My Joomla website was hijacked - Pharma hijack
How to Diagnose and Remove the Joomla Pharma Hack
It all started when I applied via HubPages to Google AdSense for an AdSense account. Google declined my application simply indicating – Unacceptable site content.
I was pretty amazed at the response from Google. This is because all the content of my Hubs and Website were techie type tutorials covering a host of Open source topics. There was nothing nasty in my content to tick off Google, or so I thought.
I immediately fired up Firefox and got into battle mode.
In its Google search box I typed in site:opensourcevarsity what I saw there took the wind out of my sails.. At least I figured out why Google refused my AdSense request. My website looked like a glorified pharmacy selling Viagra and Cailis and other invigorating pills and portions. Take a look at diagram 1
My Joomla website had been hijacked. I was in trouble.
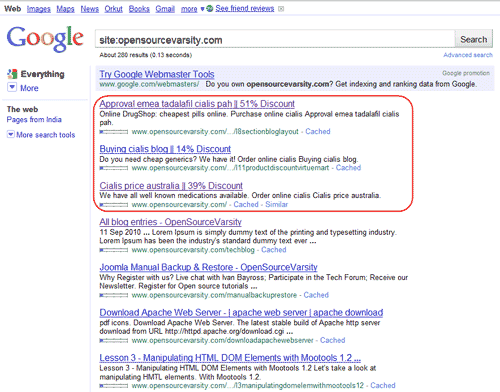
What you see in Diagram 1 is that some of my page <title> and my page <description> tags have been hacked and the hackers have placed their information there. Surprisingly the hackers had successfully attacked and changed the <title> and <description> tag information of several inner pages of my website
A lot of my pages, built using the labor of love, to provide tutorials on open source tools and technologies for free, now look like the best website for anyone with an erectile dysfunction. Seesh !!!.
Okay, so this needs to be fixed and fixed ( hopefully ) permanently before Google next spiders the website.
There are two separate problems here:
- Fix the website
This requires finding out how the hijackers achieved their goals and ( hopefully ) put an abrupt stop to this.
- Wait till Google spiders the website again and pray that their index gets cleaned up over a period of time.
Figuring out how the hijackers achieved their target is the easy part. Waiting for the Google spider to clean the index entries is the pain. This is something that no website owner has any kind of control over. I guess one has to just ‘Girdle the loins and sit tight’ if one is the praying type – Prayers may help.
What Does the Joomla Pharma Hack Do?
There were several facets of the Pharma hack that I found particularly interesting. A remarkable aspect of the Pharma hack is that it didn’t affect every page of my site.
- The results of the hack are only visible to search engines
If your website is hacked, the pages displayed to those who visit your website remain visibly unaffected. Hence, the hack will remain invisible if anyone just views the website pages.
The goal of this hack seems to be to gain valuable links from ranking pages of another website. The hackers have wisely chosen to create as few ripples in the water as possible while achieving what they want .
- Like all hacks, the pharma hack must also place malicious files in your Joomla folders somewhere order to get their job done
Like other hacks that I’ve encountered, the pharma hack also disguises all of its code using what appears to be legitimate file names when they are placed within Joomla folders.
- Additionally, never overlook the possibility of the hackers placing their rouge code within various Joomla tables
How Does the Joomla Pharma Hack Work?
Now we know what the Pharma hack does. However, in order to eliminate it from a website and to prevent attacks like this in the future, we need to know how it works.
Basically, the Pharma hack seems to consist of malicious files placed within various Joomla plugin folders.
NOTE: It’s possible that the files placed in the Joomla plugins folder contain code that in turn runs encrypted code stored in the Joomla database tables. BUT, after really carefully studying our Joomla database tables content we could not find any such codespec.
Removing the Joomla Pharma Hack
Even if you don’t see any symptoms of the Pharma hack currently (like cloaked title tags in search engine result pages), your site may still be hacked and therefore completely vulnerable.
Oh, and before we go any further, let’s get one thing straight — you are running the latest version of Joomla, aren’t you? – Great, I knew you were the serious website owner :D.
