Beat Anonymous--Be Anonymous
Data Security--AFK. . .
Anonymous has emerged as a sort of virtual brigade of the "Occupy" movement. You hear about members being arrested, but the next day hear that they've posted pages of documents.
They're made out to be lurking behing screens, intercepting e-mails, etc. Hackers, however, also rely on techniques that do not require a computer at all; infiltration, observation and deduction are as much a part of the hackers toolkit as packet sniffers.
It starts with, of all things, the garbage can. To the dumpster diver, one man's trash truly is another's treasure. A receipt could have a partial account number or the last four of a social security number and an address, An interoffice memo may have a phone number or a name. A printout might have a password or an internet address that can be exploited. Shredding documents can put a damper on the diver.
A hacker needs to get inside a building to get information. Tailgating, or simply following someone into a building is an easy way to accomplish this. Smokers and their areas are a tempting point of entry for a clever hacker, as is the simple act of holding a door open for someone. A disguise could get a hacker in to a building; with the right clothes and a tool belt, a hacker can be a plumber, an electrician, or an independent contractor, a la the Geek Squad. Simply making sure employees check IDs, and people are aware of who's supposed to be in and around the building can make a tailgater turn tail.
When a person does get inside, getting a password or other identification may be as simple as watching a person. "Shoulder Surfing" dates back to the days of having to enter a personal identification number to use a calling card. Having passwords that are long and complex, and blocking the view of the keypad or keyboard using your hands or body are two techniques that can stop a shoulder surfer.
But a shoulder surfer may not even need to infiltrate the office. Airports, libraries, bookstores, coffeehouses, restaurants, and any other place that there's a WiFi hotspot could be a place for a shoulder surfer to seek information. A company sticker or logo on a laptop is a sure way to attract the attention of a potential hacker. Being careful where you take company computers and covering up logos and stickers with post-its are simple ways to be less conspicuous in a pubic setting.
A hacker may still be able to gather information about you through a simple look at your laptop's screen, Electronic Deduction is the art of getting information like the Operating System, any messaging clients you may have running, what hardware you have and the settings for it, who ,makes the computer from the icons on your task bar or desktop. A program like Fences and making your taskbar disappear can leave any would be hacker drawing a blank.
One lower-tech tool at a hacker's disposal, is the phone. With two phone calls, a hacker could use social engineering to get sensitive and valuable information. One call to get general knowledge, a persons name, the second to get a password or account number. Asking questions like "who's your supervisor" or asking for a badge number might be enough to get a social engineer to hang up and look for a easier target. Also, ones social network can be a tool for social engineers, among other hackers. A name could be found and dropped to provide an opening a hacker needs.
People watching is more than just a way to pass time at an airport, etc. To a hacker it can be a way to locate potential high-value targets. Clothing, hair, shoes, jewelry,. luggage, are all potential things that could pique a hackers interest. Try and blend in; don't wear branded clothing or carry luggage with company logos.
While you're at the airport, or anywhere else, beware of kiosks. A shoulder surfer could easily swipe an id number, or a people watcher see a logo and begin their surveillance.
Your car can be a source of information of use to a hacker. Government plates will surely have a hacker heading to take a look. Stickers on a window can reveal where you live or work. Mail or receipts on a seat can be photographed and analyzed to get the same data that a dumpster dive would find, minus the mess.
