Debating the Factors that Motivate Hackers
When hackers debuted in the 1960’s, as presented by Voiskounsk and Smyslova (2003), the hacker culture was based on an intense interest in computer hardware and software. The predominant motivation was a common quest for knowledge and society benefited from the activities of the hacking community. “Many people believe that the best software products ever created were composed by hackers” (p. 172). Some of these pursuits led to the establishment of companies; the names of which are today household words, for example Apple Computer and Microsoft Corporation.
The rise of the Internet as a global community that permits an unregulated exchange of ideas led a contingent of hackers down a path to mayhem rather than enlightenment. These hackers, or black hats as they are sometimes known, create exploits to break into systems they do not own, write viruses and other malware, and sometimes compromise or destroy data or hardware. This paper presents a debate on the motivating factors that lead individuals to become hackers and continue to hack once hooked. The discussion is a comparison of the views of Sarah Gordon as produced by a 2008 PBS Frontline interview with those of the author. Since the public considers virus writing to be a form of black-hat hacking, this debate focuses on black hat activities including virus writing.

Cybercrime Defined
Public perceptions of hackers promote hackers as cybercriminals, which may be a realistic view in the case of black hat hackers but an understanding of cybercrime is necessary before discussing motivational factors that lead individuals to participate in such activities. Cybercrime, according to Nykodym, Ariss, and Kurtz (2008), includes any crime committed using a computer to commit the crime or aid in the commission of the crime. With the proliferation of the Internet and nearly global individual access to computers and the Internet, all types of criminals may now use computers as tools for criminal activity. However, the Internet as a medium provides certain advantages to cybercriminals Those advantages include the following:
- promote a perception of anonymity
- provide a global presence
- facilitate the identification of victims
- prevent discovery of the criminal
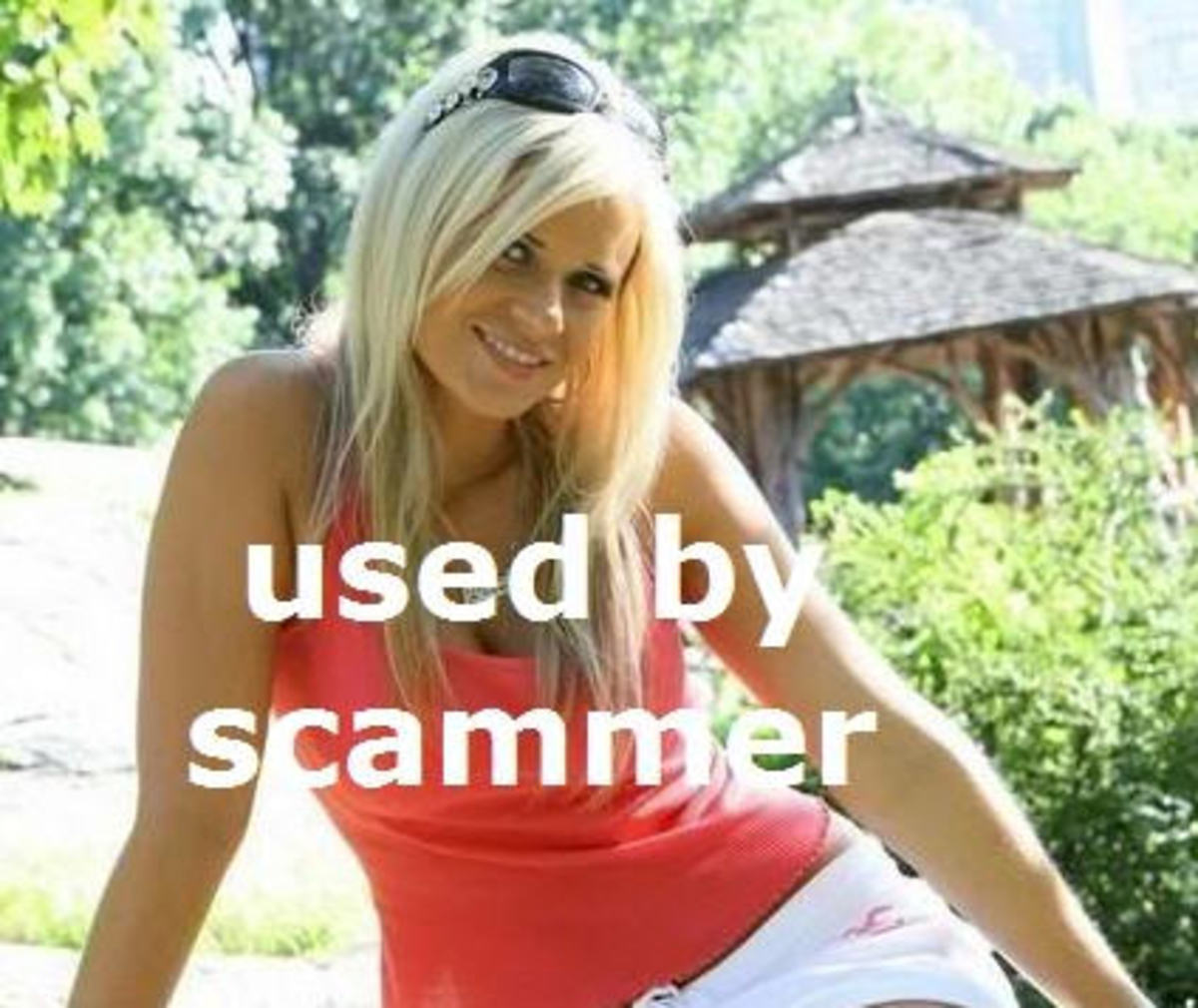
The reader should understand that access to the Internet has not led to the development of new types of crime but has provided new vectors to commit existing crime types in a global arena. For example, thieves committed identity theft long before the rise of the personal computer but access to the Internet replaced dumpster diving with Google searches.
