- HubPages»
- Technology»
- Internet & the Web»
- Viruses, Spyware & Internet Security
How to Remove Viruses, Malware and Spyware From Your Computer or Phone

Clean Up Your Computer
Now a days, it's very hard to protect your computer from viruses and threats found today online. Lets face even a car needs work, sometimes more then others or maybe a new engine. Think of it the same way. Your car will run better and smoother as long as you take care of it. Your computer is the same way. So why down download one of the these great free offers to clean up your computer.
Remember, there are a lot of great deals online for cleaning up your computer and getting rid of viruses. Don't rush in to anything before checking out what great deals you could miss while saving a lot of money!

Removing The Almighty Trojan Horse
You need a trojan horse virus removal tool? Some of the viruses won't even let you download trojan virus removal tools in order to fix your computer. Some of them try to fool you into buying their trojan horse virus removal tools instead. Some of them might be hiding within a set of seemingly useful software programs. It can be very frustrating. Hopefully, you already have some sort of tool downloaded onto your computer, but if you did you wouldn't be here to begin with. Right?
Before we begin listing the best trojan horse virus removal tools please let me run you through a few alternative options that you can try first:
- Call IT Support - Having a department can really save you a lot of work as they can do all the work for you with remote desktop software. If you have access to an IT Support team, I would recommend trying this first.
- Disconnect- You need to disconnect from the Internet. You have to make sure that the virus developer can not access your computer files. Especially if it is extremely top-secret job-related information.
- Back up- Back up your files! Take all of your important files and burn them onto a cd or dvd. Remember you can't trust all of your files.
- Scan- Start scanning your computer with a trojan horse virus removal tool. Using a live cd to scan your cd is your best option. This is a cd with trojan horse virus removal tools installed on it.
Okay here are a few of the best FREEWARE trojan horse virus removal programs on the market. I use more then one because while one scan may not detect a virus, another may be able to.
- Ad-Aware- Ad-Aware is a long running software program developed by LavaSoft. It has been very popular for a very long time. Ad-Aware is better for scanning spyware, but it also picks up most viruses too. The current version is called Ad-Aware Anniversary Edition 8.0.
- HijackThis! - Developed by Trend Micro. It basically scans the registry, and hard-drive for malicious content. It doesn't target specific programs, but the methods that hackers use to attack your computer. That means that it can find a lot of things that aren't really viruses, and you may not want to delete. That's why you have to be extra careful with this program, and read the details of everything the scan brings up before you delete anything. However, it works GREAT. Do not be too scared of this program, but please take caution with it. It's worth the risk.
Those are just some of the programs that I use. There are probably quite a few other excellent trojan horse virus removal tools that I did not list. You should travel to the various download sites, and find out what is rating the highest. You might find a program that you really like, and one that works even better. Don't be afraid to read up on it!
Removing Virus from Android phones
Spyware information from articlebase.com
Spyware is something like computer software which enters your computer without your permission. Its motive is to take control over interactions held between the computer and the user. A spyware can do great harm to your personal computer. If you are not yet familiar with this dangerous thing then read on.
A spyware can track down your credit card number and also the things you purchase online. A spyware can easily send e-mails from your e-mail account to the listed contacts without even getting you to know about it. Spywares can easily track down your personal information. A spyware can change the settings of your computer and may crash down your PC. Programs can also be installed without your intimation through spyware. Your important files can get damaged form these.
These were some of the problems created by a spyware. But it can be removed by using spyware remover program such as adware.
As now you know that a spyware enters a personal computer without the knowledge of the user, it becomes necessary to prevent it. There are two types of spyware removal programs. One is the program which is capable of preventing the spyware from entering your computer and the other one detects the spyware and eliminates it from the infected files. Usually, the detection and removal of the spyware is quite easy compared to its prevention. When the process of detection goes on, then all the files of the system are scanned and then the spyware is detected and removed.
There are many new versions of the spyware which are regularly released just after you have got rid of one of the spywares. In order to prevent this you need to keep your system regularly updated. Generally it takes no time for a spyware to replace the old one.
These days the spyware has grown so advanced that it is sold off in shops. Those spyware are even ‘sold’ or distributed over internet form of anti-virus software which is not genuine and you end up installing the spyware itself and then expect your computer to get rid of the same. So check the software properly before installing it into your PC. Buying anti-virus software of a reputed company is always recommended.
Help! How do I clean my computer?
Spyware and virus removal
Inside Spyware: A Guide to Finding, Removing and Preventing Online Pests
Most computer users are aware of the dark side of the Internet. Our online world brings issues of credit card and identity theft, junk mail and seedy content right into our homes and offices. But how many computer users are unwitting accomplices to such activities?
Your computer, or those of the people in your organization, is possibly being used to send spam, harvest e-mail addresses for spam, make purchases using stolen credit cards or take part in a denial of service (DoS) attack, where an army of computers shuts down a Web site by flooding its servers with HTTP requests.
