Computers---Tips on how to protect your Computer and Identity!

Intro
Many people do not realize that their computer is at risk for many types of Malware. An infected computer can easily infect other computers as well as personal websites and home networks.
With just a few lines of code, even a low level programmer can steal an individual's identity as well as cause mischief with the computer by slowing down programs, eating away at files, and eventually deem the computer useless.
This article lists ways that a computer can be infected with Malware, lists a few ways to protect a computer from the threat, as well as tips to prevent a computer from such Malware attacks.
Below lists different types of Malware as well as different types of ways of receiving malicious software.

Malware



Malware
Malware, is a general short name standing for malicious software, unfortunately lurks everywhere. Malware includes all types of viruses, worms, malicious scripts, trojan horses, spyware, and adware. There are many ways of coming across Malware.
Most common ways:
- Flaws in programs--Hackers search for vulnerabilities/weaknesses in programs. Often times when the weakness is spotted, vendors will release a patch to seal the vulnerability. However, until that patch is released, there is a time where Malware can lurk and infect a computer.
- User Actions--Most common ways of receiving Malware on a computer can happen by clicking on links that are infected or downloading infected software. Nearly guaranteed places to watch out for are pornography sites, "free" software sites that are most likely illegal or contain pirated material, as well as clicking on "You Won" type of links.
Some Signs of Infected Computer:
- Will run slower, may crash often, may shut down unexpectedly, or not shut down at all.
- User may have a ton more pop-ups that are hard to get rid of.
- May have new toolbars in browsers.
- May have new icons from unsolicited downloads.
- May display webpages that were not clicked on.
- Computer may show other quirky behavior.
Below lists some of the different types of Malware as well as a brief description and harm the Malware can do to a computer.



Viruses
Viruses need a program to attach to in order to infect a computer. When the program is executed by a computer or even a mobile device, the virus will infect other programs.
Viruses can be found by downloading infected programs, embedded in e-mail attachments, or visiting other websites that are infected--this includes websites that are legitimate.
Worms
Worms are very tricky because they do not need to attach other programs and can spread from computer to computer at amazing speeds.
Worms can be found and spread through e-mail as well as specific computer weaknesses.
Scripts
Scripts are pieces of code (snippets) that are executed as soon as a webpage is displayed. HTML (Hyper Text Markup Language) used to create webpages often contain such scripts. Most scripts are harmless and are used to enhance a webpage. However, there are some scripts that if the browser shows any weakness can infect the webpage.
Scripts can infect a computer just by visiting a webpage or can download malicious programs that can do damage.

Trojan Horses/Spyware
Trojan Horses and Spyware are often disguised as system files and extremely dangerous because this type of Malware is used to steal information from a computer.
Some just collect information about websites visited, however other types can literally log each keystroke on the keyboard which can look for personal information such as passwords, credit card numbers, social security numbers, as well as other personal information.
This can be installed easily through other viruses, worms, directly from a hacker, downloaded within files, pictures, e-mails etc. Once a Trojan is installed, it will find and exploit the individual user for as long as necessary.
Phishing
Phishing is a very dangerous type of spam. Phishing is common through clicking on e-mails that look authentic.
Basically, the e-mail can look like a bank that is used, common credit card companies, as well as companies like PayPal, or any other type of company.
Another way phishing is done is by creating fake yet authentic looking websites. Phishing is tricky to find.
The purpose of phishing is to find usernames and passwords to real accounts. Do NOT click on links in e-mails. Instead log into the secured encrypted website that often begin with https://. Often if the information is important it can be found on the encrypted website.


Tips to Prevent Malware
The tips below are just some ways to prevent Malware. This does NOT guarantee that the computer will not become infected, however, will help against attacks.


