- HubPages»
- Technology»
- Internet & the Web»
- Viruses, Spyware & Internet Security
Maximizing Online Anonynimity

What is Online Anonymity?
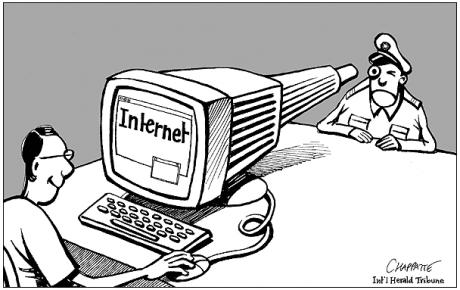
Being anonymous is something everyone is curious about. We all know that the major email services (GMail, HotMail, Yahoo!) scans our emails and builds a profile based upon our internet activity. What many may not know is that nearly all of your online activity is (or can be) tracked, unless you take active measures to hide your identity.
In addition, the latest Heartbleed SSL exploit as well as the Internet Explorer vulnerabilities leave us scratching our heads and worried that our personal data is not secure.
This article will help you increase your anonymity online and help you understand how the process works to better safeguard your personal data.
Limits to Online Anonymity
Before going any further, it is important to discuss and understand the limits of any actions you may take to become anonymous online.
There is no single step solution to maintaining privacy online. If you need complete privacy, and security you will have to permanently unplug your computer from the internet.
Understanding this, there are some steps you can take that will make it very difficult for your internet activity to be tracked.
The very first step is to understand that no software solution will protect your anonymity if you willingly give it away!
Browser Plugins
If you are just getting your feet wet with online privacy, you may want to consider some browser plugins/extensions. Browser plugins fall into a few categories: Scripts, privacy, and tracking. While the methods used to track your behavior online are many, here are a few good plugins which should get you started.
Script Blocking Plugins
These will help block harmful scripts which allow attackers to control your computer, as well as blocking scripts that help track your online activity.
Privacy Plugins
These plugins will help keep any data you transmit secure and private.
Tracking Plugins
These plugins help to block any attempts to track your online trail. Tracking comes in many forms and when combined, can create a complete profile of your online activity.
Plugin Name
| Script Blocking
| Privacy
| Tracking
| Firefox
| Chrome
|
|---|---|---|---|---|---|
AdBlock Plus
| x
| x
| x
| x
| |
SafeScript
| x
| x
| x
| x
| |
Disconnect
| x
| x
| x
| x
| |
HTTPS Everywhere
| x
|
The tools are available, it's up to you to install what works best for you.

TOR Browser Bundle
The Tor Browser Bundle lets you use Tor on Windows, Mac OS X, or Linux without needing to install any software. It can run off a USB flash drive, comes with a pre-configured web browser to protect your anonymity, and is self-contained.
After you've begun changing your online habits, and incorporate browser based privacy plugins, you may wish to consider taking your anonymity and security a step further by installing the Tor Browser Bundle.
The bundle includes a modified version of the Firefox web browser, a connection to the TOR network, and some of the privacy plugins mentioned above.
Using the browser bundle provides a medium level of security, but has faults and cannot provide 100% privacy (does that even exist?)!
Many of the functions we're accustomed to in a normal browsing experience are not available by default with the Tor Browser Bundle. This is because many of these tools (javascript, cookies, flash, etc.) can be used to track your online behavior and are a privacy risk. It's amazing how different the internet looks without all of the tracking tools enabled.
Using TOR Browser Bundle

TAILS
Tails is a live operating system, that you can start on almost any computer from a DVD, USB stick, or SD card. It aims at preserving your privacy and anonymity, and helps you to:
- use the Internet anonymously and circumvent censorship;
all connections to the Internet are forced to go through the Tor network;- leave no trace on the computer you are using unless you ask it explicitly;
- use state-of-the-art cryptographic tools to encrypt your files, emails and instant messaging.
TAILS can be downloaded and run from a USB drive, or a CD-ROM. It leaves no trace of its activity on the computer it is run from. TAILS provides a great layer of anonymity and privacy, assuming it is used correctly.
TAILS should never be used within a virtual machine environment, unless it is for testing! This ensures your main OS never knows about your use of TAILS. Imagine if your main OS was compromised, your virtual machines would then be considered compromised.
TAILS routes all traffic through the TOR network (mentioned above), and includes productivity tools as well as communication software. Since TAILS includes the TOR Browser Bundle, it also includes many of the browser plugins mentioned above. For this reason, TAILS can be considered some of the best anonymity and privacy software available to us.
Using TAILS
Weigh In
How serious are you about online privacy?
Do You Take Privacy Seriously?
Perhaps you've never considered your online privacy until now. That's ok. If you are concerned about information about you being in the wrong hands, you can use the information in this article to help you get a handle on the data you provide. This will help you to minimize the impact of your online footprint.
Did I forget something, or is there are part of the article that is unclear? If so, let me know in the comment section below. I look forward to hearing from you and the steps you take to keep your private information safe online.
© 2014 davidwhoward