Oh, and before we go any further, let’s get another thing straight — you are running the latest version of a good antivirus on your local computer and its virus signature is the latest available.
Oh !! man that’s so reassuring,
Now here’s what you can do:
Use cPanel and create a zip of all your website files and folders that belong to your website
Download this zip file to your local computer.
Immediately disconnect you computer from the Internet so that it is a standalone computer.
- This could mean simply disabling your network interface in the computer / laptop
- Removing a dongle if you use one to get on the Internet
- Switching off your Modem ( or your Switch if you are using one). Switching off any one will do
- The idea being get off the Internet after the website zip file downloads to the local computer
Okay so now we have the complete backup of your website on your local computer, and the local computer is isolated.
Navigate to the folder where you’ve downloaded the zip file to. Select the zip file and then use your antivirus to scan the zip file. Do this at least twice. I’m pretty darn certain the infected files will be identified by your antivirus.
Now , here’s a small plug for AVAST antivirus. I’ve been using the free version it for years. It’s pretty good at identifying PHP based Trojans, which I’m modestly certain your Pharma infection is all about.
Do note down the folder names and file names of all the infected files so that you document what was infected this time around. An XL spread sheet should be fine. Will be a big help the next time around ;-0.
Next you can let your antivirus Delete the infected files in the folders
OR
You can unzip the downloaded zip file and use your file browser and Shift
/ Del each of them personally.
I love the personal deletion process, gives me a good feeling.
If you have unzipped the files because:
Your antivirus cannot delete an infected file from within an archive
OR
Because you wanted the sheer pleasure of killing them yourself
You will have to re-zip the whole shebang to ready it for upload once again to your website.
Congratulation!!!!!! The cleaned zipped file is - your cleaned website.
But Wait – there’s one more job.
Using your cPanel, scan your current website on your hosting server.
BTW, all cPanel’s I’ve used offer you’re an antivirus (normally Clam antivirus if you are hosting on a Linux box) and permit you to scan your website on the hosting server itself.
Why – Good question – Often such hackers have placed there obnoxious files in a folder outside public_html which is where your website is normally located. Hence, if these obnoxious files are not found, and deleted your cleaned / uploaded website will get infected again almost immediately.
BTW - my hackers had placed their files in the /tmp folder above pubic_html on my hosting server.
cPanel’s antivirus software ( most likely ) will only identify the infected files not kill them. You have to note down the folder and files and then use cPanel’s file manager to delete these files manually or FTP and delete these files - choose whatever you are most comfortable with.
Now your hosting server is ( hopefully ) clean.
Delete all the files and folders within public_html. Yes, delete all the files and folders of your website. Was that a quiet sob I just heard? Nevertheless:
Re-connect you local computer back to the Internet, remember you had isolated it?
Upload your cleaned out re-zipped file back into public_html,.
Using cPanel, unzip the uploaded zipped file. In an instant you should have a clean, un-hijacked website running on the internet.
Break out a chilled one, take the weight off your feet and . . . sip.
To Effectively Round-Up
( After completing the chilled one - is fine )
When you scanned your website using cPanel, I'm sure you documented which plugin folders were infected.
Uninstall that plugin immediately. Use the Joomla plugin directory and search for another plugin that does what you want. Install that plugin. If you have to spend a few bucks to purchase a commercial plugin maybe that would be a good idea as well.
One thing I learned the hard way was, when you locate a plugin that you like to use, there’s always the Authors website button somewhere on that plugin’s download page.
Navigate to the author’s website. Pick up the URL, and do a whois lookup on the domain name. Read the information displayed carefully. If you like what you see download the plugin and use it. If you have even a seconds hesitation, Do not use that plugin. This approach has saved my bacon on occasion.
Finally, remember to constantly check that Google has re-spidered your website and that your Title and Description information are Okay once again.
BTW, if your Joomla website has been hijacked and you are struggling, do get in touch. I'll help if I can. I've also written a few tutorials on How to harden a Joomla website. Do take a look.
Ivan Bayross
Tutorial for Joomla | Joomla Tutorials