- HubPages»
- Technology»
- Computers & Software»
- Computer How-Tos & Tutorials
Why you shouldn't still be using FTP, SSH is more secure, SFTP on windows
Why you shouldn't still be using FTP
We
all know and love FTP, most of us use it every day to move files back and forth between our web servers and local copies of our sites, but did
you know that FTP is an insecure transport and a better option exists!
A
safer alternative to FTP is to use Secure Shell, for those of you on UNIX platforms there are no worries as it comes built into the OS. Windows users have a harder path, Windows has no built in SSH server, but fortunately a number of free and robust solutions exist.
In this hub I will explain the difference between the two protocols and contrast the reasons for switching to SSH.
As Windows Server 2008 R2 does not have a native SSH Server, I propose a two candidate SFTP servers and some client applications.

File Transfer Protocol (FTP)
File transfer over the network using the File Transfer Protocol (FTP) has its roots in the 1980’s. FTP provides functions to upload, download, and delete files, to create and delete directories and read directory contents.
Although FTP is very popular, it has certain disadvantages that make it a poor choice of transport in the current technology landscape. The major drawbacks include the lack of the uniform format for directory listing and the presence of the secondary connection (DATA connection). Further, there are security holes in the FTP protocol as detailed here by RFT2577: FTP Security Considerations

Secure Shell (SSH)
The Secure Shell (SSH) family of protocols has been developed under the UNIX family of operating systems. Initially, the primary function of SSH was to secure remote shell access to UNIX systems. Later, SSH was extended with file transfer protocol, first SCP in SSH 1.x followed by SFTP in SSH2.
SSH is a very flexible protocol and many different types of services can run on top of it. Additionally, the protocol's open architecture allows these services to run all at the same time without impeding each other.
Version 1 of the SSH protocol is out-dated, insecure, and generally not recommended for use. The SSH version 2 protocol, or SSH2, specifies how a client can connect securely to an SSH server and to use the resulting secure link to access the server's resources.
SSH2 has been standardised by the Internet Engineering Task Force (IETF) and the majority of the world's SSH servers now support SSH2. The application features of SSH include enabling the client to execute programs, transfer files and forward other TCP/IP connections over the secure link.
SSH2 also provides for server authentication, encryption, data integrity verification and client authentication. Server authentication is performed using the DSA or the RSA public key algorithm. For encryption and data integrity verification, a number of algorithms are provided with every SSH2 product. Client authentication can be performed using, amongst others, a password or a public key algorithm such as DSA or RSA.
SSH Services
One service that is often used is the remote console. To provide this service, a channel is created in the SSH session, and the channel is used to exchange data using a terminal emulation protocol such as vt100 or xterm. The client displays to the user a console window within which the user can execute programs on the server as if he or she was logged on locally. For security reasons, if you are just interested in file transfer, this feature must be disabled.
Another very popular service is port forwarding also known as TCP/IP connection tunnelling. With SSH port forwarding it is possible to secure a TCP/IP connection established by an independent application that would otherwise be vulnerable to network attacks. This is akin to creating a VPN between parties.
Finally,
SSH also provides a service known as the exec request, which is
conceptually very similar to a remote console. The exec request executes
a program on the server in the same way a remote console does, but the
program's input and output are sent in a raw format without any terminal
encoding. Exec requests are very useful for network automation
purposes. For security reasons, this feature must be disabled on file transfer only type usage scenario.
FTPS...SFTP
FTPS (also called FTP Secure and FTP-SSL) is an extension to the commonly used File Transfer Protocol (FTP) that adds support for the Transport Layer Security and the Secure Sockets Layer (SSL) cryptographic protocols.
The SSH File Transfer Protocol (also called Secure File Transfer Protocol or SFTP) is a network protocol that provides file access, file transfer, and file management functionality over any reliable data stream.
The "SFTP" abbreviation is often mistakenly used to specify some kind of Secure FTP, by which people most often mean FTPS. Another regular mistake that is made is thinking of SFTP as some kind of FTP over SSL. SFTP is in fact an abbreviation of "SSH File Transfer Protocol".