Hacker Characteristics as Viewed by Sarah Gordon
To begin with, Gordon (2008) pointed out a distinction between hackers and virus writers, she claimed that the hacker community loathes virus writers believing that hacking selectively targets victims and requires a more sophisticated skill set than virus writing. On the other hand, most viruses indiscriminately affect systems using a sort of shot gun approach. However, hackers and virus writers share certain characteristics that may explain their motivational factors for indulging in these activities.
Bright and Maladjusted
Gordon (2008) presented the common conception that hackers are considered to be bright and maladjusted, with qualifications on the definitions of the terms. “Some people would argue that doing something illegal is not generally very bright” (para. 8). Gordon countered with the belief that most members of the hacker community do not participate in illegal activities and that obtaining the necessary knowledge to exploit a system requires some amount of intelligence.
Classifying individuals as maladjusted, according to Gordon (2008), requires a reference point to form the classification. Within the hacker community, normal activity would include activity that non-hackers would consider unethical so whether the hacker is maladjusted depends on the viewpoint of the individual making the classification. Hackers may believe they act in a normal manner within their community of association. However, the larger population of which the hacker community makes up a subset would consider hacking behavior maladjusted.
Anonymity and Invincibility
Hackers and virus writers participate in an environment of perceived anonymity, which Gordon (2008) claimed, “breeds feelings of 'invincibility' in many cases” (para. 17). Hackers often leave behind no physical evidence. A bank robber personally faces the victims who may later identify the criminal. A hacker, on the other hand, may conduct activities from hundreds or thousands of miles from the victim with no physical contact. Successfully conducting a number of exploits without being caught increases the feeling of low risk and enhances the belief that future exploits may be undertaken without the fear of being caught.
The Author’s Analysis
Although the author agrees with the classifications presented by Gordon (2008), there are a number of motivational factors that she failed to present during the interview. Voiskounsk and Smyslova (2003) stated that sources maintained by the hacker community attributed illegal actions and motivations to crackers or bad guys who do not associate with the loosely organized hacker community. The coverage by the news media of certain high profile cases “led to the transformations of sophisticated computer specialists into computer pirates. These pirates are usually called hackers—the newest generation of them” (p. 172).
Intrinsic Motivation and Flow
Many scholars believe that money is not a primary motivator beyond a threshold that permits the individual to sustain a particular standard of living (Liccione, 2007). Driving motivation comes from within. This internal motivation derives much strength from feelings of accomplishment and involvement, which web-developers attempt to incorporate into their web designs to generate repeat visitors.
This mechanism, known as flow, may account for the motivation of many hackers to participate in hacking activities. Voiskounsk and Smyslova (2003) provided an explanation of the mechanisms involved by stating that flow involves successive actions that freely result from previous actions. Flow is a natural response to the environment during which time the individual controls his actions for which positive self-rewards add to the experience. The individual looses track of time as one-action flows freely to the next action and “there is a little distinction between self and environment, between stimulus and response, between past, present, and future” (p. 173).
This intrinsic motivation leads hackers to hack for the pleasure they experience while hacking. This group of hackers conforms to the old-world view of hackers, which claims that hackers are motivated by a desire to increase their knowledge. Spammer-X (2004) provided one extreme example of flow leading to obsession, which follows:
By 15 I was fully immersed in everything the Internet had to offer. My father, seeing my love for computers, had bought me my own and had a second phone line installed for Internet usage. With that, I doubt my parents really saw me from age 15 until about 17. My days were spent solely online. I left the house only if it was absolutely necessary, unwilling to venture too far away from my virtual world. Ten to twelve hours a day I spent typing away, and began learning programming languages starting with Visual Basic, C, ASM, and later C++. (p.4).
