Network security concepts
Authentication technologies and protocols
Authentication is the simple process of verifying the identity of the user. The first point of controlling access to a system is the authentication. In computer security, the authentication is the method of verifying the identity of a person or an application that requires access to the system. If a user requires access a PC or system, the identity of the user is usually verified by the user entering a correct username and password. If the username and the password of the user matches the ones that are stored in the security database of the computer, the user is given access.

Username and password.
Almost every operating system implements some kind of authentication system where users can simply use a username and password to get access into the system. When the user enters their details, the local security database is checked to verify that they are correct. If a match is found, the user is granted access, and can log into the system. Although this is the most popular authentication method, it certainly has its disadvantages. Think of all the people who have ever told you their passwords. What about all the people who have their passwords written down on a piece of paper at their PC.
Biometrics.
Biometric authentication refers to the technology that is used to verify the identity of a user by measuring and analyzing the human physical and behavior characteristics.This is done with the help of an advanced bio-metric authentication system. Biometric Device can read and measure or analyze fingerprints, scan the retina of the eye, and recognize facial patterns, and also measure the body temperature. There are also biometric authentication of handwriting and voice patterns.

Smart cards.
Smart card authentication stores a small amount of data that is then used to verify the holder of the card. These cards are normally the size of a standard credit card. When you use a smart card for authentication and identification purposes, they generally prevent modification of the data stored on them. Smart cards are designed with security in mind, and to protect them against the theft of data and are immune to EMI and RFI interference.

Security tokens.
A security token is sometimes known as authentication token or a hardware token, is considered to be one of the most trusted methods for verifying the identity of a user or a system. Security tokens provide a very high level of security for authentication. It is almost impossible to copy the information that is contained in a security token. A security token is made up of two parts. These are a hardware device that is coded to generate the token values at a predetermined interval, and also a software based component that then tracks and verifies that the codes are valid.
Security tokens can also come in the form of key fobs too. Some of these security tokens will contain cryptography keys while some can contain biometric data such as fingerprints of the user. Some security tokens also have a built-in keypad, and the user is required to key a PIN number into the device.
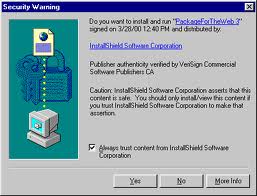
Digital certificates.
Digital certificates are very widely used for mainly for Internet based authentications on websites, and sessions. Digital certificates will authenticate the users and computers in network environments. To access the network resources and services where the directory services such as Microsoft’s Active Directory services are implemented. Certificates are a part of the public key infrastructure (PKI). In PKI the certificate servers are used to create / store / distribute / validate, and also the expiration of the digitally created signatures and other identities of the users and systems. Certificates are created normally by a trusted third-party known as the Certification Authority or the Certificate Authority (CA). Some of the more well known names are Verisign and Commodo. It is also common to create a CA within an organization to manage the certificates for the users and systems inside the organization.
Certificates are sometimes used for software signing. Software is then digitally signed to give the user confidence that it was developed by the original software vendor. It also ensures that the software has not been hacked or changed in anyway.


![How to Remove Kaspersky Password Protection? [Easily Recover] How to Remove Kaspersky Password Protection? [Easily Recover]](https://images.saymedia-content.com/.image/t_share/MTc2Mjk3NDcwOTAzNTkyMTI2/how-to-remove-kaspersky-password-protected-easily-recover.png)