BEEF UP PC SECURITY USING COMODO FIREWALL
If your PC is part of a network that has access to the Internet, malware can spread easily, making your data vulnerable. While you can get applications that govern your Internet usage in parts, a strong firewall application like Comodo helps you with the basic settings without the additional load on your PC. You can use this free application on as many PCs as you require, and it is quite easy to work with too.
INSTALL COMODO FIREWALL
Visiting Comodo official website, download the file and start the installation. Set the security level to 'Firewall with Maximum Proactive Defense' to protect your PC from every kind of threat if it is connected to a network. However, if you are a home user, you can opt for the 'Firewall with Optimum Proactive Defence', which offers security against malware that used to bypass firewall applications. If you are using the firewall on a protected corporate network, you can avoid the SecureDNS service. However, it is advisable to use the service to keep hackers at bay. Complete the installation, and you can them go ahead and secure your system further.

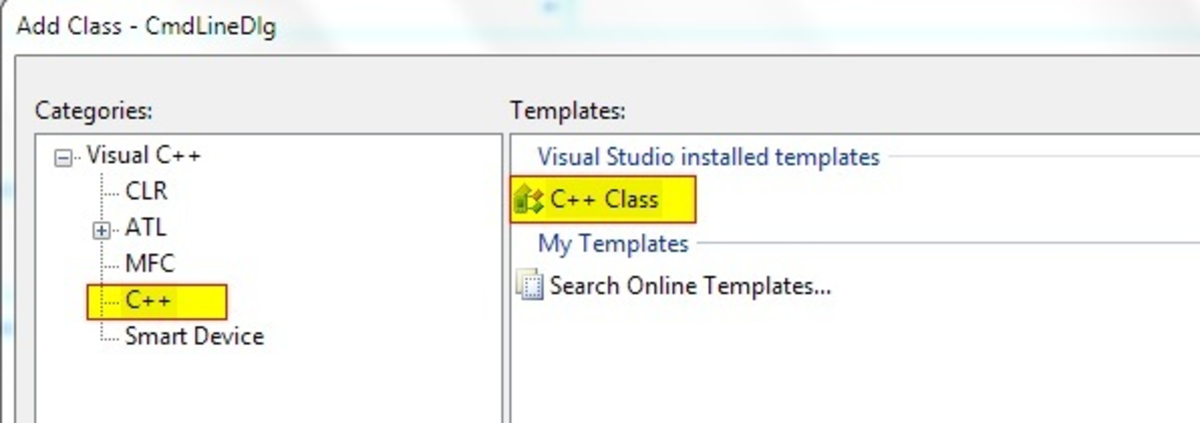
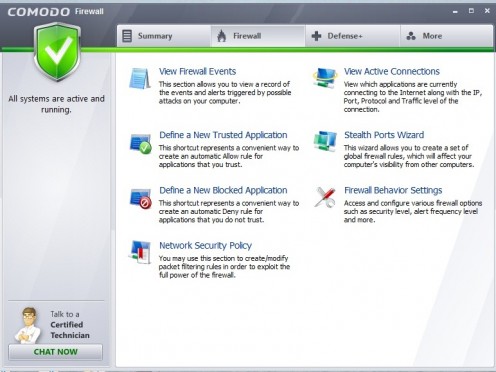
CUSTOMIZE THE FIREWALL
Start the application to customize it to your requirements. When you first start the application, a pop-up window appears that you have close for the application to begin. Click the 'Run Diagnostics' button to check the current status of your system, carry out the steps as directed, and create a diagnostics report if the errors are not fixed. Through an XML sheet, you can figure out what process evokes which module or DLL file so that you can turn them off or delete files from your PC accordingly. Next, click the 'More' button to set your firewall preferences.
SET UP A PROXY
Click the 'Preferences' link to set up the application. Here, you can configure which applications have access to the Internet, and if any new networks are being added to your PC. If you are connecting to the Internet using a proxy service, go to the 'Connection' tab of the Preference dialog box and check the 'Use http proxy' option. Key in your proxy settings and click OK. Alternatively, you can also import settings from Internet Explorer if you are using that as a default browser on your system.
SET UP PARENTAL CONTROLS
If you are looking for basic parental control settings, them Comodo would suffice. In the Preferences dialog box, go to the Parental Control tab and set a password. If you are using the application and need to bypass the firewall later, check on the 'Suppress Firewall alerts if password protection is enabled' and the 'Suppress Defense+ alerts if password protection is enabled'. Use the password to unlock the application and changes the settings.
TURN ON PROTECTION
Once you are with the preference, click the 'Manage My Configurations' link. Make sure that all the services have been activated. If not, just click the 'Activate' button and load the three configuration files. Next, you can further customize the firewall. Go to the 'Firewall' tab and click on 'Firewall Behavior Settings'. Set the 'Firewall Security Level' as required and check the 'Create rules for safe applications' and the 'Enable IPv6 filtering' options. Next, click the 'Advanced' tab, and set the 'Alert frequency Level' as per your requirements.
ENABLING AND BLOCKING APPLICATIONS
With the help of Comodo, you can block potentially harmful applications and you can also create exceptions to the list. To start, go to the Firewall tab. Click the 'Define a New Blocked Application'. Select the application type or browse to block specific applications. Similarly, you can use the 'Define a New Trusted Application' to create a list of exceptions that will run on your PC.
DEFENSE+
When you use flash drives or memory cards, you might encounter unrecognized files that come into your system without your knowledge. You can keep a tab on such files under the 'Unrecognized Files' list located under the Defense+ tab. Just select suspicious files and click 'Delete files' to make sure virus and other malware don't affect your PC. Next, click the 'Defense+ settings' link. Browse through the tabs and change the settings as required.
To further ensure the health of your PC, click the Computer Security Link. It gives you an overview of how protected your system really is. You can add registry entries, files, and folders to the protected list so that they cannot be deleted or manipulated by anyone.