How To Protect Your E-mail Address Book From Computer Worms
E-mail Address Book Protection
Viruses, Worms and Trojan Horses are malicious programs designed to cause damage to your computer. In this article I will be dealing specifically with the computer worm and how you can use an ingeniously simple trick to protect your e-mail address book.
Difference between Virus, Worm and Trojan Horse
A computer virus spreads by attaching itself to a program or file. Because a virus is normally attached to an executable file (EXE file) it can't affect your computer unless you open it. It is by human action that a computer virus is spread.
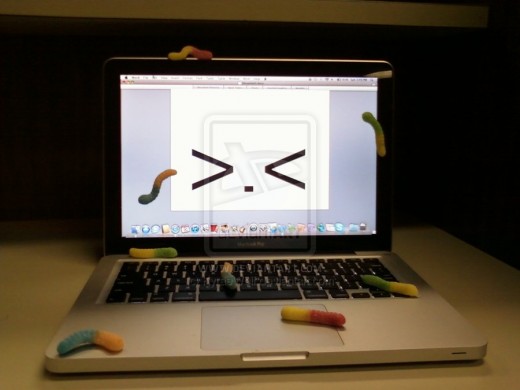
A worm is very like a virus but unlike a virus it does not require human action in order to spread.
Worms use the file transport features on a computer system and so needs no outside help to travel. What makes the worm so devastating is its ability to replicate itself so it has the ability to send out thousands of copies of itself. It can send a copy of itself to everyone listed in your e-mail address book and each person's address book who receives the worm will have copies of the worm sent to every one listed in their address book and the chain continues. Worms consume a lot of system memory and can make your computer become unresponsive. Some worms can burrow deep into your system and enable your computer to be controlled remotely.
The Trojan Horse usually comes disguised as a useful piece of software that causes damage to your computer when you install it and run it on your computer. They can cause all sorts of weird things to happen to your computer like changing your desktop or adding funny active icons to your desktop. Some Trojans are designed to create what is termed a “backdoor” to you computer which outsiders can use to access your personal or confidential information. Trojan Horses do not, however, replicate like worms.
The Trick to Protecting your E-mail Address Book
Step 1
Open your address book and click “New Contact” just as you would do if you were to add a new contact to your list of e-mail addresses.
Step 2
In the box where you would normally type your new contact's name, type the letter “A”.
Step 3
In the box for the e-mail address type: AAAAAAA@AAA.AAA
Now, here's what you've done and why it works
This will be where the worm will start in an effort to send itself to all your friends. However, when it tries to send itself to the e-mail address AAAAAAA@AAA.AAA , it will be returned to you as undeliverable because of the phony email address you entered. If the first attempt fails (which it will because of the phony address), the worm goes no further and your friends will not be infected.
Here's the second great advantage of this method:If an email cannot be delivered, you will be notified of this in your In Box almost immediately. Hence, if you ever get an email telling you that an email addressed to AAAAAAA@AAA.AAAA could not be delivered, you know right away that you have the worm virus in your system. You can then take steps to get rid of it!
What if...?
Some of you might say what if the person who sent you the worm has already created the address AAAAAAA@AAA.AAA and has also set up a worm which sends all your personal information to that address only. If so the email would be delivered because the address exists and you’d never know about it.
To take this into account you could change the e-mail address to AAA@BBB.AAA and that would make it even harder for them to outsmart you.
Spread the Word and kill the Worm!
If everybody you know does this then you need not ever worry about opening mail from friends. Pass this on to all your friends!!!
Links to similar type hubs by Spirit Whisperer
- Backlinks and Hubpages
Other names for a backlink is incoming link, inbound link,inlink, and inward link but for the purpose of this article I will stick with the more popular name backlink... - Trust On The Internet
When dealing with people on the internet it is very difficult to judge who is genuine and who is not.