Pros
FTPS Pros
| SFTP Pros
|
|---|---|
Widely known and used
| Has good standards background that strictly defines most, if not all, aspects of operations.
|
The communication can be read and understood by humans
| Has only one connection with no need for an additional DATA connection.
|
Provides services for server-to-server file transfer
| The connection is always secured.
|
SSL/TLS has good authentication mechanisms
| The directory listing is uniform and machine readable.
|
FTP and SSL/TLS support is built into many Internet communication frameworks and Windows 2008 R2 has built in support for this.
| The protocol includes operations for permissions and attributes manipulation, file locking as well as other functionality.
|
Cons
FTPS Cons
| SFTP Cons
|
|---|---|
Does not have a uniform directory listing format
| The communication is binary and can't be logged "as is" for human reading.
|
Requires a secondary DATA channel, which makes it hard to use behind the firewalls
| SSH keys are harder to manage and validate
|
Doesn't define a standard for file name character sets (encodings)
| The standards define certain things as optional or recommended, which leads to certain compatibility problems between different software titles from different vendors
|
Not all FTP servers support SSL/TLS (Windows Server 2008 R2 does)
| No server-to-server copy and recursive directory removal operations
|
Doesn't have a standard way to get and change file and directory attributes
| No built-in SSH/SFTP support in VCL and .NET frameworks.
|
Security issues exist in protocol
|
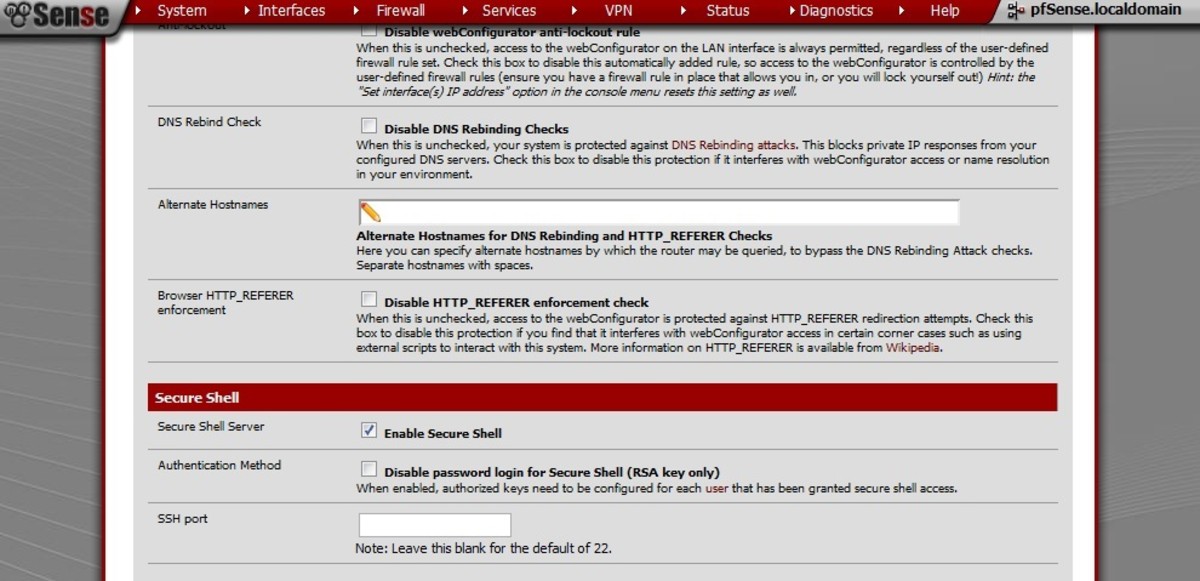
Server Selection
Option 1 - freeSSHd
freeSSHd is an open source SSH server that is simple to install. There is no official support for this product and the product forum is moderately busy.
The settings to secure the installation by disabling terminal shell, tunnelling and other types of access are not readily available. It is assumed that a moderate skill in network administration would be needed to harden this application.
No guides or detailed help files either are to be found on the product website.
Option 2 - Bitvise WinSSHD
Bitvise WinSSHD is a commercial product that has a free option for home use, so if you are just using it to move some files for yourself there is no charge. If you have greater aspirations for it, it is only $ 100 for a perpetual license per machine.
This is a very flexible and feature rich application with extensive documentation that details how to install, administer and harden the installation. The product website has an active forum and it is possible to contact the developers directly for additional support.
Client Application
A SSH Client application is required to connect to a SSH server. As the protocol is standardised any SSH client will do. Options include Tunnelier, Putty and CoffeeCupFTP. The preferred client is the Bitvise Tunnelier SSH client.
The most compelling features of this application include:
Price: Use at a one site is free as long for not more than five users. Licences over this limit cost $45.00 each.
High speed: transfer rates of up to 5MB/s when connected to a WinSSHD server and where network bandwidth and disk resources permit this.
Scriptable: A scriptable command-line remote execution client (sexec) and a command-line terminal emulation client (stermc) are included.Rock Solid File Transfer
So there you have it, rock solid and secure, just the way we like it!