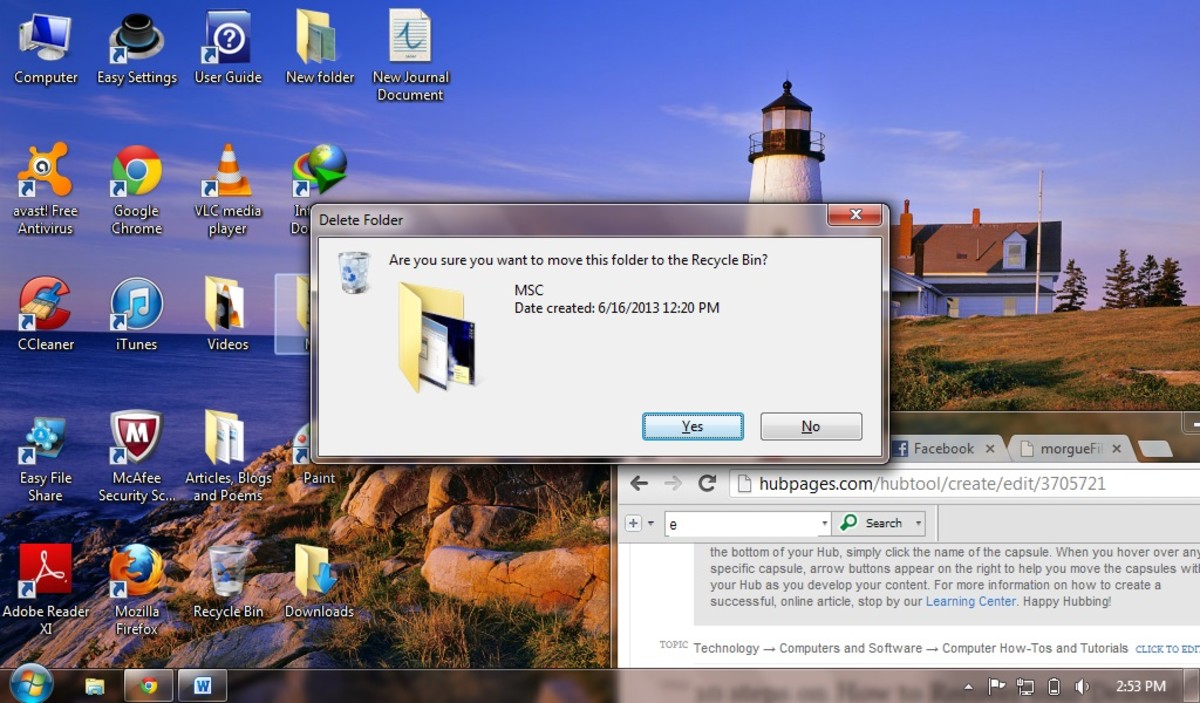
My first attempt to remove the Trojan was an utter failure. I first loaded the AVG anti-virus solution from a clean CD and ran the scan - nothing found. This Trojan either contains a rootkit or the Trojan definition was not loaded with the release. I then ran both SpyBot and AdAware from the same CD. Both these detectors located and cleaned malware from the system. I was elated when I could launch word and surf the web. Then after playing around for 20 minutes or so the pop-up reappeared. OH...
In utter frustration I called the owner and informed him that formatting the hard-drive, reinstalling the applications, and restoring his data would be necessary. The next day I performed the procedure after he dropped of the necessary CDs.
Restoring the Trojan
After rebuilding the system and burning it in to ensure that the Trojan was not hiding somewhere in the boot-sector where a format would be ineffective at removal, I downloaded the AVG anti-virus, SpyBot, and AdAware packages along with their updates. The packages downloaded, installed, and ran without incident. None of the applications located any infections so, although I was disappointed because I had to flush the system; I was content that the system acted normally.
Next I proceeded to restore the owner's data and, to my utter disgust, the Trojan reappeared. WinAntiVirus Pro had infected his data-set and the system was once again rendered unusable. I was now spitting nails.
The First Fix
I was not upset so much by the fact that the system was infected because it arrived in that state. I was upset over re-infecting the system. I should not have restored the data but all his precious family photos would have been lost if I had not tried. This time I was going to remove the Trojan without scrapping the system.
The first thing I did was to load a utility that I have experimented with in the past called Process Explorer, which is part of the Sys Internals suite of security utilities available from Microsoft. What Process Explorer revealed to me was that whenever I tried to launch an application, the application would show up and spawn a process named spools.exe that was not signed by a publisher. I initially thought that the process was related to printing until I noticed that every application attempted would spawn another instance of the process and these processes were eating up most of the CPU utilization.
I did a Google search, from my system, on spools.exe and found that the process may be a rootkit so I killed all the instances of the process using Process Explorer and was finally able to launch Internet Explorer. The home page was re-directed but I was able to replace the URL and successfully navigate to the Google web site. I walked away from the system for a half an hour to see if any pop-ups would reappear. When I returned, there were no pop-ups. The system was functional but hardly clean. If I re-booted the computer the problem would manifest once again. So how do I remove the Trojan when my normal packages are ineffective?
Find Anything on Google
Another Google search located many more sites advertising products claiming to remove WinAntiVirus Pro but none worked. Out of frustration I performed a search on the other Trojan that appeared: Trojan.Downloader. This search located a procedure to use a utility called vundofix that appeared not to succeed but the directions referenced an anti-malware product called Malwarebytes' Anti-Malware. The Malwarebytes application removed the WinAntiVirus Pro Trojan and the machine was once again bootable. After rebooting the system I also ran AdAware 2008 to clean up whatever was left behind and yes, there were some rogue files that remained.
The need for Safe Surfing Habits
he combination of these two utilities successfully removed WinAntiVirus Pro from this particular system but the ordeal involved for removal demonstrates a definite need for safe-surfing habits on the part of web-surfers.
- Sophos Analysis: WinAntiVirus Pro
Sophos is a well respected security organization and has provided an analysis of the WinAntiVirus Pro Trojan. - Vundo Removal Help
One of many sites that provides help removing the Vundo Trojan. This site makes extensive use of HijackThis published by Trend Micro. - TrendMicro HijackThis
Download.com provides a free download of the popular HijackThis utility. - Tech Support Guy
This forum provides instructions on removing WinAntiVirusPro using HijackThis and VundoFix although an operational link must be located elsewhere. - VundoFix
Download site for VundoFix.