Use Anti-Virus Software, Firewalls, and Updates
This may seem like common sense to some. However, many do not realize the importance of using Anti-Virus Software along with using Firewalls as well as Updating a Computer.
Many ISPs(Internet Service Providers) offer free virus protection. Be sure to download and use the Anti-Virus protection given. Many Anti-Virus protection programs come with a Firewall. A Firewall acts like checkpoint and checks the credentials of packets and if a packet does not have the proper credentials, the packet is thrown out.
For those that do not have virus protection, should download some sort of protection. Avast and AVG offer a free Anti-Virus program, however, be sure to use a Firewall with the free version of these products.
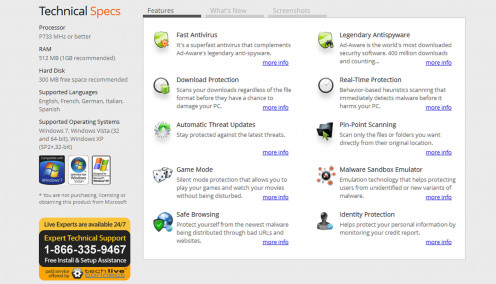
Lavasoft Ad-Aware is another highly recommended program that is free and offers Anti-Virus/Malware detection and removal and should be used in combination with a Firewall. This product is amazing and does catch both older and newer forms of Malware. This can be used and should be used along side other virus protection software.
Norton is a awesome program that offers a free 30-Day trial and does offer Firewall protection along with other tools that allow a computer to stay up-to-date. McAfee is also a awesome program that does offer Firewall protection as well.
Although Anti-Virus Software will detect and remove many viruses, they necessarily will not detect or remove worms. Worms can be prevented by using a Firewall as well as using Computer Updates. Updating a computer will help close any vulnerabilities a computer may have and will help prevent attacks.
Lavasoft Free Ad-Aware

Passwords
One of the easiest ways of hacking a computer directly is through passwords. A beginner programmer with just a little knowledge of hacking can crack passwords using what is known as a dictionary attack.
Just like the name of the attack, uses a customized dictionary to find trends in passwords by looking for direct words and names. With that information, the hacker can easily capture passwords to steal an identity or cause other havoc.
Ways to prevent this type of attack is to use long passwords mixed with upper and lowercase letters, symbols, and numbers. Because many people use basic passwords, hackers can easily find many victims with a dictionary attack. If the password is too complicated, the hacker feels there are many other fish in the sea, and most likely won't bother with using more time doing a brute force attack.
*Note never keep passwords on a mobile device or in a document. Also note be sure to use different passwords for each account and make it a habit to change passwords every few months. NEVER give passwords to others!!!
Below are some common password types.
Examples
Instead of:
| Try Something Similar to This:
|
|---|---|
Password
| P@$$w0rd&xYz
|
ILovemydog
| 1L0v3mID0gg13!
|
swordfish
| $w0rdF1$hSw!mz$
|
momanddad
| M0m@^dD@dRc0oL
|
StarWars
| $t@rW@r$R0Ck$!
|
HotStuff
| H0t$T*uF%f?
|

Other Important Tips
- Do keep computer up to date with the latest updates offered.
- Do keep Anti-Virus software up to date with the latest definitions.
- Do run virus/adware scans on a regular basis.
- Do keep browsers up to date.
- Do use, at the very least, the "medium" security setting on the browser.
- Do protect all passwords and change them every so often.
- Do backup computer on a regular basis.
- Do report Malware to the FTC.
- Do check the source code of personal website. Use a trusted webcrawler to pull the links from website and look for strange links and other code.
- Do NOT click on unsolicited material on the web! Use a pop-up blocker to prevent from accidentally clicking on potential Malware.
- Do NOT open e-mail attachments from senders that are unknown. Opening an e-mail attachment is a dangerous way for Malware to attack the computer.
- Do NOT download anything from a site that is not encrypted or secure. At the very least, make sure the website is trusted.
- Do NOT click on suspicious links on social media sites. Social media sites are a great way to trick a user into clicking on something that can contain Malware.
*NOTE If it sounds too good to be true, than most likely it is--Protect Identity at all times!!!

Other Links of Interests
- How to Remove Computer Virus and Other Computer Malware
New computer virus attacks demand new strategies to fight them. There is absolutely no Windows antivirus security that will rid a user of all viruses from the bad guys. Viruses, Trojans and all computer malware attacks have evolved over the years and - How to remove Iframe Virus or Malware-Badware Code Injection from the Pages of your Website in Fifte
The present hub seeks to explain a method for removing iframe virus from a website using C Panel and free Avast antivirus. I have presented this hub on the basis of my experiences of dealing with the malware and badware injection. - Internet Security Threats Lexicon : Virus, Malware, Trojan, Worm, Spyware, Adware, Botnet etc.