EarthLink's SpyAudit program, which scanned 1,062,756 PCs, found 29.5 million instances of spyware, an average of nearly 28 spyware items per computer.
How does this happen without your knowledge? Examples like those above are usually the work of a trojan, a small program that can be unknowingly installed on a computer and then accessed by another computer over the Internet. Together with programs called spyware, adware and viruses, trojans are a part of a group collectively known as "malware" or "pestware." While the majority of such programs are pests and nothing more, they have the potential to be quite nasty.
Trojans: RATS That Can Control Your Computer
Like the horse of old, a trojan carries with it an unexpected surprise. Trojans do not replicate like a virus, but they do leave behind a program that can be contacted by another computer. From there, they can do just about anything. While it's possible a trojan can be used to take control of a computer, the most common trojans are dialer programs. Dialers are used without your knowledge to make international or premium calls (900-type numbers) from your PC. That's more than an annoyance; it can get expensive.
Trojans are also known as RATS (remote access trojans) and they are most often hidden in games and other small software programs that unsuspecting users download then unknowingly execute on their PCs.
Two common trojans are known as Back Orifice and SubSeven. Back Orifice was originally developed as a remote administration tool. But it worked by exploiting holes in Microsoft software, which makes it a popular tool for nefarious applications. Both Back Orifice and SubSeven can be used to capture what is on a computer's screen and what is typed in using the keyboard; they can be use to remotely control devices, such as opening and closing the CD drive; or to set up FTP, HTTP or Telnet servers on an unsuspecting user's machine. Basically, anything that can be done with a computer can be done remotely using a trojan.
Spyware: Who's Watching Your Online Moves?
Spyware programs range from annoying to the dangerous, including keyboard loggers and screen capture applications that can steal passwords and other sensitive information. The programs are sometimes bundled in with shareware or freeware programs that can be downloaded from the Internet. Often times they claim to be helpful utilities that also carry a more sinister side.
Many of the programs are marketed as legitimate tools for keeping tabs on children and spouses online. One program called Activity Logger, for example, connects to the Internet on its own, records the URLs of sites visited and the keystrokes from e-mail and chat applications. It will also capture screenshots that can be made into a slide show.
If you find Intranet Journal's Spyware Guide helpful, try InsideID's Identity Theft Prevention and Recovery Guide
Adware: Caught in a Marketing Nightmare
Adware is software that displays advertisements to computer users. Some of the most strict definitions of adware include applications that are sponsored for their free use. One of the most popular examples is WeatherBug, which offers a free version of weather software and comes wrapped in a skin that displays advertising. While older versions of WeatherBug had rather significant privacy issues, newer versions are pretty straight forward: you see the ad, but you get the weather. Is this adware? In the most strict sense, many people say it is. But to some computer users, the tradeoff seems fair. Hotmail, Yahoo Mail and AOL's Instant Messenger are among other software programs and services that display ads to their users in exchange for free usage. Many of these programs off advertising-free versions for a price.
More infamous among adware watchers is Gator, which now goes by the name Claria Corp. Gator was controversial from the start. It began in 1998 offering e-wallet software. But it reports your Web surfing habits back to its parent company, which then sends you advertisements targeted according to your data. The vast majority of people consider it a pest, especially because the software is often bundled with other, more useful software. As annoying as it is, Gator is not very malicious.
As for adware that reports personally identifiable information, once again tolerance varies. Some people don't want any information, such as tracking the sites you visit, revealed. Others draw the line at logging IP addresses.
Viruses: Contagious Pests
For all the publicity viruses have gotten, they remain a serious threat. While viruses can potentially destroy a computer's data, most of the widespread viruses have leaned more toward annoyance. The most famous are e-mail viruses that replicate and spread using e-mail addresses stored on a computer. They still cost computer users and their employers hundreds of millions of dollars annually.
The MS Blaster worm that caused havoc in the summer of 2003 exploited a vulnerability in the Remote Procedure Call (RPC) function of the Windows operating system. Anyone who did not install a patch issued by Microsoft was vulnerable, marking a new era in virus prevention for many Internet users. No longer was using care with e-mail attachments enough to keep you safe.
Spyware
Spyware is a type of malware that can be installed on computers, and which collects small pieces of information about users without their knowledge. The presence of spyware is typically hidden from the user, and can be difficult to detect. Typically, spyware is secretly installed on the user's personal computer. Sometimes, however, spywares such as keyloggers are installed by the owner of a shared, corporate, or public computer on purpose in order to secretly monitor other users.
While the term spyware suggests software that secretly monitors the user's computing, the functions of spyware extend well beyond simple monitoring. Spyware programs can collect various types of personal information, such as Internet surfing habits and sites that have been visited, but can also interfere with user control of the computer in other ways, such as installing additional software and redirecting Web browser activity. Spyware is known to change computer settings, resulting in slow connection speeds, different home pages, and/or loss of Internet connection or functionality of other programs. In an attempt to increase the understanding of spyware, a more formal classification of its included software types is provided by the term privacy-invasive software.