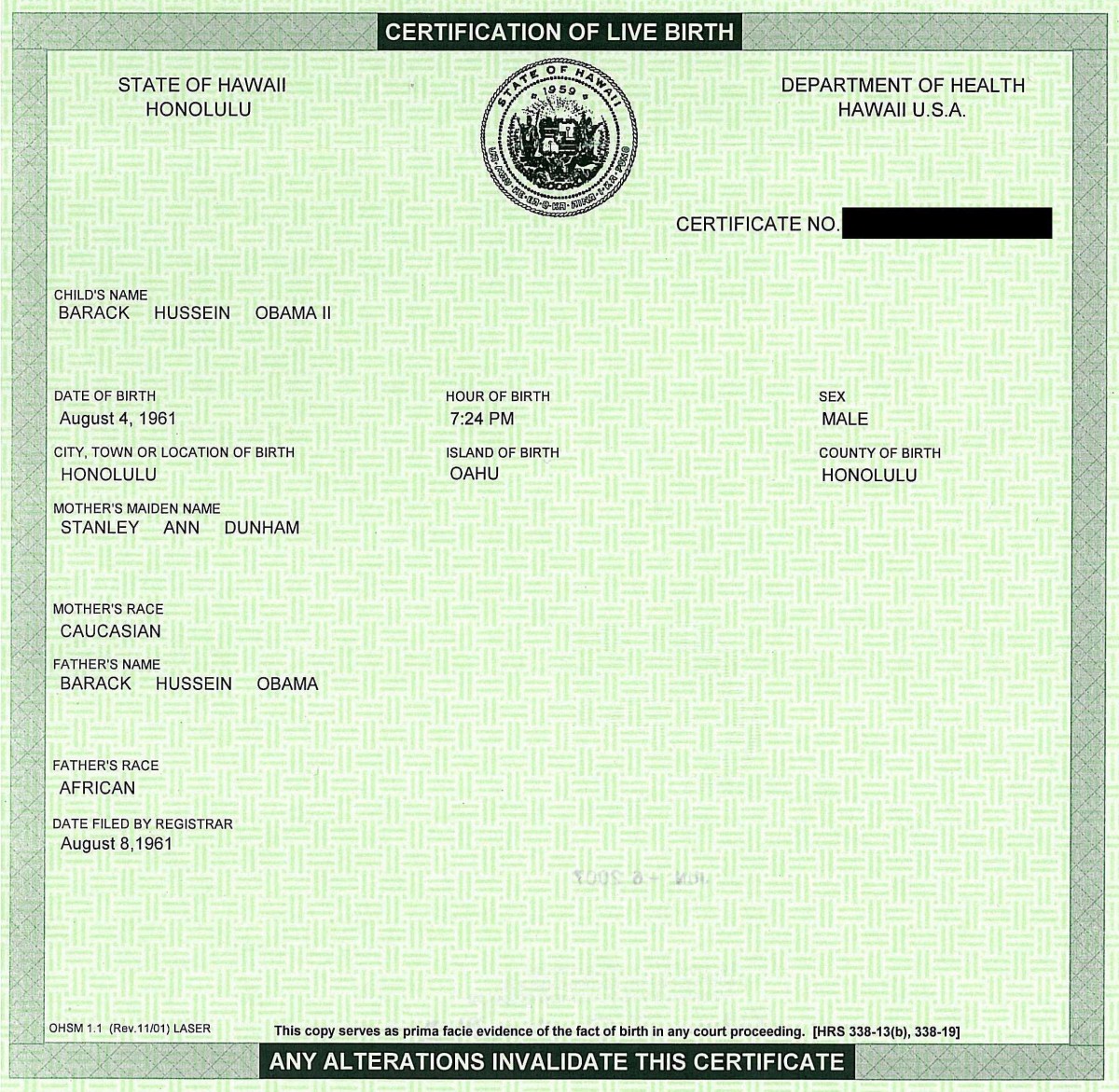
Finally, hide badges. A cell camera can capture data from a badge that with a little social engineering could lead to a leak. Proximity badges could possibly be cloned, so there'd be no need to tailgate.
Sites like Wikileaks and groups like Anonymous rely on lapses to get their information. Avoiding those lapses can go a long way in keeping private information that way
Anonymous And Allies
- AnonOps Communications
Dedicated to reporting news about the hacker collective 'Anonymous' - The Art of Electronic Deduction - DocDroppers
"Deduction is the act of applying reason to arrive at some conclusion. It is a skill that is important to detectives or investigators, but it is a skill that can come in handy for everyone, including hackers. . . " - Proximity Cards
A description of how to 'clone' a proximity card