Computer Malware- Infection Process and Removal Tips

What is Malware
During the Eighties, computers had not yet established a foothold in the world economics. Most of the reasons include less processing power and long coding languages which made the average person think twice before making an investment.
Fast forward to the present era, computer has become a necessity rather than a luxury in fields such as technology, science and processing industries, Personal PC has taken over the common household and business sectors, providing many benefits in the form of internet, office applications, video call, remote access etc.
However as computer evolved in various fields, it also brought along a darker side which is collectively known as Malware.
Malware is a computer program designed by a code writer ( more commonly known as a hacker) which causes disruptive changes in your PC.
The usual form of attack include
- Editing, deleting, changing location or blocking access to personal computer files.
- Getting access to user passwords and credit card details by means of phishing websites and key stroke loggers.
- Drastically reducing system performance and internet bandwidth.
- Unwanted pop ups appearing in the web browser and automatic redirection to webpages which contains other malicious contents.
Types of Malware
Malware as stated is a general term given to programs which performs destructive activities in your PC.
Malware is again subdivided into smaller divisions based on criteria such as
- The mode of infection:- Whether through E mail attachment, downloaded files or storage devices such as USB.
- The behavioral pattern of the particular malware :- Triggering itself on getting a response from the computer user, requiring no activation whatsoever and can spread without the support of a host file, coming into play only after a certain period of time.
- Area of attack:- Such as your PC system files, boot sector or internet browser such as Internet explorer or Mozilla Firefox.
Computer Virus
Computer Virus requires a permission from the user to execute its code (payload) and write into the system memory. For this particular reason, virus always infect the computer in the form of an executable or .exe file.
To make detection harder, the virus usually piggybacks on a software which appears to be useful and legitimate.
Whenever the software is activated by the computer user, the virus also starts replicating and infecting files in the background.
There are two categories of virus based on the type of infection
- Non Resident Virus :- These types of viruses consist of a Finder module and a Replication module. The finder module explores and seeks out files to infect. Once a file has been detected, it calls out to the replication module to infect the file.
- Resident Virus :- consist of only the Finder module. Attacks the memory of the computer and replicates itself whenever the CPU is called to execute a program.
Stealth Strategies
Computer virus use number of techniques to remain hidden from anti virus software or to prevent deletion by users.
Some of the most common ways include but not limited to are :-
- Earlier forms of viruses make sure the last modified date of a file remains the same before and after infection. This helps the virus to cover its track and fool the user into thinking that the specific file is not infected.
- There are number of services running in our PC even during idle mode. Services are important in the sense that they provide support to many of the vital processes. Eg: Dslagent is a service which if disabled can cause loss of internet connection. Winlogon.exe provides the login window when computer boots up. Certain types of viruses take advantage of this and masquerade as vital services to prevent deletion
- Cavity viruses are notorious for inserting themselves into unused space within a file. As a result, the original file size remains the same, even though a 1kb virus had infected it.
- Anti virus software regularly scans the PC for infections and if any abnormalities found, would take steps to correct it. The infected virus will sometime go into offensive mode and switch off the service which initiate the anti virus program. Also viruses can turn off the Windows Firewall allowing other malware to creep into the PC.
- Encryption virus encrypts its virus signature or program code in such a way that an anti virus software cannot find a match. As a result during normal scans, the virus file is passed off as harmless. The hidden code in the virus body is decrypted using a decryption engine which is activated every time a new file needs to be infected.
- Polymorphic Virus which is a grade higher, changes its decryption routine every time it infects a file, so as to prevent anti virus programs from zeroing in on its Decryption engine.
Use of Antivirus software, performing regular system scans and downloading from legitimate websites help reduce virus infections.

Computer Worm
Worm differ from Virus in the following aspects
- Unlike Virus, Worm self replicate on their own. They do not need a user intervention to get activated. In short, they need not attach themselves to a program to get access to a PC. Worms take advantage of security failures in order to infect a host PC.
- Computer worms rarely affect the files on a Computer. They are more concerned with reducing network bandwidth and installing a back door in your PC. Through this back door a hacker can take control of your computer and can use it to send spams or mask his/her own websites. The affected computers are called BotNet which can be used to launch a Denial of Service attack.
As worms exploit the security loop holes in the PC to gain access, regular updates/software patches of the Operating System must be installed from time to time. Installing Anti virus and Anti Spyware software can also strengthen the defense against this malware.
Refrain from opening unknown e mail attachments especially clicking on suspicious web links directing to a particular website
Always keep Windows firewall application in your system activated and do not turn off this feature except for valid reasons.