This theory of flow does not explain the main motivation for all hackers. The expectation of money drives many black hats. A news article (as cited by Kshetri, 2009) “quoted a Russian hacker: ‘There is more of a financial incentive now for hackers and crackers as well as for virus writers to write for money and not just for glory or some political motive’” (p. 142).
Increasing Positive Outcomes
The relative ease of committing hacker related offenses combined with the significant financial rewards associated with committing those offenses provide what Kshetri (2009) referred to as “positive economic feedback” (p.141). This self-reinforcing system of feedback combined with the comparatively low success rate for successful prosecution of hackers leads to increasing positive outcomes. These outcomes then propel the hacker on to commit more offenses.
The teenage experiences of one prominent hacker were chronicled in a book written by that hacker, titled Inside the SPAM Cartel: Trade Secrets from the Dark Side. Spammer-X (2004) stated as the anonymous author of that book, that his high school buddies would often prompt him to take down the school’s Internet access at times when that access was necessary for students to complete assignments. Spammer-X delighted his buddies by fulfilling their requests to perform these denial of service attacks, which led to high levels of praise and propelled SpammerX on to even more invasive exploits; winding up as a spammer in adult life.
What are the most important motivational factors for hackers?
Expectancy and Equity Theories of Motivation
The equity theory of motivation, as summarized by Vecchio (1981), holds that an individual’s level of motivation toward completing a given task relates to the amount of reward the individual could receive in return for the task’s completion. The expectancy theory of motivation relates an individual’s tendency toward attempting tasks viewed with the potential to maximize positive outcomes. These two theories also relate to individuals within the black hat community.
The draw of easy money reaches out to individuals who experience difficulties in the traditional workforce. The high reward achieved from hacking activities compared to the relatively low amount of required effort necessary for those activities has led many technically oriented people down the hacker path in times or areas of economic down turn. “In Russia and Eastern Europe, students good in mathematics, physics, and computer science are having difficulty to find jobs. Evidence indicates that parents and teachers encourage certain computer crimes such as software piracy thereby providing social legitimacy to cybercrimes” (Kshetri, 2009, p. 143).
Conclusion
The interview with Sara Gordon in 2008 provided certain characteristics for hackers, which could lead to an understanding of the motivational factors that lead hackers to participate in less than legitimate activities. However, the author felt that the position taken by Gordon (2008) fell short of providing specific motivational examples. The author also felt that the interview demonstrated that Gordon (2008) refused to provide specific character classifications for hackers, a high degree of qualifying answers seemed precede the responses. For instance, when asked if hackers were maladjusted, the response was “Maladjusted? Sometimes. Again, depends on how you define maladjusted” (para. 9).
The author presented certain motivational factors that the interview seemed to lack. Included in these motivational factors were intrinsic motivation and flow, increasing positive outcomes, and the equity and expectancy theories of motivation. Each of these motivational characteristics apply to traditional careers but take on an added dimension when referring to hackers; what motivates traditional workers also motivates hackers.
Among the hacking motivational factors, the relationship of the equity and expectancy theories of motivation may be most disturbing. These two motivational factors link hacking to economic need and demonstrate that hacking activity may increase during tough economic times. They may also partially explain why so many cybercrime exploits originate from Eastern Europe.
- Who Are Hackers - Studying The Psychology Of Vilrus Writers And Hackers | Hackers | FRONTLINE | PBS
Gordon, S. (2008). Studying the psychology of virus writers and hackers: An interview with Sarah Gordon. PBS: Frontline.
- Kshetri, N. (2009). Positive Externality, Increasing Returns, and the Rise in Cybercrimes. Communications of the ACM , 141-144.
- Liccione, W. (2007). A framework for compensation plans with incentive value. Performance Improvement , 46 (2), 16-21.
- Nykodym, N., Ariss, S., & Kurtz, K. (2008). Computer addiction and cyber crime. Journal of Leadership, Accountability and Ethics , 78-85.
- Spammer-X. (2004). Chapter 1: Inside the head of a spammer. Inside the SPAM Cartel: Trade Secrets from the Dark Side [Electronic Version].
- Vecchio, R. P. (1981). An Individual-Differences Interpretation of the Conflicting Predictions
- Generated by Equity Theory and Expectancy Theory. Journal of Applied Psychology , 66 (4), 470-481.
- Voiskounsky, A. E., & Smyslova, O. V. (2003). Flow-Based Model of Computer Hackers' Motivation. Cyberpsychology & Behavior, 6(2), 171-180. doi:10.1089/109493103321640365