In response to the emergence of spyware, a small industry has sprung up dealing in anti-spyware software. Running anti-spyware software has become a widely recognized element of computer security practices for computers, especially those running Microsoft Windows. A number of jurisdictions have passed anti-spyware laws, which usually target any software that is surreptitiously installed to control a user's computer.
Malware
Malware, short for malicious software, consists of programming (code, scripts, active content, and other software) designed to disrupt or deny operation, gather information that leads to loss of privacy or exploitation, gain unauthorized access to system resources, and other abusive behavior. The expression is a general term used by computer professionals to mean a variety of forms of hostile, intrusive, or annoying software or program code.
Software is considered to be malware based on the perceived intent of the creator rather than any particular features. Malware includes computer viruses, worms, trojan horses, spyware, dishonest adware, scareware, crimeware, most rootkits, and other malicious and unwanted software or program. In law, malware is sometimes known as a computer contaminant, for instance in the legal codes of several U.S. states, including California and West Virginia.
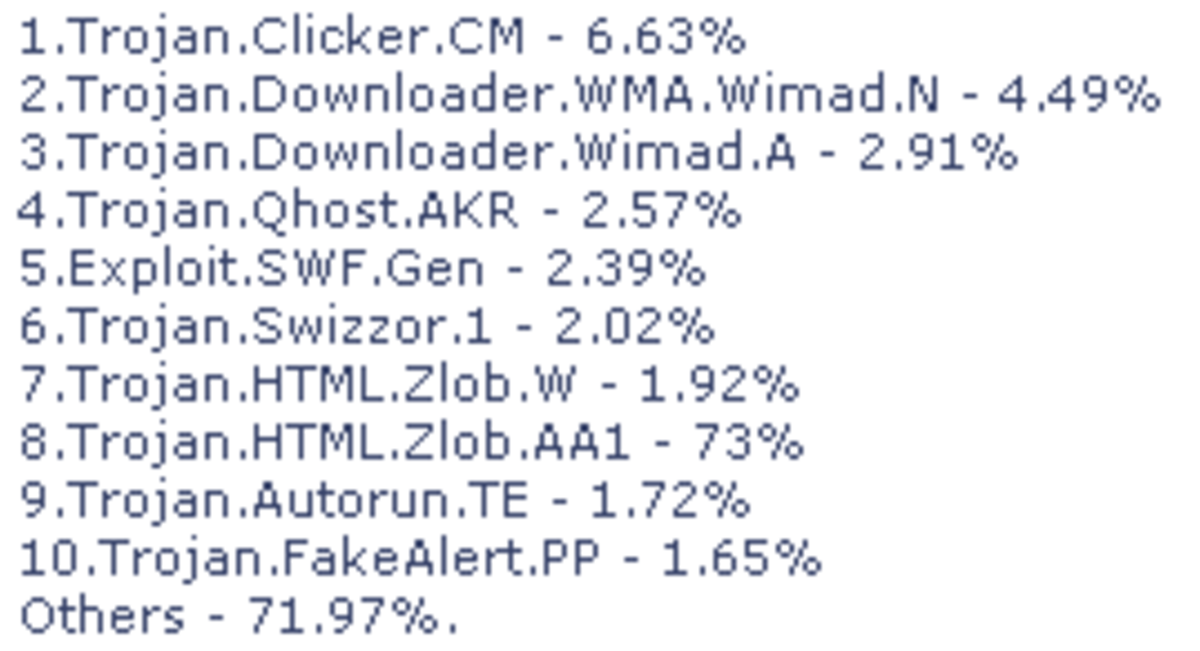
Preliminary results from Symantec published in 2008 suggested that "the release rate of malicious code and other unwanted programs may be exceeding that of legitimate software applications."According to F-Secure, "As much malware [was] produced in 2007 as in the previous 20 years altogether."Malware's most common pathway from criminals to users is through the Internet: primarily by e-mail and the World Wide Web.
The prevalence of malware as a vehicle for organized Internet crime, along with the general inability of traditional anti-malware protection platforms (products) to protect against the continuous stream of unique and newly produced malware, has seen the adoption of a new mindset for businesses operating on the Internet: the acknowledgment that some sizable percentage of Internet customers will always be infected for some reason or another, and that they need to continue doing business with infected customers. The result is a greater emphasis on back-office systems designed to spot fraudulent activities associated with advanced malware operating on customers' computers.
On March 29, 2010, Symantec Corporation named Shaoxing, China, as the world's malware capital.
Malware is not the same as defective software, that is, software that has a legitimate purpose but contains harmful bugs. Sometimes, malware is disguised as genuine software, and may come from an official site. Therefore, some security programs, such as McAfee may call malware "potentially unwanted programs" or "PUP". Though a computer virus is malware that can reproduce itself, the term is often used erroneously to refer to the entire category.
© 2010 Ryan Christopher Beitler