Spyware
Spyware is a broad term used to define a group of malware, which try's to steal information from a host PC, mostly financial in nature. This includes credit card information, user passwords, online transaction details, net surfing habits etc.
They rarely cause any harm directly to the computer. They are more concerned with stealing sensitive data than affecting host files.
Spywares include but not limited to :-
1. Trojan Horse
Named after the wooden horse in the historical battle of Troy, Trojan horse is a spyware which attaches itself to a useful software, in order to get downloaded into your computer
Once the software is installed in the PC, the Trojan horse starts working in the background collecting information which it is programmed to. They can also enter the system through Drive by Download (Plugins in a Website). Some of the main behavioral pattern of this spyware include
- Creating a back door in the affected PC, to provide access to a hacker. Then the PC becomes a botnet and is used to launch a Denial of Service (DOS) attack.
- Crashing the computer or creating a Blue Screen of Death.
- Keystroke logging.
- Data theft.
- Viewing the user webcam or Screen.
- Operating the affecting computer remotely..
- Altering, Uploading or Downloading files without the users consent.
Link between the hacker and the Trojan horse is required in order to complete the desired operation. These type of spyware do not self replicate nor inject themselves into computer files.
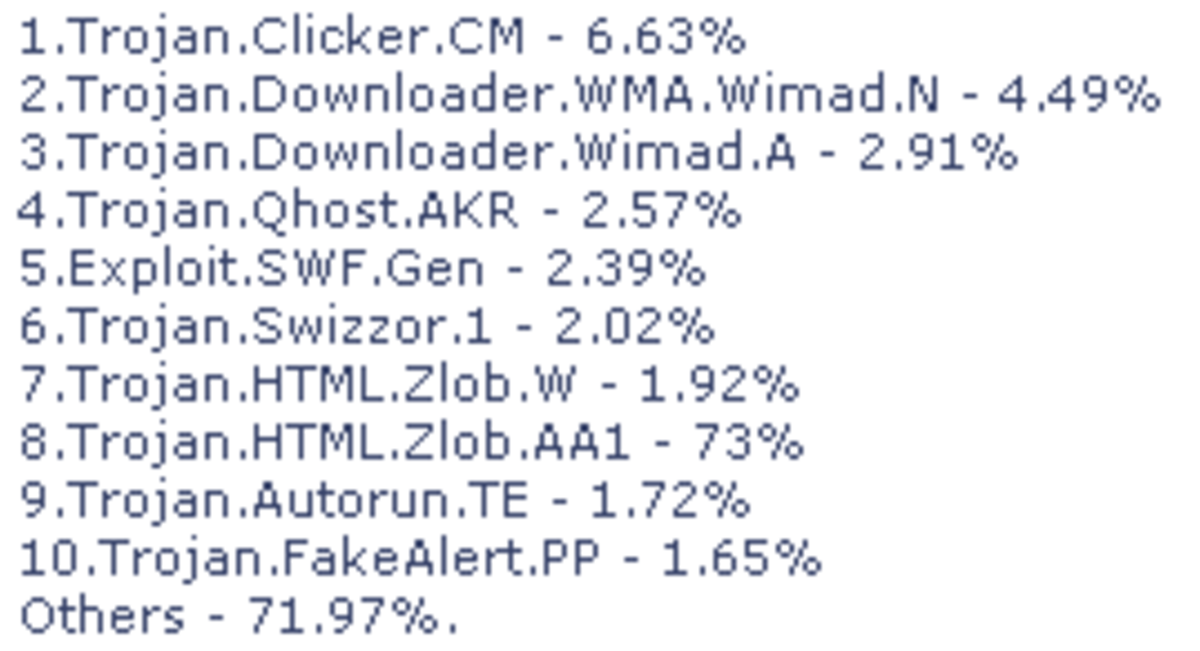
Anti spyware and Anti virus software are crucial in order to detect the presence of Trojans in a computer. A good firewall can also help by severing the link between the hacker and the spyware.
2. Adware
Adware is actually a program designed to promote advertisement for its creator or author. Examples include user interface of certain software, which display information about a product or links to a certain company website.
However Adware can also exhibit Malware properties through certain behavioral patterns.
This includes annoying pop ups when visiting a website. It might also act as a Trojan, recording users web surfing habits and providing the information to a third party.
Anti spyware and pop up blocker software can be installed to protect against Adware.

Joke Program
Joke programs are purely intended to play a prank. They appear and even exhibit Malware type behavior. However they are non destructive in nature and only used to scare a user into thinking his/her computer is affected by a virus.
Some joke programs are also used to check the vigilance of your anti virus software. Eg. Eicar Test File.